The process of Bitcoin mining has evolved from a hobbyist activity performed on personal computers into a highly sophisticated, industrial-scale technological endeavor. At its core, Bitcoin mining is the backbone of the decentralized network, serving as the mechanism for transaction verification and the issuance of new currency. For those looking to enter the space today, understanding the technical nuances—from the intricacies of hashing algorithms to the cooling requirements of high-density hardware—is essential. This guide provides a deep dive into the technical architecture required to successfully mine for Bitcoin in the modern era.
Understanding the Proof of Work Mechanism
To understand how to mine Bitcoin, one must first grasp the underlying consensus protocol known as Proof of Work (PoW). This protocol is the cryptographic foundation that ensures the security and immutability of the blockchain without the need for a central authority.
The Role of SHA-256 Hashing
Bitcoin mining utilizes the SHA-256 (Secure Hash Algorithm 256-bit) hashing function. In technical terms, miners are engaged in a race to find a specific output—a hash—that is lower than a target value set by the network. This process involves taking a block header as input and passing it through the SHA-256 algorithm. Because the output of a hash function is entirely unpredictable, miners must repeatedly change a small variable called a “nonce” (number used once) and re-hash the data until a valid result is found. This “brute force” computation is what requires massive amounts of processing power.
Difficulty Adjustments and Block Rewards
The Bitcoin protocol is designed to produce a new block approximately every ten minutes. To maintain this consistency despite fluctuations in the total computational power (hash rate) of the network, the protocol includes a “difficulty adjustment” mechanism. Every 2,016 blocks (roughly every two weeks), the network evaluates how long it took to mine those blocks. If the blocks were found too quickly, the difficulty increases; if too slowly, it decreases. This self-regulating system ensures that as more efficient hardware enters the market, the issuance of Bitcoin remains controlled and predictable.
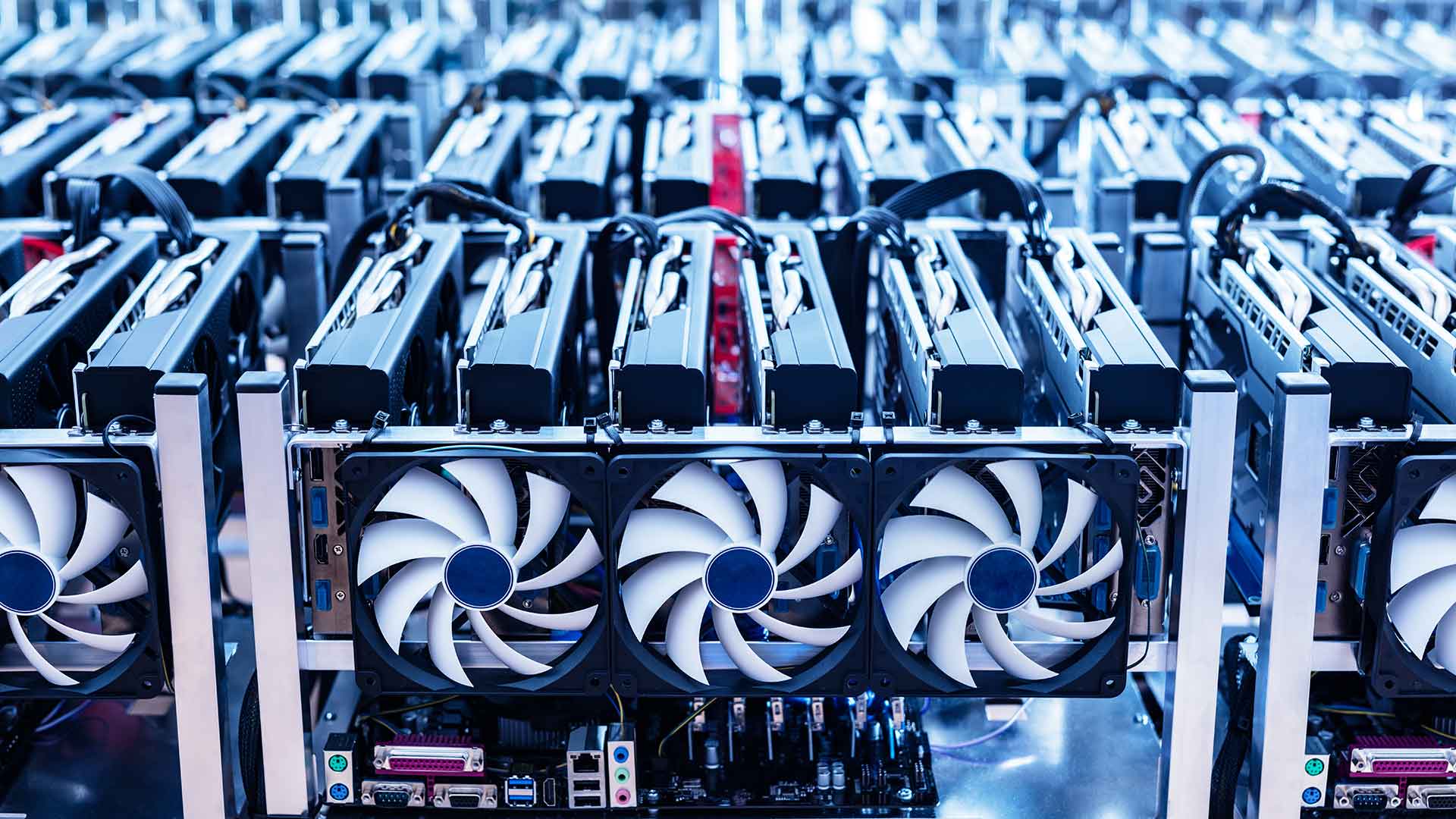
Essential Hardware for Modern Bitcoin Mining
The days of using a Central Processing Unit (CPU) or a Graphics Processing Unit (GPU) to mine Bitcoin are long gone. The network has transitioned through several stages of hardware evolution, leading to the current standard: the Application-Specific Integrated Circuit (ASIC).
The Evolution from CPUs to ASICs
In the early days of Bitcoin (2009–2010), mining could be done on a standard laptop. However, as the network grew, miners moved to GPUs, which could handle the repetitive mathematical calculations of SHA-256 much faster. By 2013, the first ASICs were introduced. Unlike general-purpose hardware, an ASIC is designed for one task and one task only: calculating SHA-256 hashes. This specialization makes ASICs thousands of times more efficient than even the most powerful gaming computers, effectively pricing out all other forms of hardware from the Bitcoin ecosystem.
Key Performance Metrics: Hash Rate and Efficiency
When selecting mining hardware, technical specifications are paramount. The two most critical metrics are:
- Hash Rate (TH/s): This measures how many trillions of hashes the machine can calculate per second. Modern flagship miners, such as the Antminer S21 or Whatsminer M60 series, produce hash rates well exceeding 200 TH/s.
- Efficiency (J/TH): This measures how much energy (in Joules) is required to produce one Terahash of computing power. As energy costs are the primary overhead in mining, lower J/TH ratings indicate a more technologically advanced and profitable machine.
Cooling and Infrastructure Requirements
ASIC miners generate an immense amount of heat because they operate at maximum capacity 24/7. Managing this thermal output is a significant technical challenge. Most miners utilize high-RPM (revolutions per minute) fans to pull air across heat sinks. However, industrial operations are increasingly moving toward Immersion Cooling. In this setup, the ASIC boards are submerged in a non-conductive, dielectric fluid that absorbs heat more efficiently than air. This not only allows for higher overclocking potential but also extends the lifespan of the hardware by protecting it from dust and humidity.
Choosing and Configuring Mining Software

Hardware alone cannot communicate with the Bitcoin blockchain; it requires a software layer to manage the hashing process, communicate with the network, and report performance data back to the operator.
Popular Mining Software Options
Most modern ASICs come with pre-installed firmware from the manufacturer. However, many professional miners opt for third-party “aftermarket” firmware, such as Braiins OS+ or LuxOS. These software packages offer advanced features like:
- Autotuning: Automatically adjusting the frequency and voltage of individual hashing chips to find the “sweet spot” of performance and efficiency.
- Thermal Protection: Shutting down the hardware if temperatures exceed a safe threshold.
- Real-time Monitoring: Providing detailed APIs to track hash rates and hardware health through centralized dashboards.
Connecting to the Stratum Protocol
Mining software communicates with the network using the Stratum protocol. This is a messaging protocol that allows the mining hardware to receive “jobs” from a pool and submit “shares” (valid hashes) back to the server. When configuring your software, you must input a Stratum URL provided by your mining pool. This technical handshake ensures that the work your hardware performs is correctly attributed to your account, facilitating accurate payouts.
Monitoring Tools and Remote Management
For those running more than one or two machines, manual monitoring is impossible. Technical setups often include a “Management Proxy” or a dedicated monitoring server. Tools like Foreman or Awesome Miner allow operators to manage hundreds of ASICs from a single interface, perform bulk firmware updates, and receive alerts via mobile apps if a machine goes offline or a fan fails.
The Logistics of Mining Pools vs. Solo Mining
Because the Bitcoin network’s total hash rate is so high, the statistical probability of a single ASIC miner finding a block on its own is nearly zero. This has led to the technical necessity of mining pools.
How Mining Pools Distribute Work
A mining pool acts as a central coordinator that combines the computational power of thousands of individual miners. The pool server breaks the cryptographic puzzle into smaller “shares.” When a miner in the pool finds a hash that meets the pool’s lower difficulty threshold, they submit it as proof of work. If any member of the pool finds a hash that meets the network’s actual difficulty, the entire pool is rewarded, and the Bitcoin is distributed among members based on their contributed hash rate.
Payout Schemes: PPS vs. PPLNS
There are several technical methods for calculating how rewards are distributed within a pool:
- PPS (Pay Per Share): The pool pays a flat rate for every valid share submitted, regardless of whether the pool actually finds a block. This offers the most stable income but usually comes with higher pool fees.
- PPLNS (Pay Per Last N Shares): This method only pays out when the pool actually finds a block, looking back at the shares contributed during a specific window of time. This is more variable but often more profitable for long-term, consistent miners.
Securing Your Mining Operation and Digital Assets
Mining is a technical target for cyberattacks. From “jackpotting” attacks on firmware to network-level intrusions, security must be integrated into every step of the setup.
Network Security and Firewall Configuration
Mining hardware should never be exposed directly to the public internet. A secure setup involves placing ASICs behind a robust firewall and using a Virtual Private Network (VPN) for remote access. Furthermore, miners should disable unnecessary services on the ASIC’s control board, such as SSH or Telnet, which are frequent entry points for malware designed to redirect hashing power to an attacker’s wallet.

Secure Wallet Integration and Node Management
The final step in the technical chain is the receipt of mined Bitcoin. For maximum security and privacy, advanced miners run their own Bitcoin Full Node. By connecting their mining pool payouts to a wallet derived from their own node, they can verify their own transactions without relying on third-party block explorers. Furthermore, using “Cold Storage” (hardware wallets like Trezor or Ledger) for long-term accumulation of rewards ensures that even if the mining software or network is compromised, the earned assets remain safe in an offline environment.
In conclusion, Bitcoin mining is a complex synergy of high-performance computing, thermodynamics, and network protocols. By mastering the hardware specifications of ASICs, optimizing software through custom firmware, and implementing rigorous security protocols, an operator can contribute effectively to the security of the global Bitcoin network while maintaining a stable and professional technical environment.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.