In the rapidly evolving landscape of information technology, the metaphors we use to describe security are shifting from static physical barriers—like walls and moats—to dynamic biological systems. As cyber threats become more sophisticated, mirroring the behavior of biological viruses, the tech industry has looked toward immunology to build more resilient infrastructures. To understand modern digital defense, we must explore the functional differences between an “antigen” and an “antibody” within the context of cybersecurity and artificial intelligence.
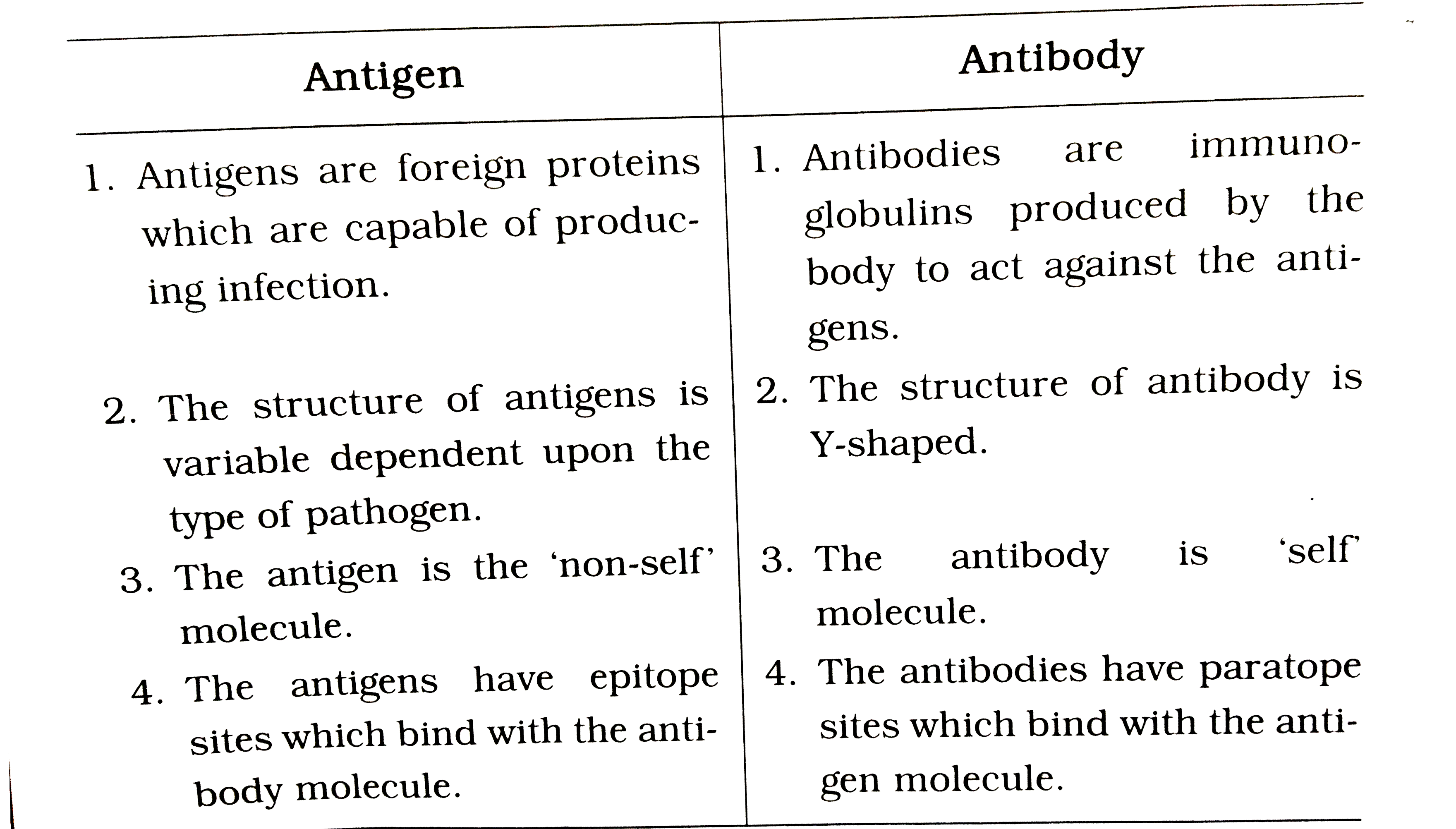
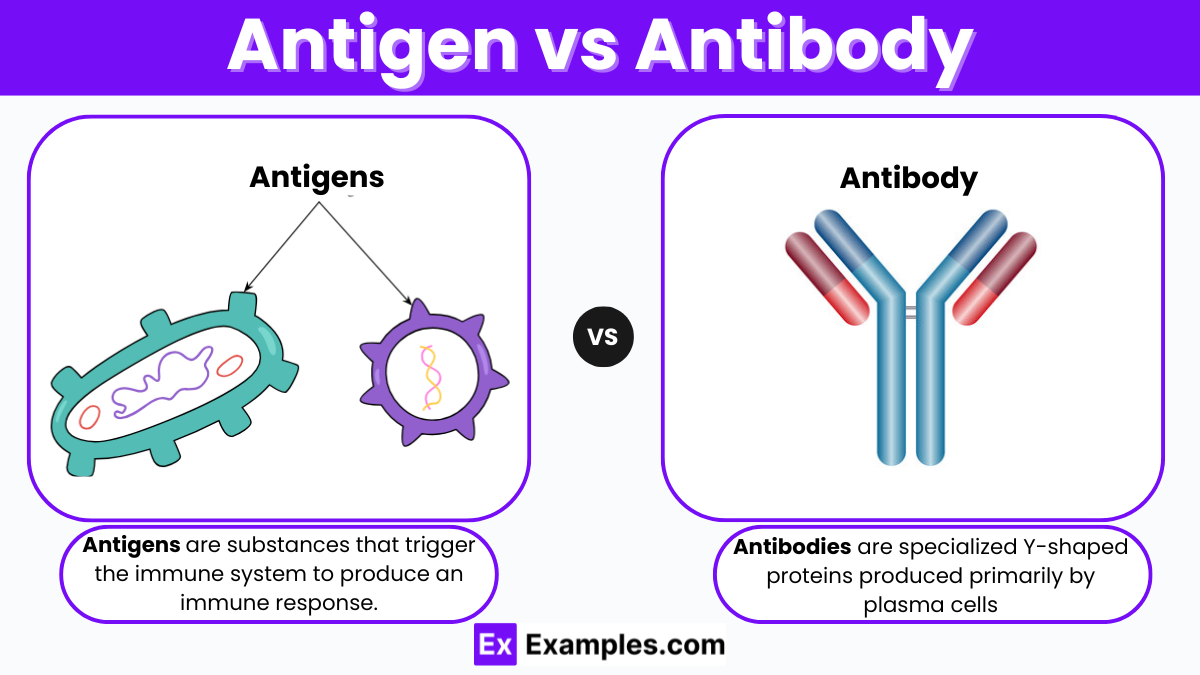
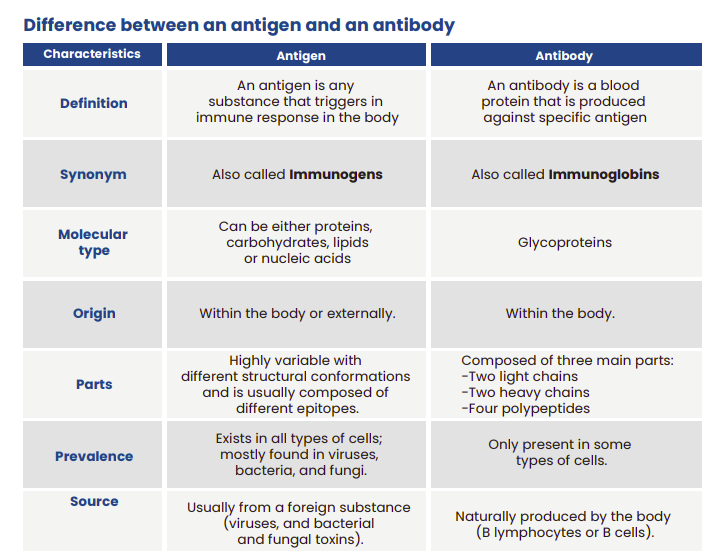
In biology, an antigen is a foreign substance that triggers an immune response, while an antibody is the protein produced to neutralize that specific threat. In the tech world, this relationship forms the basis of “Digital Immunity.” Understanding the distinction between the two is not just a matter of semantics; it is the key to mastering proactive threat hunting, automated incident response, and the future of AI-driven security.
The Biological Blueprint of Digital Defense
To grasp the difference between digital antigens and antibodies, we must first look at how they interact within a network’s ecosystem. Just as the human body is constantly bombarded by pathogens, a modern enterprise network faces thousands of “probes” and “attacks” every hour. The transition from signature-based antivirus software to behavioral AI marks our move toward a truly biological model of tech defense.
Defining the Digital Antigen: The Catalyst of a Breach
In a technological framework, a digital antigen is any signal, piece of code, or behavior that the system identifies as “non-self” or potentially harmful. It is the catalyst that forces the security stack to react. Digital antigens can take many forms:
- Malware Signatures: The specific byte sequences of a ransomware strain.
- Anomalous Traffic: A sudden spike in data egress to an unrecognized IP address in a foreign jurisdiction.
- Unauthorized Access Attempts: A series of failed logins followed by a successful one from an unusual geographic location.
- Zero-Day Vulnerabilities: Previously unknown flaws in software that act as “stealth antigens,” bypassing traditional filters because the system hasn’t learned to recognize them yet.
An antigen is fundamentally an identifier. It is the red flag that tells the system, “Something here does not belong.” However, an antigen by itself does not cause the response; rather, its recognition by the system’s sensors (SIEM, EDR, or NDR tools) triggers the countermeasure.
Defining the Digital Antibody: The Code that Protects
If the antigen is the threat, the digital antibody is the targeted solution. In cybersecurity, an antibody is a specific defensive protocol, patch, or automated script designed to neutralize a detected antigen. Unlike a general firewall (which acts more like the skin—a primary, non-specific barrier), a digital antibody is highly specific.
Digital antibodies manifest as:
- Automated Response Scripts: If an “antigen” (unauthorized data movement) is detected, the “antibody” (SOAR protocol) automatically isolates the affected server.
- Patch Management: A software update designed specifically to close a hole exploited by a specific virus.
- Encryption Keys: Specific cryptographic defenses that render stolen data (the antigen’s goal) useless to the attacker.
The primary difference lies in their roles: the antigen is the problem (the intruder), and the antibody is the encoded intelligence used to stop that specific problem.
How AI Replicates the Adaptive Immune System
The most significant advancement in modern tech is the move from “Innate Immunity” (basic firewalls) to “Adaptive Immunity” (Machine Learning). In humans, the adaptive immune system “remembers” past infections to fight them better in the future. In technology, we achieve this through AI-driven threat intelligence.
Machine Learning as the “Memory Cell”
In biology, memory B-cells store the information needed to create antibodies quickly if a pathogen returns. In the tech niche, Machine Learning (ML) models serve this exact purpose. When a new strain of polymorphic malware (an antigen that changes its code to avoid detection) enters a network, AI tools analyze its behavior rather than its literal “appearance.”
Once the AI identifies the malicious intent, it creates a “behavioral fingerprint.” This fingerprint is stored in the cloud-based threat database. This is the digital equivalent of developing long-term immunity. The next time any variation of that antigen appears—even if its code is 90% different—the AI “antibodies” recognize the underlying pattern and neutralize it instantly.
Pattern Recognition vs. Signature-Based Detection
The core difference between old-school tech and modern AI-driven systems lies in how they distinguish antigens from antibodies.
- Signature-Based (Static): This is like an immune system that only recognizes a virus if it looks exactly like a picture in a textbook. If the virus wears a hat (slight code obfuscation), the system fails.
- Heuristic/Behavioral (Dynamic): This is modern tech immunity. It doesn’t look at what the antigen is; it looks at what the antigen does. If a file starts encrypting directories at lightning speed, the system identifies it as a threat. The “antibody” generated is an immediate suspension of the process and a rollback to the last known healthy state.
Strategies for Building a Robust Digital Immune System
For CTOs and IT professionals, distinguishing between antigens and antibodies allows for a more structured approach to “Cyber Resilience.” Instead of trying to block every possible antigen—which is impossible—the focus shifts to building a more versatile library of antibodies.
Threat Hunting: Proactive Antibody Generation
Traditional security is reactive: wait for an antigen to appear, then build an antibody. Proactive “Threat Hunting” flips this script. Tech teams use “Red Teaming” (simulated attacks) to introduce “controlled antigens” into their own systems.
This is essentially a digital vaccine. By simulating a breach, the organization forces its security team to develop the necessary antibodies—incident response plans, firewall rules, and communication protocols—before a real-world threat ever arrives. This ensures that when a real antigen strikes, the “memory cells” of the organization are already prepared to respond.
Zero Trust Architecture: The Cellular Membrane of the Network
In biology, every cell has a membrane that regulates what enters and exits. In Tech, the “Zero Trust” model applies this to every user and device. In a Zero Trust environment, everything is treated as a potential antigen until proven otherwise.
- Continuous Authentication: Every request is a potential threat (antigen).
- Micro-segmentation: Even if an antigen breaches the outer perimeter, it is contained within a small “cell” of the network, preventing it from spreading (lateral movement).
- Least Privilege Access: Only the “antibodies” (authorized users/processes) necessary for a specific function are allowed to interact with sensitive data.
This strategy shifts the focus from the “periphery” to the “individual data point,” creating a much more granular and effective immune response.
The Future of Autonomous Cybersecurity: Self-Healing Systems
As we look toward the future of technology, the line between detecting an antigen and deploying an antibody is blurring. We are entering the era of “Self-Healing Infrastructure,” where the system acts autonomously without human intervention.
From Detection to Neutralization
The time between the detection of an antigen and the deployment of an antibody is known as “dwell time.” In the past, dwell time was measured in weeks or months. In the modern tech landscape, AI has reduced this to milliseconds.
Self-healing systems use “Digital Twins”—virtual replicas of the network—to test antibody responses in real-time. If an antigen is detected in the live environment, the AI tests multiple defensive scripts on the Digital Twin to see which one neutralizes the threat most effectively without crashing the system. Once the optimal “antibody” is found, it is deployed to the live network.
The Risks of Overactive Digital Immunity (False Positives)
Just as a human immune system can sometimes overreact and cause an autoimmune disease (attacking its own healthy cells), a digital immune system can suffer from “False Positives.” If a security AI is too aggressive, it may identify a legitimate software update or a busy employee as a “digital antigen.”
When this happens, the “antibodies” (security blocks) can inadvertently shut down business operations, causing self-inflicted downtime. The challenge for the next generation of Tech and AI tools is “tuning”—finding the perfect balance where the system is sensitive enough to catch every antigen but intelligent enough to recognize its own “self” code.
Conclusion
The difference between an antigen and an antibody is the difference between the challenge and the solution. In the world of technology, antigens are the ever-evolving threats—the exploits, the social engineering, and the malware—that seek to disrupt our digital lives. Antibodies are the innovation, the encryption, the AI models, and the strategic frameworks we build to neutralize those threats.
By adopting a biological mindset toward cybersecurity, organizations can move beyond the “fortress” mentality. Instead of building higher walls, they can build smarter systems—networks that learn, adapt, and grow stronger with every attack. In the digital age, survival belongs not to the strongest, but to the most adaptive. As we refine our digital antibodies, we pave the way for a more secure, resilient, and autonomous technological future.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.