In the biological world, spore-forming bacteria represent the ultimate survivalists. When faced with extreme heat, radiation, or a lack of nutrients, these organisms undergo a transformation into endospores—stripped-down, dormant versions of themselves that can survive for centuries. In the realm of technology, this biological phenomenon is no longer just a curiosity for microbiologists; it has become a foundational blueprint for architects of resilient data systems, cybersecurity frameworks, and synthetic biological computing.
As we push the boundaries of how much data we can store and how resilient our networks must be, the “spore” model offers a masterclass in efficiency and persistence. This article explores how the principles of spore-forming bacteria are being translated into the next generation of technology, from immutable data storage to the burgeoning field of biocomputing.
Understanding the “Spore” Architecture in Modern Software
In software engineering, the concept of “state” is everything. A system is either running, or it is off. However, modern distributed systems are increasingly adopting a third state: the dormant, or “spore-like,” state. This architectural pattern focuses on minimizing resource consumption while maximizing the potential for rapid reactivation.
The Concept of Dormancy in Data Storage
Just as a spore contains only the essential genetic blueprints required to restart life, modern “cold storage” and “serverless” architectures utilize a similar philosophy. In a serverless environment (Function-as-a-Service), code exists in a dormant state—much like a bacterial spore. It consumes no CPU cycles and holds no active memory until an external trigger (an environmental cue) causes it to “germinate.”
This transition from dormancy to activity allows tech companies to scale infinitely without the overhead of maintaining thousands of “active” but idle biological-like cells. By studying the metabolic inactivity of spores, software architects are refining how “hibernation” works in cloud computing, ensuring that even if a system is offline for years, the integrity of its “genetic” code—its core logic—remains uncorrupted.
Activation Triggers: From Environmental Cues to System API Calls
Biological germination is triggered by specific nutrient sensors. In the tech world, we see this replicated through event-driven architecture. A specific API call, a change in a database, or a security breach can act as the “nutrient” that signals a dormant process to activate.
The engineering challenge lies in the speed of this transition. For a spore, germination can take minutes or hours. For a high-frequency trading platform or a critical defense system, the “digital germination” must happen in milliseconds. Engineers are currently developing “warm start” protocols that mimic the pre-activated state of certain spores, keeping just enough system resources active to allow for an instantaneous return to full metabolic (computational) function.
Cybersecurity and the Spore Strategy: Protecting Infrastructure Against Total Erasure
Cybersecurity professionals are increasingly looking at the morphology of spore-forming bacteria to solve the problem of “persistent presence” and “disaster recovery.” In a landscape where ransomware can wipe out entire server farms, the ability to retreat into a “spore-like” immutable state is a powerful defense mechanism.
Immutable Backups as Digital Endospores
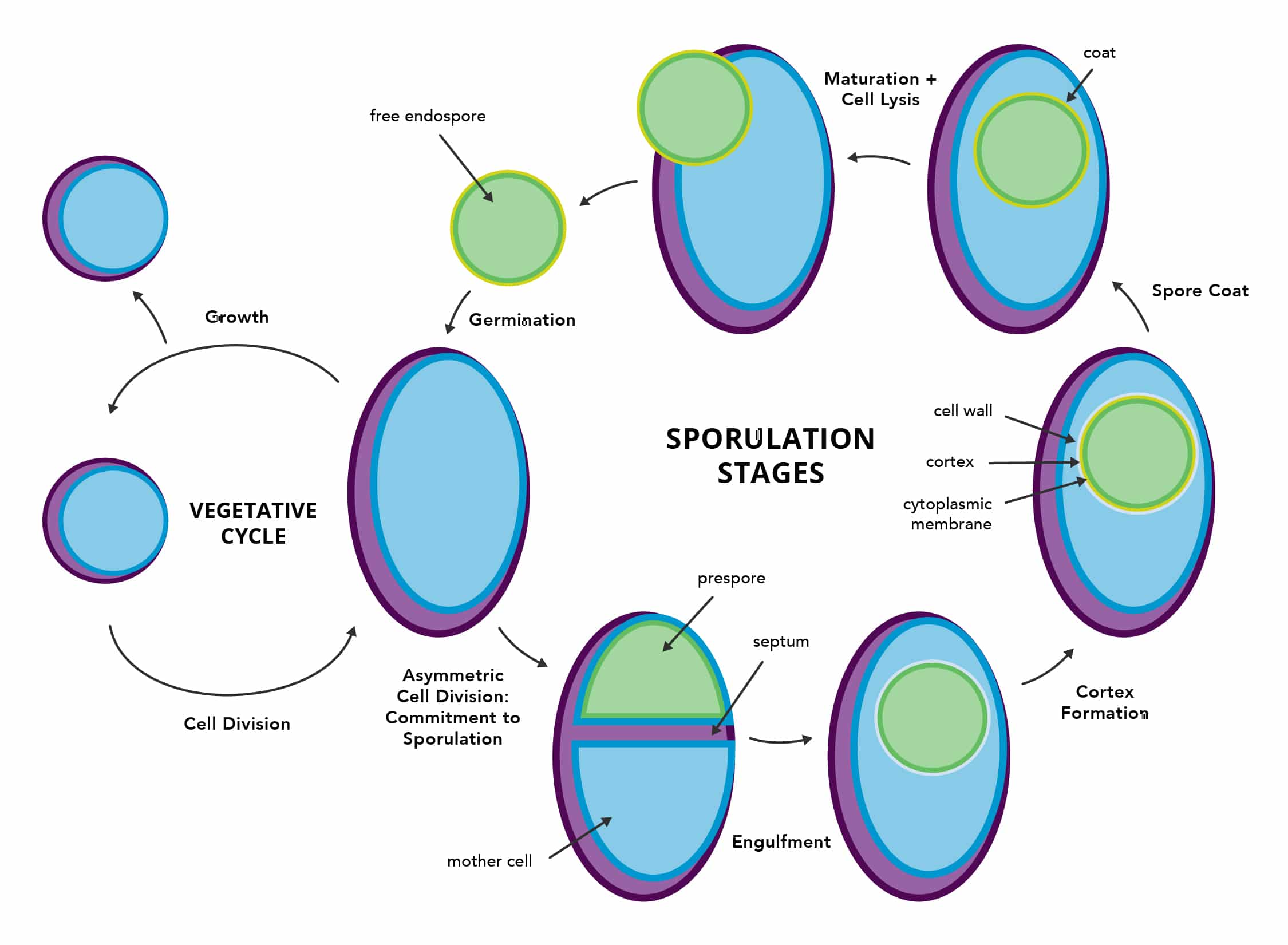
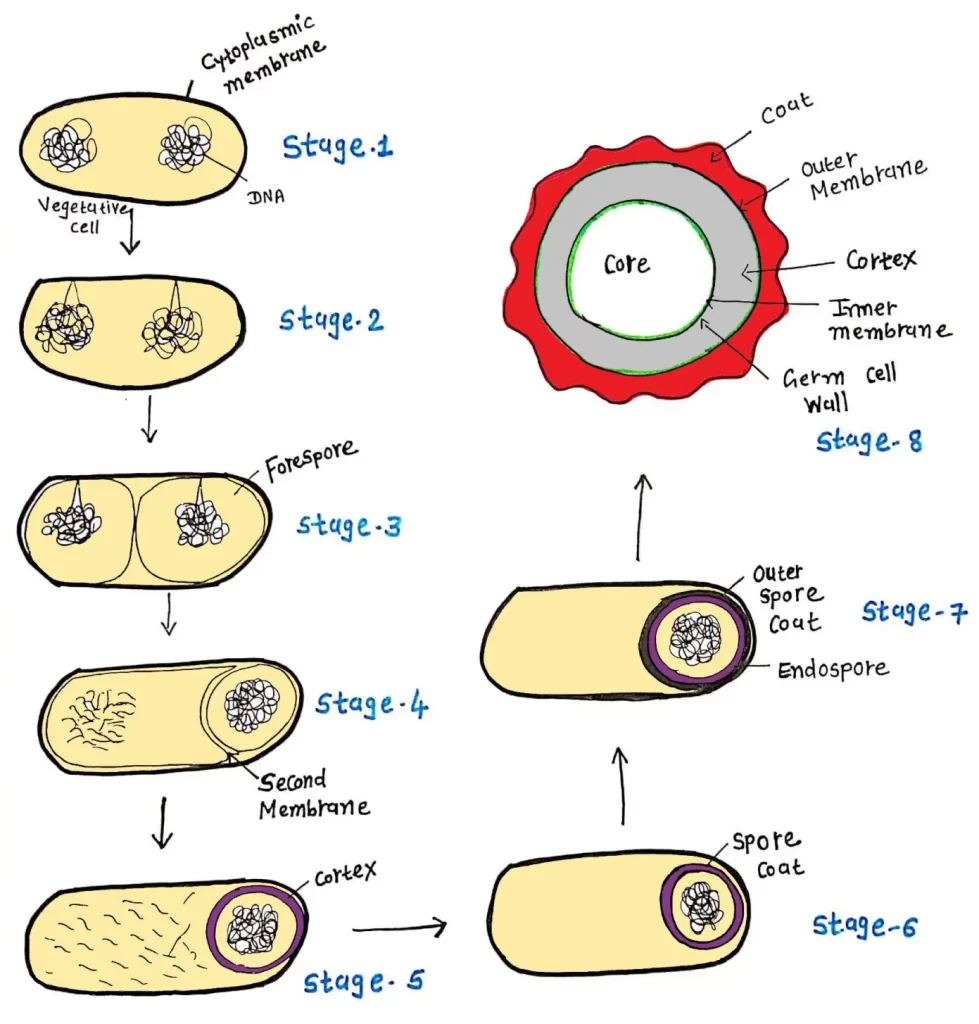
The endospore is protected by a tough, multi-layered protein coat that resists chemicals and heat. In cybersecurity, we replicate this through “Air-Gapped” and “Immutable” backups. This is the digital equivalent of spore formation.
An immutable backup is a version of data that cannot be changed or deleted, even by an administrator with full privileges. By “encysting” critical system data in an immutable format, organizations ensure that even if the active “vegetative” system is killed by a virus or a cyberattack, the “spore” (the backup) remains intact. Recovery, then, is not just about restoring files; it is about the “germination” of a clean, uninfected system from a protected, dormant seed.
Stealth Persistence: How Advanced Persistent Threats (APTs) Mimic Bacterial Life Cycles
Unfortunately, the spore strategy is also utilized by malicious actors. Advanced Persistent Threats (APTs) often employ a “spore-forming” tactic to remain undetected within a network. Once a hacker gains access, they may leave behind a small, dormant piece of code—a digital spore—that does nothing for months.
Because it is dormant, it doesn’t trigger traditional behavioral heuristics or consume network traffic. It waits for a specific “environmental trigger,” such as a certain date or a specific command from a command-and-control server, to reactivate and begin its mission. Understanding the biology of how spores hide from the immune system is helping cybersecurity firms develop “bio-inspired” scanning tools that look for these dormant signatures before they have the chance to germinate.
Synthetic Biology and the Future of Biological Data Storage
Perhaps the most literal application of “what is spore-forming bacteria” in tech is the use of actual bacteria as data storage devices. As we reach the physical limits of silicon-based storage, DNA-based storage is emerging as a viable alternative, and spores are the perfect “hard drives” for this data.
Using Spore-Forming Bacteria for Terabyte-Scale Archiving
DNA can store astronomical amounts of data in a microscopic space. However, DNA is fragile and degrades when exposed to the elements. This is where the spore comes in. By encoding digital data (converted from binary to the A, T, C, G of DNA) and inserting it into the genome of a spore-forming bacterium like Bacillus subtilis, scientists can create a living, resilient data archive.
Once the bacteria form spores, the data is essentially “shrink-wrapped” in a biological armor. Researchers have demonstrated that data stored in this way can survive extreme radiation, vacuum conditions, and thousands of years of time. To retrieve the data, one simply “feeds” the spores, lets them germinate and multiply, and then sequences their DNA to convert it back into digital code. This is the ultimate “cold storage” solution for humanity’s most important information.
The Intersection of CRISPR and Information Technology
The tools of gene editing, such as CRISPR-Cas9, act as the “write” head of these biological drives. In this new tech niche, software engineers and bio-engineers are collaborating to create “biological compilers.” These are programs that take high-level code and translate it into DNA sequences designed to be stable within a bacterial spore. This cross-disciplinary field is redefining what we consider “hardware,” moving us away from metal and silicon toward organic, self-replicating, and ultra-resilient biological units.
Scaling the Spore Model: Decentralized Systems and Edge Computing
As we move toward a world of billions of IoT (Internet of Things) devices, the central cloud model is becoming strained. The “spore model” offers a decentralized alternative where every node has the capacity for dormancy and independent survival.
Node Resiliency in Distributed Ledgers
In a decentralized network or blockchain, the death of a single node (a server) shouldn’t affect the whole. However, maintaining thousands of active nodes is energy-intensive. A “spore-inspired” blockchain would allow for nodes to enter a low-power, dormant state while still maintaining the integrity of the ledger.
These “spore nodes” would only re-sync and become active when network traffic increases or when specific validation is required. This would significantly reduce the carbon footprint of decentralized technologies while maintaining the “extreme survival” characteristics that make blockchain attractive for financial and logistical systems.
Survival Mechanisms for IoT in Extreme Environments
IoT devices in the field—whether they are sensors on a remote farm, in a deep-sea trench, or on a Mars rover—face “harsh environments” similar to those that trigger bacterial spore formation.
Tech companies are now designing “spore-mode” firmware for these devices. When a sensor detects that its battery is critically low or the environment is too hostile (extreme heat or lack of connectivity), it enters a “spore state.” It saves its current state to non-volatile memory, shuts down all but the most basic sensory “triggers,” and waits. This bio-mimicry allows for technology to persist in environments where traditional, “always-on” hardware would simply fail.

The Convergence of Biology and Technology
The question “what is spore-forming bacteria” leads us down a path that transcends biology and enters the heart of modern technological innovation. We are moving away from fragile, high-maintenance systems toward a future of “resilient computing.”
By adopting the spore’s strategy of dormancy, protection, and rapid reactivation, we are building software that is harder to kill, databases that can last for millennia, and hardware that can survive the vacuum of space. The spore is no longer just a biological entity; it is a design philosophy that ensures that in the digital world, as in the natural one, life (and data) finds a way to persist.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.