The emergence of Bitcoin in 2009 introduced the world to a radical new concept: a digital medium of exchange that operates without the need for a central authority. While many discuss cryptocurrencies through the lens of market volatility or investment potential, the true innovation lies in the underlying technology. At its core, a cryptocurrency is a complex synthesis of distributed computing, advanced cryptography, and game theory. Understanding how these assets work requires peeling back the layers of the digital infrastructure that enables trust in a trustless environment.
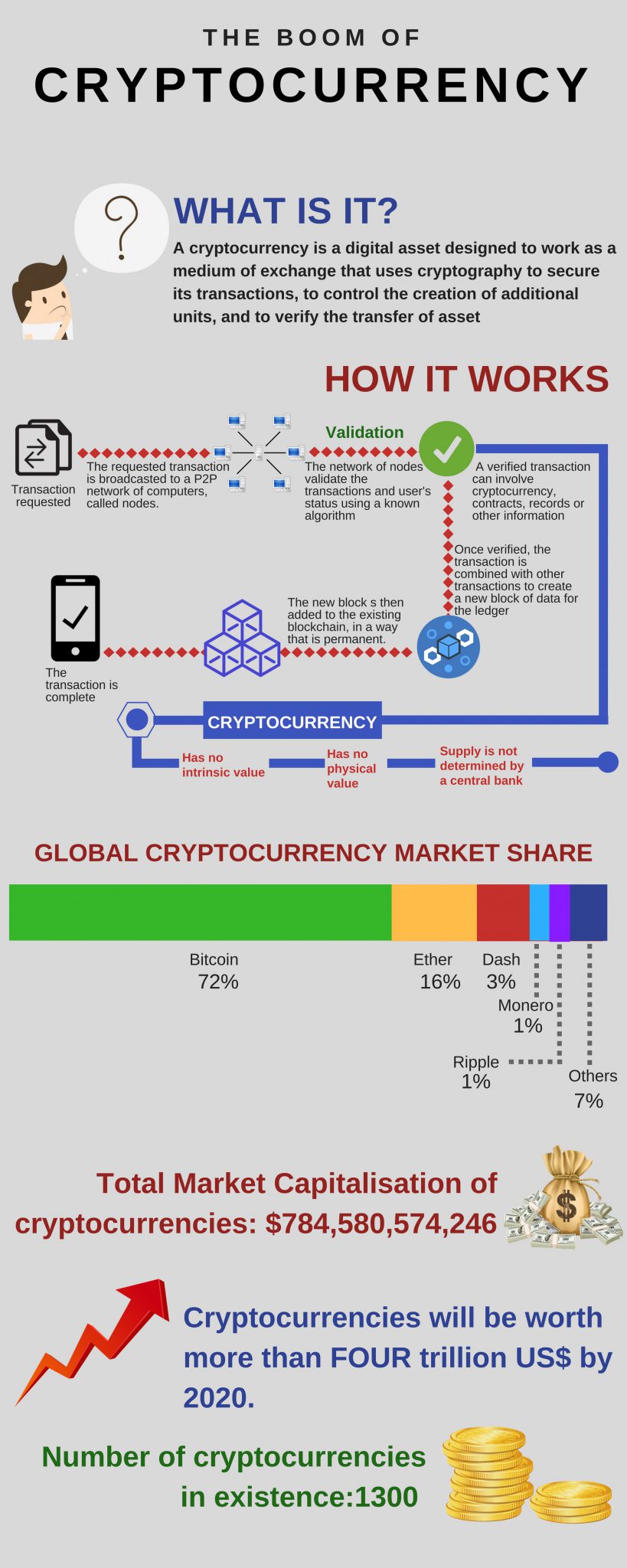
To understand the mechanics of cryptocurrency, one must move past the idea of “coins” as physical or even digital files. Instead, think of a cryptocurrency as a massive, globally distributed database—a ledger—that records every transaction ever made. This ledger is maintained not by a bank, but by a network of computers around the world.
The Foundation: Distributed Ledger Technology and Decentralization
The primary technological breakthrough that makes cryptocurrency possible is Distributed Ledger Technology (DLT), most commonly implemented as a “blockchain.” In traditional finance, if you want to send money to a friend, you rely on a bank to verify that you have the funds and to update its private database. In the world of cryptocurrency, there is no central database.
The Concept of the Blockchain
A blockchain is exactly what it sounds like: a chain of blocks. Each block contains a list of validated transactions. When a block is filled, it is mathematically “chained” to the previous block using a cryptographic signature. This creates a chronological and immutable history of data. Because every new block contains a reference to the one before it, altering a single transaction in an old block would require regenerating every subsequent block in the chain—a feat that is computationally impossible for most modern networks.
Decentralization vs. Centralized Systems
In a centralized system, a single point of failure exists. If a bank’s servers are compromised or if the institution goes bankrupt, the ledger is at risk. Cryptocurrencies solve this through decentralization. The ledger is shared across thousands of “nodes” (individual computers) simultaneously. These nodes communicate with each other to ensure they all possess the exact same version of the ledger. This redundancy ensures that the network remains functional even if a significant portion of the nodes goes offline or is attacked.
Cryptography: The Science of Security
The “crypto” in cryptocurrency refers to the sophisticated mathematical techniques used to secure the network and verify transactions. Without these cryptographic safeguards, a digital currency would be trivial to counterfeit or steal.
Public and Private Keys
Every user on a blockchain network possesses a pair of cryptographic keys: a public key and a private key. This is known as Asymmetric Encryption.
- The Public Key: Think of this as your email address or bank account number. You share this with others so they can send you funds.
- The Private Key: This is your digital signature and password combined. It allows you to “sign” transactions, proving to the network that you are the rightful owner of the funds you are trying to move.
The security of the entire system relies on the fact that while it is easy to derive a public key from a private key, it is mathematically impossible to do the reverse. If you lose your private key, you lose access to your funds forever, as there is no “Forgot Password” service in a decentralized environment.
Hashing and Data Integrity
Another pillar of cryptocurrency security is “hashing.” A cryptographic hash function takes an input (like a block of transaction data) and turns it into a fixed-length string of characters. Even a tiny change in the input—changing a decimal point in a transaction, for example—will result in a completely different hash. This allows the network to verify the integrity of the data instantly. If the hash of a block doesn’t match what the rest of the network expects, the block is rejected as fraudulent.
Consensus Mechanisms: How the Network Agrees
Since there is no central authority to decide which transactions are valid, the decentralized nodes must follow a strict set of rules to reach an agreement. This process is called a “consensus mechanism.” It is the engine that keeps the blockchain moving and prevents “double-spending” (spending the same digital token twice).
Proof of Work (PoW) and Mining
Proof of Work was the first consensus mechanism, famously utilized by Bitcoin. In this system, “miners” compete to solve complex mathematical puzzles. The first miner to solve the puzzle earns the right to add the next block to the blockchain and is rewarded with newly minted cryptocurrency.
This process is purposefully resource-intensive. It requires vast amounts of computational power (and electricity), which serves as a security feature. To attack the network, a malicious actor would need to control more than 51% of the network’s total computing power, making the cost of an attack far higher than any potential gain.
Proof of Stake (PoS) and Validating
As concerns over the energy consumption of Proof of Work grew, many modern blockchains, including Ethereum, transitioned to Proof of Stake. In a PoS system, there are no miners. Instead, there are “validators.”
Validators are chosen to create new blocks based on the number of coins they “stake” (lock up) as collateral. If a validator attempts to process fraudulent transactions, they lose their staked coins. This creates a financial incentive for honesty without the need for massive energy consumption. PoS is generally considered more scalable and environmentally friendly than PoW.
The Lifecycle of a Transaction
To understand how these technical components work in harmony, it is helpful to follow the journey of a single cryptocurrency transaction from start to finish.
Initiation and Broadcasting
When User A wants to send 1 Bitcoin to User B, they create a transaction request using their wallet software. They sign this request with their private key, proving they have the authority to move the funds. The transaction is then broadcast to the network, where it enters a “mempool” (memory pool)—a digital waiting room for unconfirmed transactions.
Verification and Block Formation
Nodes on the network pick up the transaction from the mempool and check it against the existing blockchain to ensure User A actually has the funds. Once verified, the transaction is bundled with others into a candidate block. Depending on the network’s consensus mechanism, a miner or validator will then work to “finalize” this block. Once the block is added to the chain, User B sees the funds in their wallet. The transaction is now part of the permanent, public record.
Beyond Currency: Smart Contracts and the Future of Programmable Money
While the earliest cryptocurrencies were designed simply as alternatives to cash, the technology has evolved into a platform for “programmable money.” This is largely thanks to the introduction of smart contracts.
What are Smart Contracts?
First popularized by the Ethereum network, smart contracts are self-executing contracts with the terms of the agreement written directly into code. They reside on the blockchain and execute automatically when certain conditions are met. For example, a smart contract could be programmed to release a payment to a freelancer only after a specific digital file is uploaded to a shared server. Because they run on the blockchain, smart contracts eliminate the need for intermediaries like escrow agents or lawyers, reducing costs and increasing transparency.
The Evolution of Web3 and Decentralized Applications (dApps)
Smart contracts have paved the way for Decentralized Applications (dApps). These are applications that look and feel like regular apps—such as social media platforms, marketplaces, or gaming sites—but are powered by blockchain technology rather than a centralized server. This ecosystem, often referred to as “Web3,” represents a shift toward a more user-centric internet where data and value are controlled by individuals rather than tech giants.

Conclusion
Cryptocurrencies represent a monumental shift in how we perceive and handle data and value in the digital age. By combining the transparency of a distributed ledger, the security of advanced cryptography, and the efficiency of decentralized consensus mechanisms, they provide a robust framework for a new financial and technological reality. While the complexities of blockchain can be daunting, the core mission is simple: to create a secure, transparent, and immutable record of truth that belongs to no one and is accessible to everyone. As the technology continues to mature, its applications will likely extend far beyond simple transactions, fundamentally altering the fabric of the digital world.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.