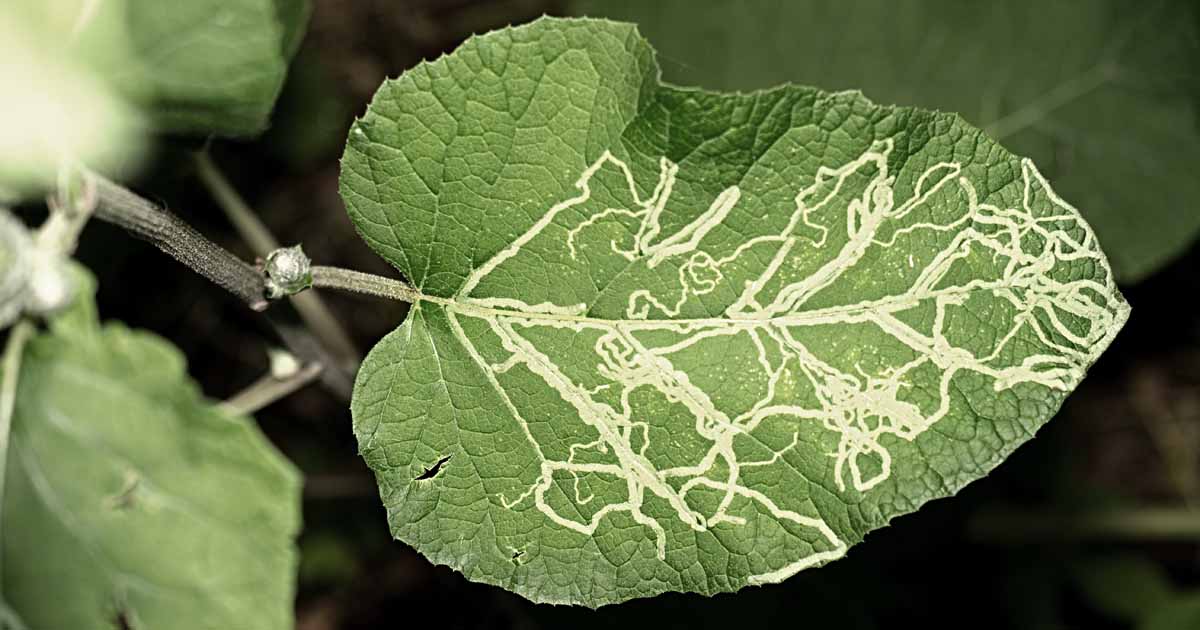
In the natural world, a leaf miner is a fascinating organism, typically the larva of an insect that lives and feeds within the tissue of a plant leaf. Its presence is often inferred by the winding tunnels it carves, leaving behind visible trails and damage. In the vast and increasingly complex digital ecosystem, we encounter analogous entities – not biological insects, but specialized software agents, algorithms, or even human-driven processes that “mine” through layers of information, often leaving their own unique digital signatures. We’ve termed these the “Digital Leaf Miners.”

Just as a biological leaf miner extracts sustenance from a leaf, a Digital Leaf Miner extracts valuable, often hidden, insights or data points from massive, interconnected digital “leaves” – be they datasets, web pages, social media feeds, code repositories, or network traffic. The question, “what does a leaf miner look like?” when applied to the digital realm, transcends a simple visual description. It demands an understanding of its functional architecture, its operational manifestations, its subtle outputs, and its profound impacts on the digital landscape. Identifying and understanding these digital entities is crucial for anyone navigating or building within modern tech, from developers and data scientists to cybersecurity professionals and business strategists. This exploration delves into the characteristics, behaviors, and implications of these digital agents, offering a comprehensive view of their “appearance” in our increasingly data-driven world.
Defining the Digital Leaf Miner: More Than Just a Bot
To truly grasp what a Digital Leaf Miner “looks like,” we must first define its conceptual boundaries. It’s a specialized form of automated agent or analytical framework, engineered to delve deep into specific layers of digital information, often bypassing surface-level observations to extract particular, granular data. Unlike a broad web crawler that indexes entire sites, or a simple scraper that pulls visible text, a Digital Leaf Miner is often characterized by its precision and its ability to operate within the “tissue” of data structures.
Intentionality and Specialization
The hallmark of a Digital Leaf Miner is its intentionality and specialization. It isn’t merely scanning; it’s searching for something specific. This could be a particular pattern within a vast log file, a subtle trend in user behavior across multiple platforms, an overlooked dependency in a complex codebase, or an anomaly in a network’s data flow. Its “vision” is highly tuned to a narrow band of information, allowing it to penetrate noise and extract specific signals. This specialization implies sophisticated algorithms, often incorporating machine learning, pattern recognition, and sometimes even natural language processing (NLP) to interpret and contextualize the extracted data. Its “look” is thus defined by its purpose – whether it’s optimizing ad targeting, detecting financial fraud, uncovering security vulnerabilities, or personalizing user experiences, its underlying design reflects its mission.
Operating Beneath the Surface
Just as its biological counterpart operates unseen within the leaf, a Digital Leaf Miner often operates beneath the surface of conventional data interaction. This might mean:
- Analyzing metadata: It extracts information not from the primary content, but from the data about the data – timestamps, authorship, file origins, embedded tags.
- Observing interaction patterns: Instead of content, it studies how users interact with content – click paths, scroll depths, session durations, inter-component dependencies.
- Deconstructing complex structures: It navigates intricate APIs, database schemas, or code architectures to find connections and dependencies that aren’t immediately obvious.
This subterranean operation makes its “presence” less about direct visibility and more about inferring its activity from the changes or patterns it leaves in its wake, much like the winding tunnels of a biological leaf miner. Its “look” is therefore often indirect, revealed by its impact rather than its direct observable form.
The Anatomy of a Digital Leaf Miner: Functional Architectures and Algorithms
Understanding the “look” of a Digital Leaf Miner requires dissecting its core components and the intelligence that drives it. It’s not a physical entity, but a construct of code, data, and computational logic.
Algorithmic Core: The Brain of the Miner
At the heart of every Digital Leaf Miner lies its algorithmic core. This is where the specialized “mining” logic resides. Depending on its objective, this core could employ:
- Pattern Recognition Algorithms: To identify recurring sequences, shapes, or structures within data streams (e.g., specific attack signatures in network packets, common coding errors).
- Machine Learning Models: For adaptive learning and prediction, allowing the miner to refine its search criteria and identify increasingly subtle or complex patterns over time (e.g., anomaly detection for fraud, predictive maintenance in IoT systems).
- Graph Traversal Algorithms: To navigate interconnected datasets, identifying relationships and dependencies that are not linear (e.g., social network analysis, supply chain optimization).
- Natural Language Processing (NLP) Engines: To extract sentiment, entities, or specific information from unstructured text data (e.g., market research from social media, competitive intelligence from news articles).
The “look” of its brain is therefore a reflection of these sophisticated computational techniques – complex neural networks, intricate decision trees, or finely tuned statistical models. Its efficiency and accuracy are direct indicators of its algorithmic sophistication.
Data Hooks and Probes: The Sensory Organs
To extract information, a Digital Leaf Miner needs data hooks and probes – its “sensory organs.” These are the interfaces and protocols it uses to interact with its digital environment. This might involve:
- API Integrations: Connecting to various services and platforms to pull structured data.
- Network Packet Interceptors: Monitoring data flow at a low level to identify specific transmissions or anomalies.
- Database Query Engines: Performing complex queries to extract granular information from structured databases.
- Web Scraping Modules (Advanced): Intelligent agents designed to navigate web pages, render content (including JavaScript-driven elements), and extract information dynamically, often mimicking human interaction to avoid detection.
The “look” of these probes varies widely. For an API-driven miner, it might be a set of defined request/response formats. For a network miner, it might be the configuration of a deep packet inspection tool. Their effectiveness lies in their ability to seamlessly and often invisibly integrate with various data sources, acting as digital parasites drawing information without disrupting the host “leaf.”
Orchestration and Scalability: The Body and Limbs
A single Digital Leaf Miner is often part of a larger, orchestrated system. Its body and limbs comprise the infrastructure that supports its operation and allows it to scale. This includes:
- Distributed Computing Frameworks: For processing massive datasets across multiple machines (e.g., Apache Spark, Hadoop).
- Cloud Infrastructure: Leveraging scalable computing resources to handle fluctuating data volumes and processing demands.
- Containerization (e.g., Docker, Kubernetes): For deploying and managing multiple miner instances efficiently and reliably.
- Monitoring and Logging Systems: To track its own performance, identify issues, and ensure its operations remain within desired parameters.
The “look” here is one of robustness and elasticity. A healthy Digital Leaf Miner ecosystem is characterized by its ability to process vast amounts of data, adapt to changing conditions, and provide reliable, consistent output, all while maintaining efficiency. Its infrastructure is designed for resilience, much like a thriving organism’s ability to withstand environmental pressures.
Operational Manifestations: Where and How Digital Leaf Miners Operate
The “look” of a Digital Leaf Miner is often best understood by observing its operational manifestations – where it operates and the methods it employs. Its habitat dictates its form and behavior.
Legitimate vs. Malicious Miners: The Dual Nature
Digital Leaf Miners exist on a spectrum, from highly beneficial to overtly malicious.
- Legitimate Leaf Miners: These are designed for positive impact. Examples include:
- Business Intelligence & Analytics: Extracting market trends, customer insights, or operational efficiencies from internal and external data.
- Research & Development: Accelerating scientific discovery by mining academic papers, genetic sequences, or experimental data.
- Cybersecurity Defense: Identifying vulnerabilities, detecting intrusions, or monitoring for anomalous network activity.
- Content Recommendation Systems: Personalizing user feeds by understanding viewing habits and preferences.
Their “look” in operation is typically transparent, with clear objectives, documented methodologies, and adherence to ethical guidelines. They seek to enhance, protect, and inform.
- Malicious Leaf Miners: These are designed for illicit purposes, often infringing on privacy, security, or fair competition. Examples include:
- Data Exfiltration Bots: Stealing sensitive corporate or personal data.
- Competitive Intelligence (Black Hat): Illegally scraping competitor pricing, product data, or customer reviews.
- Ad Fraud Bots: Simulating human interaction to generate fake clicks or impressions.
- Vulnerability Scanners (Exploitative): Identifying weaknesses in systems for later exploitation.
Their “look” is clandestine, often employing cloaking techniques, botnets, IP rotation, and sophisticated evasion tactics to avoid detection. They operate in the shadows, their presence revealed only by the damage or unauthorized data they extract.
The Footprint: Traces and Tunnels
Regardless of intent, every Digital Leaf Miner leaves a footprint – digital “tunnels” or traces of its activity.
- Network Logs: Increased traffic to specific endpoints, unusual request patterns, or connections from unexpected IP addresses.
- System Logs: Records of database queries, API calls, file access, or command executions.
- Data Store Anomalies: Missing data, altered records, or the presence of unexpected new datasets.
- Performance Impacts: Unexplained slowdowns, increased resource consumption, or spikes in server load.
The “look” of these footprints can vary wildly. For a well-behaved miner, the footprint is typically organized, structured, and within expected parameters. For a malicious one, it’s often chaotic, evasive, or designed to mimic legitimate activity, making it harder to discern. Identifying these traces requires robust monitoring, sophisticated analytics, and a deep understanding of baseline system behavior.
Seeing Beyond the Surface: Identifying the Outputs and Impacts of Digital Leaf Miners
The ultimate “look” of a Digital Leaf Miner is in its output and the impact it has on the digital environment. This is where its true nature and effectiveness become apparent.
Data Synthesis and Insight Generation: The Mined Resources
The primary output of a Digital Leaf Miner is synthesized data and generated insights. It doesn’t just collect raw data; it processes, aggregates, and often interprets it.
- Structured Reports: For business intelligence, detailing trends, anomalies, or performance metrics.
- Alerts and Notifications: In cybersecurity, flagging suspicious activities or potential threats.
- Personalized Content Streams: In recommendation engines, tailored news feeds or product suggestions.
- Code Patches or Refactorings: Identifying inefficiencies or vulnerabilities within software.
The “look” of this output is its utility. For legitimate miners, it’s about clarity, accuracy, and actionable intelligence. For malicious ones, it might be the illicit data payload itself – a list of credit card numbers, a database dump, or a trove of proprietary information. The quality and value of these outputs are direct indicators of the miner’s efficacy and purpose.
Ecosystem Transformation: The Landscape Changes
The most profound “look” of a Digital Leaf Miner is its contribution to or alteration of the digital ecosystem.
- Enhanced Decision-Making: Legitimate miners empower organizations with data-driven insights, leading to better products, services, and strategies. This transforms business landscapes, fostering innovation and efficiency.
- Improved Security Posture: Cybersecurity miners strengthen digital defenses, making systems more resilient to attacks and fostering a safer online environment.
- Erosion of Trust and Privacy: Malicious miners contribute to data breaches, identity theft, and privacy violations, eroding user trust and necessitating more stringent security measures and regulatory frameworks.
- Resource Drain and Infrastructure Burden: Both legitimate and malicious miners, if poorly optimized, can consume significant computational resources, impacting system performance and increasing operational costs.
The “look” of this transformation can be seen in the evolution of digital industries, the constant arms race in cybersecurity, the ever-changing privacy regulations, and the demand for more robust, scalable infrastructure. Digital Leaf Miners are not merely extracting data; they are actively shaping the environment in which that data resides.
Cultivating Healthy Digital Ecosystems: Managing and Mitigating Malignant Leaf Miners
Given the pervasive nature and dual potential of Digital Leaf Miners, understanding “what they look like” is fundamental to effective management and mitigation. This involves strategic implementation for beneficial miners and robust defense mechanisms against malicious ones.
Strategic Deployment and Ethical AI Practices
For organizations leveraging Digital Leaf Miners for legitimate purposes, the “look” of responsible deployment is characterized by:
- Transparency: Clearly defining the purpose, scope, and data sources of the miner.
- Data Governance: Adhering to strict data privacy regulations (e.g., GDPR, CCPA) and ethical data handling practices.
- Bias Mitigation: Designing algorithms that minimize inherent biases, ensuring fair and equitable outcomes.
- Regular Audits: Continuously monitoring the miner’s performance, impact, and compliance with ethical guidelines.
This proactive approach ensures that beneficial miners contribute positively to the digital ecosystem without unintended negative consequences, creating a “look” of trustworthiness and responsible innovation.
Detection, Defense, and Digital Security
Identifying and mitigating malicious Digital Leaf Miners requires a multi-layered security strategy. The “look” of effective defense includes:
- Advanced Threat Detection Systems: Employing AI-powered anomaly detection, intrusion detection/prevention systems (IDS/IPS), and security information and event management (SIEM) platforms to identify unusual patterns indicative of miner activity.
- Behavioral Analytics: Profiling normal user and system behavior to quickly spot deviations that might signal a malicious miner at work.
- API Security and Rate Limiting: Protecting API endpoints from excessive or unauthorized requests, which are common entry points for data exfiltration.
- Bot Management Solutions: Specialized tools designed to distinguish between legitimate and malicious bot traffic, often employing captchas, fingerprinting, and behavioral analysis.
- Regular Security Audits and Penetration Testing: Proactively searching for vulnerabilities that malicious miners might exploit.
The “look” of a well-defended digital environment is one of vigilance and resilience. It’s an ecosystem that actively monitors for the “tunnels” and “traces” of unwanted intruders, quickly isolating and neutralizing them before significant damage can occur.
In conclusion, the question “what does a leaf miner look like?” when transposed to the digital ecosystem, reveals a complex, multifaceted entity. It’s not a creature of flesh and blood, but a construct of code and logic, whose appearance is defined by its intent, its algorithmic sophistication, its operational footprint, and its profound impact on the data-rich environments we inhabit. Understanding these digital agents, whether beneficial or malicious, is paramount for shaping a secure, insightful, and resilient technological future. As our digital “leaves” grow richer and more intricate, the art of identifying and managing these digital “miners” will only become more critical.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.