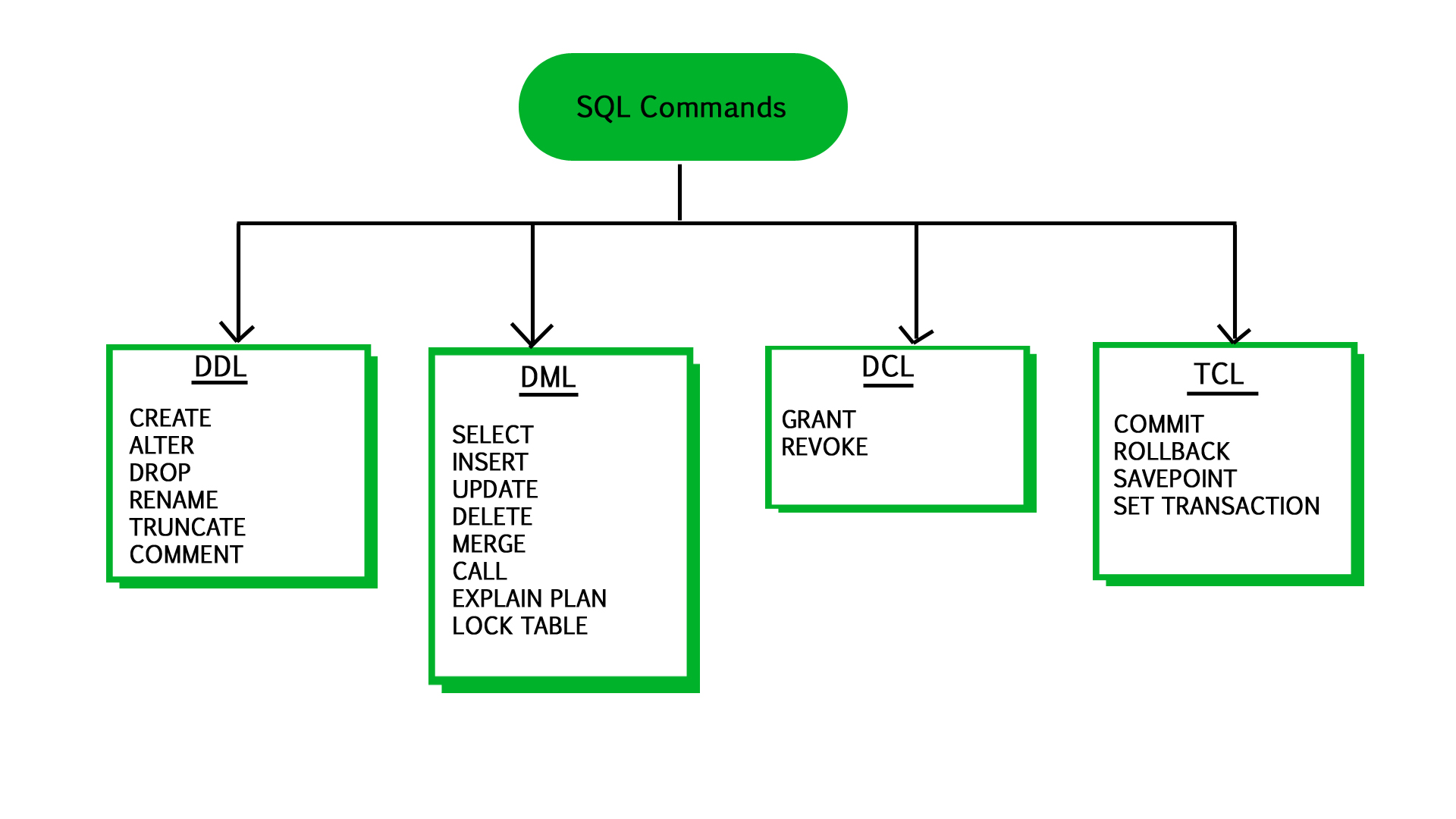
In the vast landscape of database management and software engineering, Structured Query Language (SQL) serves as the primary medium for communicating with relational databases. While many developers are intimately familiar with Data Manipulation Language (DML) for handling records and Data Definition Language (DDL) for creating schemas, a third, critical component often operates behind the scenes: Data Control Language, or DCL.
DCL is the subset of SQL commands specifically designed to control access to data within a database. It functions as the administrative layer, ensuring that only authorized users can perform specific actions on the data. In an era where data security is paramount and regulatory compliance (such as GDPR or CCPA) is mandatory, understanding DCL is not just a technical requirement for database administrators (DBAs)—it is a fundamental pillar of modern digital security and software architecture.
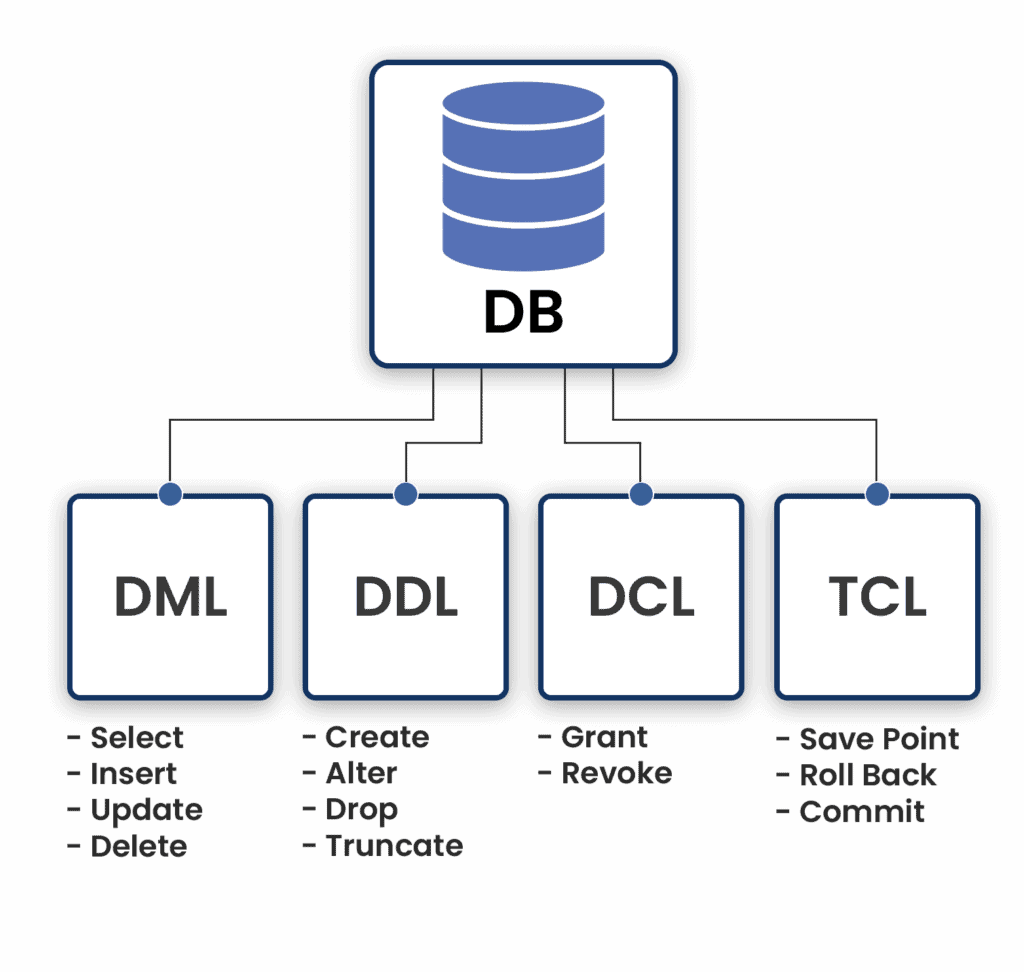
The Core Components of DCL: GRANT and REVOKE
At its heart, Data Control Language is composed of two primary commands: GRANT and REVOKE. These commands are the gatekeepers of the database environment, defining the permissions and privileges assigned to users or roles.
The GRANT Command: Assigning Privileges
The GRANT command is used to provide specific privileges to database users. These privileges can range from basic read access to the ability to modify table structures or execute complex procedures. In a typical software development lifecycle, a DBA might use the GRANT command to allow a web application’s service account to read from a “Products” table while preventing it from deleting user accounts.
The syntax for GRANT usually involves specifying the privilege (like SELECT, INSERT, or UPDATE), the object (the table or view), and the recipient (the user or role). For example, GRANT SELECT ON orders TO marketing_team; allows members of the marketing team to view the orders table without giving them the power to change any data. This granular control is essential for maintaining a secure environment where users only have the tools they need to perform their specific tasks.
The REVOKE Command: Rescinding Access
Equally important to granting access is the ability to take it away. The REVOKE command is used to withdraw previously assigned privileges. This is a critical function during employee offboarding, role changes, or when a security audit reveals that a user has excessive permissions.
Using REVOKE is a proactive security measure. If an analyst moves from the finance department to the design department, their access to sensitive payroll data must be rescinded immediately. The command ensures that access rights are not static; they are dynamic reflections of the current organizational structure and security requirements. By effectively managing the lifecycle of a privilege, organizations can prevent “privilege creep,” where users accumulate rights over time that they no longer require.
Why DCL Matters: The Intersection of Security and Accessibility
In the realm of technology trends, the focus has shifted from merely “storing data” to “protecting and governing data.” DCL is the technical manifestation of data governance. It balances the need for accessibility—ensuring developers and analysts can do their jobs—with the need for security—ensuring that sensitive data remains confidential.
Implementing the Principle of Least Privilege (PoLP)
The Principle of Least Privilege (PoLP) is a foundational concept in digital security. It dictates that any user, program, or process should have only the bare minimum privileges necessary to perform its function. DCL is the primary tool used to implement PoLP within a database environment.
When a software engineer builds a microservice, that service should not have “root” or “admin” access to the entire database. Instead, using DCL, the DBA grants the microservice access only to the specific tables and specific actions (e.g., INSERT but not DELETE) it requires. This limits the “blast radius” in the event of a security breach. If a hacker gains control of a service with limited DCL-defined permissions, they cannot drop entire tables or extract sensitive user passwords from other parts of the database.
Protecting Data Integrity and Privacy
Beyond external threats, DCL protects against internal errors. Human error remains one of the leading causes of data loss. By restricting DELETE or DROP permissions to only the most senior administrators via DCL, a company reduces the risk of a junior developer accidentally wiping a production database.
Furthermore, privacy regulations require strict control over who can see Personally Identifiable Information (PII). DCL allows organizations to mask or restrict access to specific columns (like Social Security numbers or credit card details) while still allowing users to query non-sensitive columns in the same table. This level of control is indispensable for companies that must prove to auditors that they are handling consumer data responsibly.
DCL in the Lifecycle of Database Administration
The role of a Database Administrator has evolved, but the reliance on DCL remains constant. It is integrated into the daily workflow of user management, system maintenance, and compliance reporting.
User Management and Role-Based Access Control (RBAC)
In large-scale enterprise environments, managing individual permissions for hundreds of users is inefficient and prone to error. Instead, DBAs use DCL in conjunction with Role-Based Access Control (RBAC). In this model, permissions are granted to “roles” (e.g., Developer, Analyst, Manager), and users are then assigned to these roles.
This abstraction layer simplifies management. If the requirements for the Analyst role change, the DBA only needs to update the permissions for that role once using DCL commands, and the changes automatically propagate to all users assigned to that role. This ensures consistency across the organization and reduces the administrative overhead of managing digital identities.
Auditing and Compliance via DCL Commands
Modern database systems keep detailed logs of every DCL command executed. This creates a clear audit trail of who granted what permission to whom and when. During a security audit, these logs provide evidence that the organization is following its internal security policies.
For instance, if a data breach occurs, forensic analysts will look at DCL logs to see if any unauthorized GRANT commands were executed recently. This transparency is vital for accountability. In the context of “Digital Security,” DCL acts as both a lock on the door and a camera recording who has the keys.
Best Practices for Implementing DCL in Enterprise Environments
To leverage DCL effectively, organizations should follow established best practices that align with modern software engineering standards.
Automating Permissions via Scripts and Version Control
In the age of DevOps and “Infrastructure as Code” (IaC), manually typing SQL commands into a terminal is increasingly discouraged for production environments. Instead, DCL commands should be scripted and stored in version control systems like Git.
By treating DCL commands as code, teams can perform peer reviews on permission changes before they are applied. This adds a layer of scrutiny that can catch potential security holes. Furthermore, automation tools can ensure that permissions are applied consistently across development, staging, and production environments, eliminating the “it works on my machine” syndrome caused by mismatched database privileges.
Common Pitfalls and How to Avoid Them
One of the most common pitfalls in DCL management is the “WITH GRANT OPTION” clause. This allows a user who has been granted a privilege to pass that privilege on to others. While useful in some decentralized environments, it can quickly lead to a loss of control over the permission hierarchy. In most high-security tech environments, the use of WITH GRANT OPTION is strictly limited to top-level administrators.
Another pitfall is failing to clean up permissions after a project concludes. Temporary access granted for a specific debugging task often remains in place long after the task is finished. Regular “permission pruning” sessions, where DBAs review and REVOKE unnecessary privileges, are essential for maintaining a lean and secure database posture.

Conclusion: The Future of DCL in a Cloud-Native World
As we move further into the era of cloud-native applications and AI-driven data analysis, the importance of Data Control Language only grows. Cloud providers like AWS, Azure, and Google Cloud have extended the concepts of DCL into their Identity and Access Management (IAM) systems, allowing for even more complex permission structures that span across different services.
Whether you are a developer building the next great app, a security professional guarding a corporation’s assets, or a tech enthusiast curious about how the digital world remains organized, DCL is a critical piece of the puzzle. It is the silent enforcer of order, the guardian of privacy, and the foundational tool that allows us to trust the systems that store our most valuable digital information. By mastering the commands and philosophy of DCL, we ensure that the power of data is harnessed safely and effectively in an increasingly interconnected world.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.