In an increasingly interconnected digital world, the phrase “network credentials” is heard frequently, yet its full scope and critical importance are often underestimated. At its core, a network credential is a set of information used to verify an individual’s or a system’s identity when attempting to access a digital resource, whether it’s a Wi-Fi network, an online banking portal, a corporate server, or a social media account. These credentials act as digital keys, granting access to a vast array of services, data, and opportunities that define our modern lives and economies. Without them, digital access is impossible; when compromised, our digital lives can unravel with alarming speed.
Understanding network credentials isn’t merely a technical exercise; it’s a fundamental aspect of digital literacy, personal security, and even financial well-being in the 21st century. From securing personal photographs on a cloud drive to protecting multi-million dollar business transactions, the integrity of these digital identifiers is paramount. This article will delve into what network credentials truly entail, explore their diverse forms, underscore their critical importance from a technological, branding, and financial perspective, and outline best practices for managing and securing them in an ever-evolving threat landscape.
The Core Concept: Understanding Network Credentials
At the heart of every digital interaction that requires access or authorization lies the concept of network credentials. They are the bedrock upon which digital trust is built, enabling systems to distinguish between legitimate users and unauthorized intruders.
A Digital Key to Your World
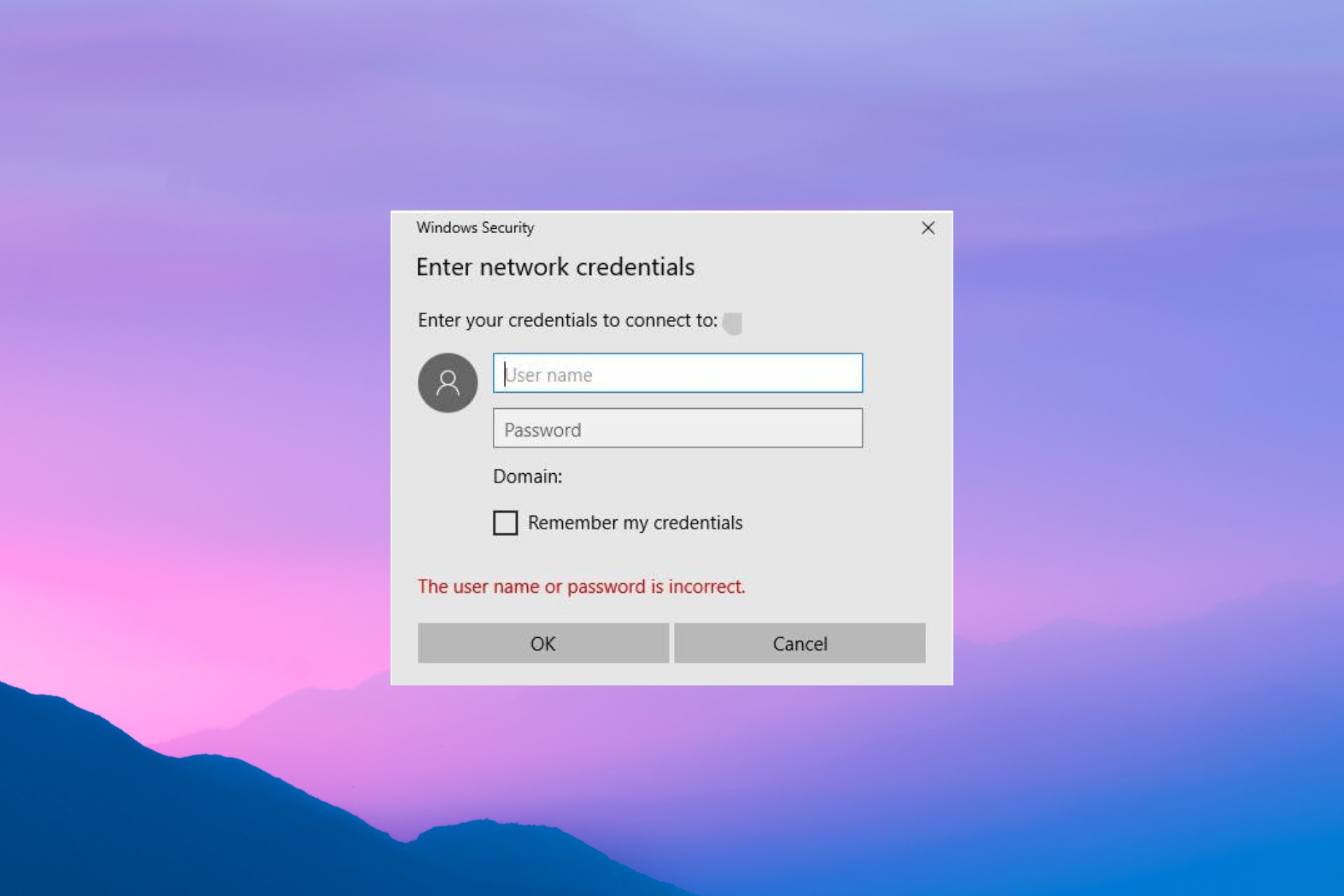
Think of network credentials as your digital fingerprint combined with a secret password – a unique identifier paired with a verification method that proves you are who you claim to be. Fundamentally, they are pieces of data used by authentication systems to confirm a user’s identity before granting access to a network, device, application, or specific data. While the most common form we encounter is a username and password combination, this definition has expanded significantly to include a myriad of other verification methods like security tokens, biometric data, digital certificates, and more.
These credentials are not just for humans; machines and software applications also use them to communicate securely. An application programming interface (API) key, for instance, allows one software application to securely interact with another, automating tasks and sharing data without human intervention. Regardless of the form they take, their purpose remains consistent: to establish and verify identity in the digital realm.
Why They Matter: Access and Authorization
The primary function of network credentials is two-fold: access and authorization.
- Access: This refers to the ability to get into a system, network, or service. When you enter your Wi-Fi password, you’re gaining access to your home network. When you log into your email, you’re gaining access to your inbox. Credentials are the gateway.
- Authorization: Once access is granted, authorization determines what you can do within that system. A system administrator might have full access and control over a server, while a standard user might only be able to view certain files. Your credentials don’t just let you in; they define your role and permissions within.
This distinction is crucial for maintaining security and control, especially in complex environments like corporate networks or cloud platforms where different users require varying levels of access to sensitive data and functionalities. Without robust credential systems, digital environments would be open to all, leading to chaos, data breaches, and a complete breakdown of trust.
The Ubiquity of Credentials
In today’s hyper-connected society, network credentials are omnipresent. They are woven into the fabric of our daily digital existence. Every time you:
- Connect to a public or private Wi-Fi network.
- Log into your email, social media, or online shopping accounts.
- Access your bank account or investment portfolio online.
- Unlock your smartphone or laptop.
- Use a company VPN to access internal resources.
- Sign into a streaming service or a gaming platform.
- Even install certain software or apps.
You are utilizing or being prompted for network credentials. Their ubiquity means that the security of these credentials is not just an IT concern; it’s a fundamental aspect of personal privacy, financial stability, and professional integrity in the digital age.
Diverse Types of Network Credentials
While the username and password remain the most recognized form, the landscape of network credentials has diversified significantly to meet evolving security challenges and technological advancements. Understanding these different types is crucial for appreciating the layers of protection available.
Traditional Username and Password Pairs
Still the most common form of authentication, a username (or email address) identifies the user, and a password acts as the secret proof of identity. They are ubiquitous, simple to understand, and easy to implement. However, their simplicity is also their biggest vulnerability. Weak passwords, reused passwords, and susceptibility to dictionary attacks or brute-force methods make them a prime target for cybercriminals. Despite their shortcomings, they remain a foundational element, often augmented by other security measures.
Multi-Factor Authentication (MFA) Tokens
MFA represents a significant leap forward in credential security. Instead of relying on “something you know” (the password) alone, MFA requires two or more distinct verification factors. These typically include:
- Something you know: Your password or PIN.
- Something you have: A physical device like a smartphone (for an SMS code or authenticator app), a hardware token (like a YubiKey), or a smart card.
- Something you are: Biometric data such as a fingerprint, facial scan, or iris scan.
When you log in and then receive a code on your phone, or are prompted to touch a fingerprint sensor, you’re engaging with MFA. This layered approach drastically reduces the risk of unauthorized access, even if your password is compromised, making it an essential tool for securing high-value accounts.
Digital Certificates and Keys
Digital certificates are electronic documents used to verify the ownership of a public key. Issued by trusted Certificate Authorities (CAs), they are foundational for secure communication over the internet, particularly with SSL/TLS (the “S” in HTTPS). They assure users that they are communicating with the authentic website or server, and not an imposter. Beyond websites, digital certificates are used for:
- VPNs: To authenticate users and devices to a secure private network.
- Email encryption: To secure email communications.
- Software signing: To verify the authenticity and integrity of software.
- Smart cards: Often used in corporate environments for secure login.
- SSH keys: Used for secure remote access to servers, offering a more robust alternative to passwords for command-line interfaces.
These credentials rely on cryptographic principles, offering a higher level of trust and security than simple password authentication.
API Keys and OAuth Tokens
For applications and services that need to interact programmatically, different types of credentials are used.
- API Keys: These are unique strings of characters used to authenticate a project or application when it makes requests to an API (Application Programming Interface). They identify the calling entity and control its access rights to the API’s functions. They are common in cloud services, payment gateways, and third-party integrations.
- OAuth Tokens: OAuth (Open Authorization) is an open standard for access delegation, commonly used as a way for internet users to grant websites or applications access to their information on other websites without giving them their passwords. For example, when you “Sign in with Google” or “Connect with Facebook,” you’re often using OAuth. It issues temporary tokens instead of sharing your actual credentials, enhancing security by limiting the scope and duration of access.
Biometric Data
Biometric credentials utilize unique biological characteristics for authentication. This includes:
- Fingerprint scans: Common on smartphones and laptops.
- Facial recognition: Used to unlock devices or authenticate transactions.
- Iris scans: Offering high accuracy, often seen in high-security environments.
- Voice recognition: Analyzing unique vocal patterns.
Biometrics offer convenience and can be highly secure, as they are “something you are” and generally cannot be forgotten, lost, or stolen in the traditional sense. However, they also raise privacy concerns and the irreversible nature of a biometric compromise necessitates robust storage and processing mechanisms.
The Critical Importance of Credential Security
The digital age has transformed how we live, work, and interact. With this transformation comes an increased reliance on network credentials, making their security not just a best practice, but a critical imperative for individuals, brands, and financial stability.
Protecting Your Digital Identity
Your network credentials are the gatekeepers to your digital identity. They protect your personal data, private communications, and online reputation. A compromised email account, for instance, can quickly lead to a domino effect, granting attackers access to linked services like social media, cloud storage, and even financial accounts through password reset options. This can result in:
- Privacy breaches: Exposure of personal photos, documents, and communications.
- Identity theft: Malicious actors impersonating you to open new accounts or commit fraud.
- Reputational damage (Brand): If your social media or professional networking accounts are hacked, malicious content could be posted under your name, severely damaging your personal brand and credibility. In the context of “Brand,” protecting these credentials is about safeguarding your digital self and how you are perceived online.
Safeguarding Financial Assets and Online Income

Perhaps one of the most immediate and tangible consequences of credential compromise relates to finance. Almost all financial transactions, investments, and online income streams today rely on secure network credentials.
- Bank accounts and credit cards: Compromised banking credentials can lead to direct financial loss, unauthorized transfers, and fraudulent transactions.
- Investment platforms: Access to brokerage accounts or cryptocurrency wallets can result in the theft of valuable assets.
- Online income and side hustles (Money): For freelancers, e-commerce entrepreneurs, or those relying on online platforms for income, a breach of credentials for payment processors, marketplace accounts, or business banking can cripple operations, lead to lost income, and even deplete funds earned through “Online Income” and “Side Hustles.” In the realm of “Money,” robust credential security is the frontline defense against financial ruin in the digital sphere.
Ensuring Business Continuity and Data Integrity
For businesses, the stakes are even higher. Corporate network credentials protect not only employee data but also intellectual property, customer databases, strategic plans, and operational control systems.
- Data breaches: A single compromised employee credential can open the door to a large-scale data breach, leading to regulatory fines, legal liabilities, loss of customer trust, and severe reputational damage (Brand).
- Operational disruption: Attacks like ransomware, often initiated through credential compromise, can cripple an organization’s IT infrastructure, halting operations, causing significant financial losses, and impacting the company’s ability to serve its customers. This directly impacts “Business Finance” and overall business health.
- Competitive advantage: Sensitive corporate data, if stolen, can be used by competitors or sold on the dark web, undermining a company’s market position. Protecting credentials is therefore crucial for maintaining the “Brand” and competitive edge of a business.
Preventing Cyberattacks
Weak or compromised credentials are the most common entry point for a vast array of cyberattacks. Understanding these threats underscores the importance of strong security:
- Phishing: Social engineering attacks trick users into divulging credentials on fake websites or through malicious emails.
- Brute-force attacks: Automated attempts to guess passwords by trying numerous combinations.
- Credential stuffing: Using lists of stolen usernames and passwords (from one breach) to try and log into other services, exploiting password reuse.
- Man-in-the-Middle (MITM) attacks: Intercepting communication between a user and a service to steal credentials or data.
- Malware: Keyloggers and spyware can record keystrokes or steal stored credentials from infected devices.
Robust credential security, empowered by “Digital Security” principles (Tech), is the primary barrier against these pervasive threats, shielding individuals and organizations from their damaging consequences.
Best Practices for Managing and Securing Your Credentials
Given the paramount importance of network credentials, adopting proactive and diligent security practices is non-negotiable. These measures are crucial for everyone, from individual users to large enterprises, to safeguard their digital assets.
Cultivating Strong Credential Habits
The foundation of good credential security lies in creating and managing strong passwords and passphrases.
- Unique and Complex: Every account should have a unique password. Never reuse passwords across different services. Passwords should be long (ideally 12-16 characters or more), complex combinations of uppercase and lowercase letters, numbers, and symbols. Passphrases, which are long strings of unrelated words, can be easier to remember and even more secure.
- Password Managers: These tools (e.g., LastPass, 1Password, Bitwarden) generate, store, and auto-fill strong, unique passwords for all your accounts, encrypted under a single master password. They are indispensable for achieving true password hygiene without the burden of memorization.
- Regular Updates: While password managers handle much of this, it’s good practice to change critical passwords periodically, especially for high-value accounts, and immediately if there’s any suspicion of a breach.
- Avoid Physical Notes: Resist the temptation to write down passwords on sticky notes near your computer or in easily accessible files. If you must record them, use a secure, encrypted method.
Embracing Multi-Factor Authentication (MFA) Everywhere
MFA is no longer an optional security enhancement; it’s a fundamental requirement.
- Enable MFA for All Accounts: Activate MFA on every service that offers it, especially for email, banking, social media, and any “Online Income” or “Business Finance” related platforms.
- Prioritize Strong MFA Methods: While SMS-based MFA is better than nothing, authenticator apps (e.g., Google Authenticator, Authy) or hardware security keys (e.g., YubiKey) offer superior protection as they are less susceptible to interception than SMS.
- Educate Others: Encourage family members, friends, and colleagues to adopt MFA.
Recognizing and Avoiding Phishing Attempts
Phishing is a leading cause of credential compromise. Vigilance and education are key.
- Scrutinize Emails and Messages: Always check the sender’s email address, look for grammatical errors, generic greetings, and suspicious links. Hover over links to see the actual URL before clicking.
- Be Wary of Urgency: Phishing attempts often create a sense of urgency or fear to pressure you into acting without thinking.
- Verify Independently: If you receive a suspicious request from a known entity (e.g., your bank, a service provider), contact them directly using official channels (their website, a known phone number) rather than replying to the suspicious message.
- Report Suspicious Activity: Reporting phishing attempts helps protect others and improves overall “Digital Security.”
Secure Network Practices
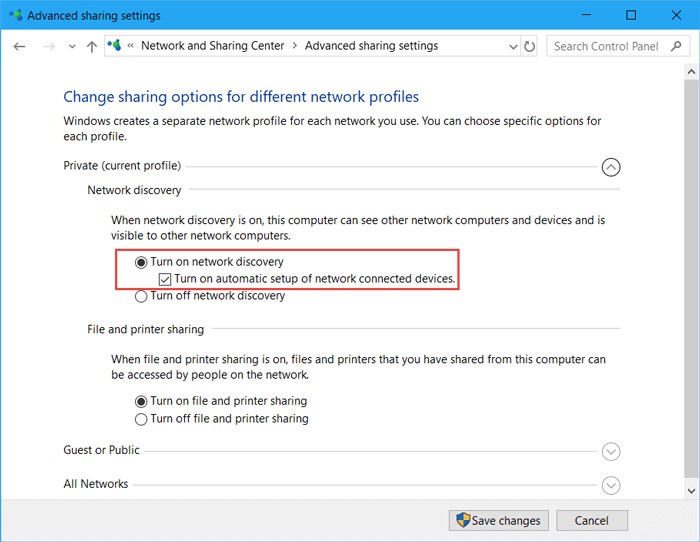
How you connect to networks also impacts your credential security.
- Use VPNs on Public Wi-Fi: Public Wi-Fi networks are often unsecured, making it easy for attackers to intercept your data, including credentials. A Virtual Private Network (VPN) encrypts your internet traffic, providing a secure tunnel.
- Keep Software Updated: Operating systems, web browsers, and all software should be kept up-to-date. Updates often include critical security patches that fix vulnerabilities exploited by attackers to steal credentials or gain access.
- Understand Network Security Protocols: For businesses, implementing strong network access control, segmenting networks, and using secure protocols (like WPA3 for Wi-Fi) are essential to prevent unauthorized access.
Monitoring Your Digital Footprint
Proactive monitoring can alert you to potential breaches before they cause significant damage.
- Check for Data Breaches: Utilize services like HaveIBeenPwned.com to check if your email addresses or phone numbers have been part of known data breaches. If so, immediately change passwords for affected accounts.
- Review Account Activity: Regularly check your bank statements, credit card reports, and online account activity logs for any suspicious or unauthorized transactions or logins.
- Set Up Alerts: Many services offer alerts for suspicious login attempts or changes to account settings. Enable these whenever possible.
Implementing Zero Trust Principles (for businesses/advanced users)
For organizations, moving towards a Zero Trust security model can profoundly enhance credential security. This principle dictates “never trust, always verify.” It means:
- Verify Every Access Attempt: Assume every user and device, whether inside or outside the network perimeter, is untrusted until explicitly verified.
- Least Privilege Access: Grant users only the minimum access rights necessary to perform their job functions.
- Continuous Verification: Authentication and authorization are not one-time events but continuous processes, adapting to changes in context or risk.
These practices, taken together, form a robust defense against the sophisticated threats targeting network credentials, bolstering personal “Digital Security” and protecting “Brand” reputation and “Money” from illicit access.
The Future of Network Credentials
The quest for more secure, convenient, and user-friendly authentication methods is ongoing. As technology evolves and cyber threats become more sophisticated, the landscape of network credentials is set to undergo significant transformation.
Passwordless Authentication
The eventual demise of the traditional password has long been predicted, and we are now seeing concrete steps towards passwordless authentication. This paradigm shift aims to eliminate the vulnerabilities associated with passwords while enhancing user experience.
- Biometrics (Enhanced): Beyond simple fingerprint or face scans, advanced biometrics like behavioral biometrics (analyzing typing patterns, mouse movements, gait) or vein patterns are emerging.
- FIDO Alliance and WebAuthn: The Fast IDentity Online (FIDO) Alliance is developing open standards for passwordless authentication, with WebAuthn being a core component. This allows users to authenticate using cryptographic keys stored securely on their devices (e.g., via a hardware security key or the device’s built-in authenticator), eliminating the need for shared secrets (passwords).
- Magic Links and One-Time Passcodes (OTPs): While not entirely new, their integration into seamless login flows is becoming more sophisticated, allowing users to log in by clicking a unique, temporary link sent to their verified email or phone, or by entering an OTP from an authenticator app.
Decentralized Identity
Blockchain technology and distributed ledger technologies are paving the way for decentralized identity systems, also known as self-sovereign identity (SSI).
- User Control: In SSI models, individuals own and control their digital identities, rather than relying on centralized entities (like social media companies or governments) to store and manage their data.
- Verifiable Credentials: Users can present verifiable digital credentials (e.g., a digital driver’s license, academic degree, or employment verification) directly from their digital wallet to services that require them, without exposing unnecessary personal information. This promises enhanced privacy and security by reducing the risk of large-scale data breaches associated with centralized identity providers.
AI and Behavioral Biometrics
Artificial intelligence and machine learning are increasingly being integrated into authentication systems to provide a continuous and adaptive layer of security.
- Continuous Authentication: Instead of authenticating only at login, AI can continuously monitor user behavior (e.g., typing speed, cursor movements, device location, typical usage patterns) to detect anomalies that might indicate an unauthorized user. If suspicious activity is detected, it can trigger additional authentication challenges or lock the account.
- Risk-Based Authentication: AI can assess the risk of a login attempt in real-time based on various contextual factors (e.g., new device, unusual location, time of day) and dynamically adjust the authentication requirements accordingly. A low-risk login might require only a password, while a high-risk one could demand multiple MFA factors.
These future developments promise a more secure and seamless digital experience, moving beyond the vulnerabilities of traditional passwords while adapting to the complexity of our increasingly digital lives.
Conclusion
Network credentials are the invisible threads that weave together our digital existence, granting us access to the vast opportunities and resources of the modern internet. From connecting to your home Wi-Fi to securing complex financial transactions and managing a global brand, their role is undeniably central. They are the frontline defense for your personal privacy, financial well-being, and professional integrity in an era defined by digital interaction.
Understanding what network credentials are, recognizing their diverse forms, and appreciating their critical importance from technological, branding, and monetary perspectives is no longer optional; it is fundamental to navigating the digital world safely and productively. By diligently adopting best practices—cultivating strong password habits, embracing Multi-Factor Authentication universally, staying vigilant against phishing, and maintaining secure network hygiene—we empower ourselves to protect our digital identities.
As we look to the future, the evolution towards passwordless and decentralized authentication, augmented by AI and behavioral biometrics, promises even greater security and convenience. Yet, regardless of the technological advancements, the core responsibility remains with the user. Our commitment to securing our network credentials today will define the safety and resilience of our digital tomorrow. In a world where technology converges with personal finance and brand reputation, mastering credential security is truly mastering the keys to the kingdom.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.