In the early days of the internet, a common piece of advice for staying safe online was simple: “Don’t click on suspicious links or download unknown attachments.” While that remains sound advice, the threat landscape has evolved into something far more insidious. Today, a user can compromise their entire system without ever clicking a “Download” button or opening a malicious file. This phenomenon, known as a “drive-by download,” represents one of the most sophisticated challenges in modern cybersecurity.
Understanding how malware is installed simply by visiting a website is crucial for anyone navigating the digital world. It is no longer just about avoiding the “dark corners” of the web; even legitimate, high-traffic websites can become unwitting conduits for cyberattacks. This article delves into the technical mechanics of web-based infections, the vulnerabilities they exploit, and the best practices for maintaining digital security.

The Mechanics of Drive-By Downloads
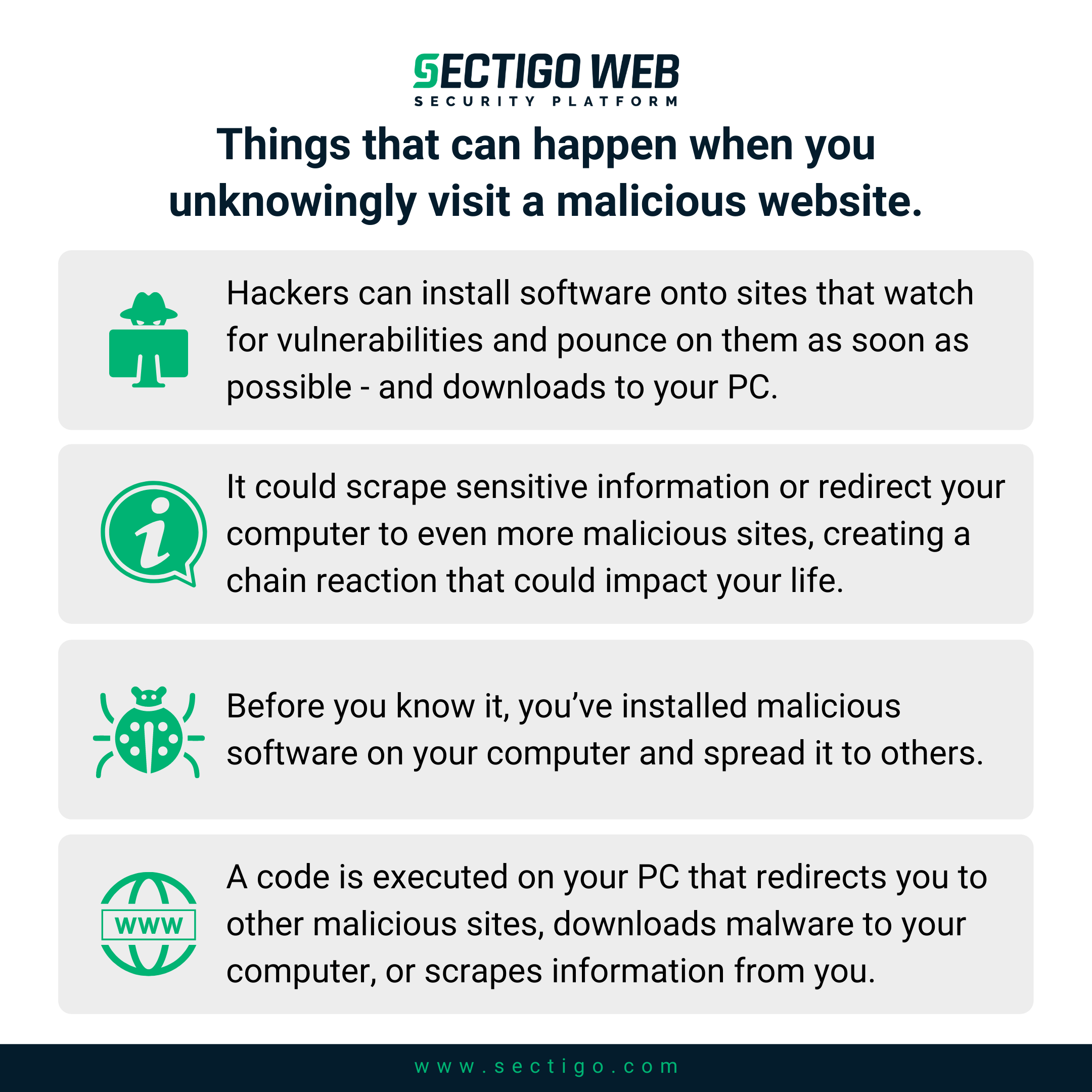
A drive-by download refers to the unintentional download of malicious code onto a computer or mobile device without the user’s knowledge or consent. Unlike traditional malware delivery, which requires social engineering to trick a user into taking an action, drive-by attacks exploit the automated way web browsers interact with servers.
Exploit Kits and Automated Attacks
The engine behind most drive-by downloads is the “exploit kit.” This is a pre-packaged software system used by cybercriminals to identify vulnerabilities in a visitor’s web browser or its plugins (such as Java, Adobe Reader, or outdated video players). When a user visits a compromised site, the exploit kit silently scans the user’s system for “holes” in its security. If a vulnerability is found, the kit automatically pushes a “payload”—the actual malware—into the system. This entire process happens in the background, often in a fraction of a second, leaving the user completely unaware that their security has been breached.
The Role of Iframes and Malicious Scripts
To initiate the attack, hackers must first find a way to run their scripts on a website. This is often done through hidden HTML elements called “iframes.” An iframe (inline frame) allows a website to embed content from another source. While used legitimately for things like YouTube videos or social media feeds, hackers use invisible 1×1 pixel iframes to redirect a user’s browser to a malicious server. Because the iframe is invisible, the user sees the legitimate website they intended to visit, while their browser is simultaneously communicating with a server controlled by an attacker.
Redirection Chains
Malware delivery is rarely a direct path. Attackers often use a series of redirections to mask the source of the malware and evade security filters. A user might visit Website A, which contains a script that redirects to Website B (a “gate” server), which finally sends the browser to Website C (the exploit kit server). This complexity makes it difficult for security researchers to track the origin of the attack and allows the malicious infrastructure to remain active for longer periods.
Common Methods of Web-Based Infection
While the underlying technology involves scripts and exploits, the “delivery vehicle” for malware can take several forms. These methods leverage the trust users have in established platforms or the sheer ubiquity of certain web elements.
Malvertising (Malicious Advertising)
One of the most prevalent ways malware is spread is through “malvertising.” This technique involves injecting malicious code into legitimate online advertising networks. Because ads are served dynamically by third-party providers, even a highly secure website like a major news outlet or a social media platform can inadvertently display an ad containing a malicious script. When the ad loads in the user’s browser, the script executes, triggering the drive-by download process. The site owner is often unaware their ad space is being used for criminal activity.
Compromised Legitimate Websites
Hackers frequently target websites with poor security—such as those using outdated Content Management Systems (CMS) like older versions of WordPress or Joomla. By exploiting a vulnerability in the website’s own code, the attacker can inject malicious JavaScript directly into the site’s pages. Every visitor to that site then becomes a potential victim. This is particularly dangerous because users trust these sites and are less likely to suspect that a familiar blog or local business page could be a source of infection.
Social Engineering and Fake Update Prompts
While some downloads are truly silent, others use “browser-based social engineering.” This occurs when a website displays a convincing pop-up or overlay claiming that the user’s software is out of date. Common examples include fake “Chrome Update Required” or “Flash Player is Outdated” warnings. When the user clicks “Update,” they are actually downloading a malicious executable. Although this requires a click, it is categorized with web-based infections because the delivery is initiated entirely through the web browsing experience.
Vulnerabilities That Facilitate Silent Installation
For a drive-by download to succeed, there must be a vulnerability to exploit. These weaknesses generally fall into three categories: browser flaws, plugin vulnerabilities, and operating system gaps.
Unpatched Browser Engines and Plugins
The web browser is the most complex piece of software on most computers. Engines like Chromium (Chrome, Edge, Brave) or Gecko (Firefox) are constantly updated to patch security flaws. However, if a user fails to update their browser, they remain vulnerable to “known exploits”—bugs that the developer has already fixed but that still exist on the user’s machine. Historically, third-party plugins like Adobe Flash, Java, and Silverlight were the primary targets for exploit kits. While these plugins are becoming obsolete, modern vulnerabilities often target how browsers handle JavaScript, CSS, or PDF rendering.
Zero-Day Exploits
The most dangerous type of vulnerability is the “zero-day.” This is a security flaw that is unknown to the software vendor. Since the developer is unaware of the bug, no patch exists. Cybercriminals who discover (or purchase) zero-day exploits can use them to bypass even the most up-to-date security measures. While zero-days are relatively rare and often reserved for high-value targets, they represent a significant risk in the ecosystem of web-based malware installation.
Operating System Weaknesses
Sometimes, the browser is just the entry point. Once the exploit kit gains a foothold through the browser, it may attempt to escalate privileges by exploiting vulnerabilities within the operating system (OS) itself. This allows the malware to move out of the “sandbox”—the restricted environment where the browser runs—and gain access to the system’s core files, registry, and hardware.
The Impact of Web-Injected Malware
Once the malware is successfully installed, the consequences depend on the “payload” chosen by the attacker. Modern malware is modular, meaning hackers can deploy different tools depending on the victim’s profile.
Data Exfiltration and Identity Theft
Many drive-by downloads install “infostealers.” These programs sit quietly in the background, monitoring keystrokes (keyloggers) or scraping data from browser auto-fill forms. The goal is to capture sensitive information such as banking credentials, passwords, and personal identification. This data is then sent back to the attacker’s command-and-control (C2) server to be used for identity theft or sold on the dark web.
Ransomware and System Lockdowns
In some cases, the payload is ransomware. Within minutes of visiting a compromised site, the user’s files are encrypted, and a demand for payment appears on the screen. Because drive-by downloads are automated, they allow ransomware operators to cast a very wide net, infecting thousands of users simultaneously to maximize their potential profit.
Botnets and Crypto-jacking
Not all malware wants to be noticed. Some payloads turn the infected computer into a “zombie” in a botnet. These hijacked computers can be used to launch Distributed Denial of Service (DDoS) attacks, send out millions of spam emails, or mine cryptocurrency (crypto-jacking). In the case of crypto-jacking, the user may only notice that their computer is running slowly or that the cooling fans are constantly spinning, as the malware consumes system resources to generate digital currency for the attacker.
Defense Strategies for the Modern Web User
Given that malware can be installed simply by viewing a webpage, a passive approach to security is no longer sufficient. Protection requires a combination of automated tools and proactive habits.
Layered Security and Endpoint Protection
The first line of defense is a robust endpoint security solution. Modern antivirus and anti-malware programs do more than just scan files; they offer “web protection” that monitors network traffic in real-time. These tools can block access to known exploit kit servers and identify the behavioral patterns of a drive-by download before the payload is executed.
Patch Management and Browser Hardening
The single most effective way to prevent drive-by downloads is to keep all software updated. This includes the operating system, the web browser, and any applications that interact with web content. Enabling “auto-update” ensures that as soon as a security flaw is patched, your system is protected. Additionally, “hardening” the browser—by using extensions that block malicious scripts (like uBlock Origin) and disabling unnecessary plugins—drastically reduces the attack surface.

The Importance of Safe Browsing Habits
While technology does the heavy lifting, user awareness is still vital. Modern browsers provide “Safe Browsing” warnings when a site is known to be dangerous; these warnings should never be ignored. Furthermore, users should be wary of any site that prompts for unexpected downloads or software updates. Using a non-administrative account for daily browsing can also limit the damage of an infection, as the malware may lack the permissions needed to install itself deep within the system.
In conclusion, the evolution of web-based threats means that “browsing” is an active security risk. By understanding the mechanics of drive-by downloads and the vulnerabilities of the web ecosystem, users and organizations can better prepare themselves. Through rigorous software updates, the use of advanced security tools, and a healthy dose of digital skepticism, it is possible to navigate the modern web without becoming a victim of silent malware installation.
