In the intricate world of biological systems, a sphincter acts as a precise gatekeeper, ensuring that substances move in one direction and only at the appropriate time. In the realm of enterprise technology and high-scale software architecture, we encounter a strikingly similar phenomenon. The modern “system sphincter”—often manifested as an API gateway, a load balancer, or a security firewall—must decide instantaneously when to open and allow data to flow and when to remain firmly shut to protect the integrity of the internal environment.
Understanding what event triggers the opening of these digital gateways is essential for any technologist, developer, or systems architect. Just as a biological system relies on chemical and mechanical signals, a digital ecosystem relies on a complex hierarchy of automated triggers, security handshakes, and event-driven protocols. This article explores the technical mechanics behind these triggers and how they facilitate the seamless movement of data across global networks.
1. The Architecture of Flow: Defining the Digital Gatekeeper
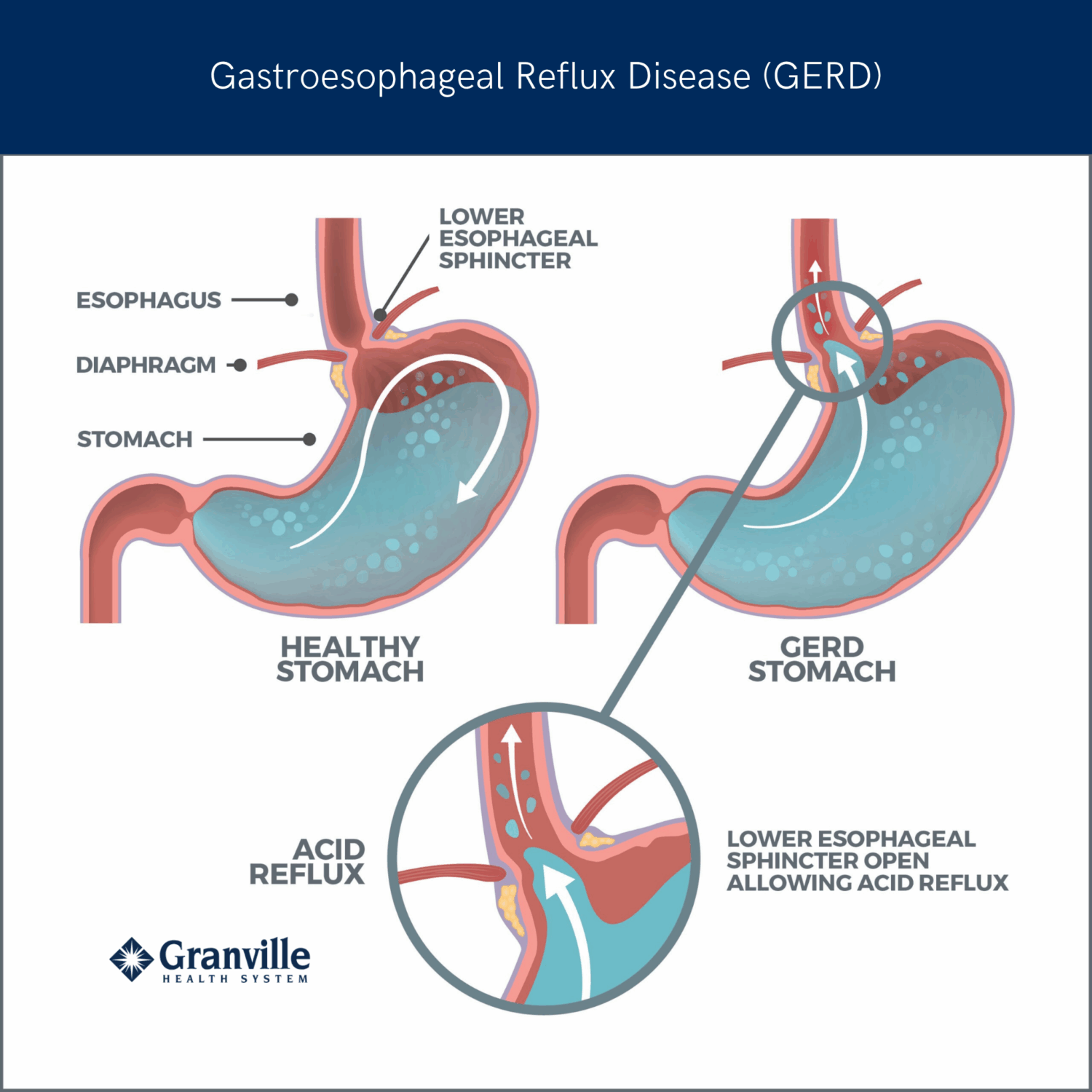
To understand the triggers, we must first define the structure. In a microservices architecture, the “gastroesophageal sphincter” of the system is the API Gateway. This single entry point acts as a buffer between the chaotic public internet (the “external environment”) and the sensitive internal microservices (the “internal organs”).
The Role of the API Gateway
The API Gateway is responsible for request routing, composition, and protocol translation. When a user interacts with a mobile app, their request doesn’t go straight to a database. It hits the gateway first. The “opening” of this gateway is not a binary switch but a sophisticated validation process.
Load Balancers as Pressure Valves
While the gateway handles the type of data, the Load Balancer handles the volume. In high-traffic environments, these systems act as pressure valves. When internal “pressure”—measured by CPU usage or memory consumption—reaches a certain threshold, the load balancer triggers the opening of new “valves” (spinning up new server instances) to distribute the load and prevent a system-wide collapse.
Defining the “Event” in Tech
In technology, an “event” is any identifiable occurrence that has significance for system hardware or software. This could be a user clicking a “Purchase” button, a sensor detecting a temperature change in a data center, or a cron job reaching its scheduled execution time. These events provide the stimulus necessary for the digital gatekeeper to react.
2. Event-Driven Triggers: The Peristalsis of Data Streams
In biology, the opening of the gastroesophageal sphincter is triggered by the arrival of a bolus of food, facilitated by a process called peristalsis. In technology, we see a parallel in Event-Driven Architecture (EDA). Here, the “movement” of data is propelled by specific triggers that signal the next stage of processing.
Webhooks: The Proactive Notification
A Webhook is perhaps the most common event trigger in modern web development. Unlike traditional polling—where a system repeatedly asks, “Is there data yet?”—a Webhook acts as a nervous system signal. When a specific event occurs in a source system (like a successful credit card payment), it sends a real-time HTTP POST request to a destination system. This “event” triggers the opening of the receiving system’s gateway to accept and process the incoming data.
Pub/Sub Models and Message Queues
For massive data flows, systems use a Publisher/Subscriber (Pub/Sub) model. This is the “peristalsis” of the tech world. A “Publisher” pushes a message into a queue (like Apache Kafka or RabbitMQ). The “Subscriber” (the gateway or service) is triggered to open and consume that message only when it matches specific criteria. This ensures that the internal system is never overwhelmed, maintaining a steady, controlled flow.
Serverless Triggers and Lambda Functions
The rise of serverless computing (AWS Lambda, Google Cloud Functions) has refined the “trigger” mechanism. In this model, the “sphincter” is completely closed—costing the company zero dollars—until a specific event occurs. This could be an image upload to a storage bucket or a new entry in a database. The moment the event is detected, the gateway “opens” (the function executes), processes the data, and immediately closes again.
3. Security Protocols: The “Neural Signals” of Authentication
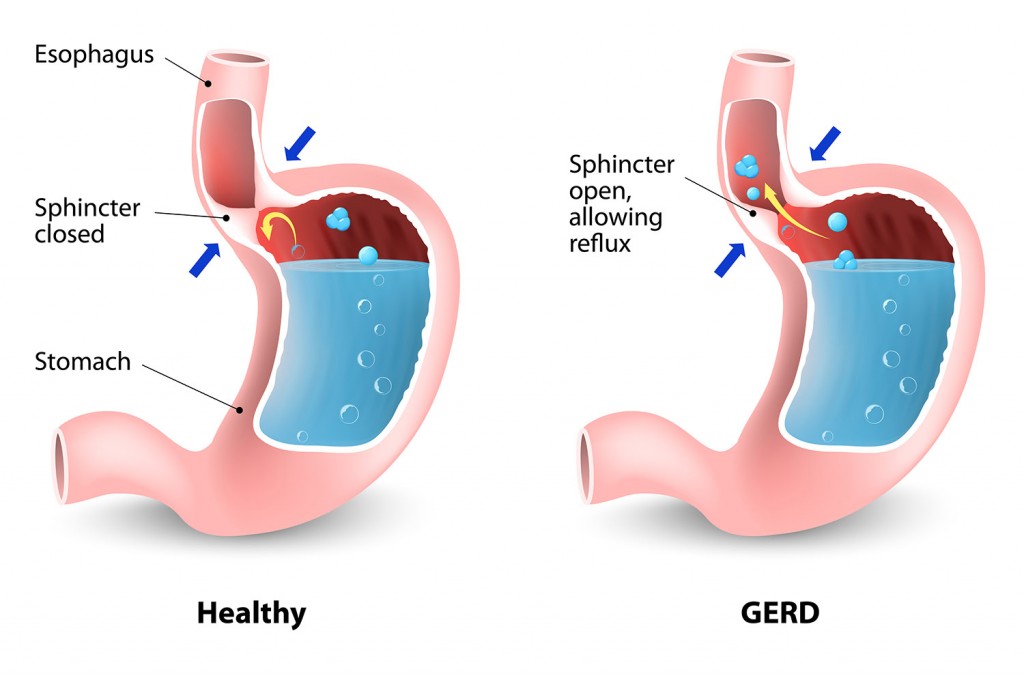
A biological sphincter must distinguish between what is beneficial and what is harmful. Similarly, the “opening” of a digital gateway is strictly governed by security triggers. If the “chemical signature” (the credentials) is wrong, the gate stays shut to prevent an architectural “infection” or data breach.
OAuth 2.0 and JWT Handshakes
The most common trigger for opening a secure API is the presentation of a valid JSON Web Token (JWT). When a user logs in, they receive a token. Every subsequent request must present this token. The gateway performs a cryptographic check—a digital handshake. If the token is valid, the “event” of a successful authentication triggers the gateway to open the path to the protected resource.
Zero Trust Architecture (ZTA)
In a Zero Trust environment, the “trigger” for opening a gateway is much more stringent. It is not enough to simply be “inside the network.” Every single request is treated as a potential threat. The trigger for opening the gate includes a multi-factor verification: the user’s identity, the device’s health, the geographic location, and the time of day. Only when all these “signals” align does the system allow the “bolus” of data to pass through.
Rate Limiting and Circuit Breakers
To protect the internal health of a system, architects implement “Circuit Breakers.” If a service is failing or under attack, the “event” of repeated 500-series errors triggers the circuit breaker to “trip.” This effectively locks the gateway, preventing any more traffic from reaching the failing service. This is a protective reflex, much like how a biological system might reject harmful substances to prevent further damage to the organism.
4. Scaling the Throughput: Managing System Congestion
In any system, whether biological or digital, congestion is the enemy of efficiency. When the “event” that triggers the opening of a gateway happens too frequently, or when the data volume is too large, the system must adapt to prevent “reflux” or total failure.
Horizontal vs. Vertical Scaling Triggers
When a system detects a “High Traffic Event”—such as a Black Friday sale or a viral social media post—it triggers a scaling response.
- Vertical Scaling involves increasing the “muscle” of the existing gatekeeper (adding more RAM or CPU).
- Horizontal Scaling involves creating more gatekeepers.
The event trigger here is usually a telemetry signal from a monitoring tool like Prometheus or Datadog, which observes that the gateway is operating at 80% capacity.
Edge Computing and Latency Reduction
To make the “opening” of the gate faster, tech companies are moving the gatekeepers closer to the user. This is known as Edge Computing. By placing small, nimble gateways (CDN nodes) at the “edge” of the network, the “event” (the user request) doesn’t have to travel halfway around the world to trigger an opening. It happens locally, reducing latency and ensuring a smooth “swallowing” of data into the network.
Data Compression and Transformation
Sometimes the “event” triggers not just an opening, but a transformation. Just as food is broken down as it passes through various stages of the digestive tract, data is often compressed or reformatted at the gateway. A trigger might detect that a user is on a low-bandwidth mobile connection and automatically trigger a “compression gate” that shrinks the size of the data being transmitted.
5. The Future: AI-Driven Autonomous Gateways
As we look toward the future of technology, the triggers that open our digital sphincters are becoming more intelligent. We are moving away from hard-coded “if-this-then-that” logic and toward autonomous, AI-driven decision-making.
Predictive Triggering
Using machine learning, modern systems can now predict when an event is about to happen. If an AI detects a pattern of traffic that historically leads to a surge, it can trigger the opening of additional resources before the surge actually arrives. This is akin to the body’s cephalic phase of digestion, where the sight or smell of food triggers the system to prepare before the food even enters the mouth.
Self-Healing Infrastructure
The ultimate goal of modern DevOps is the “Self-Healing” system. In this scenario, if a gateway detects that its own “sphincter” is malfunctioning (perhaps due to a software bug or a hardware failure), it triggers an automated remediation event. It can close itself off, redirect traffic to a healthy “organ” (node), and initiate a reboot or a version rollback without any human intervention.

Conclusion: The Elegance of the Trigger
The question of “what event triggers the opening of the gastroesophageal sphincter” leads us to a profound appreciation for the complexity of gated systems. In technology, as in biology, the “opening” is never a simple act. It is the culmination of sensory input, security validation, and architectural readiness.
Whether it is a Webhook signaling a transaction, an OAuth token validating a user, or an AI predicting a traffic spike, these triggers are the heartbeat of the digital age. By mastering these triggers, technology leaders can build systems that are not only resilient and secure but also capable of handling the massive, complex flows of information that define our modern world. In the end, the health of any system—biological or digital—depends entirely on the precision and reliability of its gatekeepers.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.