In the vast, interconnected landscape of global computing, time is the invisible thread that holds everything together. From the timestamps on a simple email to the high-frequency trades executed on Wall Street, the precision of a clock can be the difference between a successful transaction and a catastrophic system failure. At the heart of this temporal coordination lies the Network Time Protocol (NTP). Developed in the early 1980s, NTP is one of the oldest Internet protocols still in active use, ensuring that devices across the globe—from massive data centers to small IoT sensors—remain in perfect harmony.

The Architecture of Time: How NTP Works
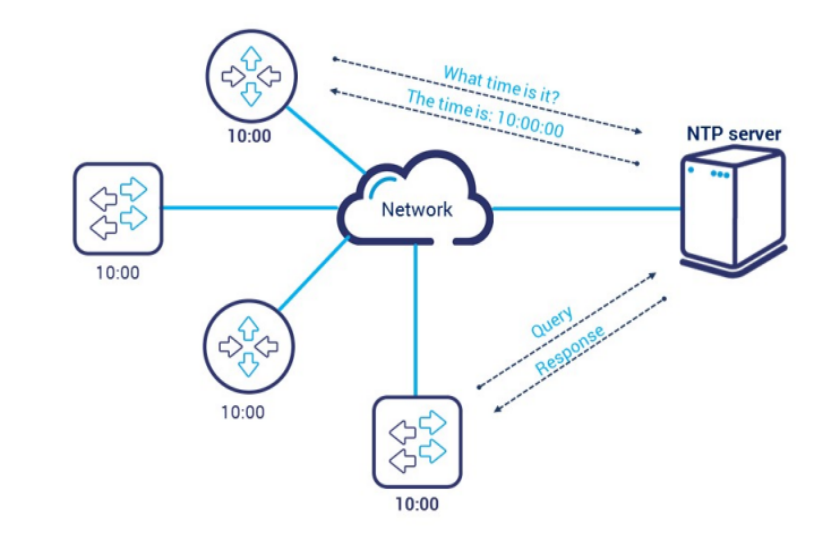
To understand NTP, one must first view it as a hierarchical system of time distribution. It is not merely a method for a computer to “ask” for the time; it is a sophisticated suite of algorithms designed to mitigate the inherent unpredictability of network latency. Because data packets take time to travel across the internet, a simple “current time” message would be obsolete by the time it reached the receiver. NTP compensates for this delay with surgical precision.
The Stratum Hierarchy
NTP utilizes a hierarchical system of clock sources known as “strata.” This hierarchy is designed to ensure accuracy while preventing any single server from becoming a bottleneck.
- Stratum 0: These are high-precision timekeeping devices such as atomic clocks, GPS clocks, or radio clocks. Stratum 0 devices are not connected directly to the network; instead, they are attached to a computer that serves as a Stratum 1 source.
- Stratum 1: These are servers directly linked to a Stratum 0 device. They act as the primary network time standards.
- Stratum 2: These servers receive their time from Stratum 1 servers over a network. Most corporate NTP servers are Stratum 2, as they sync with public Stratum 1 sources and then distribute that time to local clients.
- Stratum 3 and Below: This continues down the chain. While NTP supports up to 15 strata, the precision decreases slightly with each hop, though it remains more than sufficient for most commercial applications.
The Client-Server Exchange Process
When a client device wants to synchronize its clock, it initiates a bidirectional exchange of packets. The client sends a request containing its local timestamp. The server receives this, adds its own “receive” timestamp, and then adds a “transmit” timestamp before sending the packet back. By the time the client receives the return packet, it has four distinct timestamps. Using these, NTP calculates the “round-trip delay” and the “clock offset.” This allows the client to adjust its local clock to match the server’s time, accounting for the exact amount of time the data spent traveling through wires and routers.
The Marzullo Algorithm
A standout feature of NTP is its ability to handle “liars”—servers that provide inaccurate time. NTP clients often poll multiple time sources simultaneously. Using the Marzullo algorithm (or the updated intersection algorithm), the NTP software filters out statistical outliers and selects the most reliable “truechimers” while discarding “falsetickers.” This ensures that even if one server’s hardware fails or is hijacked, the client remains synchronized to the correct time.
Why Precision Timekeeping Matters in Modern Networking
In a domestic setting, a computer clock being off by a few seconds might result in nothing more than a minor annoyance. However, in the enterprise and technology sectors, time synchronization is a fundamental requirement for security, data integrity, and legal compliance.
Log File Consistency and Troubleshooting
In the world of IT operations and cybersecurity, logs are the primary tool for post-mortem analysis. When a security breach or a system crash occurs, administrators must piece together events from dozens of different servers, firewalls, and databases. If these devices are not synchronized via NTP, correlating the logs becomes an impossible puzzle. An event that appears to happen at 10:00:01 on a database might actually be a reaction to an event logged at 10:00:05 on a web server if their clocks are out of sync. NTP provides the “common language” of time required for forensic accuracy.
Security Protocols and Authentication
Many modern security mechanisms rely heavily on time-based tokens. For example, the Kerberos authentication protocol—used extensively in Windows Active Directory environments—requires that the client and server clocks be within five minutes of each other. If the offset is greater, the system assumes a “replay attack” is in progress and denies the login. Similarly, SSL/TLS certificates have specific validity periods. If a device’s clock is set incorrectly to a date in the past or future, it will flag perfectly valid websites as insecure, breaking encrypted communications across the network.

High-Frequency Trading and Legal Compliance
In the financial sector, time is literally money. High-frequency trading (HFT) platforms execute thousands of orders per second. To ensure fairness and transparency, regulatory bodies like FINRA and ESMA require that financial institutions timestamp transactions with microsecond-level accuracy. NTP, and its more precise cousin PTP (Precision Time Protocol), are essential for meeting these regulatory mandates and ensuring that the sequence of trades is recorded exactly as it occurred.
Security Challenges and the Evolution of NTP
Despite its longevity and utility, NTP was designed in an era when the internet was a much friendlier place. As a result, the protocol has several inherent vulnerabilities that modern network administrators must address.
NTP Amplification Attacks
One of the most common security issues associated with NTP is its susceptibility to Distributed Denial of Service (DDoS) amplification attacks. Older versions of the NTP daemon included a command called monlist, which allowed a user to request a list of the last 600 IP addresses that had synced with the server. A malicious actor could send a small request to an NTP server with a “spoofed” IP address (the address of their victim). The server would then respond with a massive data packet to the victim’s IP. By leveraging thousands of open NTP servers, an attacker can crash a target’s network with a massive flood of unwanted data.
Securing the Infrastructure: NTPsec and NTS
To combat these vulnerabilities, the tech community has developed more secure iterations of the protocol. NTPsec is a hardened version of the original NTP code, stripped of legacy features that caused security holes. More importantly, the industry is moving toward Network Time Security (NTS). NTS adds a layer of cryptography to NTP, ensuring that the time data a client receives is actually from the intended server and has not been tampered with by a “man-in-the-middle.” This is a critical evolution for securing critical infrastructure and public utilities.
The Leap Second Dilemma
A fascinating technical challenge for NTP is the “leap second.” Because the Earth’s rotation is gradually slowing down, the International Earth Rotation and Reference Systems Service (IERS) occasionally adds a second to Coordinated Universal Time (UTC) to keep it in sync with solar time. While this sounds simple, it can cause havoc in distributed systems. Some NTP implementations “smear” the extra second over several hours to prevent a sudden jump, while others simply repeat a second. Ensuring all servers in a cluster handle a leap second identically is a major focus for site reliability engineers (SREs).
Implementing and Configuring NTP in Modern Systems
For most organizations, implementing NTP involves a mix of using public pools and maintaining private internal masters. Understanding the configuration landscape is key to a robust network.
Public NTP Pools vs. Private Sources
The NTP Pool Project is a massive virtual cluster of timeservers providing reliable NTP service to millions of clients. For most general-purpose applications, using pool.ntp.org is the standard. However, for organizations with strict security requirements, relying on the open internet for time is a risk. These entities often deploy “GPS-disciplined” NTP appliances within their own data centers. These devices pull time directly from satellites, providing a Stratum 1 source that functions even if the organization’s internet connection is severed.
Configuration Best Practices
When configuring NTP on Linux (using ntpd or chrony) or Windows (using the Windows Time Service), there are several best practices to follow:
- Multiple Sources: Always configure at least three or four time sources. This allows the Marzullo algorithm to identify a “falseticker” if one source goes rogue.
- Use Drift Files: NTP keeps track of how much a hardware clock tends to gain or lose time. This “drift” is stored in a file, allowing the system to maintain relative accuracy even if the network connection is temporarily lost.
- Restrict Access: Use Access Control Lists (ACLs) to ensure that only authorized clients can query your time servers, preventing your infrastructure from being used in amplification attacks.
NTP vs. SNTP
It is important to distinguish between NTP and SNTP (Simple Network Time Protocol). SNTP is a stripped-down version of the protocol that lacks the complex filtering and error-correction algorithms of full NTP. While SNTP is suitable for low-power IoT devices or simple desktop applications where millisecond precision isn’t vital, it should never be used for core infrastructure or synchronized database clusters.
Conclusion: The Timeless Necessity of NTP
As we move further into the era of 5G, autonomous vehicles, and decentralized finance, the demand for precision timing will only grow. While the underlying code of Network Time Protocol has been refined over four decades, its core mission remains unchanged: to provide a single, universal source of truth for the digital world. By understanding its hierarchy, respecting its security requirements, and implementing it with redundancy, technology professionals can ensure that their networks remain synchronized, secure, and ready for the future. NTP is not just a utility; it is the heartbeat of the internet.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.