In the world of dentistry, a cavity is a permanent area of damage that develops into tiny openings or holes. In the world of high-scale technology, software engineering, and digital infrastructure, the metaphor is strikingly apt. A “beginning cavity” in a tech stack—often referred to as technical debt, bit rot, or a latent security vulnerability—starts as a microscopic flaw. It is a slight deviation from best practices, a minor patch that wasn’t quite clean, or an overlooked dependency.
To the untrained eye, the system looks functional. To the expert, however, identifying what a beginning cavity looks like in a digital environment is the difference between a routine update and a catastrophic system failure. Understanding these early signs of decay is essential for maintaining the “hygiene” of software and ensuring the longevity of digital assets.

The Anatomy of Digital Decay: Defining the Tech Cavity
Just as biological cavities are caused by the gradual erosion of enamel, tech cavities are caused by the gradual erosion of code quality and architectural integrity. This decay is rarely sudden; it is a cumulative process driven by the pressure of release cycles and the accumulation of “quick fixes.”
Latent Bugs and Technical Debt
A beginning cavity often manifests as technical debt. This isn’t always “bad code”; rather, it is code that was written to meet a specific deadline at the expense of long-term scalability. A beginning cavity in this context looks like a “TODO” comment left in a repository for six months or a hard-coded variable that should have been an environment configuration. These small compromises represent the softening of the software’s structural integrity. When you look at the source code, these “white spots”—the early signs of demineralization—are the sections that developers are “afraid to touch” because they don’t quite understand how they interact with the rest of the system.
The Silent Erosion of Security Protocols
In cybersecurity, a beginning cavity is a misconfiguration that has yet to be exploited. It might look like an S3 bucket with slightly-too-permissive access controls or an API endpoint that lacks rate limiting. These are the microscopic pits where malicious actors can eventually find purchase. Unlike a full-blown breach, a beginning cavity is silent. It doesn’t trigger alarms; it simply waits. Identifying it requires a proactive shift in perspective, looking for the “painless” gaps in the perimeter before they turn into deep-seated vulnerabilities.
Visual Cues of a Tech Cavity: Identifying Symptoms Early
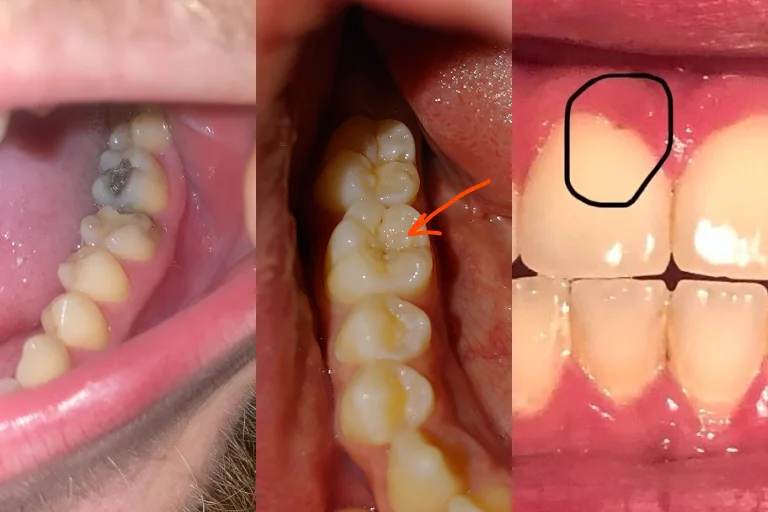
In a clinical setting, a beginning cavity might appear as a faint white spot on the tooth. In a tech ecosystem, the visual cues are found in performance metrics, log files, and user interface inconsistencies. Recognizing these signs requires a sophisticated monitoring strategy that goes beyond “up or down” status checks.
Performance Lag and “White Spots” in UI/UX
One of the first signs of software decay is a subtle degradation in performance—what we might call “micro-stuttering.” When a beginning cavity exists in the database layer, it doesn’t cause a crash; it causes a 50ms delay in query execution. To the end-user, the “white spot” might be a slight lag in a button response or a minor visual glitch in the UI that suggests the underlying state management is starting to fray. These inconsistencies are the visual indicators that the “enamel” of the application’s performance is thinning.
Error Logs and Anomalous Data Patterns
If you want to see what a beginning cavity looks like in a backend system, you look at the “noise” in your error logs. Many teams ignore “non-critical” warnings, but these warnings are the digital equivalent of tooth sensitivity to cold. They are the system’s way of signaling that something is misaligned. A beginning cavity might look like a recurring “Retry” in a distributed system or a series of “Null Pointer” warnings that are caught by a global exception handler but never actually fixed. These patterns indicate that the logic is beginning to break down in edge cases.
Diagnostic Tools for Early Detection: The Digital X-Ray

You cannot always see a cavity with the naked eye; sometimes, you need an X-ray. In technology, we use automated tools and AI-driven diagnostics to peer beneath the surface of the user interface and into the “dentin” of the codebase.
Automated Vulnerability Scanning and Static Analysis
Modern development workflows utilize Static Application Security Testing (SAST) and Dynamic Application Security Testing (DAST) to find beginning cavities. These tools act as digital X-rays, scanning millions of lines of code to find patterns associated with known vulnerabilities (CVEs). A beginning cavity, when caught by these tools, might be identified as an outdated library or an insecure cryptographic function. By integrating these “check-ups” into the CI/CD (Continuous Integration/Continuous Deployment) pipeline, organizations can “fill” these cavities before they require the “root canal” of a major security patch.
The Role of AI in Predictive Maintenance
Artificial Intelligence is changing the way we diagnose digital decay. AI tools can now perform “predictive maintenance” by analyzing historical data to identify where cavities are likely to form. For instance, AI can analyze a developer’s commit history and flag code that is overly complex, identifying it as a high-risk area for future bugs. This is the ultimate preventive tool: identifying where a cavity might form based on the “diet” of the codebase (the complexity and frequency of changes).
Preventive Care: Filling the Gaps Before They Expand
The best way to deal with a cavity is to prevent it from forming in the first place. In technology, this involves a rigorous commitment to “clean” practices and regular maintenance intervals.
Implementing a “Clean Code” Hygiene Routine
Just as daily brushing and flossing prevent biological decay, “Clean Code” practices prevent technical decay. This includes regular refactoring—the process of restructuring existing computer code without changing its external behavior. Refactoring is the digital equivalent of a professional cleaning. It removes the “plaque” of redundant logic and clarifies the “gum line” of the API surface. When teams prioritize refactoring, they ensure that beginning cavities are caught and filled as part of the daily workflow, rather than being left to grow into systemic issues.
Regular Security Audits as Professional Check-ups
No matter how well you brush, you still need to see a dentist. In tech, this means third-party security audits and penetration testing. These professionals are trained to find the beginning cavities that internal teams might be blind to. They look for the “sticky” spots in the authentication flow and the “recession” in the data encryption layers. A professional audit provides a roadmap for “restorative” work, ensuring that the foundation of the tech stack remains solid as the company scales.
The Cost of Neglect: From Minor Patch to Systemic Failure
The danger of a beginning cavity is its deceptive insignificance. Because it doesn’t cause immediate pain, it is easy to deprioritize. However, in the fast-paced world of technology, decay accelerates exponentially.
From Minor Patch to Systemic Failure
A beginning cavity in a legacy system can quickly lead to what engineers call “cascading failure.” What started as a minor inefficiency in a microservice can, under high load, cause a bottleneck that brings down the entire ecosystem. This is the digital equivalent of a cavity reaching the nerve. The “pain” is no longer localized; it is systemic. At this stage, the “filling” (a simple patch) is no longer enough. You are looking at a full system rewrite—the “extraction and implant” of the tech world—which is both costly and risky.
Scaling Stability in a Post-Decay Environment
For tech-driven brands, stability is the cornerstone of trust. If a company allows “beginning cavities” to proliferate across its apps and platforms, the resulting downtime and data leaks will erode brand equity faster than any marketing campaign can build it. Investing in the early identification of tech cavities is not just a technical requirement; it is a financial and strategic imperative. A “healthy mouth” (a clean, optimized tech stack) allows a company to chew through complex problems and scale into new markets with confidence.
In conclusion, knowing what a beginning cavity looks like in your technology stack is the first step toward building resilient, long-lasting digital products. Whether it is a slight deviation in code quality, a minor security misconfiguration, or a subtle performance lag, these early signs of decay demand immediate attention. By treating code hygiene with the same discipline as dental hygiene, organizations can avoid the “root canals” of tomorrow and maintain a bright, functional, and secure digital future.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.