In everyday language, the word “collision” evokes images of physical impact—two vehicles meeting on a highway or particles smashing together in a high-energy physics lab. However, in the realm of technology, “collision” carries a much more nuanced, logical, and often invisible meaning. From the way our home Wi-Fi functions to the foundational security of global banking systems, the concept of a collision is a fundamental challenge that engineers and developers must solve.
In the tech sector, a collision generally refers to a situation where two or more pieces of data attempt to occupy the same space or are assigned the same identifier within a system. Whether it is a network transmission, a cryptographic hash, or a database entry, collisions represent a breakdown in the intended uniqueness or timing of digital processes. Understanding what collision means in these contexts is essential for grasping how modern digital infrastructure maintains its speed, integrity, and security.
Network Collisions: The Mechanics of Data Transmission
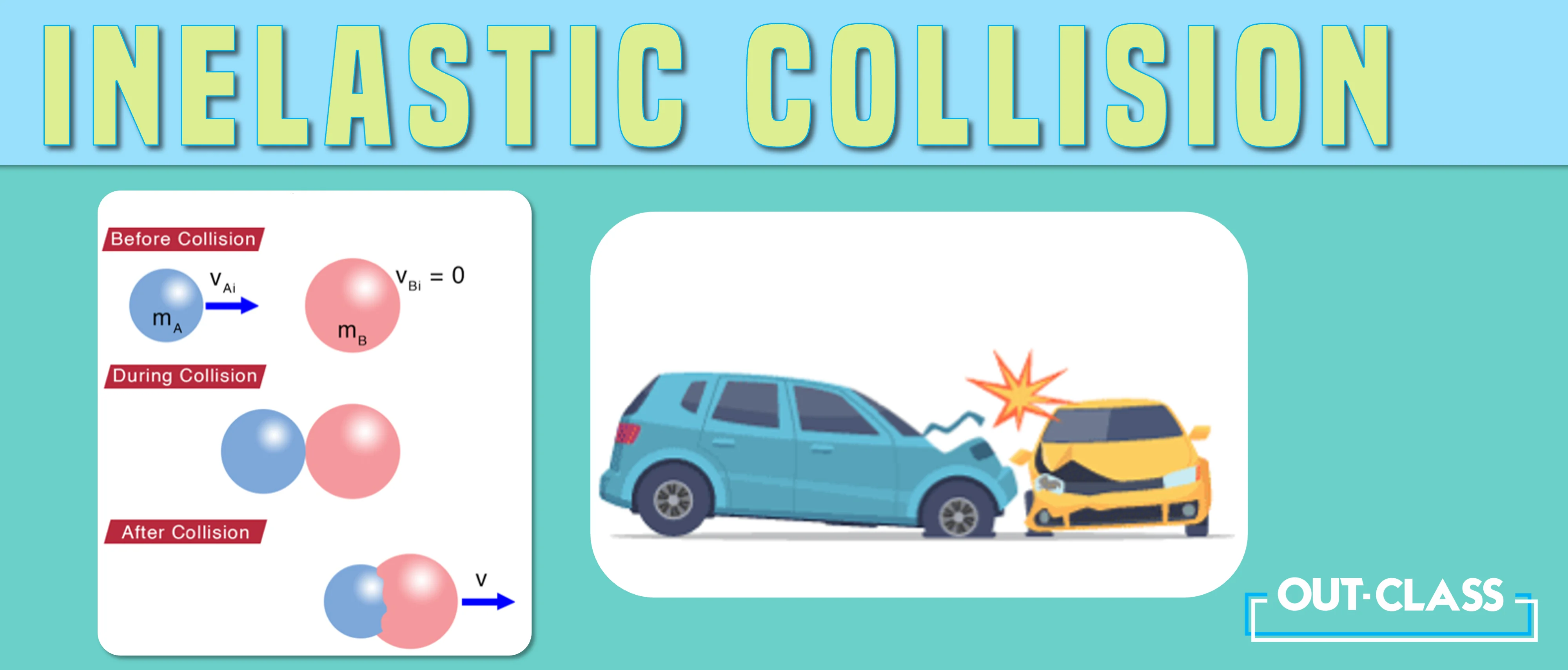
At the most basic level of hardware and networking, a collision occurs when two devices on the same network segment attempt to transmit data packets simultaneously. In the early days of the internet, when computers were connected via shared hubs, this was a constant hurdle.
How CSMA/CD Manages Shared Media
To handle these inevitable overlaps, the industry developed the Carrier Sense Multiple Access with Collision Detection (CSMA/CD) protocol. Imagine a room full of people trying to have individual conversations. If two people start talking at the exact same moment, their voices overlap, and the message is lost. In networking, CSMA/CD acts as the social etiquette for data.
Before a device sends a packet, it “listens” to the wire to see if it is clear. If two devices listen, hear silence, and transmit at once, a collision occurs. The electrical signals interfere with each other, corrupting the data. The protocol detects this, sends a “jam signal,” and forces both devices to wait for a random micro-interval before trying again. This random delay prevents them from colliding a second time.
The Impact of Collision Domains on Performance
A “collision domain” is a specific section of a network where data packets can collide with one another. In modern networking, the transition from hubs to switches has largely eliminated the frequent collisions of the past. While a hub broadcasts data to every port, a switch creates a dedicated, virtual circuit between the sender and the receiver.
By isolating traffic, switches effectively reduce the size of the collision domain to just two points: the switch port and the connected device. In full-duplex communication—where devices can send and receive at the same time—the concept of a traditional network collision is almost entirely mitigated. However, understanding this history is vital for troubleshooting legacy systems and optimizing wireless networks (Wi-Fi), which still rely on collision avoidance (CSMA/CA) because they share the same airwaves.
Hash Collisions: The Architecture of Data Security
While network collisions are about timing and physical signals, “hash collisions” are a mathematical phenomenon. This is perhaps the most critical application of the term in modern software engineering and cybersecurity.
Defining Cryptographic Hash Functions
A hash function is an algorithm that takes an input of any size (from a single letter to the entire contents of a library) and produces a fixed-size string of characters, often called a “digest” or “fingerprint.” A perfect hash function should be “collision-resistant,” meaning that no two different inputs should ever produce the same output.
For example, if you hash the word “Apple,” you get a specific string. If you hash “Apple1,” you should get a completely different string. A collision occurs when Input A and Input B both result in Hash X. In the world of data, this is a major problem because hashes are used to verify the integrity of files, secure passwords, and power the blockchain.
The Risks of Collision Attacks
If a hash function is found to be susceptible to collisions, it is considered “broken.” Historically, the MD5 and SHA-1 algorithms were the gold standards for digital security. However, researchers eventually discovered ways to deliberately create two different files that produced the same hash.
This discovery led to the “collision attack.” In a security context, an attacker could create a piece of malware that has the same hash as a legitimate software update. If the system only checks the hash to verify the file’s safety, it would unknowingly run the malware. This is why the tech industry has migrated to more robust algorithms like SHA-256 and SHA-3, where the mathematical probability of a collision occurring by accident or by force is so infinitesimally small that it is considered impossible with current computing power.
Data Collisions in Software Engineering and AI
As we move from the hardware and security layers into the application layer, the meaning of collision shifts again. Here, it often refers to conflicts in data management and the challenges of concurrent processing.
Concurrent Programming and Race Conditions
In modern software, applications often perform multiple tasks at once through “multi-threading.” A collision in this context—often called a race condition—occurs when two threads attempt to modify the same variable or memory address at the same time.
If Thread A tries to add 1 to a counter and Thread B tries to subtract 1 at the exact same millisecond, the final value depends on which thread “wins” the race. If the system does not have proper “locking” mechanisms to prevent this collision of logic, the data becomes corrupted, leading to software crashes or unpredictable behavior. Developers use “mutexes” (mutual exclusions) to ensure that only one thread can access a specific piece of data at a time, effectively acting as a traffic light to prevent logical collisions.
Training Data Collision in Machine Learning
In the rapidly evolving field of Artificial Intelligence, a new type of collision is emerging: data contamination or “training set collision.” This happens when the data used to test an AI model’s performance is accidentally included in the data used to train it.
When this collision occurs, the AI appears to be incredibly smart and accurate, but it is actually just “memorizing” the answers it has already seen. This creates a false sense of security regarding the model’s capabilities. For AI researchers, identifying and separating these data points is crucial for ensuring that the “collision” of training and testing data doesn’t result in a flawed, biased, or ineffective tool.
Mitigating Collisions in Modern Infrastructure
The history of technology is, in many ways, a history of finding more elegant ways to avoid collisions. As our data needs grow, the methods we use to keep our information separate and secure must also evolve.
Transitioning from Hubs to Switches and Fiber
The physical mitigation of collisions has been one of the greatest leaps in internet speed. By moving from shared copper wires and hubs to intelligent switches and fiber optics, we have moved from an “everyone talks at once” model to a “private express lane” model. Fiber optics, in particular, allows for massive amounts of data to travel via different wavelengths of light on the same strand, using a technique called Wavelength Division Multiplexing (WDM). This ensures that even though billions of bits are moving through the same cable, they never “collide” in a way that disrupts the signal.
Salted Hashing and Collision Resistance
In the realm of digital security, we mitigate hash collisions through “salting.” Even if a hash function has a theoretical weakness, adding a “salt”—a random string of data—to the input before hashing it makes it exponentially harder for an attacker to find a collision.
For instance, if two users have the same password, “Password123,” their hashes would normally be identical. By adding a unique salt to each, the resulting hashes become entirely different. This technique protects against pre-computed collision tables (Rainbow Tables) and ensures that even if a collision is mathematically possible, it is computationally impractical to exploit.

Conclusion
In the tech world, a “collision” is rarely a physical event, but its consequences are just as impactful. Whether it is the electrical interference of data packets on a wire, the mathematical overlap of two digital fingerprints, or the logical conflict of two threads in a program, collisions represent the friction of the digital age.
As we move toward a future defined by 5G, quantum computing, and hyper-scale AI, the definition of collision will continue to expand. However, the core challenge remains the same: how do we organize an infinite amount of information so that every piece of data has its own place, its own time, and its own unique identity? By understanding what collision means, tech professionals can better build the systems that keep our digital world running smoothly, securely, and without interference.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.