The world of Pokémon, at its core, is a fascinating microcosm of strategic thinking, resource management, and the exploitation of inherent strengths and weaknesses. While the creatures themselves are fantastical, the underlying principles of combat and counter-strategy are remarkably analogous to the challenges and triumphs faced in the technological landscape. Understanding what makes a particular element or system vulnerable, and subsequently developing effective countermeasures, is a cornerstone of technological advancement and security. Just as trainers meticulously research type matchups to gain an edge, tech professionals constantly analyze system vulnerabilities, identify optimal tool pairings, and devise strategies to overcome digital challenges. This article delves into the strategic insights derived from the concept of countering Electric-type Pokémon, translating these principles into actionable approaches within the tech domain, focusing on how to identify, exploit, and defend against digital “types.”
The Vulnerability Landscape: Identifying Digital “Types” and Their Weaknesses
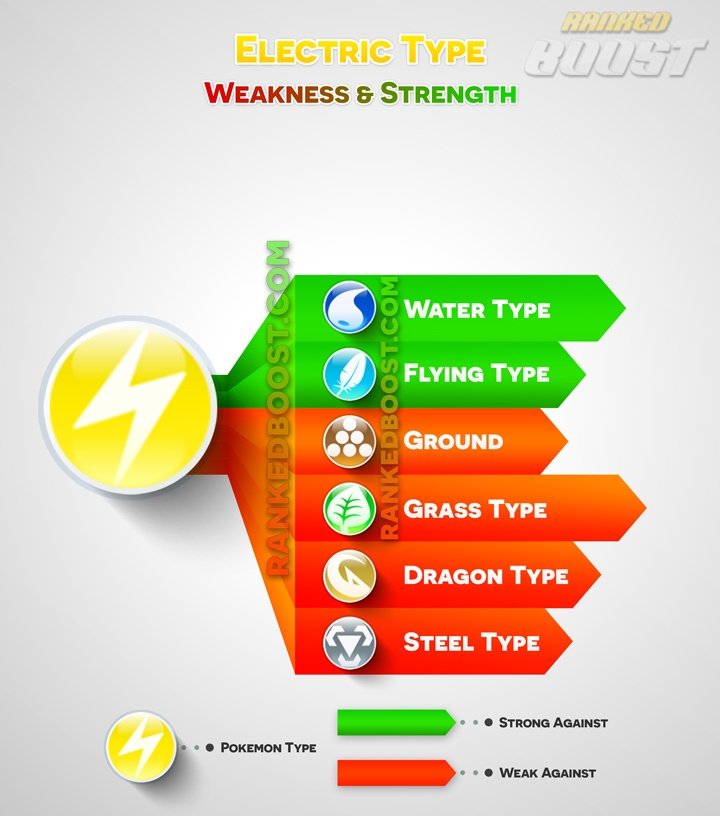
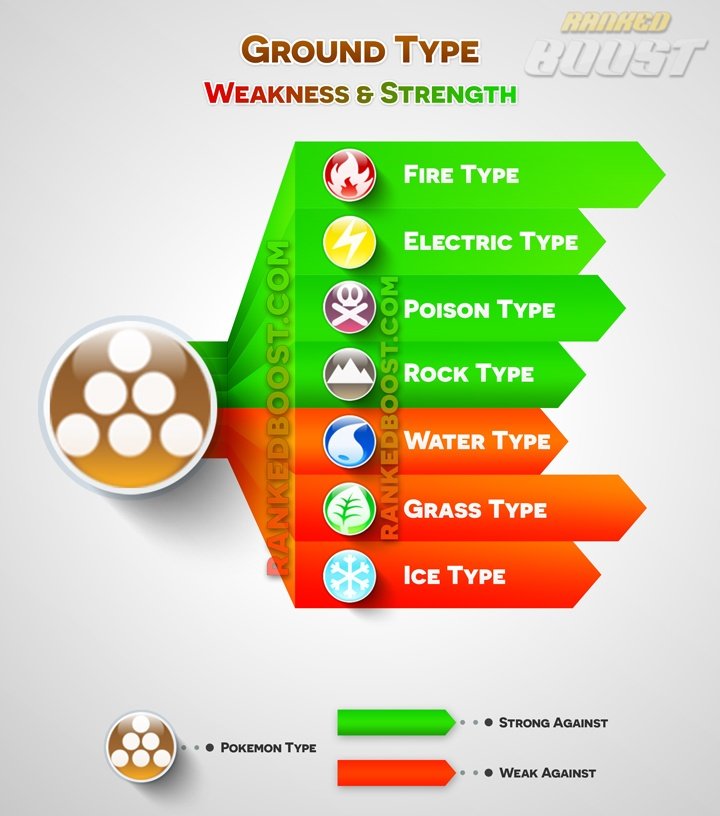
In the Pokémon universe, Electric-type Pokémon are potent, known for their speed and paralyzing attacks. However, they possess critical weaknesses, primarily to Ground-type Pokémon. This fundamental type advantage is a direct parallel to understanding the inherent vulnerabilities within any technological system. Every piece of software, every network architecture, and every digital process has its own unique set of “types” – its characteristics, protocols, and operational dependencies – and consequently, its own set of vulnerabilities.
Decoding System Architectures: Recognizing the “Electric” Components
Just as an Electric-type Pokémon relies on electrical energy, many technological systems are built upon foundational components that, while powerful, can be susceptible to specific forms of disruption. These “Electric” components in the tech world can represent:
- Network Infrastructure: Reliance on specific protocols (like older versions of TCP/IP), unpatched network devices, or poorly configured firewalls can create pathways for attackers. The very infrastructure designed to transmit data can become a conduit for malicious intrusion if not properly secured.
- Software Dependencies: Complex software often relies on numerous libraries and frameworks. A vulnerability in a single, widely used dependency can have a cascading effect, impacting numerous applications and systems. These dependencies are the “electrical currents” that power the software, and a disruption here can be devastating.
- Data Transfer Protocols: Protocols designed for efficient data exchange, such as unencrypted HTTP or insecure FTP, are akin to readily available electrical outlets. They offer convenience but are vulnerable to interception and manipulation if not adequately protected.
- Cloud Services: While offering immense scalability and flexibility, over-reliance on a single cloud provider or misconfigured cloud security settings can create a centralized point of failure, much like a powerful electric generator that can be targeted.
Identifying these “Electric” components requires a deep understanding of the system’s architecture. It involves meticulous documentation, network mapping, and code auditing to pinpoint the critical pathways and dependencies that, if compromised, could lead to widespread disruption.
Exploiting the “Ground” Advantage: Strategic Counter-Attacks
The Ground-type Pokémon’s immunity to Electric-type attacks is a powerful lesson in leveraging inherent strengths to neutralize threats. In the tech world, this translates to identifying and implementing countermeasures that are fundamentally resistant to the attack vectors of specific vulnerabilities. This isn’t about patching a crack; it’s about building a system that is intrinsically impervious to a certain class of threats.
- Network Segmentation and Isolation: Similar to how Ground-types are physically removed from electrical fields, network segmentation isolates critical systems. If one segment is compromised, the “electricity” cannot easily spread to other, more sensitive areas. This creates virtual “grounding” for your digital assets.
- Encryption and Obfuscation: Encrypting sensitive data renders it unintelligible to unauthorized parties, even if intercepted. This is akin to diverting the electrical current through an insulated pathway, making it harmless. Obfuscation techniques can also make malicious code harder to analyze and exploit, effectively “insulating” it from easy discovery.
- Immutable Infrastructure: In DevOps and cloud environments, immutable infrastructure means that systems are replaced rather than modified. If a vulnerability is discovered, the compromised system is discarded and replaced with a known-good version. This eliminates the possibility of persistent “electrical damage” to a single instance.
- Leveraging Zero-Trust Architectures: The zero-trust model, which assumes no implicit trust and verifies every access request, acts as a robust “grounding” mechanism. It prevents the spread of threats by constantly scrutinizing every interaction, regardless of origin.
Understanding these “Ground” advantages allows for proactive defense, moving beyond reactive patching to architecting systems that are inherently resilient.
The Art of Prediction and Prevention: Anticipating “Electric” Surges
Just as experienced trainers anticipate their opponent’s moves, effective tech professionals focus on predictive analysis and preventative measures to stay ahead of emerging threats. The digital landscape is constantly evolving, with new vulnerabilities and attack vectors appearing regularly. A passive approach is a recipe for disaster.
Threat Intelligence and Foresight: Reading the Digital Aura
The Pokémon world often features moves that charge up, foreshadowing a powerful attack. In technology, this “charging up” phase is represented by threat intelligence. Gathering and analyzing information about potential threats allows organizations to anticipate “Electric” surges before they occur.
- Monitoring Vulnerability Databases: Regularly checking sources like CVE (Common Vulnerabilities and Exposures) databases provides early warnings of newly discovered weaknesses in software and hardware. This is akin to observing the atmospheric changes that precede an electrical storm.
- Analyzing Security News and Forums: Staying abreast of discussions on security forums, attending conferences, and following reputable cybersecurity researchers offers insights into emerging attack trends and methods. This provides an early warning system for potential “electrical surges” targeting specific technologies.
- Behavioral Analysis and Anomaly Detection: Implementing systems that monitor network traffic and user behavior for deviations from the norm can flag suspicious activity that might precede a full-blown attack. This is like sensing the static electricity build-up before a lightning strike.
- Penetration Testing and Red Teaming: Proactively simulating attacks on your own systems allows you to identify vulnerabilities before malicious actors do. This is the ultimate form of “reading the opponent’s mind,” testing your defenses against realistic scenarios.
Proactive Patching and Configuration Management: Insulating Against the Charge
Once potential vulnerabilities are identified, the next step is to proactively mitigate them. This is the technological equivalent of reinforcing your defenses and installing surge protectors.
- Automated Patch Management: Implementing robust systems for deploying software and security patches across all systems ensures that known vulnerabilities are addressed promptly. This is akin to regularly inspecting and reinforcing the insulation on electrical wiring.
- Secure Configuration Baselines: Establishing and enforcing secure configuration standards for all systems, applications, and devices minimizes the attack surface. This ensures that default, often insecure, settings are not exploited.
- Regular Security Audits and Reviews: Conducting periodic audits of security controls, access logs, and system configurations helps identify and rectify any misconfigurations or weaknesses that may have emerged.
- Employee Training and Awareness: Human error is a significant vulnerability. Educating employees about cybersecurity best practices, phishing attempts, and secure data handling is crucial for building a resilient human firewall. This is like ensuring everyone knows how to safely handle electrical equipment.
The Evolution of Defense: Adapting to New “Electric” Threats
The Pokémon meta-game is in constant flux, with new strategies and Pokémon emerging that can challenge established tactics. Similarly, the cybersecurity landscape is dynamic. New forms of malware, sophisticated phishing campaigns, and novel attack vectors are continuously being developed. Therefore, a static approach to security is insufficient.
Embracing Agile Security Methodologies: Responsive Adaptation
Agile methodologies, prevalent in software development, are equally applicable to cybersecurity. This means building systems and processes that are adaptable and can respond quickly to new threats.
- Continuous Integration/Continuous Deployment (CI/CD) Security: Integrating security checks and scans directly into the CI/CD pipeline ensures that vulnerabilities are identified and addressed early in the development lifecycle. This allows for rapid deployment of secure code.
- Incident Response Planning and Drills: Developing comprehensive incident response plans and conducting regular drills ensures that teams are prepared to react effectively and efficiently when a security incident occurs. This is like having a well-rehearsed strategy for dealing with power outages.
- Threat Hunting: Proactively searching for threats within your network that may have evaded automated defenses. This is a more advanced form of “reading the opponent’s moves” to find hidden strategies.

Learning from “Battles”: Post-Incident Analysis and Improvement
Every security incident, even a minor one, provides valuable learning opportunities. Analyzing what went wrong is critical for strengthening defenses against future “Electric” attacks.
- Root Cause Analysis: Thoroughly investigating the origin of a breach or security event to understand the fundamental reasons it occurred. This is like understanding why a particular electrical surge happened to prevent future occurrences.
- Lessons Learned Documentation: Documenting the findings of post-incident analyses and implementing the recommended improvements in policies, procedures, and technologies.
- Sharing and Collaboration: Contributing to the broader cybersecurity community by sharing anonymized threat intelligence and best practices helps collective defense efforts. This fosters a stronger “Pokémon League” of security professionals.
In conclusion, the strategic principles derived from understanding “what’s good against Electric Pokémon” offer a powerful framework for navigating the complex and ever-evolving digital landscape. By recognizing vulnerabilities, leveraging inherent strengths, predicting and preventing threats, and embracing adaptive security measures, organizations and individuals can build more robust, resilient, and secure technological environments, effectively protecting their digital assets from the “electric shocks” of the modern threat landscape.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.