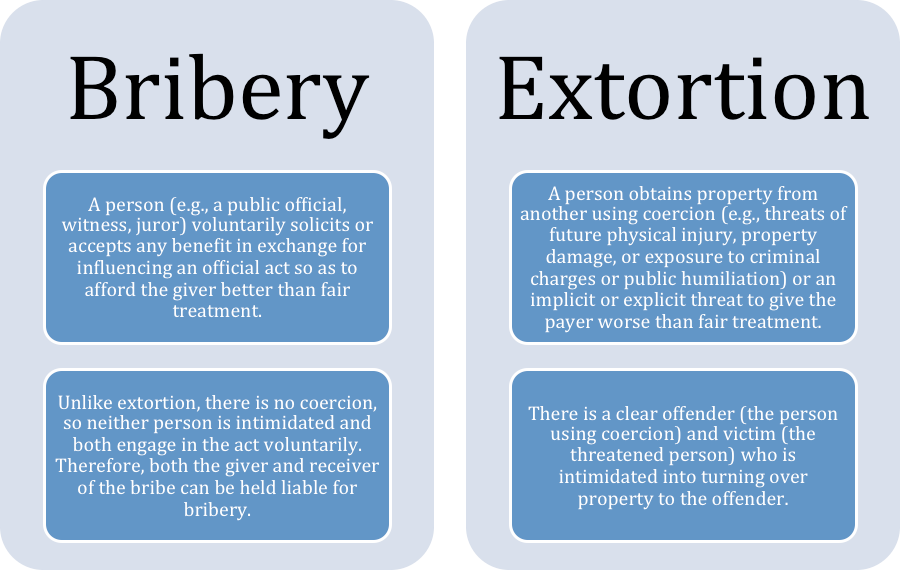
In the traditional sense, extortion has long been understood as a criminal act where an individual obtains money, property, or services from another through coercion—often involving threats of violence, property damage, or reputational harm. However, as our lives and businesses have migrated into the digital ecosystem, the definition and execution of this crime have undergone a radical transformation. In the realm of technology and digital security, extortion—specifically “cyber extortion”—has become one of the most sophisticated and prevalent threats facing global infrastructure today.
Modern extortion is no longer limited to physical intimidation. It is now a high-tech enterprise powered by encryption, anonymous cryptocurrencies, and complex social engineering. For IT professionals, business leaders, and digital citizens, understanding the technical nuances of how extortion operates in the digital age is the first step in building a resilient defense strategy.
The Mechanics of Modern Cyber Extortion
Cyber extortion is a broad category of malicious activity where threat actors hold a digital asset or service hostage until a ransom is paid. Unlike traditional theft, where the goal is to take something and disappear, extortion relies on a continuous interaction between the attacker and the victim, mediated through technology.
Understanding the Threat Actor Ecosystem
Today’s extortionists are rarely lone hackers operating from a basement. The landscape has evolved into a professionalized “Cybercrime-as-a-Service” (CaaS) economy. Ransomware-as-a-Service (RaaS) developers create the malicious code and then lease it to “affiliates” who handle the actual deployment. This specialization allows even low-skill actors to launch sophisticated extortion campaigns. These groups often have dedicated “help desks” to assist victims in purchasing Bitcoin to pay the ransom, highlighting the terrifyingly corporate nature of modern digital extortion.
Common Attack Vectors: Phishing and Vulnerabilities
Extortion typically begins with an initial breach. The most common entry point remains the human element through phishing. Attackers use social engineering to trick employees into clicking malicious links or downloading attachments that execute a payload. Beyond human error, attackers exploit unpatched software vulnerabilities (Zero-Days) and poorly secured Remote Desktop Protocol (RDP) ports. Once the perimeter is breached, the attacker moves laterally through the network to identify high-value data—financial records, intellectual property, or personal employee information—before initiating the extortion phase.
The Taxonomy of Digital Extortion Threats
Digital extortion is not a monolithic threat; it manifests in several distinct technical forms, each requiring a specific defensive posture. As technology evolves, so do the methods used to squeeze victims for capital.
Ransomware: The High-Stakes Game of Encryption
Ransomware is the most recognizable form of cyber extortion. It involves the deployment of malware that encrypts a victim’s files, making them inaccessible without a private decryption key held by the attacker. In recent years, this has evolved into “Double Extortion.” Not only is the data encrypted, but the attacker also exfiltrates (steals) a copy of the sensitive data. If the victim refuses to pay for the decryption key because they have backups, the attacker threatens to leak the sensitive information on “shame sites” on the Dark Web, damaging the victim’s brand and inviting regulatory fines.
DDoS Extortion: Weaponizing Connectivity
Distributed Denial of Service (DDoS) extortion involves a threat actor sending an ultimatum to an organization: pay a fee, or face a massive influx of traffic that will knock your website or online services offline. These attacks utilize botnets—networks of compromised IoT (Internet of Things) devices—to overwhelm a target’s bandwidth. For e-commerce platforms or financial institutions, even an hour of downtime can result in millions of dollars in lost revenue, making the “protection money” demanded by extortionists a tempting, albeit dangerous, out.
Sextortion and Personal Data Leaks
On a more individual level, tech-enabled extortion often takes the form of “sextortion.” This involves attackers claiming to have gained access to a user’s webcam or private browsing history. Using leaked passwords from old data breaches as “proof” of access, they demand cryptocurrency to keep the supposed footage private. While many of these are “spray-and-pray” spam campaigns, the technical reality of spyware and RATs (Remote Access Trojans) makes these threats credible enough to cause widespread panic.
The Architecture of Defense: Tech-Driven Solutions
To combat the rising tide of digital extortion, organizations must move beyond basic antivirus software. A modern defense-in-depth strategy focuses on making the “cost of attack” higher than the “value of the ransom.”
Zero Trust Architecture
The “Zero Trust” model operates on a simple principle: “never trust, always verify.” In an extortion context, this means that even if an attacker gains access to one part of a network (via a compromised laptop), they are blocked from moving laterally to the data center. By implementing micro-segmentation and strict Identity and Access Management (IAM), organizations can contain an extortion attempt before it reaches the “crown jewels” of the company’s data.
AI-Driven Threat Detection and EDR
Legacy security systems rely on “signatures”—known patterns of old viruses. Modern extortionists, however, create unique, polymorphic code for every attack. To counter this, businesses utilize Endpoint Detection and Response (EDR) powered by Artificial Intelligence. AI can identify “behavioral anomalies”—such as a user suddenly attempting to encrypt 5,000 files in a minute—and automatically isolate the affected machine from the network. This automated response happens at machine speed, far faster than a human security analyst could intervene.
Immutable Backups and the 3-2-1-1 Rule
The ultimate antidote to ransomware-based extortion is a robust backup strategy. However, modern malware is designed to seek out and delete backups first. The technical solution is “Immutable Backups”—data that is written once and cannot be changed or deleted for a set period, even by an administrator with full credentials. Following the 3-2-1-1 rule (3 copies of data, on 2 different media, with 1 offsite and 1 offline/immutable) ensures that even if an extortionist succeeds in encrypting the live environment, the organization can restore its operations without paying a cent.
Incident Response and Digital Recovery
When an extortion event occurs, the technical response determines the long-term survival of the organization. This phase is less about prevention and more about forensic precision.
The Role of Digital Forensics
Before any systems are wiped or restored, digital forensic experts must “preserve the scene.” This involves taking snapshots of volatile memory (RAM) and analyzing log files to determine the “Patient Zero” of the attack. Understanding how the extortionist got in is critical; if you restore your data but leave the same vulnerability open, the attacker will simply re-encrypt your network within hours of your recovery.
Decryption vs. Restoration: The Technical Dilemma
Victims often face a difficult choice: try to decrypt the files using tools provided by the attacker (if they pay) or restore from backups. Decryption is rarely 100% successful; many decryption tools provided by criminals are poorly coded and can result in data corruption. From a technical security standpoint, the “Clean Room” approach is preferred. This involves standing up an entirely new, pristine cloud environment and migrating cleaned data into it, ensuring that no “logic bombs” or backdoors left by the extortionists are carried over into the new production environment.
Future Trends in Extortion Technology
As we look toward the horizon, the tools available to extortionists are becoming increasingly sophisticated, leveraging the very same technologies designed to help us.
Deepfake Extortion
The rise of Generative AI has birthed a new frontier: Deepfake extortion. Attackers can now use a few seconds of a person’s voice or a few photos of their face to create highly convincing, fake audio or video. This technology can be used to impersonate a CEO (to authorize a fraudulent wire transfer) or to create compromising footage of an individual to demand a ransom. As AI becomes more accessible, the technical challenge for security firms will be developing “liveness detection” and “media authentication” tools to verify the reality of digital communications.

IoT and Infrastructure Vulnerabilities
The “Internet of Things” (IoT) has expanded the attack surface for extortion exponentially. In the future, we may see more “Industrial Extortion,” where attackers seize control of smart building systems—locking doors, shutting down HVAC systems, or stopping manufacturing lines—until a ransom is paid. The lack of standardized security protocols in IoT devices makes them a soft target, requiring a shift toward hardware-level security and more rigorous firmware update cycles.
In conclusion, extortion in the 21st century is a technical challenge as much as it is a criminal one. It is a battle of algorithms, encryption standards, and human psychology. By understanding the mechanics of how these threats operate and implementing a layered, tech-centric defense, individuals and organizations can protect their digital assets from those who seek to weaponize our connectivity against us. The key to resilience lies not in the hope that an attack won’t happen, but in the technical preparation that ensures an attack cannot succeed.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.