The advent of blockchain technology has ushered in a new era of digital innovation, with cryptocurrency at its forefront. More than just a digital asset, a cryptocurrency represents a fundamental shift in how value is exchanged, stored, and managed, built upon principles of decentralization, transparency, and immutability. For aspiring innovators, developers, or entrepreneurs looking to contribute to this evolving landscape, the idea of creating one’s own cryptocurrency is both fascinating and challenging. This guide delves exclusively into the technical blueprint of making cryptocurrency, exploring the underlying technologies, development methodologies, and crucial considerations that underpin its creation. From understanding the core principles of blockchain to deploying a functional token, we will navigate the intricate technical journey required to bring a digital currency to life.
Understanding the Blockchain Foundation
At its heart, every cryptocurrency is inextricably linked to blockchain technology. To truly “make” a cryptocurrency, one must first grasp the foundational concepts that enable its existence and operation.
What is a Blockchain?
A blockchain is a decentralized, distributed ledger technology (DLT) that records transactions across many computers. Each “block” in the chain contains a list of transactions, and once a block is completed, it is added to the chain, becoming an immutable part of the ledger. This immutability is guaranteed by cryptographic hashing; each block contains a hash of the previous block, creating a secure, chronological link. If any data in an earlier block is altered, its hash changes, invalidating all subsequent blocks and making tampering evident. This distributed nature means there is no central authority, and all participants in the network maintain a copy of the ledger, enhancing transparency and resistance to censorship. Public blockchains, like those supporting Bitcoin and Ethereum, are open to anyone to view and participate, while private or permissioned blockchains restrict access to a select group, often used for enterprise applications.
Consensus Mechanisms
For a decentralized network to function without a central authority, a mechanism is needed to agree on the state of the ledger and validate new transactions. This is where consensus mechanisms come into play. They are algorithms that enable all nodes in a distributed system to agree on a single source of truth, ensuring the integrity and security of the blockchain.
- Proof of Work (PoW): Pioneered by Bitcoin, PoW requires “miners” to solve complex cryptographic puzzles to add new blocks to the chain. The first miner to solve the puzzle broadcasts the solution, and if validated by other nodes, they earn a reward (newly minted cryptocurrency and transaction fees). PoW is highly secure but energy-intensive and can suffer from scalability issues.
- Proof of Stake (PoS): PoS is an alternative where validators are chosen to create new blocks based on the amount of cryptocurrency they “stake” as collateral. The more a validator stakes, the higher their chance of being selected. PoS is significantly more energy-efficient and often offers better scalability than PoW. Ethereum’s transition to PoS with “The Merge” is a prominent example.
- Delegated Proof of Stake (DPoS): In DPoS, token holders vote for a set of “delegates” or “witnesses” who are responsible for validating transactions and producing blocks. This system offers faster transaction speeds and improved scalability compared to PoW and sometimes PoS, but it can lead to a more centralized governance structure as power is concentrated among a smaller number of delegates.
The choice of consensus mechanism profoundly impacts a cryptocurrency’s security, scalability, and decentralization – a critical technical decision for any new project.
Smart Contracts and Programmability
Beyond simple value transfer, many modern cryptocurrencies leverage smart contracts. These are self-executing contracts with the terms of the agreement directly written into lines of code. They run on the blockchain, executing automatically when predefined conditions are met, eliminating the need for intermediaries. Ethereum was the first major platform to popularize smart contracts, enabling developers to build decentralized applications (dApps) and various types of tokens.
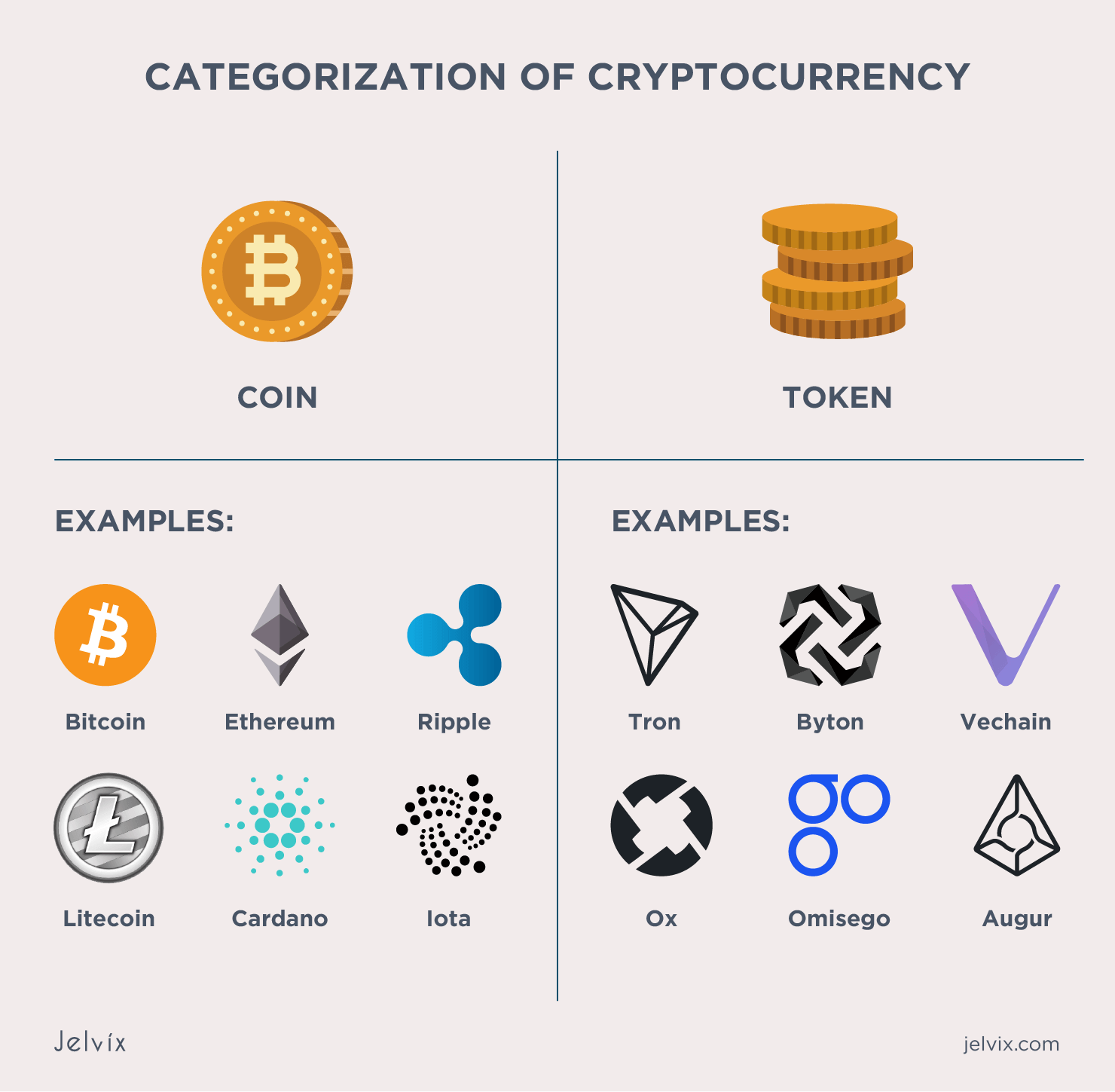
Smart contracts are essential for creating fungible tokens (like ERC-20 on Ethereum) that represent a currency, utility, or governance right, and non-fungible tokens (NFTs like ERC-721 or ERC-1155) that represent unique digital assets. Languages like Solidity (for Ethereum Virtual Machine-compatible chains), Rust (for Solana), and others are used to write these contracts. The ability to program logic directly onto a blockchain significantly expands the utility and complexity of what a cryptocurrency can achieve.
Choosing Your Path: Building from Scratch vs. Leveraging Existing Platforms
When embarking on the journey to create a cryptocurrency, one of the first and most critical technical decisions is whether to build an entirely new blockchain from the ground up or to deploy a token on an existing blockchain platform. Each approach presents distinct technical challenges, resource requirements, and benefits.
Developing Your Own Blockchain (Layer 1)
This is the most ambitious and resource-intensive path, akin to creating an entirely new operating system. Building a Layer 1 blockchain means designing and implementing every component of the network: the consensus mechanism, networking protocols, data structures, cryptographic primitives, and virtual machine (if smart contracts are desired).
Technical Requirements: This path demands profound expertise in cryptography, distributed systems, network engineering, and low-level programming languages such as C++, Go, Rust, or Python. A substantial team of highly specialized developers, researchers, and security experts is typically required.
Advantages: Full autonomy and control over the entire protocol. This allows for bespoke features, optimized performance for specific use cases, and the ability to innovate at the foundational level without being constrained by an existing network’s limitations or governance. Projects like Bitcoin, Ethereum, and Solana are examples of custom-built Layer 1 blockchains.
Disadvantages: Enormous development cost and time, significant technical complexity, and the formidable challenge of bootstrapping a secure and decentralized network from scratch. Attracting miners/validators and users to a new, unproven network requires substantial effort and resources to achieve a robust network effect and security.
Creating a Token on an Existing Blockchain (Layer 2/DApps)
For most aspiring cryptocurrency creators, leveraging an existing, robust blockchain platform is the more practical and accessible route. This involves deploying a smart contract that defines your token’s rules on a established Layer 1 blockchain, effectively creating a Layer 2 application or token.
Popular Platforms: Ethereum, Binance Smart Chain (BSC), Polygon, Solana, Avalanche, and Cardano are leading platforms that offer smart contract functionality. These platforms provide a battle-tested infrastructure, security model, and a large developer community.
Token Standards: These platforms adhere to specific token standards. For instance, on Ethereum and EVM-compatible chains (like BSC, Polygon), the ERC-20 standard is used for fungible tokens (currencies, utility tokens), while ERC-721 and ERC-1155 are used for non-fungible tokens (NFTs). Solana has its SPL Token Standard. Adhering to these standards ensures compatibility with wallets, exchanges, and other dApps.
Process: The typical process involves writing a smart contract (e.g., in Solidity for EVM chains) that specifies the token’s name, symbol, total supply, and rules for transfer, approval, and burning. This contract is then compiled and deployed to the chosen blockchain network using development tools.
Advantages: Significantly lower technical barrier and development cost. Inherits the security and network effects of the underlying blockchain. Faster time to market. Access to a vast ecosystem of tools, wallets, and exchanges.
Disadvantages: Dependence on the underlying blockchain’s performance, scalability, and security. Limited control over the core protocol and subject to its gas fees and network congestion.
Using Blockchain-as-a-Service (BaaS) Platforms
BaaS platforms offer managed blockchain solutions, primarily targeted at enterprises and for building private or consortium blockchains. These services abstract away much of the underlying infrastructure management, allowing users to focus on application development.
Examples: AWS Blockchain, Azure Blockchain Workbench, IBM Blockchain Platform.
Advantages: Rapid deployment, reduced operational overhead, managed infrastructure, and often integration with other cloud services. This can be ideal for proofs-of-concept or private blockchain applications.
Disadvantages: Often entails less decentralization (as the infrastructure is managed by a single provider), potential vendor lock-in, and limited customization options for public, permissionless cryptocurrency creation. While useful for specific enterprise applications, it’s generally not the go-to for launching a truly decentralized, public cryptocurrency in the vein of Bitcoin or Ethereum tokens.

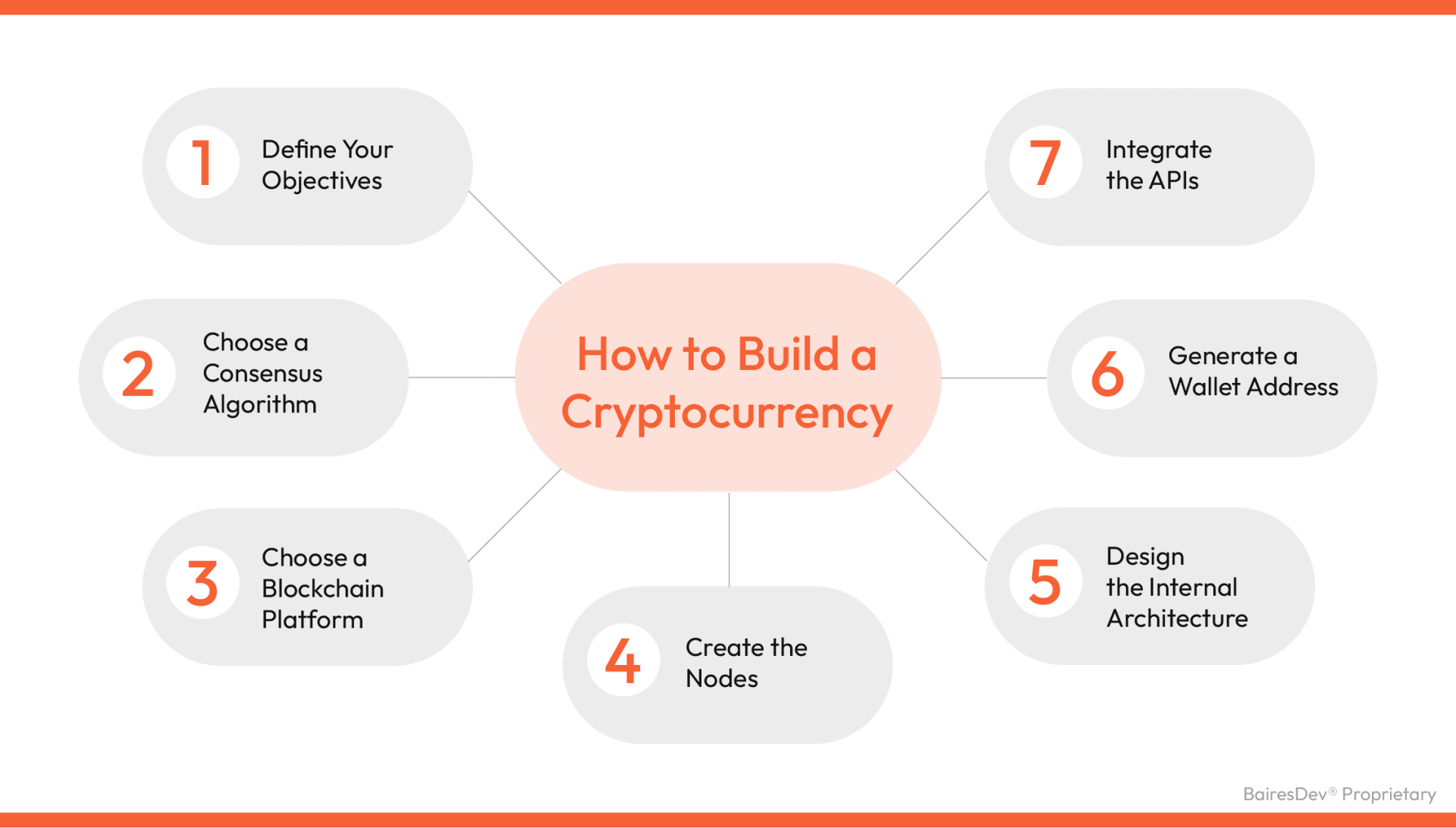
The Technical Steps to Crafting Your Cryptocurrency (Token Example)
Given that creating a token on an existing blockchain is the most common and practical approach for most projects, we will outline the detailed technical steps involved, focusing on an EVM-compatible chain (e.g., Ethereum, Binance Smart Chain, Polygon) using the ERC-20 standard as an illustrative example.
Define Your Tokenomics and Purpose
Before writing a single line of code, it’s paramount to define the fundamental technical specifications and utility of your cryptocurrency.
- Purpose/Utility: What problem does it solve? Is it a governance token, a utility token for a dApp, a stablecoin, or something else? This drives all other technical decisions.
- Token Name & Symbol: Human-readable name (e.g., “My Awesome Coin”) and a short ticker symbol (e.g., “MAC”).
- Total Supply: The maximum number of tokens that will ever exist. This can be fixed, inflationary, or deflationary (with burn mechanisms).
- Decimals: The number of decimal places the token can be divided into (e.g., 18 for Ethereum-based tokens, similar to how 1 BTC has 8 decimals). This impacts precision and user experience.
- Distribution Mechanism: How will tokens be initially allocated? (e.g., pre-mined, distributed via an Initial Coin Offering (ICO), airdrops, staking rewards). While distribution itself has economic implications, the mechanism (e.g., smart contract logic for airdrops) is a technical implementation.
Smart Contract Development
This is the core technical phase where your token’s logic is coded.
- Language Selection: For EVM-compatible chains, Solidity is the primary language. For Solana, Rust is used.
- Leverage Standards & Libraries: Do not reinvent the wheel. Utilize well-audited, open-source libraries like OpenZeppelin Contracts. OpenZeppelin provides secure, modular, and battle-tested implementations of ERC-20, ERC-721, and other standards. This drastically reduces development time and mitigates common vulnerabilities.
- Basic ERC-20 Contract Structure: A minimal ERC-20 contract defines functions for:
totalSupply(): Returns the total number of tokens in existence.balanceOf(address account): Returns the account balance of the owner.transfer(address recipient, uint256 amount): Transfersamounttokens from the caller’s account torecipient.approve(address spender, uint256 amount): Allowsspenderto withdrawamounttokens from the caller’s account.allowance(address owner, address spender): Returns the amount thatspenderis allowed to withdraw fromowner.transferFrom(address sender, address recipient, uint256 amount): Transfersamounttokens fromsendertorecipient, using thespender‘s allowance.- Events for
TransferandApprovalmust also be emitted for proper blockchain indexing and front-end interaction.
- Custom Logic: Beyond the basic ERC-20, you might add custom features like burning mechanisms, pausing transfers (in emergencies), or roles (minter, pauser) if your tokenomics require them. Implement these carefully and ensure they don’t introduce vulnerabilities.
Auditing and Testing
Security is paramount in blockchain. A single bug in a smart contract can lead to irreversible loss of funds.
- Unit Testing: Write comprehensive unit tests for your smart contract functions using frameworks like Hardhat or Truffle (for Solidity). Test every possible scenario, including edge cases, successful transactions, and expected failures.
- Vulnerability Scanning: Use static analysis tools (e.g., Slither) to automatically detect common vulnerabilities like reentrancy, integer overflows/underflows, and access control issues.
- Professional Security Audit: It is highly recommended to engage a reputable third-party blockchain security firm to conduct a thorough audit of your smart contract code. Auditors review the code for vulnerabilities, adherence to best practices, and overall robustness. This step is critical before deploying to a mainnet.
Deployment to the Blockchain
Once your smart contract is developed, tested, and audited, it’s ready for deployment.
- Testnet Deployment: Always deploy to a testnet (e.g., Goerli for Ethereum, BSC Testnet) first. This allows you to test the contract in a live blockchain environment without incurring real costs or risking real assets. You’ll need “testnet gas” (faucet tokens) for this.
- Mainnet Deployment: After successful testnet deployment and thorough testing, deploy to the mainnet of your chosen blockchain. You will need native cryptocurrency (e.g., ETH for Ethereum, BNB for BSC) in your wallet to pay for gas fees associated with the deployment transaction.
- Tools: Development environments like Remix (web-based IDE), Hardhat, or Truffle provide commands and interfaces to compile and deploy your contracts. You’ll typically use a wallet like MetaMask connected to your chosen network to sign the deployment transaction.
Listing and Integration (Post-Deployment)
After deployment, your token exists on the blockchain, but it needs integration to be usable.
- Block Explorer Integration: Your token will automatically appear on block explorers (e.g., Etherscan, BscScan) once deployed. You can often “verify” your contract code on these explorers, allowing others to view and interact with your contract with confidence.
- Wallet Integration: Many wallets will automatically recognize standard tokens once you input the contract address. However, ensure compatibility and provide clear instructions for users to add your token to their wallets.
- Decentralized Exchanges (DEXs): For your token to be tradable, you’ll likely want to provide liquidity on a Decentralized Exchange (DEX) like Uniswap or PancakeSwap. This involves creating a liquidity pool (e.g., your token/WETH pair) and providing initial liquidity via a smart contract. This is a technical interaction with existing DEX protocols.
Technical Considerations and Best Practices
Creating a cryptocurrency is an ongoing technical commitment that requires continuous attention to security, performance, and adaptability.
Security Imperatives
Beyond initial auditing, security is a continuous process.
- Ongoing Monitoring: Implement monitoring tools to detect unusual activity or potential exploits.
- Multi-Sig Wallets: For treasury management or critical contract upgrades, use multi-signature (multi-sig) wallets that require multiple private keys to authorize transactions, significantly reducing the risk of single points of failure or insider threats.
- Bug Bounty Programs: Consider running a bug bounty program to incentivize ethical hackers to discover and report vulnerabilities before malicious actors exploit them.
- Crisis Management Plan: Have a technical plan in place for responding to security incidents, including pausing functionalities if necessary (if designed into the contract).
Scalability and Performance
As your cryptocurrency gains adoption, its ability to handle transaction volume and maintain low latency becomes critical.
- Layer 2 Scaling Solutions: If your token is on a congested Layer 1 (like Ethereum), explore Layer 2 scaling solutions (e.g., Optimistic Rollups, ZK-Rollups, sidechains) that can process transactions off-chain while still leveraging the Layer 1’s security. Integrating with these involves technical bridging solutions.
- Blockchain Design Choices: If building a custom Layer 1, scalability must be designed into the architecture from the outset, considering factors like block size, block time, and sharding.
Decentralization vs. Centralization Trade-offs
The degree of decentralization chosen has profound technical implications.
- Centralized Components: Features like an
ownerrole in a smart contract or a pause function introduce a degree of centralization. While useful for rapid bug fixes or emergency responses, they also present potential points of control or censorship. - Governance: For a truly decentralized cryptocurrency, technical mechanisms for community governance (e.g., on-chain voting via smart contracts) must be implemented, allowing token holders to propose and vote on protocol upgrades or changes.
- Node Distribution: For a custom blockchain, the technical design should encourage a wide distribution of nodes/validators to prevent single points of failure and enhance censorship resistance.
Long-Term Maintainability and Upgradability
Blockchain technology evolves rapidly, and your cryptocurrency’s smart contracts may need updates or bug fixes.
- Upgradable Contracts: Standard smart contracts are immutable once deployed. To allow for future updates, implement proxy patterns (e.g., using OpenZeppelin’s Upgradable Contracts) which allow the logic contract to be swapped out while maintaining the same contract address and state. This is a complex technical pattern requiring careful implementation.
- Documentation: Maintain thorough technical documentation for your smart contracts, architecture, and deployment procedures.
- Community and Open-Source: Engage with the developer community, contribute to open-source projects, and foster a technical ecosystem around your cryptocurrency for long-term support and innovation.
Conclusion
Creating a cryptocurrency is a demanding yet immensely rewarding technical endeavor. It requires a deep understanding of blockchain fundamentals, meticulous smart contract development, rigorous testing, and an unwavering commitment to security. Whether opting for the monumental task of building a new Layer 1 blockchain or the more accessible route of deploying a token on an existing platform, the journey is one fraught with technical challenges that demand precision, expertise, and foresight. By adhering to best practices, leveraging existing standards, and continuously prioritizing robust technical design and security, developers can successfully contribute to the decentralized future by crafting their own impactful digital currencies. The future of finance and technology is being built, one line of code at a time.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.