The Geneva Conventions have long served as the moral and legal bedrock of international humanitarian law. Established to mitigate the effects of war on those who do not participate in hostilities, these four treaties and their subsequent protocols define the limits of permissible conduct during armed conflict. However, as the 21st century progresses, the nature of warfare has shifted from physical trenches to digital networks. In an era defined by artificial intelligence, state-sponsored cyberattacks, and autonomous weaponry, the tech industry is increasingly looking toward the framework of the Geneva Conventions to establish a “Digital Geneva Convention” that protects civilians in the fifth domain of warfare: cyberspace.
To understand how technology is reshaping global security, one must first understand the foundational principles of the original four conventions and how they are being reinterpreted through the lens of modern digital security and AI.
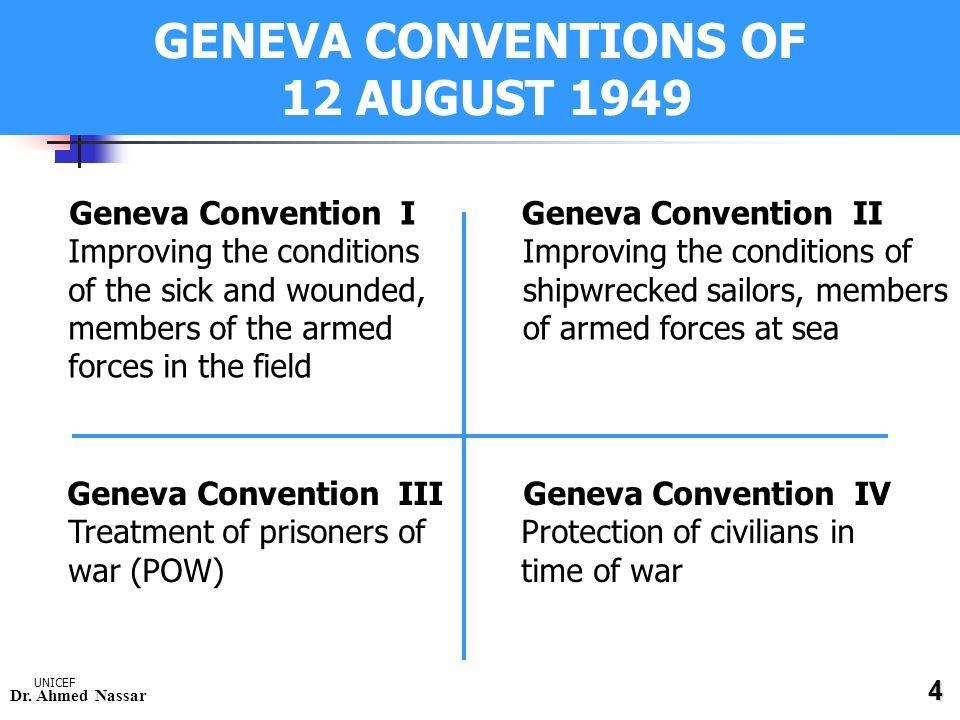
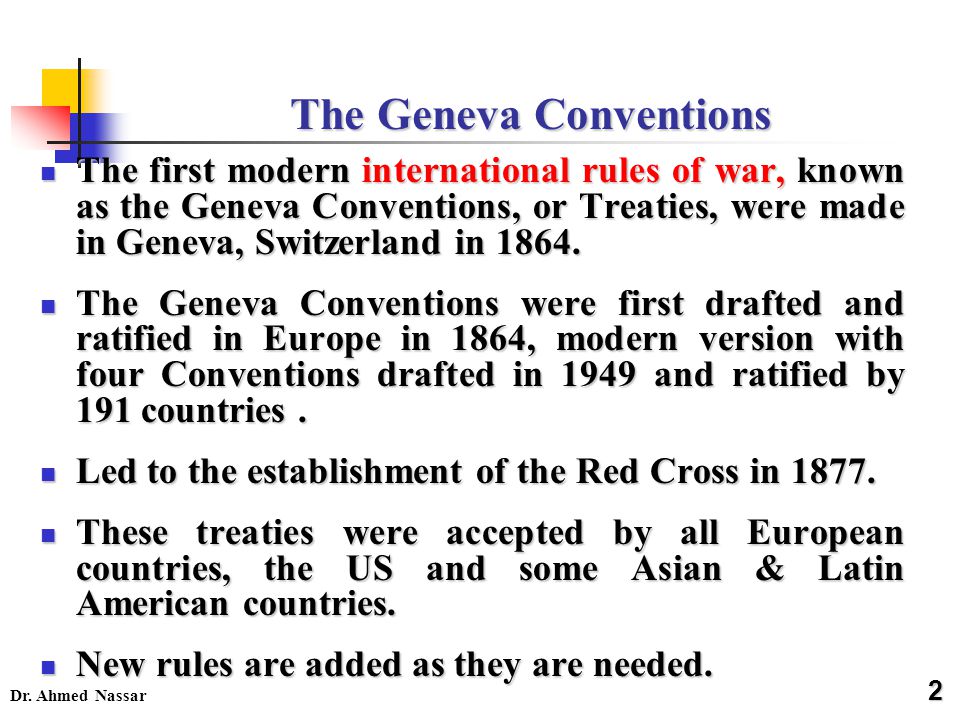
1. The Foundation of International Humanitarian Law: The Four Original Conventions
The Geneva Conventions are not merely historical documents; they are living frameworks that govern the behavior of nations. For the tech sector, these conventions provide the ethical scaffolding needed to develop responsible software and AI tools.
The First and Second Conventions: Care for the Wounded
The First Geneva Convention (1864) focuses on the protection of wounded and sick soldiers on land, while the Second Geneva Convention (1906/1949) extends these protections to those at sea. In a technological context, these conventions have birthed the concept of “digital neutrality.” Just as medical ships and ambulances are off-limits, modern digital security advocates argue that critical healthcare infrastructure—including hospital servers and medical IoT devices—should be immune from cyberattacks.
The Third Convention: Treatment of Prisoners of War
The Third Geneva Convention (1929/1949) outlines the rights of prisoners of war (POWs). In the digital age, this has evolved into discussions regarding digital privacy and the use of biometric data. The capture of a combatant today often includes the seizure of their digital identity. Tech experts are now debating how the principles of the Third Convention apply to the protection of a prisoner’s digital footprint and personal data during interrogation or detention.
The Fourth Convention: Protection of Civilians
Perhaps the most relevant to the tech niche is the Fourth Geneva Convention (1949), which protects civilians in war zones. In the 21st century, the “war zone” is often the internet. When a nation-state deploys malware to disable a power grid or a water treatment plant, the victims are civilians. This convention is the primary driver behind the movement for a Digital Geneva Convention, as it emphasizes that non-combatants should never be the target of technological warfare.
2. The Digital Geneva Convention: Protecting the Global Tech Infrastructure
As cyber warfare becomes a standard tool of statecraft, the tech industry, led by giants like Microsoft and Google, has called for a new international treaty. The proposed “Digital Geneva Convention” aims to establish a set of rules that prevent governments from targeting the private sector and civilian infrastructure.
The Role of Tech Giants as Neutral Actors
In traditional conflict, the Red Cross acts as a neutral intermediary. In the digital realm, tech companies often find themselves on the front lines. Whether it is a cloud service provider defending against a distributed denial-of-service (DDoS) attack or a software company patching a zero-day vulnerability used by a state actor, these companies are the new “first responders.” The Digital Geneva Convention proposes that tech companies should remain neutral, refusing to assist in offensive cyber operations while committed to protecting all users, regardless of nationality.
Protecting the Integrity of the Supply Chain
One of the greatest digital security threats today is the compromise of the software supply chain. When a government embeds a “backdoor” into a widely used software update, they violate the spirit of humanitarian law by turning a civilian tool into a weapon. A tech-focused interpretation of the Geneva Conventions demands that the integrity of software be maintained, ensuring that the tools civilians rely on for communication, banking, and health remain untainted by military objectives.
Preventing the Militarization of Vulnerabilities
In the current tech landscape, governments often stockpile “zero-day” vulnerabilities (security flaws unknown to the software vendor) to use in future attacks. A digital humanitarian framework would require states to report these vulnerabilities to vendors rather than weaponizing them. This shift would prioritize global digital security over tactical military advantage, mirroring the Geneva Conventions’ goal of minimizing unnecessary suffering.
3. AI and Autonomous Systems: The New Frontier of Humanitarian Law
Artificial Intelligence is fundamentally changing how decisions are made on the battlefield. As we move toward Lethal Autonomous Weapons Systems (LAWS), the legal and ethical questions surrounding the 4 Geneva Conventions become even more complex.
Algorithmic Accountability and Target Identification
The Geneva Conventions require “distinction”—the ability to distinguish between combatants and civilians. In the tech niche, this places an immense burden on AI developers. If an AI tool is used to identify targets, the software must be sophisticated enough to adhere to international law. Tech reviews and audits of these AI systems are becoming critical, as a “black box” algorithm that cannot explain its reasoning may be in inherent violation of the Fourth Geneva Convention’s civilian protection mandates.
The Human-in-the-Loop Requirement
A core principle derived from the spirit of the Geneva Conventions is that human agency must be preserved in life-and-death decisions. The tech community is currently debating the “human-in-the-loop” requirement for AI weaponry. From a digital security and ethics standpoint, allowing software to autonomously initiate lethal force removes the accountability that the Geneva Conventions were designed to enforce. Software engineering standards are now being proposed to ensure that AI remains a tool for human decision-making rather than a replacement for it.
AI in Cyber Defense and Humanitarian Aid
While much of the focus is on AI as a weapon, the tech niche also highlights AI’s role in upholding the Geneva Conventions. AI tools are being used to monitor conflict zones for human rights abuses, analyze satellite imagery to track the movement of displaced persons, and secure humanitarian databases from hacking. By leveraging AI for these purposes, the tech industry directly supports the mandates of the 1949 treaties.
4. Implementing Digital Security as a Global Humanitarian Standard
The transition from the physical 4 Geneva Conventions to a digital framework requires more than just high-level treaties; it requires technical implementation and global cooperation among software developers, security researchers, and policymakers.
International Cooperation and the Paris Call
The “Paris Call for Trust and Security in Cyberspace” is a prime example of how the tech niche is operationalizing the Geneva principles. This multi-stakeholder agreement brings together tech companies and governments to stop malicious cyber activity that threatens civilian life. It emphasizes the “protection of the public core of the internet,” a concept that mirrors the protected status of hospitals and religious sites in the original conventions.
The Challenge of Attribution and Digital Enforcement
One of the primary hurdles in applying the Geneva Conventions to technology is attribution. In physical warfare, it is usually clear which army is attacking. In the digital world, attackers use proxies, VPNs, and sophisticated obfuscation techniques to hide their tracks. Enhancing digital security and forensic tools is therefore not just a technical challenge, but a legal necessity. Without the ability to prove who launched a cyberattack, the Geneva Conventions cannot be enforced in the digital domain.
Ethical Software Development as a Modern Duty
For the individual software developer or tech lead, the legacy of the Geneva Conventions serves as a reminder of the impact of their work. Designing “secure by design” software and advocating for user privacy are modern ways of upholding humanitarian values. As technology becomes more integrated into the fabric of society, the line between a “tech gadget” and a “critical life-support system” blurs. This reality mandates that the tech industry adopts a proactive stance on digital security, treating every line of code as a potential safeguard or a potential threat to civilian safety.
Conclusion: The Future of Conflict and Technology
The 4 Geneva Conventions were born out of the horrors of the 19th and 20th centuries to ensure that even in our darkest moments, humanity remains. Today, our lives are lived through screens and powered by algorithms, making the digital world the new frontier of human rights.
By reinterpreting these conventions for the tech niche, we recognize that digital security is no longer just about protecting data—it is about protecting people. Whether through the proposal of a Digital Geneva Convention, the ethical development of AI, or the hardening of civilian infrastructure against cyber threats, the tech industry is the new guardian of international humanitarian law. As we move forward, the challenge will be to ensure that our technological progress does not outpace our moral and legal commitments to peace and civilian protection.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.