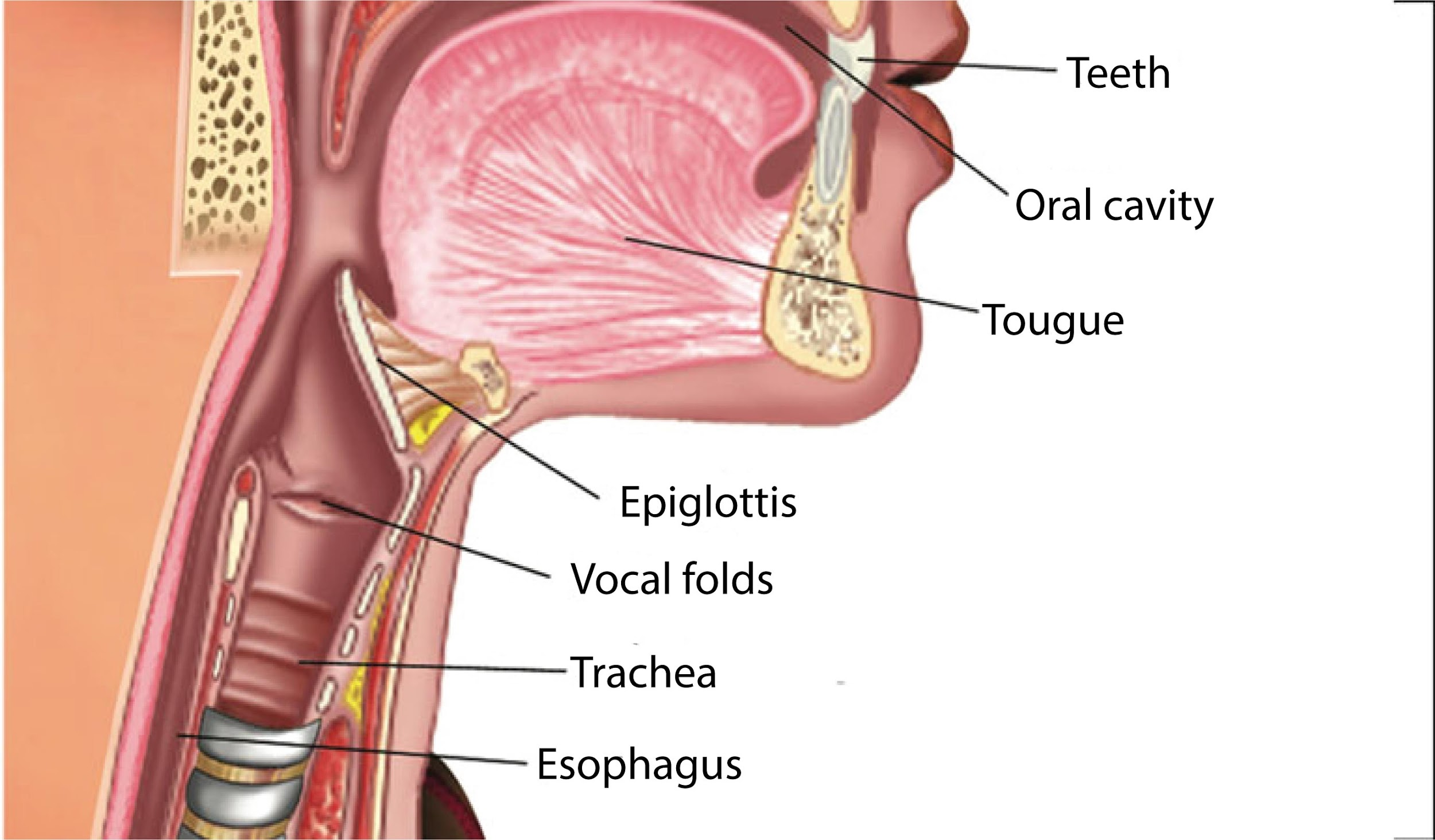
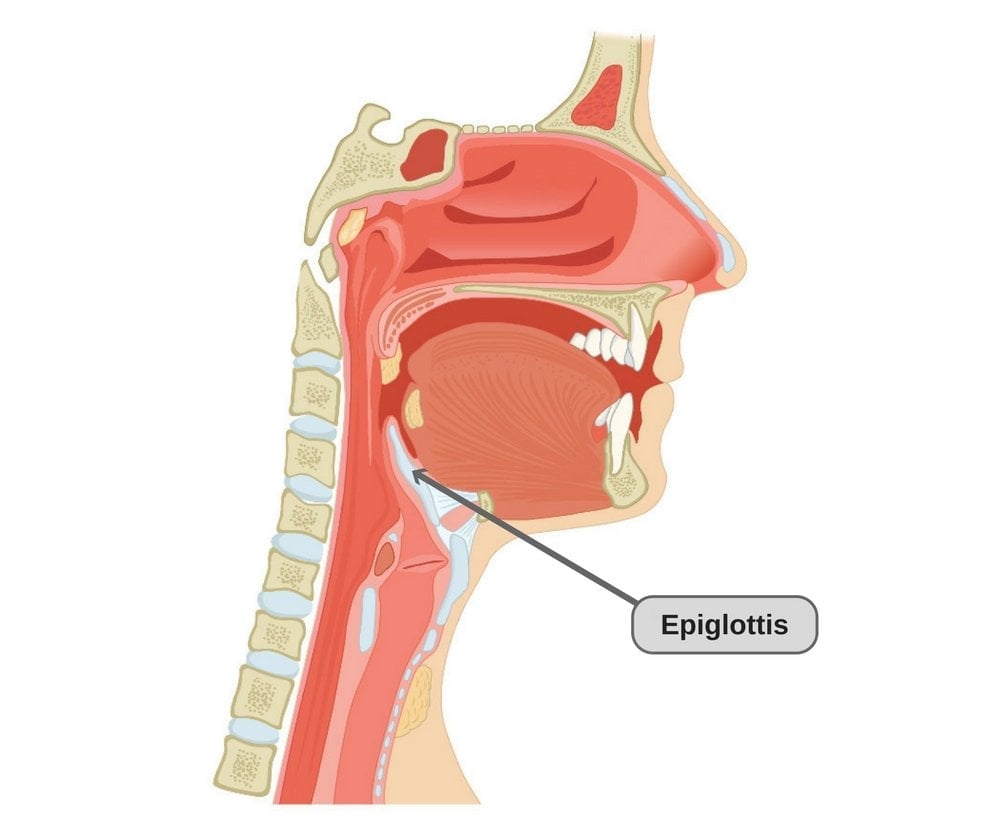
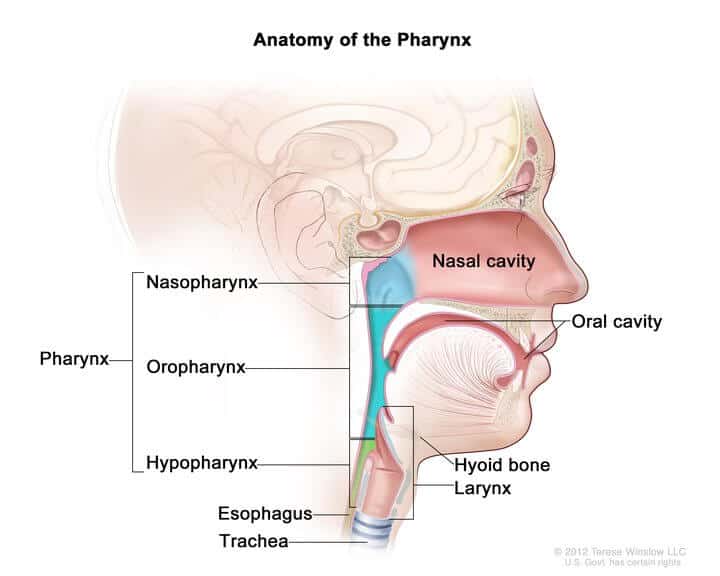
In the intricate design of the human body, a small yet incredibly vital structure acts as the guardian of our airways: the epiglottis. This leaf-shaped flap of cartilage, situated at the base of the tongue, meticulously folds down during swallowing, sealing off the trachea (windpipe) and directing food and liquids safely into the esophagus. Without this critical preventative mechanism, every meal or sip of water would pose an immediate and severe threat, leading to choking, aspiration pneumonia, and potentially fatal outcomes.
This seemingly biological question, “what structure prevents food and liquids from entering the trachea,” offers a profoundly insightful metaphor for understanding the paramount importance of robust preventative mechanisms in the digital world. In the complex, interconnected realm of technology, our core digital systems – networks, databases, applications, and sensitive data – are constantly bombarded by “food and liquids” in the form of malicious data, cyber threats, unauthorized access attempts, and system vulnerabilities. Just as the body relies on the epiglottis, the digital ecosystem demands sophisticated “structures” to safeguard its integrity, prevent catastrophic breaches, and ensure continuous operation. This article will delve into these digital preventative structures, exploring their architecture, function, and the critical role they play in fortifying our technological infrastructure against an ever-evolving landscape of threats.
The Digital Epiglottis: Safeguarding Core Infrastructure
The analogy of the epiglottis vividly underscores the non-negotiable need for proactive defense in the digital sphere. Our core digital infrastructure—the “trachea” of our technological world—is a vital conduit for information, services, and operations. Any compromise or contamination, much like food entering the windpipe, can have immediate and severe repercussions.
Understanding the Analogy
To fully appreciate this metaphor, it’s essential to map its components to the digital realm. The “trachea” represents critical digital pathways and repositories: corporate networks, cloud environments, sensitive databases, proprietary applications, and user accounts. The “food and liquids” are the myriad threats aiming to infiltrate or disrupt these systems: malware (viruses, ransomware, spyware), phishing attempts, unauthorized access, SQL injections, DDoS attacks, and even accidental data corruption from legitimate but flawed inputs. The “structure” we seek to identify and understand is the comprehensive, layered security architecture designed to prevent these harmful elements from reaching and compromising the core digital functions.
The Imperative of Prevention
In cybersecurity, the adage “an ounce of prevention is worth a pound of cure” has never been more relevant. While reactive measures like incident response and disaster recovery are crucial, they address the aftermath of a failure. True resilience stems from preventative design—building systems that are inherently secure and resilient from the ground up. This proactive mindset recognizes that waiting for a breach to occur is akin to waiting to choke before learning to swallow. The goal is to establish digital “epiglottises” that automatically and continuously divert threats away from critical systems, allowing legitimate data and operations to flow unimpeded.
Beyond Simple Barriers
Just as the epiglottis is part of a larger swallowing reflex involving many muscles and nerves, digital prevention isn’t a single “fix.” It’s a complex interplay of technologies, policies, processes, and human vigilance. A truly effective digital defense system is a layered architecture, often referred to as “defense-in-depth,” where multiple security controls are strategically placed throughout an organization’s IT infrastructure. This ensures that if one “structure” fails or is bypassed, others are there to catch the threat, preventing it from reaching the most critical “airways.”
Architectural Pillars of Digital Defense
The “structures” that prevent digital “food and liquids” from entering the “trachea” are manifold, forming robust layers of protection. These architectural pillars are designed into every facet of the digital ecosystem, from network perimeters to individual applications and user identities.
Network Security Mechanisms
At the very perimeter of a digital system, network security acts as the first line of defense.
- Firewalls: These are fundamental “gates” that control incoming and outgoing network traffic based on predefined security rules. They inspect data packets, blocking unauthorized access attempts and preventing malicious traffic from reaching internal networks, much like a security guard checking IDs at an entrance.
- Intrusion Detection/Prevention Systems (IDS/IPS): These systems continuously monitor network traffic for suspicious activity and known attack patterns. An IDS alerts administrators to potential threats, while an IPS actively blocks or drops malicious packets, acting as an automated bouncer.
- Virtual Private Networks (VPNs): For remote access, VPNs create secure, encrypted tunnels over public networks, ensuring that data transmitted between a remote user and the corporate network remains private and protected from eavesdropping, much like a secure, enclosed pathway.
Access Control and Identity Management
Controlling who can access what, and when, is a critical preventative structure.
- Authentication and Authorization: Authentication verifies a user’s identity (e.g., username/password, biometrics), while authorization determines what resources that verified user can access. This ensures only legitimate users, like specific enzymes in the body, can interact with specific functions.
- Multi-Factor Authentication (MFA): Requiring two or more verification factors significantly strengthens authentication, making it much harder for attackers to gain access even if they steal credentials.
- Principle of Least Privilege (PoLP): This security principle dictates that users and processes should be granted only the minimum access rights necessary to perform their job functions. This limits the potential damage an attacker can inflict if they compromise an account, minimizing the “volume” of “food” that can enter if defenses are breached.
Secure Software Development Lifecycle (SSDLC)
Security must be baked into software from its inception, not bolted on as an afterthought.
- Shifting Left: Integrating security practices (threat modeling, secure coding guidelines, vulnerability scanning) at every stage of the development lifecycle, from design to deployment, ensures that potential weaknesses are identified and remediated early, preventing vulnerabilities from becoming exploitable entry points.
- Code Review and Static/Dynamic Analysis: Automated tools and manual reviews help identify security flaws in code before it goes live, catching “malformed food” before it’s ever served.
Data Protection Strategies
Protecting data itself, regardless of its location or transmission, is a fundamental preventative measure.
- Encryption: Encrypting data at rest (on servers, storage devices) and in transit (over networks) renders it unreadable to unauthorized parties, even if they manage to bypass other defenses. This makes the “food” unpalatable and useless to an attacker.
- Data Loss Prevention (DLP): DLP solutions monitor, detect, and block the unauthorized transmission of sensitive information, preventing “liquids” from leaking out of the “trachea” to unintended destinations.
- Backup and Recovery: While not strictly preventative in blocking initial entry, robust backup and recovery systems act as a critical safety net, allowing organizations to restore operations and data after a successful attack, preventing permanent “damage to the lungs.”
Proactive Threat Intelligence and Incident Response Readiness
Beyond static architectural controls, continuous vigilance and the ability to adapt are crucial. The digital environment is constantly evolving, with new “food” and “liquids” being engineered daily.
Anticipating the Digital Dangers
Effective prevention requires understanding the adversary.
- Threat Intelligence Feeds: Subscribing to and analyzing real-time threat intelligence provides insights into emerging attack vectors, vulnerabilities, and attacker tactics, techniques, and procedures (TTPs). This allows organizations to proactively strengthen their defenses against anticipated “dangers.”
- Vulnerability Research and Patch Management: Regularly scanning for vulnerabilities in systems and applications, combined with a robust patch management program, ensures that known weaknesses are closed before attackers can exploit them.
Continuous Monitoring and Anomaly Detection
Constant surveillance helps identify when preventative structures might be failing or under attack.
- Security Information and Event Management (SIEM): SIEM systems aggregate and analyze security logs from various sources across the IT infrastructure, providing a centralized view of security events and helping detect anomalies that could indicate a breach.
- Endpoint Detection and Response (EDR): EDR solutions monitor endpoints (laptops, servers) for malicious activity, providing detailed visibility and enabling rapid response to threats that may have bypassed perimeter defenses.
- Behavioral Analytics: AI and machine learning are increasingly used to establish baselines of normal user and system behavior, flagging deviations that could indicate a compromise or internal threat.
The Human Element as a Critical Structure
Technology alone is not enough. The human factor is often the weakest link, but also potentially the strongest defense.
- Security Awareness Training: Educating employees about phishing, social engineering, and safe computing practices empowers them to become an active “structure” in preventing attacks, recognizing and diverting “poisoned food” before it enters the system.
- Fostering a Security-First Culture: Embedding security into an organization’s DNA, where every employee understands their role in maintaining cybersecurity, creates a collective “immune system” against threats.
Incident Response Planning
Even the best preventative measures can fail. A well-defined incident response plan is like having a clear protocol for what to do if food does enter the trachea – swift, coordinated action to mitigate harm. This includes documented procedures for identification, containment, eradication, recovery, and post-incident analysis.
The Repercussions of Digital Aspiration: When Defenses Crumble
When digital “food and liquids” breach the “trachea,” the consequences are severe, often far-reaching, and costly. The failure of preventative structures can lead to a cascade of negative impacts.
Data Breaches and Reputational Damage
The most immediate and public consequence of a security failure is often a data breach. Compromised sensitive information—customer data, intellectual property, financial records—can lead to immense financial costs from investigations, remediation, legal fees, and regulatory fines. Beyond monetary impacts, a breach erodes customer trust and severely damages an organization’s brand reputation, which can take years to rebuild.
Operational Downtime and Business Interruption
Cyberattacks can lead to system outages, rendering critical business operations impossible. Ransomware attacks, for instance, encrypt systems and data, effectively halting productivity. Downtime translates directly to lost revenue, decreased productivity, and potentially critical service disruptions for customers or stakeholders, much like a compromised airway leading to immediate oxygen deprivation.
System Compromise and Data Integrity Issues
Beyond mere access, attackers can manipulate or corrupt data, leading to integrity issues that can undermine business decisions, financial reporting, and operational efficiency. Malware can persistently reside within systems, siphoning information or creating backdoors for future attacks, subtly poisoning the entire system from within.
Regulatory Penalties and Compliance Violations
Many industries are subject to stringent data protection regulations (e.g., GDPR, HIPAA, PCI DSS). Failure to adequately protect sensitive data due to compromised security structures can result in significant regulatory fines and legal liabilities, adding another layer of financial and operational burden.
Cultivating a Resilient Digital Ecosystem
Building and maintaining robust preventative structures is an ongoing journey, requiring continuous adaptation and strategic investment. The goal is to cultivate a digital ecosystem that is inherently resilient and capable of withstanding sophisticated attacks.
Adopting a Zero-Trust Model
The “Zero Trust” security model operates on the principle of “never trust, always verify.” It assumes that no user, device, or application, whether inside or outside the network perimeter, should be trusted by default. Every access request is authenticated, authorized, and continuously monitored, effectively placing an “epiglottis” around every single interaction and resource.
Regular Audits and Penetration Testing
Proactive assessment of security postures is vital. Regular security audits, vulnerability assessments, and penetration testing (ethical hacking) identify weaknesses and gaps in preventative structures before malicious actors can exploit them. These exercises provide invaluable insights, akin to stress-testing the epiglottis under various conditions.
Investing in Scalable Security Solutions
The threat landscape evolves rapidly, as do technological capabilities. Organizations must invest in security solutions that can scale with their growth, adapt to new threats, and integrate seamlessly with existing infrastructure. Cloud security, AI-powered threat detection, and automated security orchestration are becoming increasingly important.
Fostering Collaboration and Knowledge Sharing
No single organization can combat cyber threats in isolation. Participating in industry-specific information sharing and analysis centers (ISACs), collaborating with cybersecurity vendors, and engaging with the broader security community allow organizations to share threat intelligence, best practices, and lessons learned, collectively strengthening the digital immune system.
Conclusion
The humble epiglottis, a marvel of biological engineering, serves as a powerful reminder of the profound importance of preventative structures. In the digital realm, where data is the lifeblood and systems are the circulatory pathways, the need for robust mechanisms to prevent malicious “food and liquids” from entering our “trachea” is paramount. From sophisticated network firewalls and stringent access controls to secure software development and a vigilant human element, these “digital epiglottises” are not merely add-ons but foundational pillars of a resilient technological future. As cyber threats grow in sophistication and volume, a proactive, layered, and continuously adaptive approach to security architecture and design is not just a best practice—it is an existential imperative for every organization operating in the digital age. The health and functionality of our digital ecosystems depend entirely on our ability to build, maintain, and evolve these critical preventative structures.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.