In the rapidly evolving landscape of digital transformation, the perimeter of the traditional enterprise has dissolved. As organizations migrate to the cloud, adopt remote work models, and integrate a plethora of SaaS applications, the primary focus of cybersecurity has shifted from protecting the network to protecting the “identity.” This shift has brought a specific discipline to the forefront of IT strategy: Identity Governance.
Identity Governance, often referred to as Identity Governance and Administration (IGA), is the policy-based centralized orchestration of user identity management and access control. It ensures that the right individuals have the right access to the right resources at the right time—and, perhaps most importantly, for the right reasons. This article explores the intricate world of IGA, its role in modern technology stacks, and why it has become the bedrock of digital security and compliance.

Understanding the Pillars of Identity Governance and Administration (IGA)
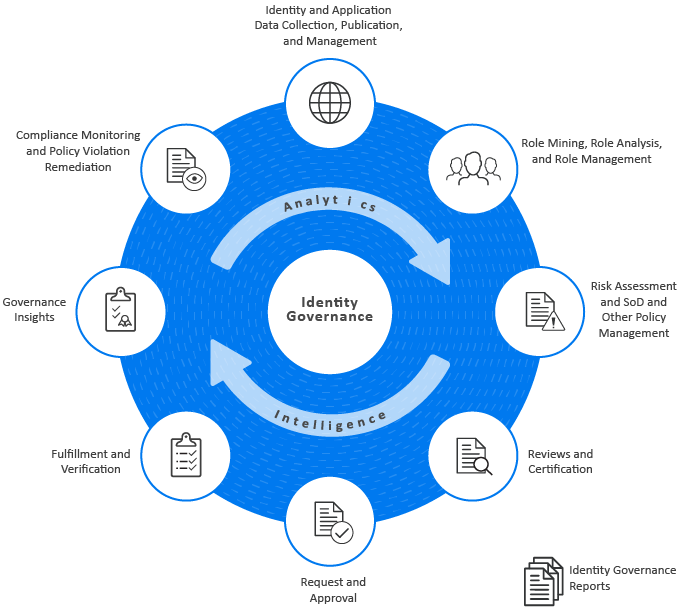
To understand identity governance, one must first distinguish it from its broader parent category, Identity and Access Management (IAM). While IAM is the overarching framework for managing digital identities, IGA provides the “intelligence” and “oversight” layer.
The Critical Difference Between IAM and IGA
Standard IAM systems are designed to facilitate access. They handle the technical aspects of authentication (logging in) and authorization (granting permission). However, they often lack the visibility to answer the “who, what, where, and why” over a long period.
IGA fills this gap by adding a layer of transparency and accountability. While IAM might grant a user access to a database, IGA asks: “Does this user still need this access? Was this access approved by a manager? Does this access violate any internal policies?” In essence, IAM is the lock and the key, while IGA is the security audit that ensures only authorized personnel hold those keys.
The Lifecycle of a Digital Identity: Joiners, Movers, and Leavers
At the heart of IGA is the management of the identity lifecycle. Digital identities are not static; they evolve as individuals progress through an organization. IGA frameworks typically manage three primary phases:
- Joiners: When a new employee or contractor joins, IGA tools automatically provision the necessary accounts and permissions based on their role. This ensures productivity from day one without over-provisioning.
- Movers: When an employee changes departments or receives a promotion, their access needs change. IGA ensures that old permissions are revoked (to prevent “access creep”) and new ones are granted.
- Leavers: When an individual leaves the organization, IGA triggers an immediate de-provisioning process. This is a critical security step, as “orphaned accounts”—active accounts belonging to former employees—are a prime target for cybercriminals.
Why Identity Governance is Critical in the Modern Enterprise
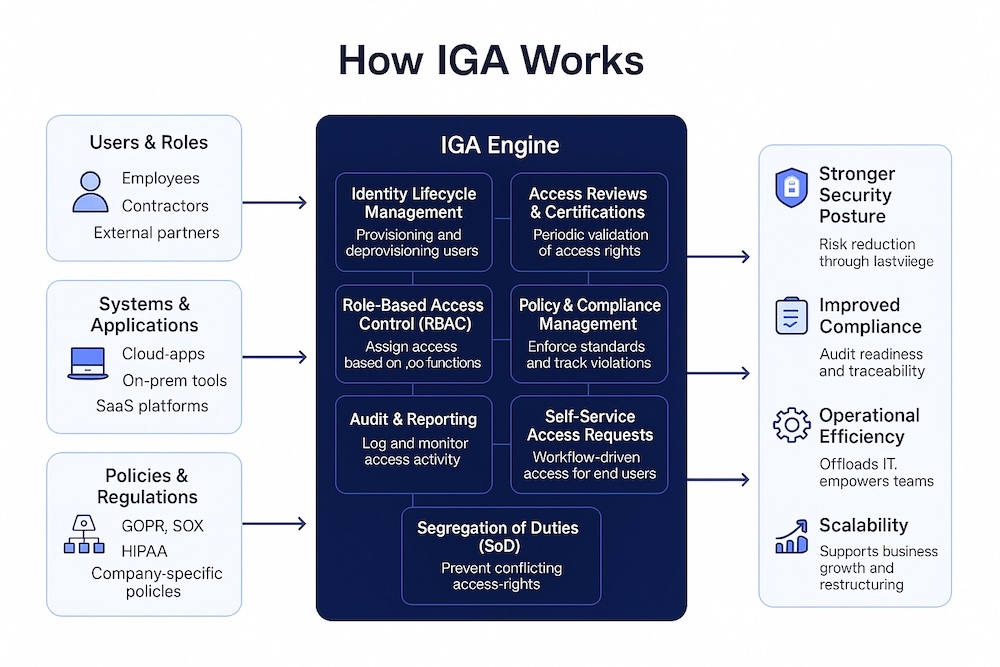
The modern tech environment is a complex web of on-premise servers, cloud platforms (AWS, Azure, Google Cloud), and hundreds of third-party applications. Without a centralized governance strategy, this complexity becomes a significant liability.
Mitigating Insider Threats and Cyber Attacks
Data breaches are rarely the result of high-tech “hacking” in the cinematic sense; instead, they often involve the exploitation of compromised credentials or excessive privileges. If an entry-level employee has administrative access to a sensitive financial server, a single phishing attack on that employee can lead to a catastrophic breach.
Identity Governance enforces the “Principle of Least Privilege” (PoLP). By ensuring that every user has only the minimum level of access required to perform their job, IGA significantly shrinks the “attack surface.” Even if a credential is stolen, the damage is contained because the identity’s permissions are strictly governed and monitored.
Navigating Complex Regulatory Compliance
For businesses operating in the digital age, compliance is not optional. Frameworks such as the General Data Protection Regulation (GDPR), the Health Insurance Portability and Accountability Act (HIPAA), and the Sarbanes-Oxley Act (SOX) demand rigorous controls over data access.
IGA provides the “proof” that auditors require. It generates detailed reports and audit trails showing who has access to sensitive data and proving that access is regularly reviewed. Without an automated IGA solution, providing this documentation manually is an expensive, error-prone, and time-consuming process that risks heavy fines and legal repercussions.
Key Components and Best Practices for Implementation
Implementing an IGA strategy is not merely a matter of installing software; it requires a cultural shift in how an organization views security and data ownership.
Role-Based Access Control (RBAC) and Attribute-Based Access Control (ABAC)
One of the most effective ways to govern identity is through Role-Based Access Control (RBAC). In this model, permissions are tied to job functions rather than individuals. For example, every “Marketing Manager” is automatically granted access to the social media dashboard and the CRM.
For more granular control, organizations are increasingly turning to Attribute-Based Access Control (ABAC). This model considers variables like the user’s location, the device they are using, and the time of day. For instance, an employee might have access to a secure server while in the office on a company laptop but be blocked when trying to access it from a public Wi-Fi network in another country.
Automated Provisioning and De-provisioning
Manual provisioning is the enemy of security. When IT teams have to manually create accounts for every new hire, mistakes happen. Access is often duplicated from another user, leading to “privilege inheritance” where users end up with more power than they need.
Advanced IGA tools integrate directly with Human Resources Information Systems (HRIS). When HR updates an employee’s status to “Active” or “Terminated,” the IGA system automatically orchestrates the creation or deletion of accounts across the entire tech ecosystem. This automation reduces human error and ensures that security policies are applied consistently.
Continuous Auditing and Access Certification Campaigns
Access “creep” is a phenomenon where users accumulate permissions over years of service, eventually possessing a dangerous level of access. To combat this, IGA introduces “Access Certification Campaigns.”
These are periodic reviews where managers or data owners are required to verify that their subordinates still require specific permissions. If a manager fails to certify a permission, the IGA system can automatically revoke it. This proactive “spring cleaning” of permissions ensures that the digital environment remains lean and secure.
The Future of IGA: AI, Machine Learning, and Cloud Integration
As we look toward the future of technology, the sheer volume of data and identities is surpassing human management capabilities. The next generation of Identity Governance is being shaped by artificial intelligence and the specific needs of cloud-native environments.
Predictive Analytics and AI-Driven Governance
The integration of Artificial Intelligence (AI) and Machine Learning (ML) into IGA tools is a game-changer. AI can analyze patterns of access across thousands of users to identify anomalies. For example, if an AI detects that a user is accessing files they haven’t touched in three years, or if their access patterns significantly deviate from their “peer group” (others with the same role), it can flag the account for an immediate security review.
Furthermore, AI can assist in “Role Mining.” It can look at existing access patterns to suggest new, more efficient roles, helping organizations refine their RBAC models without months of manual analysis.
Scaling Governance for Hybrid and Multi-Cloud Environments
The rise of “Microservices” and “Containers” (like Docker and Kubernetes) has introduced a new type of identity: the non-human identity. Bots, service accounts, and API keys now outnumber human users in many tech organizations.
Modern IGA must extend its governance to these non-human entities. Ensuring that a cloud-based application has the correct permissions to talk to a database—and no more—is just as vital as managing a human’s password. As organizations continue to embrace multi-cloud strategies, the ability of an IGA platform to provide a “single pane of glass” view across different cloud providers will be the defining factor of its success.
Conclusion
Identity Governance is no longer just a niche IT requirement; it is a fundamental pillar of modern digital business. By shifting the focus from the network perimeter to the individual identity, IGA provides the security, visibility, and compliance necessary to operate in an increasingly hostile and complex digital world.
For organizations looking to scale, IGA offers the automation needed to manage growth without sacrificing security. For those in highly regulated industries, it offers the peace of mind that comes with audit-readiness. As technology continues to advance, the governance of digital identities will remain the most critical line of defense in protecting an organization’s most valuable asset: its data. In the era of the cloud, identity is the new perimeter—and governance is the gatekeeper.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.