In an era where our physical lives are inextricably linked to our digital identities, the concept of security has evolved far beyond locks and alarms. As we migrate our social interactions, professional collaborations, and personal memories to the cloud, a new breed of threat has emerged: cyberstalking. Often misunderstood as a mere nuisance or a series of unwelcome social media interactions, cyberstalking is a sophisticated and dangerous form of digital harassment. From a technological perspective, it represents a systematic breach of privacy and a misuse of digital tools to exert control, instill fear, or humiliate an individual. Understanding what is considered cyberstalking is the first step in fortifying our digital defenses and reclaiming our right to a secure online existence.
Defining Cyberstalking in the Digital Age
At its core, cyberstalking is the use of the internet, email, or other electronic communications devices to stalk or harass an individual. However, the technical definition is often more nuanced, involving a pattern of behavior rather than a single isolated incident. In the realm of digital security, it is classified as a targeted attack on an individual’s privacy and psychological well-being.
The Transition from Physical to Digital Harassment
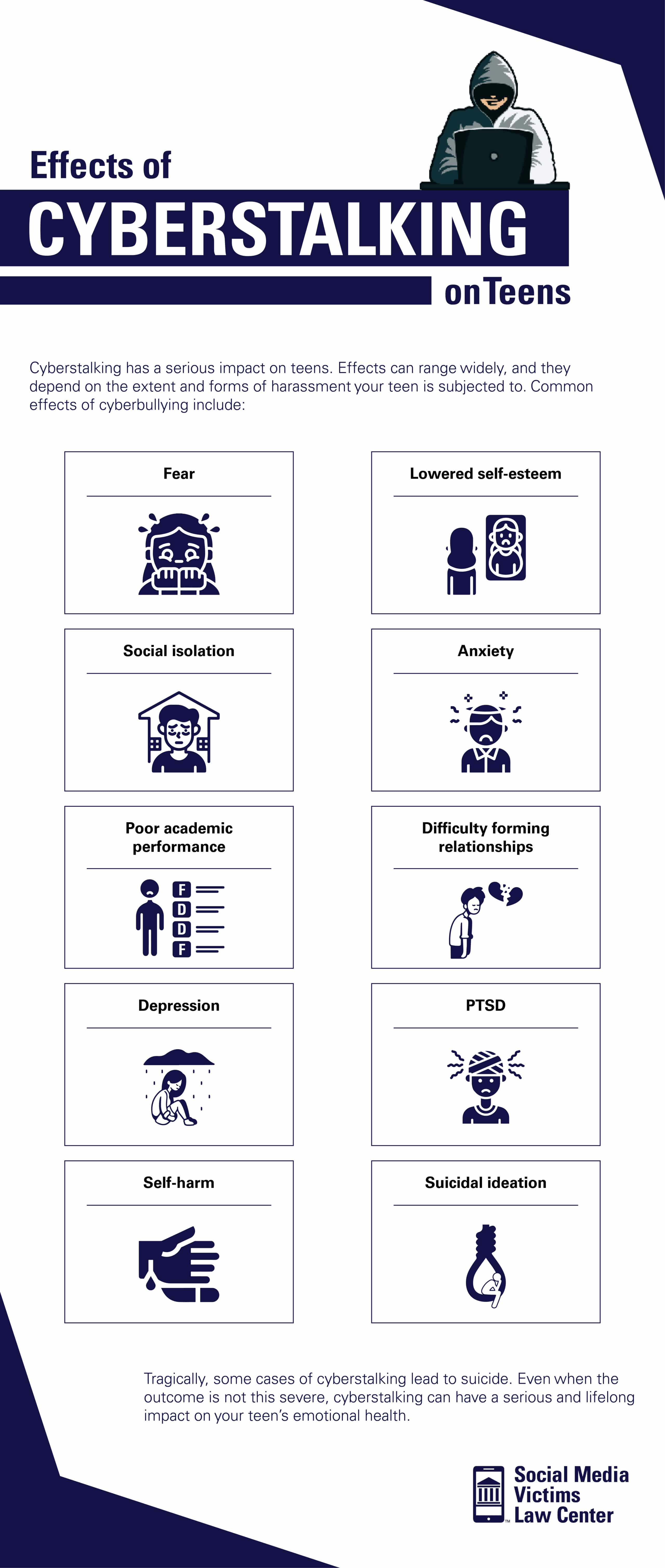
Historically, stalking required physical proximity. The advent of high-speed internet and ubiquitous mobile connectivity has removed this barrier. A cyberstalker can be thousands of miles away yet remain more invasive than a physical shadow. This transition is characterized by the “always-on” nature of modern technology. Where a victim could once find sanctuary within their home, the digital world ensures that the harasser can reach them through their pocketed devices at any hour. This constant accessibility is what makes cyberstalking a unique challenge for cybersecurity experts and law enforcement alike.
Key Components of Cyberstalking Behavior
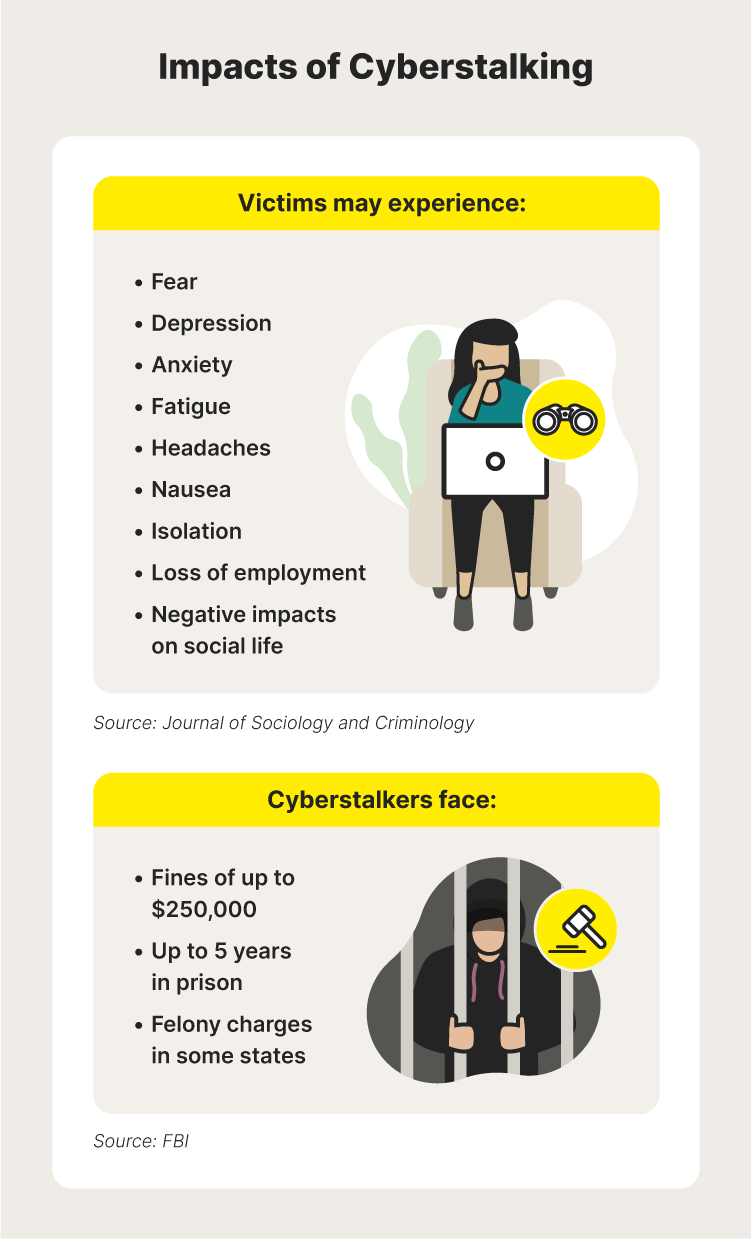
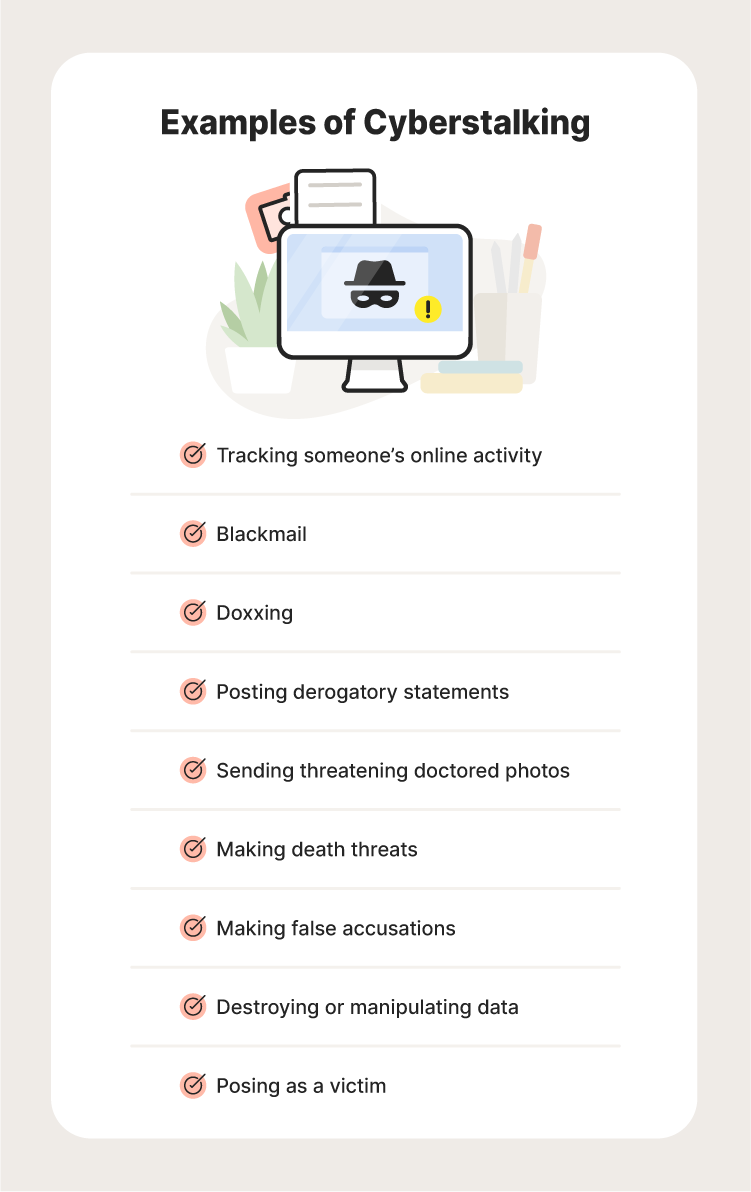
To distinguish cyberstalking from general online rudeness or “trolling,” experts look for specific technological markers. These include persistence, intent to cause distress, and the bypass of privacy boundaries. Activities often include monitoring a victim’s online activity, harvesting their metadata to determine their location, sending threatening messages, or spreading false information across digital platforms. When a user’s “digital exhaust”—the trail of data left behind by everyday activities—is weaponized against them, the threshold of cyberstalking has been crossed.
The Technological Tools of Cyberstalking
The sophistication of cyberstalking is often a reflection of the tools available in the current tech landscape. While many of these tools were designed for legitimate purposes, such as parental monitoring or device recovery, they are frequently repurposed by malicious actors.
Stalkerware and Invasive Monitoring Apps
One of the most insidious developments in digital harassment is the rise of “stalkerware.” These are software programs installed on a victim’s device without their knowledge or consent. Once active, stalkerware can grant an attacker total access to the victim’s smartphone or computer. This includes the ability to read private messages, intercept phone calls, view browsing history, and even activate the camera or microphone remotely. Because these apps often operate in “stealth mode,” hiding their icons from the home screen and evading basic antivirus scans, they represent a significant breach of mobile security protocols.
Social Media Exploitation and Data Scraping
Social media platforms are the primary hunting grounds for cyberstalkers. Through techniques like data scraping—using automated scripts to harvest personal information—a stalker can compile a comprehensive profile of a victim. This profile might include their place of employment, frequent hangouts, and the names of family members. Even when privacy settings are high, “catfishing” (creating fake personas) or “social engineering” can be used to infiltrate a victim’s inner circle. The technical ease with which an individual can create dozens of burner accounts allows a stalker to bypass blocks and continue their harassment indefinitely.
IoT Devices and Smart Home Vulnerabilities
As we move toward a fully integrated “Internet of Things” (IoT), the surfaces for cyberstalking attacks have expanded. Smart doorbells, thermostats, and security cameras are designed for convenience, but if their security is lax, they can be hijacked. A cyberstalker with access to a victim’s smart home ecosystem can track when they arrive home, control their lights, or even watch them through their own security feeds. This convergence of hardware and software vulnerabilities creates a high-stakes environment where digital security becomes a prerequisite for physical safety.
Identifying the Signs of Online Harassment
Identifying cyberstalking early is essential for mitigating damage. Because many stalking techniques are designed to be covert, users must be vigilant regarding the behavior of their hardware and the integrity of their digital accounts.
Unexplained Digital Presence and Communication
One of the first red flags of cyberstalking is the “unexplained presence.” This occurs when a harasser reveals information that they could not have known through legitimate means. For example, if an individual receives a message regarding a private conversation they had via a supposedly encrypted app, it suggests that their device or account has been compromised. Similarly, receiving a high volume of unsolicited communications across multiple platforms—email, LinkedIn, Instagram, and gaming forums—indicates a persistent and coordinated effort to penetrate the victim’s digital life.
Compromised Personal Accounts and Privacy Leaks
Cyberstalkers often attempt to gain control over a victim’s digital identity. This may manifest as frequent password reset notifications, unauthorized logins from unrecognized IP addresses, or the sudden appearance of “private” photos or documents on public forums (doxing). Technical indicators also include rapid battery drain on mobile devices or unexpected data usage spikes, which can suggest that unauthorized monitoring software is running in the background and transmitting data to a remote server.
Strengthening Your Digital Defense Strategy
Protecting oneself from cyberstalking requires a proactive approach to digital hygiene. It is not enough to simply delete a profile; one must harden their entire digital ecosystem.
Multi-Factor Authentication (MFA) and Robust Password Management
The first line of defense is securing the gateway to your accounts. Utilizing Multi-Factor Authentication (MFA) is non-negotiable in the modern tech landscape. By requiring a physical token or a biometric scan in addition to a password, MFA makes it significantly harder for a stalker to gain unauthorized access, even if they have successfully phished a password. Furthermore, using a reputable password manager ensures that every account has a unique, high-entropy password, preventing the “domino effect” where one compromised account leads to the breach of all others.
Privacy Settings and Digital Footprint Minimization
Users should conduct regular “privacy audits” of their social media and cloud services. This involves restricting post visibility to “Friends Only,” disabling “Geotagging” on photos, and reviewing which third-party applications have access to your data. Minimizing your digital footprint—the amount of personal information publicly searchable—is crucial. This might include using “Googling yourself” to see what information is available and utilizing tools to request the removal of personal data from “people-search” websites and data brokers.
Legal Recourse and Technical Documentation
When cyberstalking occurs, documentation is the most important technical asset. Victims should avoid deleting harassing messages or accounts immediately. Instead, they should take screenshots that include timestamps, headers, and any identifying metadata. From a legal and forensic standpoint, this data is essential for identifying the perpetrator’s IP address and building a case for law enforcement. Many jurisdictions now have specific cybercrime units equipped to handle the technical nuances of these investigations.
The Future of Digital Privacy and Protective Tech
As cyberstalking tactics evolve, so too must the technologies designed to combat them. The tech industry is currently seeing a shift toward privacy-by-design, where security features are baked into software from the ground up.
AI-Driven Detection Systems
Artificial Intelligence (AI) is playing an increasingly vital role in identifying stalking patterns. Modern security software can now use behavioral analytics to detect “anomalous” activity—such as a login attempt from a suspicious location or a script attempting to scrape a profile. Some social media platforms are implementing AI that can recognize and shadow-ban accounts that exhibit “stalker-like” behavior, such as creating multiple accounts to contact a single user who has blocked them.
The Role of Cybersecurity Regulations
Legislation is beginning to catch up with technological reality. New regulations are holding software developers accountable for “dual-use” apps that facilitate stalking. In the future, we can expect stricter requirements for encryption and data anonymity, as well as more robust protections for IoT devices. By treating cyberstalking as a top-tier cybersecurity threat, the industry can create a safer digital environment where users can engage with technology without fear of exploitation.
In conclusion, cyberstalking is a multifaceted digital threat that requires a sophisticated technological response. By understanding the tools used by harassers—from stalkerware to IoT exploitation—and implementing rigorous digital security measures, individuals can protect their privacy and well-being. The battle against cyberstalking is not just a legal one; it is a technical challenge that demands constant vigilance, better software design, and a commitment to maintaining the integrity of our digital lives.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.