In the vast, interconnected landscape of the 21st century, every interaction we have with a machine, a website, or a cloud-based application begins with a fundamental question of identity. At the heart of this interaction lies the “UserID.” While it may seem like a simple string of characters entered during a login process, the UserID is actually the cornerstone of modern computing architecture, digital security, and personalized user experiences.
In this comprehensive guide, we will explore the technical nuances of the UserID, its role in database management, its critical importance in cybersecurity, and how it is evolving in an era of decentralized technology.

1. Defining the UserID in the Modern Digital Ecosystem
At its most basic level, a UserID (User Identification) is a unique string of characters used by a computing system to identify a specific entity. This entity is usually a human being, but it can also represent a “service account” or a bot designed to perform automated tasks.
The Core Concept: Unique Identification
The primary function of a UserID is uniqueness. Within any given system—whether it is a local operating system like Windows or a global platform like Google—no two entities can share the same UserID. This uniqueness ensures that the system can accurately attribute actions, files, and permissions to the correct individual. Without this foundational element, the digital world would collapse into a chaotic state where data becomes untraceable and privacy is non-existent.
UserID vs. Username: Understanding the Nuance
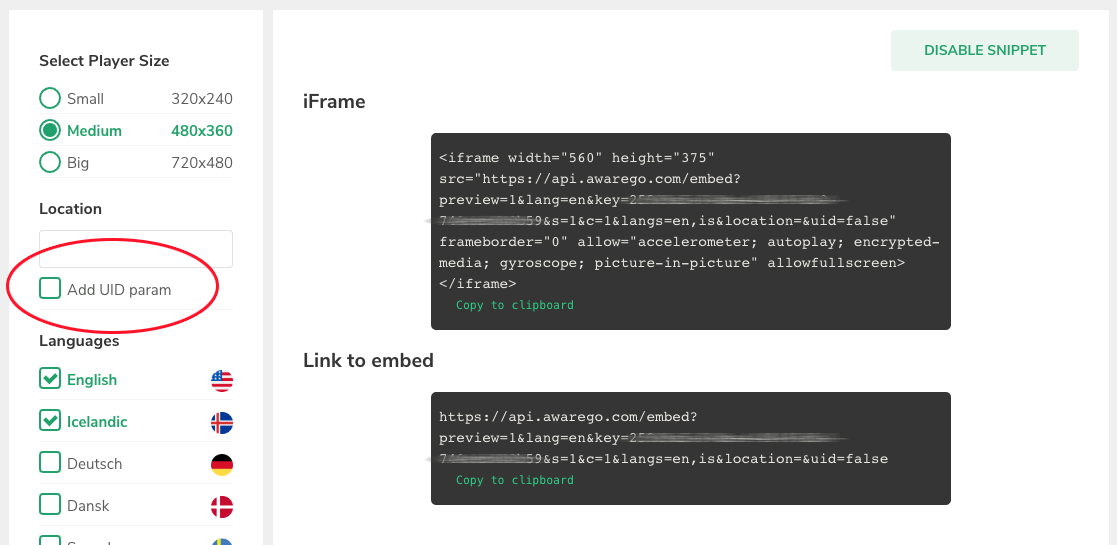
In common parlance, “UserID” and “username” are often used interchangeably, but in technical architecture, they often represent different layers. A username is typically a human-readable identifier (e.g., “TechGuru88”) that a user chooses for themselves. A UserID, however, is often a system-generated numeric or alphanumeric code (e.g., “550e8400-e29b-41d4-a716-446655440000”) that remains constant even if the user changes their display name or email address. This underlying ID is what the database uses to link tables and maintain record integrity.
The Role of UserIDs in Database Management
From a developer’s perspective, the UserID functions as a “Primary Key.” When you interact with an application, your data is not stored in one giant file. Instead, it is spread across dozens of relational database tables—one for your profile information, one for your security settings, and another for your activity logs. The UserID is the glue that binds these tables together. By querying a specific UserID, the system can instantly aggregate all relevant data points to present a cohesive experience to the end-user.
2. Technical Architectures and Implementation
The way a UserID is generated and managed depends heavily on the scale and purpose of the software. Engineers must choose between different formats to balance performance, security, and scalability.
Primary Keys and GUIDs/UUIDs
In small-scale applications, developers might use simple incremental integers (User 1, User 2, User 3) as IDs. However, modern, distributed systems require something more robust. This is where UUIDs (Universally Unique Identifiers) or GUIDs (Globally Unique Identifiers) come into play. A UUID is a 128-bit label that is essentially guaranteed to be unique across all space and time. Because these IDs are generated using complex algorithms involving timestamps and hardware addresses, two systems can generate UUIDs independently without the risk of a “collision” (two users having the same ID).
Email-based Identification
Many modern SaaS (Software as a Service) platforms have moved toward using email addresses as the primary UserID. This simplifies the user experience, as users do not have to remember a separate username. Technically, however, this presents challenges. If a user changes their email address, the system must either update all linked records or maintain a hidden, immutable internal ID while using the email merely as a login alias. Most high-level architectures prefer the latter to ensure data persistence.
Federated Identity and Single Sign-On (SSO)
In the corporate tech world, we are seeing a shift away from isolated UserIDs toward Federated Identity. Through protocols like SAML (Security Assertion Markup Language) and OpenID Connect, a single UserID can grant access to multiple independent systems. When you “Sign in with Google” on a third-party app, you are utilizing a federated identity. The third-party app receives a unique identifier from Google that confirms who you are without the app ever needing to store its own version of your credentials.
3. The Crucial Role of UserIDs in Digital Security
The UserID is the first line of defense—and the first point of attack—in the realm of cybersecurity. It is the “identity” component of the “Identity and Access Management” (IAM) framework.
Authentication vs. Authorization
Understanding UserIDs requires understanding the difference between authentication and authorization.
- Authentication is the process of verifying that you are who you say you are (usually via the UserID and a password).
- Authorization happens after the ID is verified. The system looks at the UserID and checks the “Access Control List” (ACL) to see what that specific ID is allowed to do.
For example, a UserID belonging to an “Admin” has different authorization levels than a UserID belonging to a “Guest,” even though both have been successfully authenticated.
Securing the Identity Layer: Multi-Factor Authentication (MFA)
Because a UserID is often public or easily guessed (like an email), security cannot rely on the ID alone. This has led to the rise of MFA. In this setup, the UserID acts as the “claim” of identity, while the password and a secondary factor (like a hardware security key or a biometric scan) act as the “proof.” Even if a malicious actor discovers a UserID, they cannot bypass the security layer without the secondary proofs.
Preventing Identity Hijacking and Credential Stuffing
Cybercriminals often use “Credential Stuffing” attacks, where they take lists of leaked UserIDs and passwords from one site and try them on others. To combat this, tech companies use sophisticated monitoring on UserIDs. If a specific ID attempts to log in from three different continents within an hour, the system’s AI tools flag the activity as “impossible travel” and temporarily lock the ID to protect the user’s data.
4. Best Practices for Developing and Managing UserIDs
For software engineers and IT professionals, designing a UserID system requires foresight. Mistakes made at the architectural level can lead to massive data migrations or security vulnerabilities later on.
Privacy by Design: Avoiding PII in IDs
A critical best practice in modern tech is “Privacy by Design.” Developers should avoid using Personally Identifiable Information (PII)—such as Social Security numbers or full legal names—as the underlying UserID. If a database is breached, having an ID like “User9921″ is much safer than “JohnDoe_12345.” By using “opaque” IDs (random strings), organizations can limit the amount of sensitive data exposed during a security incident.
Scalability and Persistence
A UserID should be immutable. Once an ID is assigned to a user, it should never change. If a system allows the internal ID to change (for instance, if it’s tied to a username that the user can edit), it can break the links to historical data, logs, and purchased digital goods. A robust system ensures that the internal pointer remains the same for the entire lifecycle of the account.
User Experience (UX) Considerations
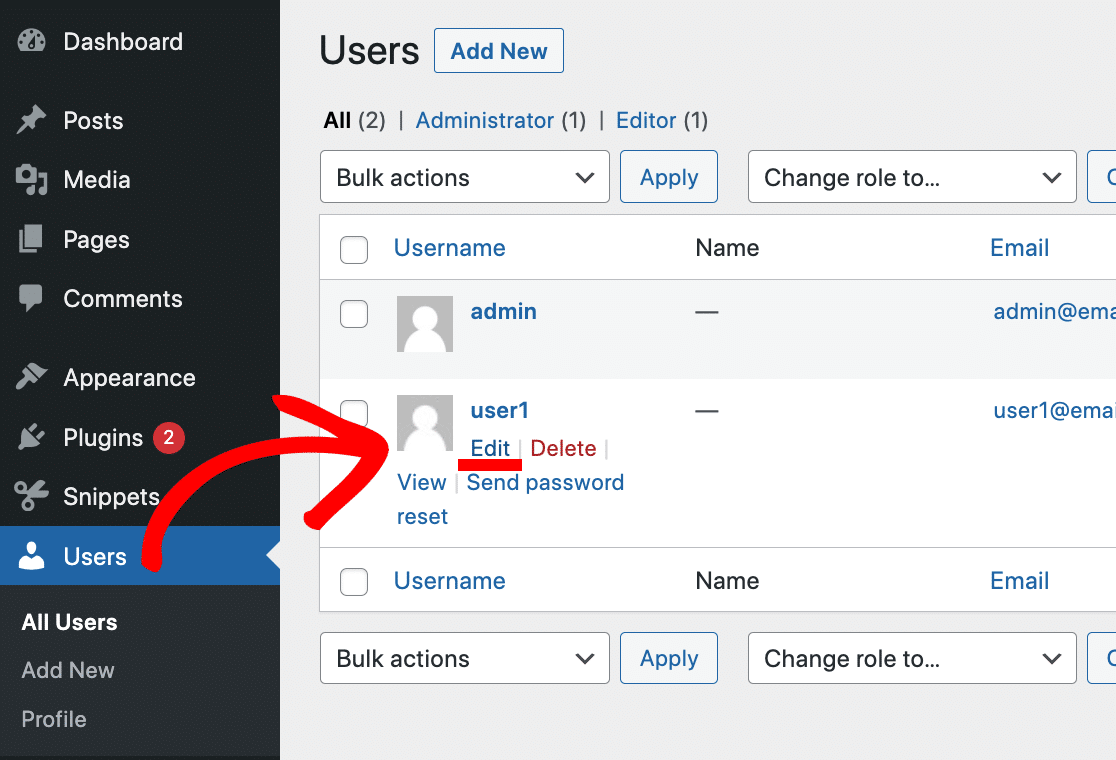
While the back-end needs complex IDs, the front-end should be user-friendly. Tech companies often separate the “Internal ID” (used by the database) from the “Public ID” (what other users see). For example, on platforms like Discord, users have a display name, but their true identity is managed by a “Snowflake ID”—a unique, time-sorted identifier that ensures the system handles millions of messages per second without error.
5. The Future of Identification: Beyond the Standard UserID
As we look toward the future of technology, the concept of the UserID is undergoing a radical transformation, moving away from centralized servers toward more user-centric models.
Biometric Integration and the Passwordless Future
The tech industry is rapidly moving toward a “passwordless” environment. In this scenario, your UserID is no longer tied to a secret string of text, but to a cryptographic key stored on your device and unlocked by your biometrics (FaceID or fingerprints). Protocols like FIDO2 allow your device to prove your identity to a server without ever sending your biometric data over the internet, making the UserID more secure than ever before.
Decentralized Identity (DID) and Blockchain
Perhaps the most significant trend in the “Tech” niche today is Decentralized Identity (DID). Currently, your digital identity is owned by giant corporations (Google, Meta, Amazon). If they delete your account, you lose your UserID and all associated data.
With DID, built on blockchain technology, the UserID belongs to the individual. You hold a “digital wallet” containing “Verifiable Credentials.” When you need to log into a service, you provide a cryptographic proof of your identity. In this model, the UserID is not stored in a company’s database; rather, the company simply “verifies” the ID that you present. This shifts the power dynamics of the internet, providing greater privacy and giving users total control over their digital footprint.
Conclusion
The UserID is far more than a simple login credential; it is the fundamental unit of the digital world. It enables the complex databases that power our favorite apps, provides the framework for global cybersecurity, and serves as the primary link between a human being and their digital life. As we move into an era of AI and decentralization, the way we define and protect our UserIDs will determine the future of privacy and security in the digital age. Understanding the technical depth behind those few characters on a login screen is the first step in mastering the modern technological landscape.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.