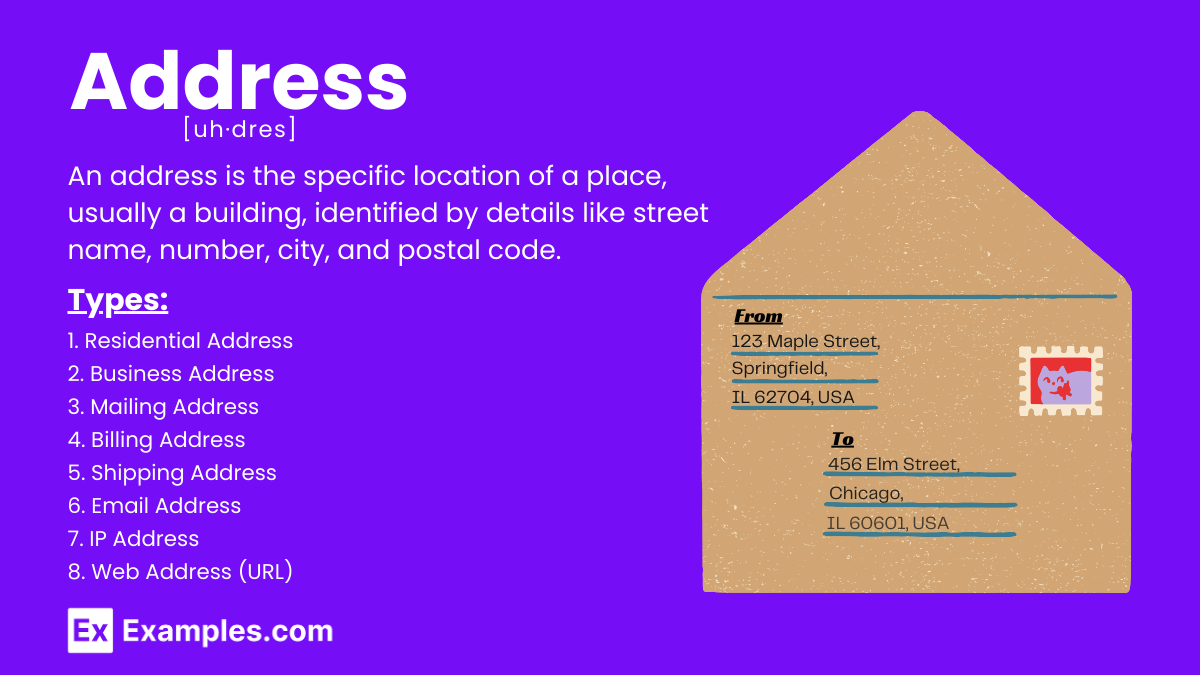
In the rapidly evolving landscape of information technology, terminology often carries multiple layers of meaning depending on the context of the infrastructure, software development, or hardware architecture. The term “addressed” is a foundational concept that permeates almost every facet of the digital world. While a layperson might think of a physical mailing address, in the tech sector, to be “addressed” refers to two primary pillars: the location of data within a system and the resolution of technical challenges.
Understanding what “addressed” means in a technical sense is essential for developers, network engineers, and system architects. It is the difference between a functional system where data flows seamlessly and a chaotic environment where information is lost in the void. This article explores the nuanced definitions of “addressed” across memory architecture, network protocols, and software lifecycle management.

The Architecture of Memory: Understanding Memory Addressing
At the most fundamental level of computing, “addressed” refers to the process by which a Central Processing Unit (CPU) locates specific pieces of data within a computer’s memory (RAM). Every byte of data stored in memory is assigned a unique identifier, known as a memory address. When a program needs to retrieve or store information, it doesn’t search through the entire system; it points to a specific address.
Virtual vs. Physical Addresses
Modern operating systems use a sophisticated layer of abstraction known as Virtual Memory. In this context, “addressed” takes on a dual meaning. A software application sees a “virtual address,” which is a simplified, logical map of the data it needs. However, the hardware must map this to a “physical address”—the actual hardware location on the RAM chips.
This mapping is handled by the Memory Management Unit (MMU). When we say a memory location has been “addressed,” we are referring to the successful translation of these virtual coordinates into physical ones. This abstraction allows multiple programs to run simultaneously without interfering with each other’s data, ensuring system stability and security.
The Shift from 32-bit to 64-bit Addressing
The history of computing is defined by our capacity to “address” larger amounts of information. For decades, 32-bit architecture was the standard. A 32-bit system can address approximately 4.29 billion unique memory locations, which translates to a maximum of 4GB of RAM. As software became more resource-intensive, this limit became a bottleneck.
The transition to 64-bit addressing changed the landscape entirely. A 64-bit system can theoretically address 18.4 quintillion bytes (16 exabytes) of memory. In this tech niche, “addressed” defines the limits of human innovation; by expanding the address space, we enabled the rise of big data, complex 3D rendering, and high-performance AI models that require massive amounts of data to be “addressed” in real-time.
Navigating the Digital Map: IP Addressing and Network Protocols
Beyond the internal components of a computer, “addressed” is the cornerstone of the internet. Every device connected to a network—whether it’s a smartphone, a smart fridge, or a massive server in a data center—must be uniquely addressed to send and receive data packets. This is the realm of Internet Protocol (IP) addressing.
IPv4 vs. IPv6: The Expansion of the Global Address Space
For years, the internet ran on IPv4, which uses a 32-bit addressing scheme (similar to old memory limits). This allowed for about 4.3 billion unique IP addresses. However, with the explosion of the Internet of Things (IoT), we effectively ran out of addresses. The tech community “addressed” this shortage by developing IPv6.
IPv6 uses a 128-bit address, providing an astronomical number of potential addresses (340 undecillion). When a device is “addressed” under IPv6, it isn’t just a part of a local network; it has a globally unique identifier that facilitates more efficient routing and better security. This evolution ensures that every sensor in an automated factory or every wearable device can be specifically addressed across the global web.
Static vs. Dynamic IP Addresses
How a device is addressed also depends on the stability required for its function.
- Static Addressing: A permanent address assigned to a device. This is crucial for servers, printers, and web hosts. If a website’s address changed every hour, your browser would never be able to “address” the server to load the page.
- Dynamic Addressing: Managed via DHCP (Dynamic Host Configuration Protocol), this assigns a temporary address to devices as they join a network. This is more efficient for consumer devices (like your phone) that move between networks.
In both cases, “addressed” implies that the network infrastructure has successfully recognized the device and provided it with the necessary credentials to communicate within the ecosystem.
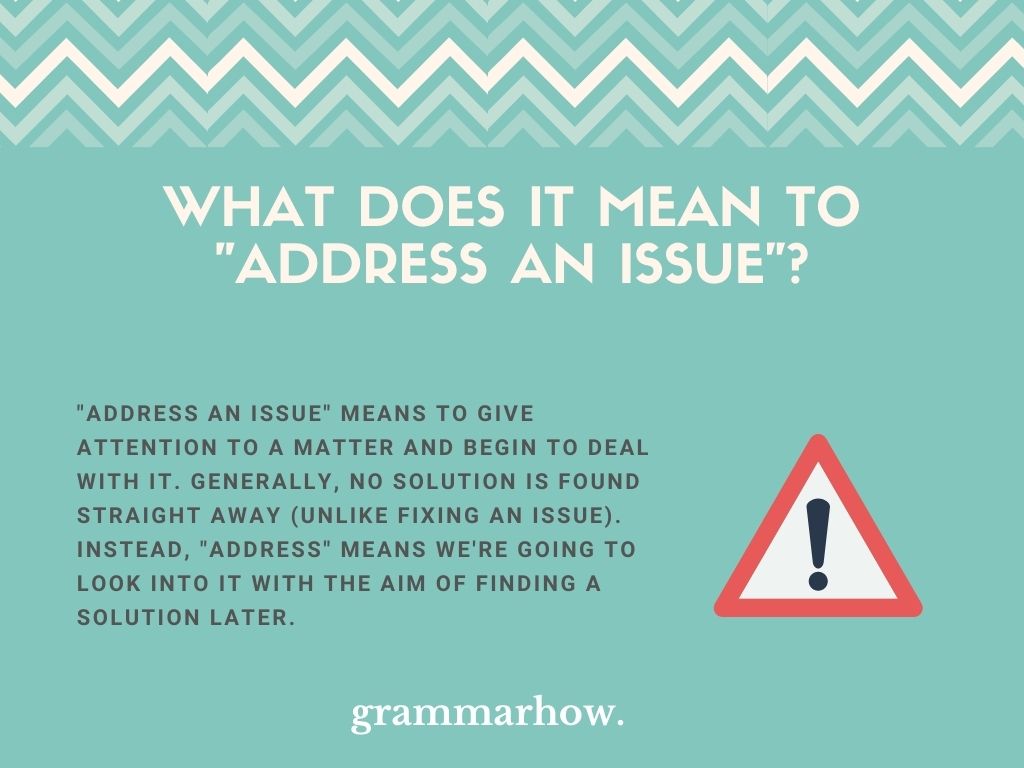
Software Lifecycle and Issue Resolution: When a Bug is “Addressed”
In the world of software engineering and DevOps, the word “addressed” moves away from location and toward action. When a developer or a project manager states that a vulnerability or a bug has been “addressed,” it signifies a complete lifecycle of identification, isolation, and resolution.
The Debugging Workflow: From Identification to Resolution
An “unaddressed” issue in software is a liability. It could be a memory leak, a logical error, or a security flaw. The process of addressing these issues involves several technical steps:
- Triage: Determining the severity of the issue.
- Reproduction: Creating a controlled environment where the bug consistently appears.
- Root Cause Analysis: Using diagnostic tools to find the specific line of code or configuration causing the error.
- Mitigation: Developing a patch or a workaround.
Once these steps are completed and verified through automated testing, the issue is officially “addressed.” In this context, the term serves as a milestone in the software development life cycle (SDLC), moving a task from the “backlog” to “resolved.”
Patch Management and Version Control
Addressing software issues isn’t a one-time event; it’s an ongoing process of maintenance. In modern CI/CD (Continuous Integration/Continuous Deployment) pipelines, addressed vulnerabilities are pushed to users through patches and updates.
Using version control systems like Git, developers can track exactly how a problem was addressed, by whom, and when. This creates a historical record that is vital for digital security. If a new update breaks a feature, engineers can look back at how previous issues were addressed to find a solution. “Addressed” here is a synonym for technical accountability and progress.
The Future of Digital Identity: Addressing in Web3 and Beyond
As we look toward the future of technology, the concept of being “addressed” is shifting toward decentralized models. In traditional systems, addresses are assigned by centralized authorities (like ISPs or hardware manufacturers). In the emerging Web3 and blockchain niche, addressing is becoming a matter of cryptographic identity.
Wallet Addresses and Blockchain Transparency
On a blockchain, a “wallet address” is a hashed version of a public key. It is the destination for digital assets and the identifier for smart contract interactions. When a transaction is “addressed” to a specific wallet, it is immutable and transparent. Unlike a traditional bank account, these addresses do not require a central intermediary to validate them; they are addressed via mathematical consensus.
This has massive implications for the “Tech” niche, as it changes how we perceive ownership and data transfer. Being “addressed” on a blockchain means your digital footprint is verified by a distributed ledger, providing a level of security and autonomy that was previously impossible.
Decentralized Identifiers (DIDs)
The next frontier is Decentralized Identifiers (DIDs). Current web addressing relies on URLs and centralized logins (like “Sign in with Google”). However, tech innovators are working on ways for users to be “addressed” through self-sovereign identities.
A DID is a new type of identifier that enables a verifiable, decentralized digital identity. It allows a person or a device to be “addressed” across different platforms without needing a central database. This technology addresses the growing concerns surrounding data privacy and centralized control, representing the next logical step in how we define “addressed” in a digital-first society.
Conclusion: The Multi-Faceted Definition of “Addressed”
In the tech industry, “addressed” is far more than a simple verb. It is a technical requirement for hardware communication, a protocol for global connectivity, a standard for software reliability, and a framework for future digital identity.
Whether we are discussing the microscopic pathways of a CPU’s memory bus, the global routing of data packets via IPv6, or the rigorous process of patching a critical security vulnerability, the concept remains the same: “addressed” signifies that a specific point of data or a specific problem has been identified, located, and successfully managed. As technology continues to advance into the realms of quantum computing and decentralized webs, the way we “address” our digital world will only become more complex, requiring even more precision and innovation from the professionals who build and maintain our modern infrastructure.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.