In the ever-evolving landscape of digital security, network access control is paramount. Organizations of all sizes grapple with the challenge of ensuring that only authorized devices and users can connect to their networks. This is where IEEE 802.1X emerges as a critical technology, providing a robust framework for port-based network access control (PNAC). It’s not merely a feature; it’s a foundational standard that underpins secure network connectivity, acting as a digital gatekeeper that verifies the identity of entities before granting them access to sensitive resources.
IEEE 802.1X addresses a fundamental security vulnerability: the ease with which an unauthorized device could potentially connect to a network and gain access to its resources. Without proper authentication, a simple physical connection to an Ethernet port or a Wi-Fi access point could compromise an entire network. This standard, developed by the Institute of Electrical and Electronics Engineers (IEEE), introduces a standardized method for authenticating and authorizing devices and users on a network, thereby significantly enhancing its overall security posture.

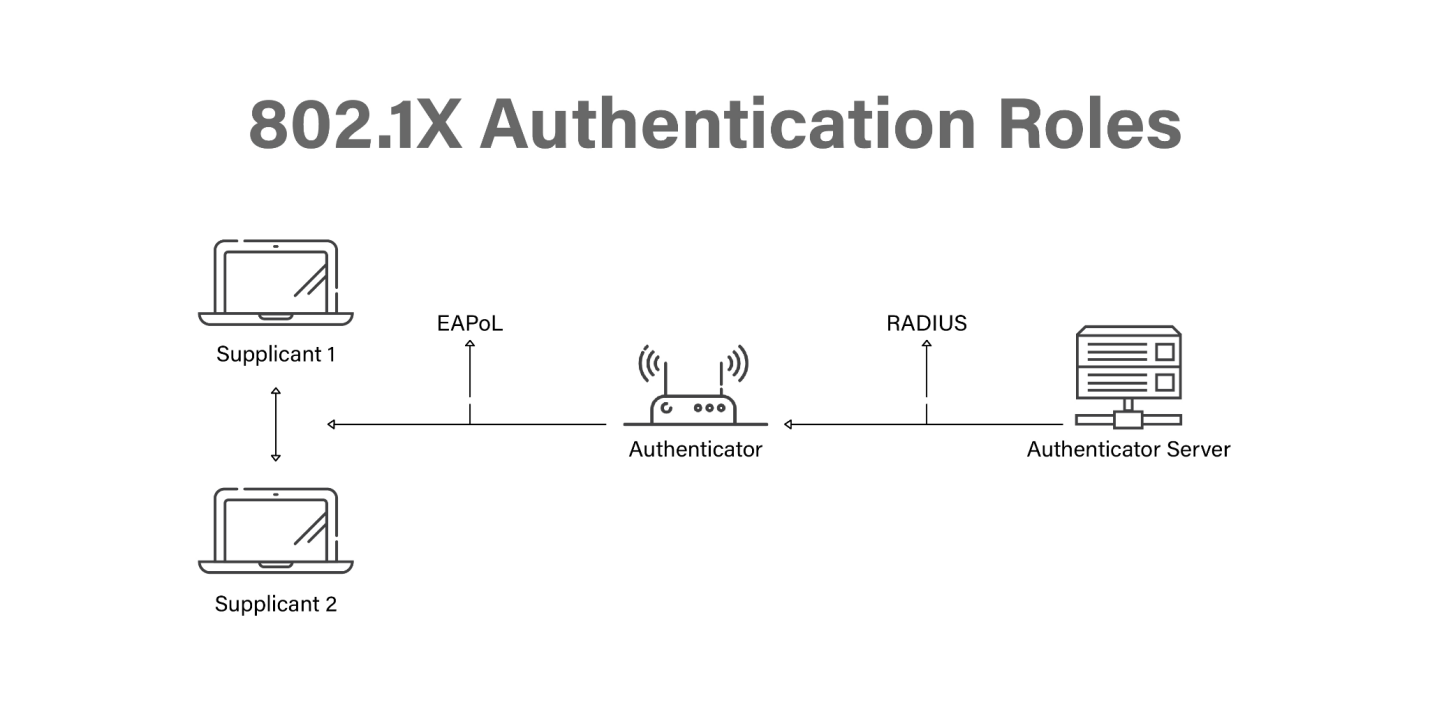
The primary objective of IEEE 802.1X is to prevent unauthorized network access by ensuring that only authenticated and authorized users and devices can connect to a network port. It achieves this through a three-component architecture involving an Supplicant, an Authenticator, and an Authentication Server. This collaborative approach forms the backbone of its effectiveness, creating a secure handshake before any data can traverse the network. Understanding these components and how they interact is key to appreciating the power and utility of IEEE 802.1X in modern network security.
The Core Architecture: Supplicant, Authenticator, and Authentication Server
At its heart, IEEE 802.1X operates on a well-defined architectural model comprising three essential entities that work in concert to establish and manage network access. This tripartite system ensures that the authentication process is centralized, auditable, and robust, forming a critical layer of defense against unauthorized access.
The Supplicant: The Client’s Voice
The Supplicant is the device or application requesting access to the network. This could be a laptop, a smartphone, a printer, or any other network-enabled device. The Supplicant initiates the authentication process by responding to requests from the Authenticator and providing its credentials. These credentials can take various forms, including usernames and passwords, digital certificates, or other authentication factors. The Supplicant’s role is to present its identity and be ready to undergo the verification checks dictated by the network’s security policy. In essence, it’s the entity that needs to prove its legitimacy.
The Authenticator: The Network’s Gatekeeper
The Authenticator is typically a network access device, such as a switch or a wireless access point (WAP). Its primary responsibility is to enforce access control on its ports. When a Supplicant attempts to connect, the Authenticator intercepts the connection attempt. Instead of immediately granting access, it initiates the 802.1X authentication process. The Authenticator acts as an intermediary, forwarding the Supplicant’s credentials to the Authentication Server and then acting upon the server’s decision. It blocks all traffic from the Supplicant except for the authentication exchange until the process is successfully completed. Once authenticated, the Authenticator dynamically configures the network port to allow or deny access based on the Authentication Server’s instructions.
The Authentication Server: The Ultimate Arbiter
The Authentication Server is the trusted entity responsible for verifying the identity of the Supplicant and making the final decision on whether to grant network access. Most commonly, this role is fulfilled by a RADIUS (Remote Authentication Dial-In User Service) server, although other protocols can also be used. The Authentication Server receives the Supplicant’s credentials from the Authenticator, validates them against a database of authorized users and devices, and then sends an Access-Accept or Access-Reject message back to the Authenticator. If the authentication is successful, the Authentication Server can also provide information to the Authenticator about specific network policies to be applied, such as assigning a VLAN or setting bandwidth limitations. This centralized authority ensures consistency and simplifies management of network access policies.
The Authentication Process: A Step-by-Step Flow
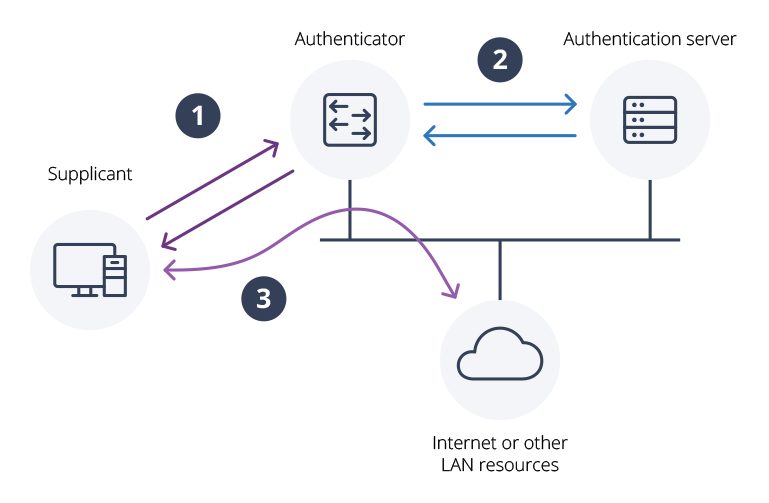
The IEEE 802.1X authentication process is a structured dialogue between the Supplicant, Authenticator, and Authentication Server, designed to securely verify the identity of the connecting entity. While the specifics can vary slightly depending on the chosen Extensible Authentication Protocol (EAP) method, the fundamental steps remain consistent.
Initiating the Conversation: EAP-Start and EAP-Request
When a Supplicant connects to a port managed by an Authenticator, the Authenticator will typically send an EAP-Request/Identity message to the Supplicant. This message signals that the network is ready for the authentication process to begin and prompts the Supplicant to identify itself. The Supplicant responds with an EAP-Response/Identity message, containing its username or other identifying information. This exchange initiates the EAP conversation.
The Authentication Exchange: EAP Methods in Action
Following the initial identity exchange, the Authenticator passes the Supplicant’s identity to the Authentication Server. The Authentication Server then selects an appropriate EAP method and sends an EAP-Request to the Authenticator, which in turn forwards it to the Supplicant. This begins a series of back-and-forth messages between the Supplicant and the Authentication Server, facilitated by the Authenticator. The specific EAP method employed dictates the nature of this exchange. Common EAP methods include:
- EAP-TLS (Extensible Authentication Protocol – Transport Layer Security): This is a widely used and highly secure method that relies on mutual authentication using digital certificates. Both the Supplicant and the Authentication Server possess certificates, and they authenticate each other. This provides strong assurance of identity.
- PEAP (Protected Extensible Authentication Protocol): PEAP provides a secure TLS tunnel between the Supplicant and the Authentication Server, within which other authentication methods, such as username and password (often using EAP-MSCHAPv2), can be securely transmitted. This is common in enterprise Wi-Fi deployments.
- EAP-TTLS (Extensible Authentication Protocol – Tunneled Transport Layer Security): Similar to PEAP, EAP-TTLS establishes a TLS tunnel but typically uses a server-side certificate and then allows for various client authentication methods within the tunnel, including username/password.
- EAP-MD5 (Message Digest 5): While less secure due to known vulnerabilities in MD5, this method uses a challenge-response mechanism with a one-way hash function. It is generally not recommended for new deployments.
During this phase, the Supplicant and Authentication Server engage in a cryptographic dialogue to verify credentials. The Authenticator simply relays these messages, acting as a transparent conduit.
The Verdict: Access-Accept or Access-Reject
Once the Authentication Server has successfully verified the Supplicant’s credentials through the chosen EAP method, it sends an EAP-Success message back to the Authenticator. Along with this success notification, the Authentication Server can also send information about the network policies to be applied to the Supplicant’s connection. This could include specifying which VLAN the Supplicant should be placed on, setting Quality of Service (QoS) parameters, or defining access control lists (ACLs). The Authenticator then configures the network port accordingly and grants the Supplicant access.
Conversely, if the authentication fails for any reason (e.g., incorrect credentials, invalid certificate, or lack of authorization), the Authentication Server sends an EAP-Failure message to the Authenticator. The Authenticator then denies access to the Supplicant and typically logs the failed attempt. The network port remains in a restricted state, preventing any further network communication until a successful authentication occurs.
Benefits and Use Cases of IEEE 802.1X
The implementation of IEEE 802.1X offers a multitude of advantages for organizations seeking to bolster their network security. Its structured approach to access control addresses critical vulnerabilities and provides a scalable solution for managing network access across diverse environments.
Enhanced Network Security and Threat Mitigation
The most significant benefit of IEEE 802.1X is its ability to prevent unauthorized access to the network. By requiring strong authentication before granting access, it acts as a powerful deterrent against various threats, including:
- Rogue Devices: Unauthorized devices attempting to connect to the network are immediately identified and blocked.
- Man-in-the-Middle Attacks: By ensuring that only authenticated clients can communicate with the network infrastructure, 802.1X helps mitigate man-in-the-middle attacks that rely on impersonating network devices.
- Credential Theft: While not a direct defense against credential theft itself, when used with strong authentication methods like EAP-TLS or PEAP, it significantly reduces the risk of compromised credentials leading to unauthorized access.
- Insider Threats: By enforcing granular access policies, 802.1X can help limit the lateral movement of threats from within the network.
Centralized Access Control and Policy Management
IEEE 802.1X centralizes the authentication and authorization process through the Authentication Server. This provides several advantages for network administrators:
- Simplified Management: Instead of configuring access control lists on individual ports or devices, policies are managed centrally on the RADIUS server. This makes it easier to deploy, update, and revoke access for users and devices.
- Consistent Enforcement: Centralized management ensures that access policies are applied consistently across the entire network, reducing the risk of misconfigurations and security loopholes.
- Dynamic Policy Application: As mentioned earlier, the Authentication Server can dynamically assign network policies, such as VLANs, based on user roles or device types. This allows for flexible and adaptive network segmentation.
- Auditing and Reporting: Centralized authentication logs provide valuable audit trails for security monitoring, incident response, and compliance reporting.
Support for Wired and Wireless Networks
IEEE 802.1X is a versatile standard that is widely supported across both wired (Ethernet) and wireless (Wi-Fi) networks.
- Wired Networks: In wired environments, 802.1X is implemented at the switch port level. When a device is plugged into a switch port configured for 802.1X, the switch acts as the Authenticator, initiating the authentication process.
- Wireless Networks: For Wi-Fi, 802.1X is the backbone of WPA2-Enterprise and WPA3-Enterprise security protocols. The wireless access point acts as the Authenticator, and the client device runs the Supplicant. This provides a much higher level of security than pre-shared key (PSK) authentication, especially in environments with many users.
Integration with Existing Infrastructure
IEEE 802.1X is designed to be interoperable with existing network infrastructure and identity management systems. It commonly integrates with:
- Active Directory (AD): User credentials stored in Active Directory can be used for authentication via RADIUS.
- LDAP Servers: Similar to AD, LDAP directories can serve as the source of user and device authentication.
- Certificate Authorities (CAs): For certificate-based authentication methods like EAP-TLS, integration with a CA is essential for issuing and managing digital certificates.
Implementing IEEE 802.1X: Considerations and Best Practices
While the benefits of IEEE 802.1X are substantial, its successful implementation requires careful planning, configuration, and ongoing management. Addressing potential challenges and adopting best practices are crucial for maximizing its effectiveness.
Planning and Design
Before deploying IEEE 802.1X, it is essential to have a well-defined network access control strategy. Key considerations include:
- Authentication Methods: Choose appropriate EAP methods based on security requirements, available infrastructure, and user experience. For most enterprise environments, PEAP or EAP-TLS are recommended.
- Credential Management: Decide how user and device credentials will be managed. This involves integrating with existing directories or establishing a robust certificate management system.
- Network Segmentation: Plan how network segmentation (e.g., VLANs) will be used to isolate different groups of users or devices based on their roles and authorization levels.
- Guest Access: Develop a separate strategy for providing secure guest access, as direct 802.1X authentication for guests might not be practical.
Configuration and Deployment
The technical implementation of 802.1X involves configuring various components:
- Authenticator Configuration: Configure network switches and wireless access points to act as Authenticators, specifying the RADIUS server details and enabling 802.1X on the desired ports or SSIDs.
- Authentication Server Configuration: Set up and configure the RADIUS server, defining authentication policies, user groups, and access rules. Integrate it with your directory services or certificate authority.
- Supplicant Configuration: Ensure that client devices are configured to support and use the chosen EAP methods. This often involves installing supplicant software or configuring built-in operating system settings. For certificate-based methods, the necessary certificates must be deployed to the client devices.
Ongoing Management and Maintenance
IEEE 802.1X is not a set-it-and-forget-it solution. Ongoing management is critical for maintaining its security posture:
- Regular Auditing: Periodically review authentication logs for suspicious activity, failed login attempts, and unauthorized access patterns.
- Policy Updates: Keep access control policies up-to-date to reflect changes in organizational structure, user roles, and security threats.
- Certificate Renewal: If using certificate-based authentication, ensure a process is in place for timely certificate renewal and revocation.
- Firmware Updates: Keep the firmware of network devices (switches, WAPs) and operating systems on client devices updated to patch any known vulnerabilities.
- Monitoring and Alerting: Implement monitoring and alerting systems to proactively identify and respond to potential security incidents related to network access.
By understanding the intricate workings of IEEE 802.1X, its architecture, and its practical implications, organizations can leverage this powerful standard to build a more secure, controlled, and resilient network environment. It represents a significant leap forward in network access control, moving beyond simple password-based authentication to a more robust, identity-centric security model.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.