The phrase “jammed finger” conjures an immediate, visceral image: a digit bent at an unnatural angle, swollen, throbbing, and intensely painful. It’s a common, often sports-related injury, characterized by the forceful hyperextension or impact on an extended finger, forcing the joint beyond its normal range of motion. While the human body’s response to such trauma is remarkably consistent, the technological world, in its own intricate and interconnected way, experiences phenomena that can be described as analogous – systemic blockages, performance degradation, and unexpected failures that hinder optimal function. This article will explore the visual and symptomatic characteristics of a jammed finger, not just in its biological sense, but also by drawing parallels to how similar “jamming” or critical disruptions manifest within technological systems, and how technology itself aids in understanding and resolving both.

The Biological Jam: Visualizing and Understanding Finger Trauma
A jammed finger, medically termed a sprain of the interphalangeal joint, is primarily a soft tissue injury. The ligaments that stabilize the finger joints are stretched or torn. The visual cues are immediate and often dramatic, serving as clear indicators of the underlying damage. Understanding these visual markers is crucial for initial assessment and seeking appropriate care.
Swelling and Discoloration: The Body’s Inflammatory Response
The most prominent visual sign of a jammed finger is rapid and significant swelling. This is the body’s immediate and natural inflammatory response to injury. Blood vessels dilate to deliver immune cells and healing factors to the affected area, leading to fluid accumulation and distension of the tissues. The finger will appear noticeably larger than its uninjured counterpart, often making it difficult or impossible to wear rings.
Following the swelling, discoloration is a common, albeit delayed, symptom. Bruising, or ecchymosis, occurs when small blood vessels beneath the skin rupture, releasing blood into the surrounding tissues. This can manifest as shades of red, purple, blue, and eventually green or yellow as the blood is reabsorbed by the body. The extent and location of the discoloration can provide clues about the severity and precise area of ligament damage. A severe jamming injury might present with extensive bruising that spreads down the finger and even into the hand.
Deformity and Angulation: Obvious Signs of Joint Disruption
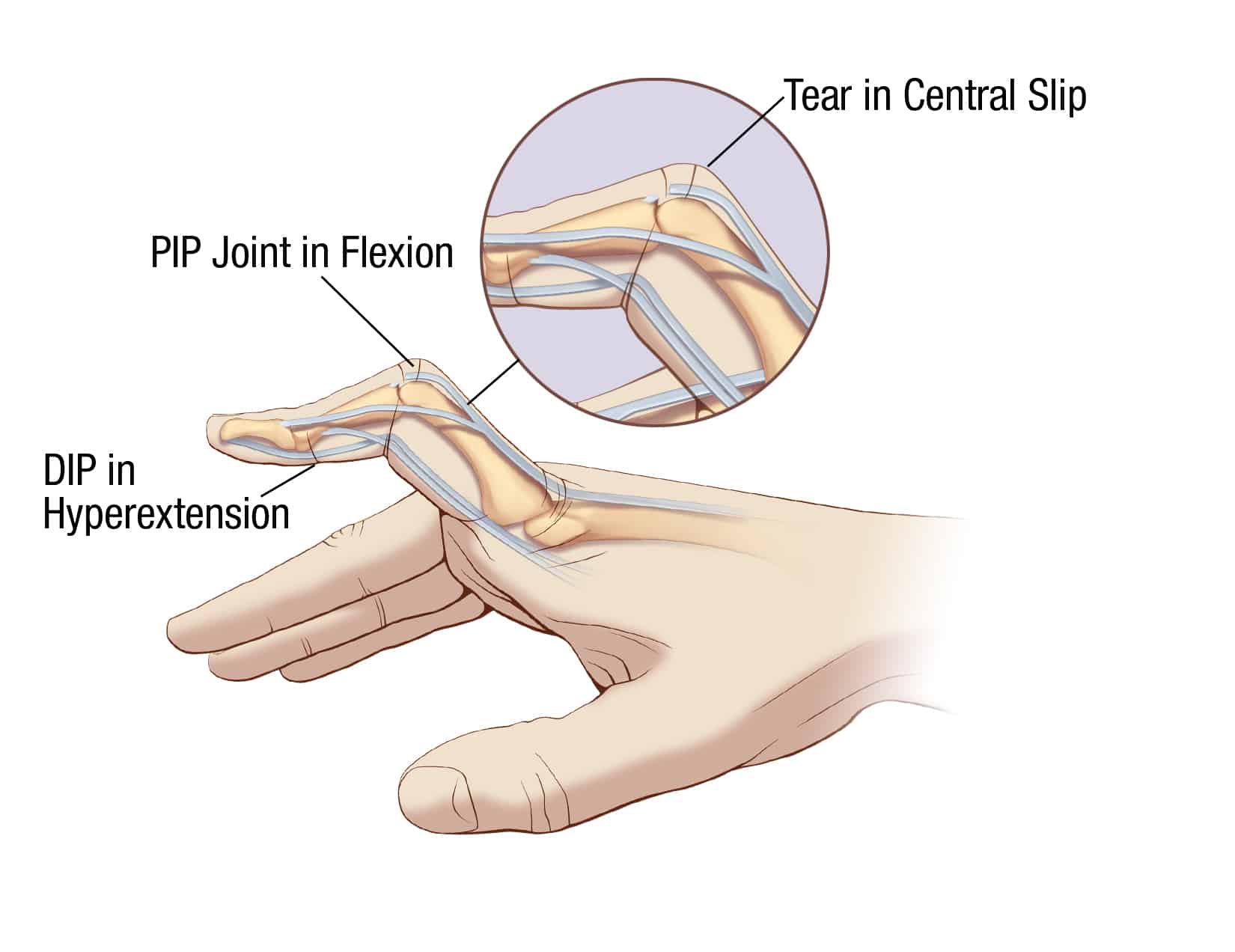
While not all jammed fingers result in visible deformity, a significant hyperextension or a complete tear of supporting ligaments can lead to a noticeable misalignment of the finger. The joint might appear bent at an unnatural angle, or the finger might droop in a way it wouldn’t in its healthy state. This angulation is a critical visual indicator, suggesting that the skeletal structure may be compromised or that the ligaments are no longer adequately stabilizing the joint. In severe cases, the finger might appear shorter or significantly out of proportion compared to the others.
The Painful Reality: Subjective Symptoms and Functional Impairment
Beyond the visible signs, the subjective experience of pain is paramount. A jammed finger is typically excruciatingly painful, especially when attempting to move the affected digit or apply any pressure. This pain is sharp and immediate upon impact, and can linger as a dull ache when at rest. The intensity of the pain often correlates with the severity of the ligamentous injury.
Functional impairment is also a defining characteristic. The ability to grip, grasp, or even make a fist is severely compromised. Everyday tasks that involve fine motor skills, such as typing, buttoning clothes, or using utensils, become incredibly difficult, if not impossible. The mere act of touching the injured finger can elicit a sharp, intense pain, further limiting its use.
Tech Analogies: Systemic Blockages and Performance Degradation
The concept of a “jammed finger” in the human body resonates with several critical issues within technological systems. When a complex system, whether it’s a software application, a network, or a sophisticated piece of hardware, experiences a disruption that halts or severely impedes its intended function, we can observe analogous symptoms of “jamming” or critical failure. Technology, in turn, provides sophisticated tools to diagnose, visualize, and rectify these digital “injuries.”
Software Bottlenecks and Crashes: The Digital “Pain”
In software development and IT operations, a “bottleneck” is a point of congestion in a system that limits its throughput. This is akin to the swelling and pain in a jammed finger, where the flow of essential resources (like blood) is impeded, causing discomfort and reduced function. Users might experience extreme slowdowns, unresponsiveness, or application crashes. These are the digital equivalents of the excruciating pain and inability to move a jammed digit.
Visualizing these bottlenecks often involves sophisticated monitoring tools. Performance dashboards, real-time metrics, and system logs act as our diagnostic “imaging” for software. For instance, a web application might show a spike in server response times, indicating a database query is taking too long, or a particular API call is failing repeatedly. These indicators, much like the swelling of a finger, point to an underlying issue that is causing a functional blockage. A full-blown application crash is the ultimate manifestation of a system “jam,” rendering it completely unusable, analogous to a severely fractured or dislocated finger.
Network Congestion and Packet Loss: The Digital “Discoloration”
Network infrastructure, the digital nervous system of our interconnected world, is also susceptible to “jamming.” Network congestion occurs when the demand for bandwidth exceeds the available capacity, leading to delays and dropped data packets. This is similar to how tissue damage in a jammed finger leads to impaired blood flow and subsequent swelling and discoloration.
Tools like network analyzers (e.g., Wireshark) and ping utilities allow IT professionals to “see” the effects of network congestion. Packet loss, where data packets fail to reach their destination, is a direct symptom. This can manifest as choppy audio or video, interrupted downloads, or websites failing to load completely. The “discoloration” in this context is the degradation of data integrity and timely delivery. Visualizations often show packet loss rates, latency spikes, and throughput degradation, providing a clear picture of where the digital “bruising” is occurring.
Hardware Malfunctions and Component Failures: The Physical “Deformity”
At a more fundamental level, hardware components can also “jam” or fail, leading to system-wide disruptions. A failing hard drive, a malfunctioning CPU, or a corrupted memory module can cripple an entire system. This is the technological equivalent of a severe physical deformity in a jammed finger, where the structural integrity is compromised, leading to a complete breakdown in function.
Diagnostic tools for hardware are diverse, ranging from BIOS diagnostics and SMART (Self-Monitoring, Analysis and Reporting Technology) status reports for drives, to thermal imaging for overheating components. A “beeping” code from a computer’s motherboard, much like a cry of pain, signals a critical hardware issue. Error logs will often point directly to the malfunctioning component, providing a clear indication of the “deformity” that is causing the system to jam.
Technological Solutions: Diagnosis, Prevention, and Remediation
Just as medical professionals use imaging techniques and diagnostic tests to understand and treat a jammed finger, technology offers a powerful suite of tools for identifying, analyzing, and resolving digital blockages. Furthermore, proactive technological measures can prevent many of these issues from occurring in the first place, mirroring preventative strategies in physical health.
Advanced Monitoring and Analytics: Seeing the Invisible
Modern IT operations rely heavily on sophisticated monitoring and analytics platforms. These tools provide real-time visibility into the health and performance of applications, networks, and infrastructure. They can detect anomalies, predict potential failures, and pinpoint the root cause of performance degradation. This is analogous to an X-ray or MRI revealing the extent of damage to bones and ligaments in a jammed finger.
For example, Application Performance Monitoring (APM) tools can track user requests from the browser all the way to the database, identifying which specific component is causing a slowdown. Network monitoring systems can map traffic flow and identify congested links. Log aggregation and analysis tools can sift through vast amounts of data to find recurring error patterns. These insights are invaluable in understanding the complex interplay of factors that can lead to a system “jam,” allowing for targeted remediation rather than guesswork.
Automation and Orchestration: The Digital “Physical Therapy”
Once a digital “injury” is diagnosed, automation and orchestration tools play a crucial role in remediation. Automated scripts can restart services, reallocate resources, or deploy patches to resolve issues quickly. Orchestration platforms can manage complex workflows to ensure that systems return to optimal functioning efficiently and reliably. This is akin to physical therapy after an injury, where guided exercises help restore function and prevent further damage.
For instance, in cloud environments, infrastructure-as-code tools allow for the automated provisioning and scaling of resources, ensuring that applications can handle traffic spikes without becoming congested. Automated failover mechanisms can quickly switch to backup systems if a primary component fails. This proactive and responsive approach minimizes downtime and maintains the “health” of digital systems, preventing minor issues from escalating into major blockages.
Cybersecurity: Protecting Against Malicious “Trauma”
While natural phenomena can cause system “jams,” malicious actors pose a significant threat, akin to a deliberate physical assault. Cybersecurity measures are essential for protecting digital systems from attacks that can intentionally cripple functionality, steal data, or cause widespread disruption. This is the digital equivalent of wearing protective gear to prevent injuries in sports.
Firewalls, intrusion detection systems, antivirus software, and robust access control mechanisms act as digital guardians. Regular security audits, vulnerability assessments, and employee training are crucial for building resilience. A cyberattack can cause a system to “jam” in a manner that is often more severe and targeted than natural performance degradation, highlighting the critical importance of comprehensive security strategies.
The Future of “Jam” Prevention: AI and Predictive Maintenance
The evolution of technology is leading us towards an era of increasingly proactive and intelligent system management. Artificial intelligence (AI) and machine learning (ML) are poised to revolutionize how we prevent and manage “jams” in technological systems. By analyzing vast datasets of system behavior, AI can identify subtle patterns and predict potential failures before they occur, offering a glimpse into a future where digital “injuries” are largely averted.
AI-Powered Predictive Maintenance: Forecasting Future Blockages
AI algorithms can learn the normal operational patterns of complex systems and flag deviations that might indicate an impending failure. This predictive maintenance approach allows for intervention before a system jams, significantly reducing downtime and the cost associated with emergency fixes. Imagine an AI that can forecast a hard drive failure weeks in advance based on subtle changes in its read/write patterns, or predict network congestion based on historical traffic data and scheduled events.
This is analogous to a doctor using advanced diagnostics to identify a potential health risk before symptoms become severe. AI can analyze sensor data, performance metrics, and historical logs to identify weak points, anticipate resource exhaustion, and recommend proactive measures. This shift from reactive to predictive management is a cornerstone of modern IT operations.

Self-Healing Systems: The Autonomous Resolution of Digital Ailments
The ultimate goal is the development of “self-healing” systems. These systems are designed to detect, diagnose, and automatically correct problems without human intervention. When a component fails or a performance issue arises, the system can autonomously reconfigure itself, reroute traffic, or restart services to maintain continuity. This represents the pinnacle of technological resilience, a far cry from the manual troubleshooting often required for a biological jammed finger.
Such systems leverage AI, automation, and sophisticated feedback loops. They are designed to be fault-tolerant and adaptable. While still under development and most prevalent in highly specialized environments, the trend towards greater autonomy in system management promises a future where critical digital infrastructure is less susceptible to the disruptive effects of “jamming,” ensuring the smooth and continuous flow of information and services in our increasingly connected world. The “what do a jammed finger look like” question, when viewed through this technological lens, reveals not just a biological injury, but a fundamental challenge of maintaining complex systems, a challenge that technology is increasingly equipped to address.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.