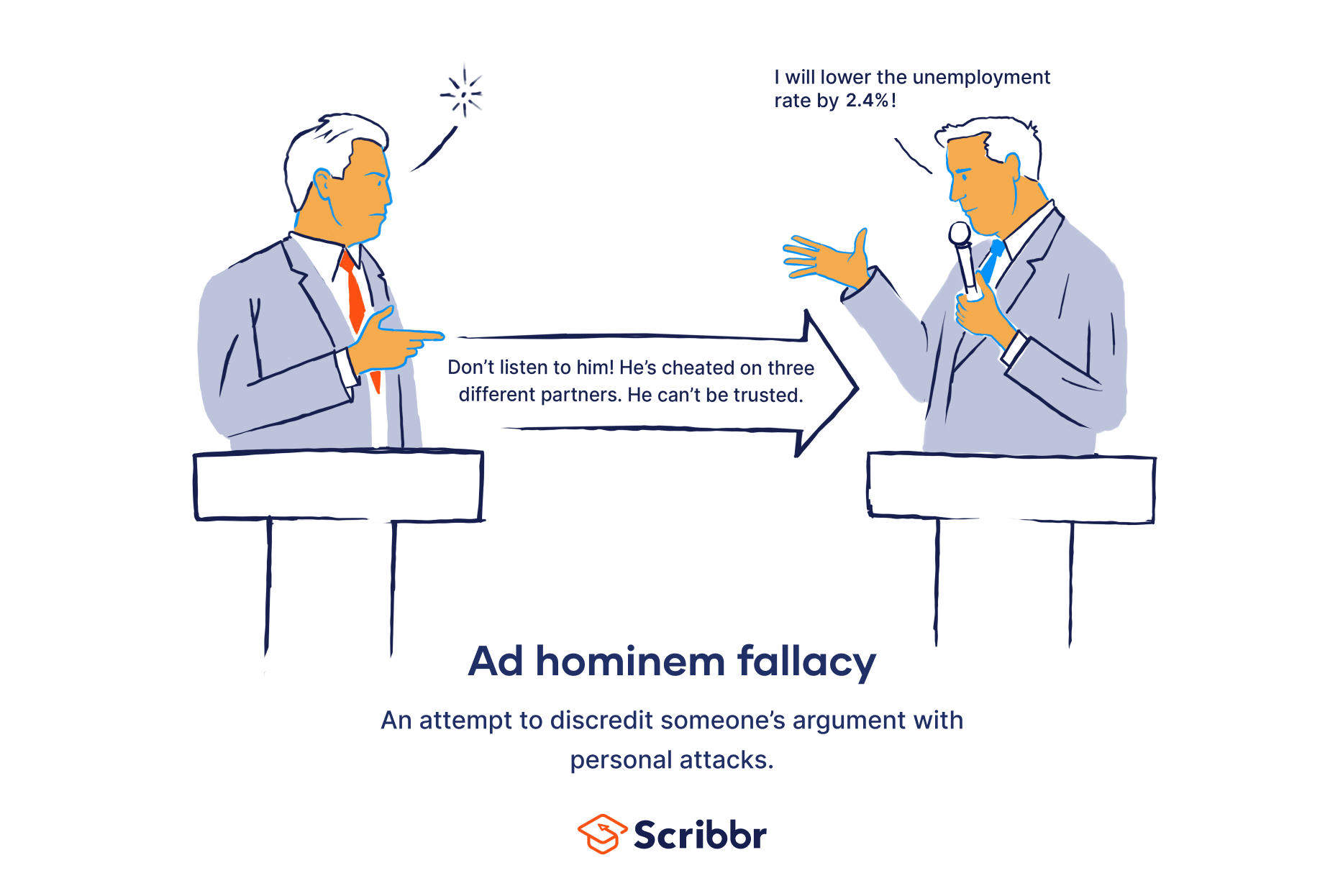
The phrase “ad hominem” often surfaces in discussions, debates, and even online skirmishes related to technology. While its roots lie in classical rhetoric, understanding its application within the tech landscape is crucial for navigating productive conversations and avoiding unproductive ones. In essence, an ad hominem attack is an argument that attacks a person’s character or personal traits rather than their argument or position. When we encounter these in the tech sphere, they can derail valuable discussions about innovation, product development, or policy, and can undermine the very foundations of collaborative problem-solving that drive the industry forward.
This article delves into the meaning of ad hominem within the specific context of technology, exploring how these fallacious arguments manifest, why they are detrimental to tech discourse, and how we can identify and counter them to foster more constructive and progress-oriented conversations. We will examine how personal attacks can cloud judgment in areas like software development, AI ethics, cybersecurity, and the evaluation of new gadgets and digital tools. By understanding the mechanics of ad hominem in this domain, we can better equip ourselves to engage in more meaningful exchanges that lead to genuine technological advancement.
The Ubiquitous Nature of Ad Hominem in Tech Discourse
The rapid evolution and often complex nature of technology can foster passionate debate. From the merits of a new programming language to the ethical implications of artificial intelligence, differing opinions are inevitable. Unfortunately, these differences can sometimes devolve into personal attacks, obscuring the substance of the technical or strategic arguments. Understanding the prevalence of ad hominem is the first step to mitigating its negative impact.
Identifying Personal Attacks in Technical Debates
Ad hominem arguments in tech aren’t always overt insults. They can be far more insidious, masquerading as legitimate criticisms. For instance, in a discussion about a new software feature, a comment might not address the feature’s functionality or user experience, but instead attack the programmer’s supposed lack of experience or the product manager’s perceived arrogance. This shifts the focus from the technical merits of the feature to the personal characteristics of the individuals involved. Similarly, when evaluating a new app, instead of discussing its usability, efficiency, or security, one might dismiss it by saying, “Well, the CEO of that company is notoriously difficult to work with, so the app is probably bad.” This is a classic example of an ad hominem circumstantial attack, where the circumstances of the person are used to discredit their work.
The Impact on Software Development and Innovation
In the realm of software development, where collaboration and iterative improvement are paramount, ad hominem attacks can be particularly damaging. When a developer’s ideas are dismissed not on their technical feasibility or elegance, but because of a personal dislike for them or their perceived lack of seniority, it stifles innovation. Junior developers may be discouraged from sharing novel approaches, and even experienced engineers might hesitate to propose unconventional solutions if they fear personal repercussions. This can lead to a homogeneous, less creative development environment, hindering the exploration of new paradigms and ultimately impacting the quality and breadth of the software produced.
Case Studies: When Personal Attacks Undermine Tech Projects
Consider a hypothetical scenario where a company is deciding on a new cybersecurity framework. Two teams present their proposals. Team A’s lead is a well-respected but somewhat reclusive engineer known for meticulous but slow work. Team B’s lead is charismatic and has a track record of rapid delivery, but has also been involved in public disagreements with colleagues. If the decision-makers focus on the personal traits of the team leads – criticizing Team A’s lead for being “too slow” or dismissing Team B’s proposal because their leader is “difficult” – rather than the technical robustness, scalability, and cost-effectiveness of their respective proposals, they are engaging in ad hominem. This can lead to the adoption of a less secure or less efficient framework, solely based on unfounded personal judgments, with potentially severe consequences for the organization’s digital security.
The Dangers of Ad Hominem in Evaluating Tech Products and Services
When we move beyond the internal development processes and into the marketplace, ad hominem attacks can significantly warp our perception and evaluation of tech products and services. This can influence consumer choices, investment decisions, and the overall reception of new technologies.
Clouded Judgment in Gadget Reviews and App Assessments
Online reviews and tech journalism, while vital for consumer guidance, are not immune to ad hominem fallacies. A review might focus excessively on the perceived personality or public image of a company’s CEO, or on unsubstantiated rumors about the engineering team, instead of providing a rigorous assessment of a gadget’s performance, battery life, user interface, or durability. Similarly, an app review might dismiss an application based on the perceived arrogance of its developers or a negative personal experience with customer support, rather than a balanced evaluation of its features, functionality, and value proposition. This leads to biased recommendations that misinform consumers and hinder them from making informed purchasing decisions based on objective criteria.
The Influence on Investment and Market Perception
In the investment world, particularly within the volatile tech sector, ad hominem attacks can have serious financial ramifications. Investors might be swayed by negative personal anecdotes about a startup’s founder, even if the company’s underlying technology is sound and its market potential is significant. Conversely, a charismatic founder might garner investment based on their personality, even if their business plan is flawed or their product lacks innovation. This “guilt by association” or “prestige by association” can lead to misallocated capital, driving down the stock prices of promising companies or propping up those with weaker fundamentals. The market’s perception becomes less about the intrinsic value and future potential of the technology and more about the perceived character of the individuals involved.
Fueling Misinformation and Distrust in Digital Security
The realm of digital security is particularly susceptible to ad hominem when discussing vulnerabilities, breaches, or security solutions. Instead of focusing on the technical flaws in a system or the effectiveness of a security tool, discussions can devolve into blaming specific individuals or teams for mistakes. For example, after a data breach, instead of a thorough post-mortem analysis of the system’s vulnerabilities and procedural failures, the conversation might pivot to criticizing the security team’s perceived incompetence or the product manager’s alleged negligence. This deflects from genuine learning and improvement, and can foster an environment of fear and distrust, making organizations less likely to be transparent about incidents and more resistant to adopting necessary security measures.
Strategies for Countering Ad Hominem in Tech Conversations
Recognizing and effectively countering ad hominem arguments is essential for fostering productive and intellectually honest dialogue within the technology sector. This requires a conscious effort from individuals and a collective commitment to higher standards of discourse.
Promoting a Culture of Evidence-Based Argumentation
The most effective way to combat ad hominem is to champion a culture that prioritizes evidence-based argumentation. This means consistently redirecting conversations back to the substance of the issue. When someone resorts to personal attacks, it’s crucial to politely but firmly point out the fallacy and request a focus on the facts, data, or logical reasoning. For instance, if someone dismisses an AI model’s capabilities by saying, “That AI is from a company that employs questionable data collection practices, so it’s inherently biased,” one could respond by saying, “While data privacy is an important concern, let’s evaluate the model’s performance on specific benchmarks and discuss its technical architecture to understand its potential biases rather than focusing on the company’s broader practices.” This encourages critical thinking and ensures that evaluations are grounded in objective analysis.
The Role of Moderators and Community Guidelines
In online forums, community platforms, and professional networks dedicated to technology, the role of moderators and well-defined community guidelines is paramount. Moderators can actively enforce rules against personal attacks, issuing warnings or removing comments that violate these guidelines. Clear guidelines should explicitly state that discussions should focus on the merits of ideas, products, and technologies, rather than on the individuals behind them. This sets a clear expectation for respectful and constructive engagement, creating a safer and more productive environment for all participants. Regular reinforcement of these guidelines through moderation and community leadership can significantly reduce the prevalence of ad hominem tactics.

Cultivating Self-Awareness and Intellectual Humility
Ultimately, overcoming ad hominem requires a degree of self-awareness and intellectual humility from all participants. We must be mindful of our own biases and the emotional responses that can lead us to lash out personally when we disagree strongly with an idea or when our own work is criticized. This involves practicing active listening, seeking to understand opposing viewpoints, and acknowledging the possibility that we might be wrong. Developing intellectual humility means being willing to concede points, admit mistakes, and engage in a spirit of collaborative inquiry, even when stakes are high or emotions are running. By fostering these qualities, we can create a tech landscape where ideas are debated rigorously and respectfully, leading to more robust innovation and a more ethical and effective technological future.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.