In the early days of computing, the pioneers of cybersecurity looked toward biology to describe the anomalies they witnessed within mainframe architectures. They saw code that could replicate, spread, and destroy, much like biological pathogens. Today, the terms “virus” and “bacteria” (often referred to in tech as “worms” or persistent system bloat) are frequently used interchangeably by the general public, but in the realm of digital security and software engineering, they represent two distinct classes of threats.
Understanding the nuance between these digital organisms is no longer just an academic exercise for IT professionals; it is a fundamental requirement for anyone navigating the modern tech landscape. Whether you are managing an enterprise network or securing a personal workstation, recognizing the mechanism of infection is the first step toward effective digital immunity.
Defining the Digital Virus: The Parasitic Code
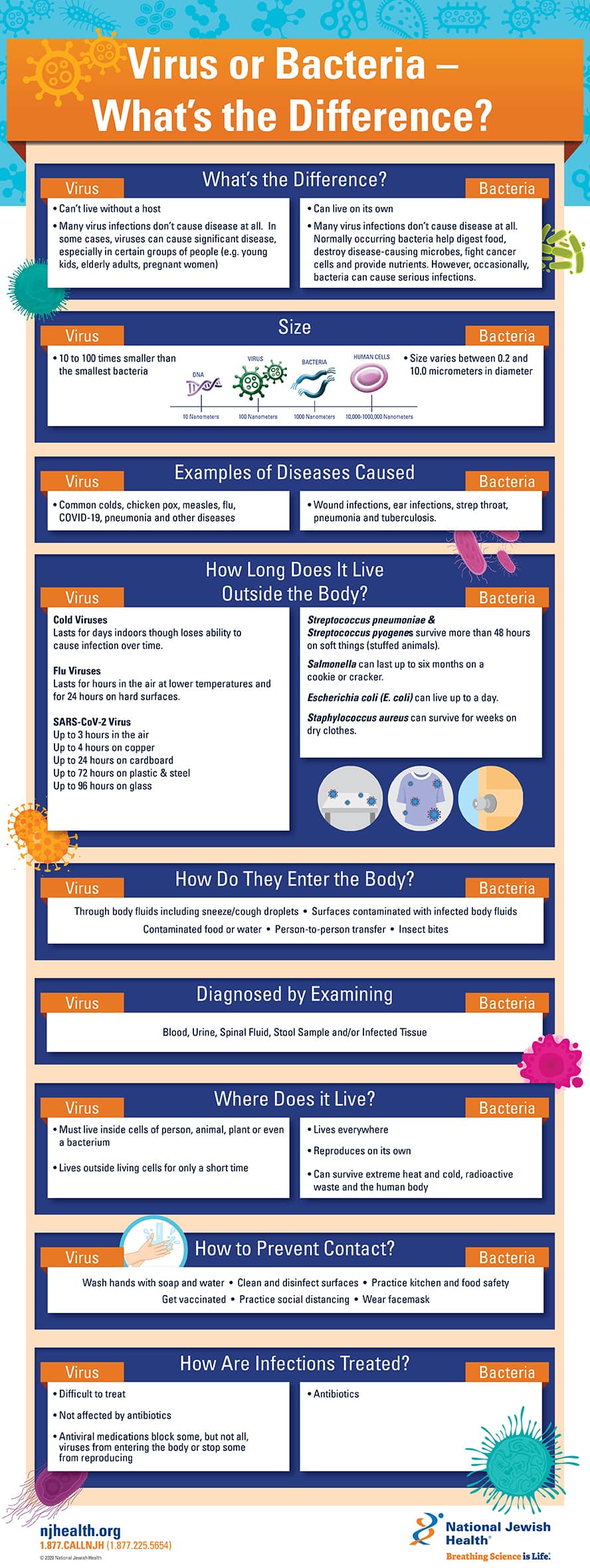
In the biological world, a virus is a microscopic parasite that cannot reproduce on its own; it requires a host cell to hijack. In technology, a digital virus follows an almost identical blueprint. It is a piece of malicious code that is not a standalone program. Instead, it must attach itself to a legitimate executable file or document.
The Mechanism of Infection and Propagation
A digital virus remains dormant until the infected “host” file is executed. This is the primary characteristic that separates a virus from other forms of malware. If an infected .exe file sits on your hard drive but is never opened, the virus cannot spread. However, once the user triggers the program, the viral code is loaded into the system’s memory. From there, it searches for other host files—such as system utilities, applications, or even document templates—and “infects” them by overwriting their code or appending itself to their structure.
This reliance on human intervention is why viruses are historically associated with file-sharing. In the 1990s, this meant floppy disks; in the 2000s, it meant email attachments; and today, it often involves downloaded software “cracks” or compromised media files.
The Payload: From Data Corruption to System Instability
The “payload” is the portion of the viral code that performs the actual malicious action. While the replication logic ensures the virus survives, the payload determines the damage. Some viruses are designed to be relatively harmless, perhaps displaying a political message or a prank on the screen. Others are catastrophic, designed to encrypt files for ransom, delete critical boot sectors, or corrupt system registries to the point where the hardware becomes a “brick.”
The evolution of the payload has moved from overt destruction to covert operation. Modern viruses often prioritize stealth, modifying the system’s security settings to allow for secondary infections while remaining undetected by traditional signature-based antivirus software.
Digital Bacteria: The Worms and Self-Sustaining Threats
If a virus is a parasite, then “digital bacteria” (commonly classified as worms or autonomous malicious scripts) are independent organisms. In the context of technology trends and digital security, these threats are arguably more dangerous because they do not require a host file or human intervention to move from one system to another.
Self-Replication Without a Host
Unlike a virus, which needs you to click “Run,” a worm exploits vulnerabilities in network protocols to move automatically. It acts like a biological bacterium that can thrive in an environment and move toward new resources independently. When a worm enters a network, it scans for other devices with similar security flaws. Once it identifies a target—such as an unpatched Windows server or an exposed IoT device—it copies itself across the network connection.
This autonomous nature allows digital bacteria to spread at exponential speeds. The infamous “I Love You” worm or the “Stuxnet” code demonstrated how autonomous scripts could traverse the globe in hours, leaping from one computer to another without a single user consciously facilitating the spread.
Resource Exhaustion and System Bloat
While some digital bacteria carry a destructive payload, many cause damage simply through their existence and replication. This is often referred to as “system bloat” or resource exhaustion. Because these entities replicate so aggressively, they consume vast amounts of network bandwidth and CPU cycles.
In a corporate environment, a bacterial-style infection can bring an entire infrastructure to a halt, not by deleting files, but by saturating the network with so much traffic that legitimate data cannot pass through. This mirrors a biological bacterial infection that overwhelms the host’s resources through sheer numbers, leading to a systemic collapse.

Diagnosis and Treatment: Antivirus vs. Endpoint Detection
As the complexity of digital pathogens has grown, so too has the technology we use to fight them. The industry has shifted from simple “antivirus” programs to comprehensive “Endpoint Detection and Response” (EDR) platforms that utilize artificial intelligence to identify threats in real-time.
Signature-Based Detection: The Digital Immune System
Traditional defense relies on “signatures”—unique strings of code that act like fingerprints for known viruses. When you run a scan, the software compares every file on your drive against a massive database of known viral signatures. If a match is found, the file is quarantined.
This is highly effective against older, established viruses, much like how a vaccine provides antibodies for known biological strains. However, it is fundamentally reactive. If a “Zero-Day” virus (one that has never been seen before) hits the system, signature-based detection is blind to it because the “fingerprint” isn’t in the database yet.
Heuristic Analysis and AI-Driven Defense
To combat “bacterial” worms and evolving viruses, modern security tools use heuristic analysis. Instead of looking for a specific fingerprint, the software looks for behavioral patterns. If a program suddenly starts attempting to modify 500 files in a second, or if it tries to send thousands of outbound requests to an unknown IP address, the AI flags it as “malicious behavior.”
This proactive approach is essential for stopping autonomous threats. By monitoring system telemetry and using machine learning models, modern tech tools can “quarantine” an unknown threat based on its actions before it has a chance to replicate across a local area network (LAN) or compromise sensitive data.
Cyber-Hygiene: Preventing the Spread in Enterprise Environments
In both biology and technology, prevention is more cost-effective than a cure. “Cyber-hygiene” refers to the routine practices and technologies that individuals and organizations use to maintain system health and prevent the “infection” of viruses and bacteria.
Patch Management as a Digital Vaccine
The most common way for digital bacteria (worms) to enter a system is through unpatched software vulnerabilities. Software companies like Microsoft, Apple, and Adobe constantly release security patches to “close the door” on potential entry points.
An unpatched system is like a person with a compromised immune system; it is susceptible to every passing threat. Robust patch management—the automated process of ensuring all software is up to date—serves as a digital vaccine, making the environment inhospitable to autonomous malware.
The Role of Zero-Trust Architecture
As the “bacteria” of the digital world become more sophisticated, the tech industry has moved toward a “Zero-Trust” model. In a traditional network, once a virus or worm gets past the outer firewall, it has free rein to move laterally. Zero-Trust changes this by assuming that every user, device, and file is a potential carrier.
By implementing micro-segmentation, organizations can ensure that even if one “cell” (a workstation) becomes infected with a virus, the “pathogen” cannot easily leap to the rest of the body (the server infrastructure). This containment strategy is the digital equivalent of an isolation ward in a hospital.
The Evolution of Malware in the AI Era
As we look toward the future of technology, the line between viruses and bacteria is blurring through the use of Artificial Intelligence. We are entering an era of “Adaptive Malware,” where malicious code can change its own structure to evade detection—a process similar to viral mutation.
AI-driven malware can study a system’s defense patterns and wait for the optimal moment to strike. These “intelligent” pathogens can remain dormant for months, acting like a latent virus, before suddenly behaving like a fast-spreading bacterium once they find a high-value target. This necessitates a shift in our tech tools from static defenses to “Active Defense” systems that use AI to fight AI.
In conclusion, while the terms virus and bacteria originate in the lab, they find a perfect home in the data center. A virus is a parasite requiring human interaction and a host file, whereas digital bacteria are autonomous, network-exploiting entities. By understanding these differences, and employing modern tools like EDR and Zero-Trust architecture, we can build a more resilient digital ecosystem that is capable of withstanding the ever-evolving pathology of the tech world.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.