In the dynamic landscape of technology, the pursuit of knowledge in cybersecurity and ethical hacking has never been more critical. As digital threats evolve at an alarming pace, understanding the tools and techniques used by both defenders and attackers is paramount. Kali Linux stands as a cornerstone in this domain, a powerful, Debian-derived operating system specifically designed for digital forensics and penetration testing. Whether you’re an aspiring cybersecurity professional, a seasoned IT administrator looking to bolster your security posture, or simply a tech enthusiast eager to explore the intricacies of network security, learning how to install Kali Linux is your essential first step.
This comprehensive guide, rooted in the foundational knowledge of Kali’s installation process and contextualized within the broader themes of Technology, Brand, and Money, will walk you through every stage of setting up this indispensable security toolkit. We’ll explore not just the “how-to” of installation, but also the strategic advantages it offers, its impact on your personal and professional brand, and the potential financial implications of mastering its capabilities.
Understanding the Foundation: Why Kali Linux?
Before diving into the installation process, it’s crucial to understand why Kali Linux is the chosen platform for so many in the cybersecurity field. Its extensive repository of pre-installed tools, meticulously curated for a wide range of security tasks, sets it apart. From network scanning and vulnerability analysis to password cracking and web application security testing, Kali provides an all-in-one solution for security professionals.
The Tech Advantage: A Toolkit for Digital Defenders and Explorers
From a Technology perspective, Kali Linux is an epitome of focused innovation. Its design philosophy prioritizes functionality for security professionals.
- Pre-installed Security Tools: Kali doesn’t require you to hunt down and manually install dozens of individual security applications. It comes packed with hundreds of the most advanced and widely recognized security tools available. This includes giants like Metasploit Framework, Nmap, Wireshark, Aircrack-ng, Burp Suite, and John the Ripper, among many others. This immediate access significantly accelerates the learning curve and practical application of ethical hacking techniques.
- Customization and Flexibility: While it comes with a comprehensive suite, Kali is also highly customizable. You can add or remove tools based on your specific needs, making it a lean and efficient operating system tailored to your workflow. This adaptability is crucial in the ever-evolving tech landscape where new tools and techniques emerge constantly.
- Debian Base: Built upon the robust and stable Debian Linux distribution, Kali benefits from a solid foundation, extensive community support, and a vast software repository beyond just security tools. This means you can use Kali for everyday computing tasks as well, although its primary focus remains on security.
- Open Source and Community Driven: As an open-source project, Kali Linux is transparent and constantly improved by a dedicated community of developers and users. This ensures that the operating system remains up-to-date with the latest security patches and technological advancements.
Building Your Brand in Cybersecurity
Mastering Kali Linux can significantly impact your Brand. In the realm of cybersecurity, a strong personal brand is often built on demonstrable skills and expertise.
- Demonstrating Technical Prowess: Proficiency with Kali Linux signals a deep understanding of network security principles, vulnerability assessment, and penetration testing methodologies. This is a highly sought-after skill set.
- Professional Credibility: Listing Kali Linux expertise on your resume or LinkedIn profile can immediately elevate your professional credibility. It’s a clear indicator that you are serious about cybersecurity and have hands-on experience with industry-standard tools.
- Networking Opportunities: Being knowledgeable about Kali can open doors to networking opportunities within the cybersecurity community. Attending conferences, participating in online forums, and engaging in discussions about security tools often revolve around platforms like Kali.
- Personal Branding in a Competitive Market: In a competitive job market, a specialized skill like Kali Linux mastery can help you stand out. It allows you to carve out a niche and position yourself as an expert in a critical area of technology.
The Financial Investment and Returns
The impact of Kali Linux extends to the Money aspect, both in terms of potential investment and significant returns.
- Cost-Effectiveness: Kali Linux itself is free and open-source. This eliminates the significant licensing costs associated with many commercial security suites, making it an accessible tool for individuals and organizations of all sizes.
- Skill Development for Higher Earning Potential: Acquiring proficiency in Kali Linux can directly translate into increased earning potential. Cybersecurity professionals are in high demand, and specialized skills command premium salaries. Roles such as penetration tester, security analyst, and ethical hacker are well-compensated.
- Business Opportunities: For entrepreneurs and small businesses, a deep understanding of Kali Linux can lead to the development of new services. Offering penetration testing, security audits, or customized security solutions can create lucrative revenue streams.
- Protecting Your Assets: For existing businesses, investing time in learning Kali can prevent costly data breaches and security incidents, directly saving money by safeguarding intellectual property, customer data, and operational continuity.
Preparing for Installation: What You’ll Need
Before you begin the installation process, ensure you have the necessary prerequisites. This preparation is akin to gathering the right tools and resources before embarking on any significant project, whether it’s a technical endeavor, a branding campaign, or a financial venture.
Hardware and Software Requirements
- System Requirements: Kali Linux can be installed on a variety of hardware. For a virtual machine, a minimum of 20GB of disk space and 2GB of RAM is recommended. For a bare-metal installation, more resources will ensure smoother performance.
- Download Kali Linux ISO: Visit the official Kali Linux website (kali.org) and download the latest ISO image for your architecture (e.g., 64-bit). It’s crucial to download from the official source to ensure the integrity and security of the image.
- Bootable Media: You’ll need a way to boot from the downloaded ISO. This typically involves creating a bootable USB drive or burning the ISO to a DVD. Tools like Rufus (Windows), Etcher (cross-platform), or the
ddcommand (Linux/macOS) can be used to create a bootable USB drive. - Virtualization Software (Optional but Recommended): For beginners, or for those who want to experiment without affecting their primary operating system, installing Kali in a virtual machine (VM) is highly recommended. Popular VM software includes VirtualBox, VMware Workstation/Fusion, or Hyper-V. This approach allows you to run Kali alongside your existing OS, providing a safe sandbox environment.
Installing Kali Linux: Step-by-Step Guide
The installation process for Kali Linux is straightforward, mirroring many standard Linux installations but with specific considerations for its security-focused nature.
Method 1: Standard Installation (Bare Metal or Virtual Machine)
This is the most common method and provides a fully functional Kali Linux system.
Step 1: Booting from the Installation Media
- Insert Bootable Media: Insert your bootable USB drive or DVD into your computer.
- Access BIOS/UEFI: Restart your computer and enter your system’s BIOS or UEFI settings. This is usually done by pressing a specific key during startup (e.g., F2, F10, F12, DEL, or ESC). The exact key varies by manufacturer.
- Change Boot Order: In the BIOS/UEFI settings, navigate to the “Boot” or “Boot Order” section and set your USB drive or DVD drive as the first boot device.
- Save and Exit: Save your changes and exit the BIOS/UEFI. Your computer will now boot from the Kali Linux installation media.
Step 2: The Kali Linux Installer

- Welcome Screen: Upon booting, you’ll be presented with the Kali Linux boot menu. Select “Graphical install” for an easier, guided installation, or “Install” for a text-based installation.
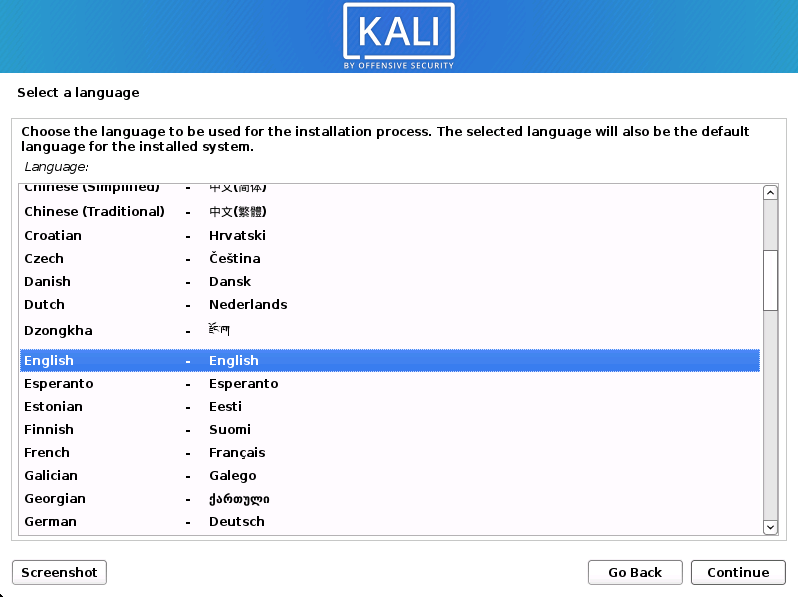
- Language, Location, and Keyboard Layout: Follow the on-screen prompts to select your preferred language, geographical location, and keyboard layout. These settings affect the system’s locale and input methods.
- Network Configuration: The installer will attempt to configure your network connection. If you’re using Wi-Fi, you may be prompted to select your network and enter the password.
- Hostname and Domain Name:
- Hostname: This is the name of your computer on the network. Choose something descriptive, like “kali-pentest.”
- Domain Name: For most home users, you can leave this blank or enter a placeholder like “localdomain.”
- User Account Setup:
- Root Password: You’ll be asked to set a password for the
rootuser. This is the superuser account with full administrative privileges. Choose a strong, unique password and remember it! - Create a New User: It’s highly recommended to create a regular user account for daily use. This improves security by limiting the need to operate as root. Enter a full name for the user, a username (which will be your login name), and a strong password for this user.
- Root Password: You’ll be asked to set a password for the
Step 3: Disk Partitioning
This is a crucial step that requires careful consideration.
- Choose a Partitioning Method:
- Guided – Use Entire Disk: This is the simplest option, especially for a dedicated Kali machine or a VM. It will erase all data on the selected disk and set up partitions automatically.
- Guided – Use Entire Disk and Set Up LVM: LVM (Logical Volume Management) provides more flexibility in managing disk space.
- Manual: This option gives you complete control over partitioning. It’s recommended for advanced users or when dual-booting with other operating systems.
- Selecting the Disk: If you choose “Guided,” select the disk you want to install Kali on. Be absolutely sure you have selected the correct disk, as all data on it will be erased.
- Partition Scheme: For beginners, the default “All files contained in one partition” is usually sufficient.
- Review and Confirm: The installer will show you the proposed partitioning scheme. Review it carefully and select “Finish partitioning and write changes to disk.” Confirm the changes when prompted.
Step 4: Installing the Base System
The installer will now proceed to copy files and install the core Kali Linux system. This process can take some time.
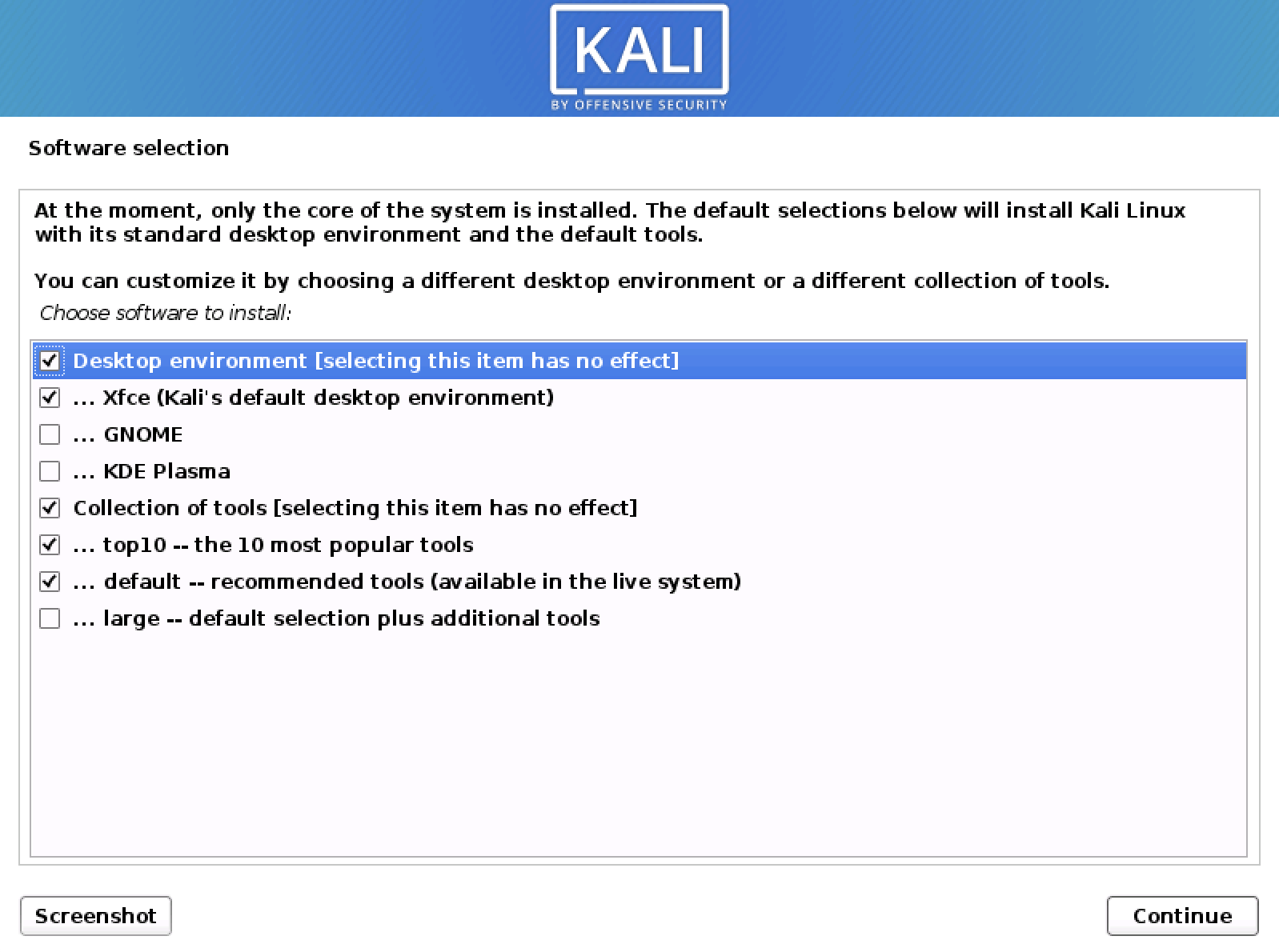
Step 5: Software Selection
- Desktop Environment: You’ll be prompted to choose your preferred desktop environment. Popular options include Xfce (lightweight and fast), GNOME (feature-rich and modern), and KDE Plasma (highly customizable). Xfce is often recommended for its performance.
- Additional Tools: You may have the option to install additional tool collections. For a comprehensive security suite, it’s advisable to select the “kali-linux-default” or even “kali-linux-everything” meta-package, depending on your available disk space and needs. Be aware that “kali-linux-everything” will install a vast number of tools, which can consume significant disk space.
Step 6: Installing the GRUB Boot Loader
The GRUB (GRand Unified Bootloader) is essential for booting your operating system.
- Install GRUB to the Master Boot Record (MBR): You’ll be asked if you want to install the GRUB boot loader to the master boot record. Select “Yes.”
- Select the Device: Choose the hard drive where you want to install GRUB. Typically, this is your primary hard drive (e.g.,
/dev/sda).
Step 7: Completing the Installation
- Installation Complete: Once the GRUB installation is finished, the installer will notify you that the installation is complete.
- Reboot: Remove the installation media (USB drive or DVD) and reboot your computer by selecting “Continue.”
Method 2: Live Boot and Installation (for Testing and Forensic Work)
Kali Linux also offers a “Live” mode, which allows you to run the operating system directly from the bootable media without installing it to your hard drive. This is incredibly useful for testing hardware compatibility, performing forensic investigations on a suspect drive without modifying it, or simply trying out Kali before committing to an installation.
- Boot from Live Media: Follow the initial booting steps as described above, but select “Live (amd64)” or a similar option from the boot menu.
- Explore Kali: You’ll be presented with a fully functional Kali desktop. You can launch applications, browse the web, and explore the tools.
- Install from Live Session: If you decide you want to install Kali after exploring it, you’ll typically find an “Install Kali Linux” icon on the desktop. Double-clicking this will launch the installer, and you can follow the same steps as outlined in Method 1. This approach allows you to test the waters before diving in.
Post-Installation: Optimizing Your Kali Environment
Once Kali Linux is installed, the real journey of cybersecurity mastery begins. Think of this as refining your personal brand or making strategic financial adjustments after a major acquisition.
Essential First Steps
- Update Your System: Immediately after installation, it’s crucial to update your system to ensure you have the latest security patches and software. Open a terminal and run:
bash
sudo apt update && sudo apt upgrade -y
This command updates the package list and then upgrades all installed packages. The-yflag automatically confirms any prompts. - Configure Network Interfaces: Ensure your network interfaces are properly configured for your needs, whether for wired or wireless connections.
- Install Additional Tools: While Kali comes with a vast array of tools, you might need specific ones not included in your initial selection. Use
apt search <tool_name>to find them andsudo apt install <tool_name>to install.
Enhancing Your Security and Workflow
- Change Default Passwords: If you haven’t already, ensure all sensitive accounts, including root and your user account, have strong, unique passwords.
- Learn Command-Line Essentials: Kali Linux heavily relies on the command line. Investing time in learning basic Linux commands (e.g.,
ls,cd,pwd,man,grep,find) will significantly improve your efficiency and understanding. - Explore the Tools: Take the time to explore the various security tools available. Understand their purpose, how they work, and their ethical implications. Websites like (offensive-security.com) and various cybersecurity blogs offer tutorials and guides for many of Kali’s tools.
Conclusion: Your Path to Cybersecurity Excellence
Installing Kali Linux is more than just setting up an operating system; it’s about equipping yourself with the tools and knowledge necessary to navigate and secure the digital world. Whether your motivation stems from technological curiosity, the desire to build a strong professional brand, or the ambition to unlock new financial opportunities through specialized skills, Kali Linux is your indispensable ally.
By following this guide, you’ve taken a significant step towards mastering this powerful platform. Remember, the installation is just the beginning. Continuous learning, ethical practice, and a commitment to understanding the evolving threat landscape are what will truly define your success in the exciting field of cybersecurity. Embrace the journey, explore the vast capabilities of Kali Linux, and contribute to a safer digital future.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.