The term “fenestrated” might initially evoke images of architectural design, conjuring visions of buildings adorned with strategically placed windows. However, in the realm of technology, “fenestrated” carries a distinct and crucial meaning, particularly within the rapidly evolving landscape of data management, network security, and distributed systems. To understand its technological implications is to grasp a fundamental concept that underpins many of the advanced systems we rely on daily.
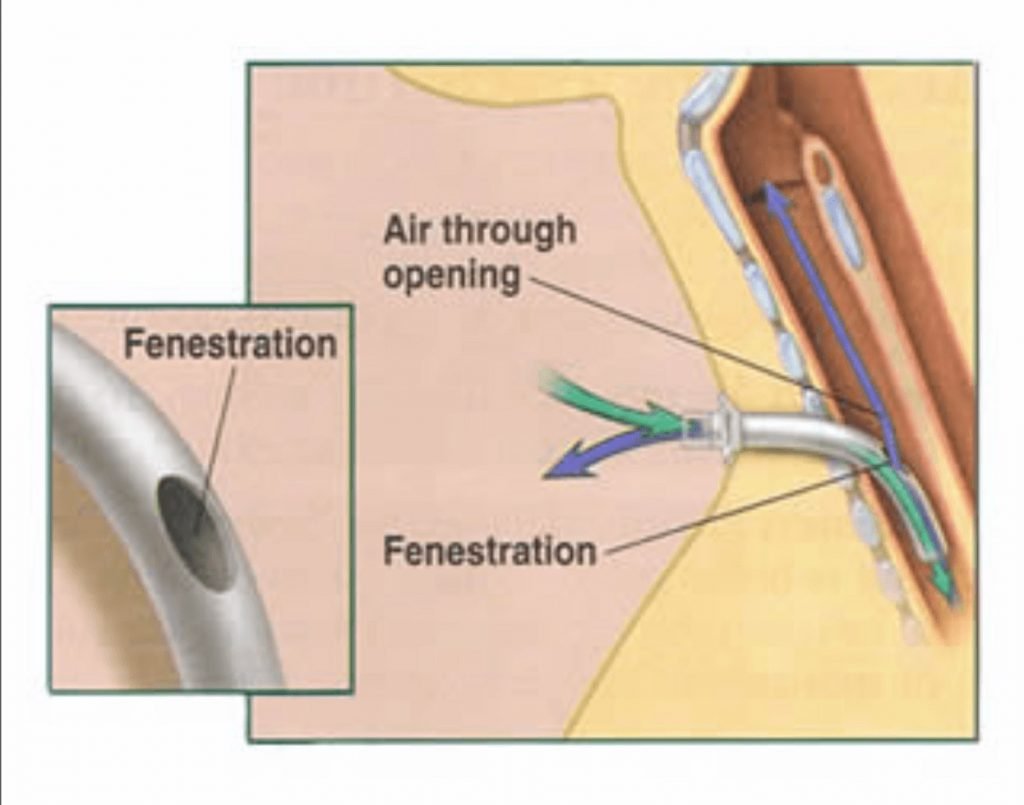
At its core, “fenestrated” describes a system, structure, or process that is characterized by the presence of openings or “windows.” In a technological context, these openings are not literal physical apertures but rather defined points of access, interaction, or controlled permeability. They serve to segment, isolate, and facilitate secure communication between different components or entities. This controlled porosity is vital for achieving both enhanced security and operational efficiency in complex technological environments.
The application of fenestration in technology is multifaceted, impacting areas such as data security, network architecture, and even the design of artificial intelligence models. By understanding what fenestrated systems entail, we gain insight into how modern technological infrastructure is built to be robust, scalable, and secure in an increasingly interconnected world. This exploration will delve into the core principles of fenestration in technology, its key applications, and the benefits it offers, ultimately clarifying its significance in our digital age.
Fenestration as a Security Paradigm: Controlled Access and Isolation
The most prominent application of the “fenestrated” concept in technology lies within the domain of security. In this context, fenestration is a deliberate design choice aimed at creating controlled pathways for data flow and interaction, thereby minimizing the attack surface and containing potential breaches. This approach moves away from monolithic, impenetrable systems towards more granularly secured environments.
The Principle of Least Privilege and Granular Access Control
At the heart of fenestrated security is the principle of least privilege, a fundamental tenet of cybersecurity. This principle dictates that any user, program, or process should have only the bare minimum permissions necessary to perform its intended function. Fenestration implements this by creating specific “windows” or interfaces through which entities can interact, rather than granting broad access to entire systems or datasets.
For instance, in a cloud computing environment, a web server might only have a fenestrated connection to a database, allowing it to retrieve specific pre-defined data points. It would not have direct access to the entire database schema or administrative functions. This limits the damage an attacker could inflict if they managed to compromise the web server. The “window” is carefully crafted to permit only the essential operations, effectively isolating sensitive data from less secure application layers. This granular control is achieved through various mechanisms like APIs (Application Programming Interfaces), microservices, and carefully configured firewalls.
Segmentation and Containment Strategies
Fenestration plays a critical role in network segmentation and breach containment. Instead of a flat, open network where a compromise in one area can easily spread to others, fenestrated networks are divided into smaller, isolated segments. Access between these segments is then strictly controlled through fenestrated interfaces.
Imagine a large enterprise network. Different departments, such as finance, HR, and engineering, would reside in separate network segments. Communication between these segments would be managed through specific, authorized channels – the “fenestrations.” If a malware outbreak were to occur in the marketing department’s segment, the fenestrated design would prevent it from easily spreading to the finance department’s highly sensitive data. This compartmentalization is a direct application of fenestration, acting like bulkheads on a ship, preventing a single breach from sinking the entire vessel. Technologies like Virtual Local Area Networks (VLANs), software-defined networking (SDN), and zero-trust architectures heavily rely on fenestrated principles for segmentation and isolation.
Secure Inter-Process Communication (IPC)
In distributed systems and microservices architectures, numerous independent processes need to communicate with each other to achieve a larger goal. Fenestration is essential for enabling this communication in a secure and efficient manner. Instead of allowing any process to directly call into any other process, fenestrated IPC mechanisms define specific, authenticated, and authorized channels for this interaction.
This ensures that only intended processes can communicate and that the data exchanged is protected from eavesdropping or tampering. For example, a microservice responsible for processing payments might expose a fenestrated API endpoint. Other services wishing to initiate a payment would interact with this endpoint, rather than directly accessing the payment service’s internal logic or data stores. This controlled communication not only enhances security but also promotes modularity and maintainability, as services can evolve independently without breaking other parts of the system, as long as the fenestrated interfaces remain consistent.
Fenestrated Architectures in Distributed Systems and Cloud Computing
The principles of fenestration are deeply embedded in the design of modern distributed systems and cloud computing platforms. These complex environments, by their very nature, involve multiple interconnected components that must operate seamlessly while maintaining security and reliability. Fenestrated architectures are key to achieving this delicate balance.
Microservices and API Gateways: The Fenestrated Interface
The rise of microservices architecture is a prime example of fenestrated design in action. Instead of building a large, monolithic application, systems are broken down into small, independent services, each responsible for a specific business capability. These microservices communicate with each other through well-defined APIs. An API gateway often acts as the primary “fenestration” point, managing external access to these microservices.

The API gateway handles concerns like authentication, authorization, rate limiting, and request routing, exposing a unified and controlled interface to the outside world. Each microservice, in turn, exposes its own fenestrated APIs for internal communication. This allows individual services to be developed, deployed, and scaled independently. If a particular service needs to be updated, it can be done without affecting the entire application, as long as its fenestrated API contract is maintained. This controlled interaction, mediated by fenestrated interfaces, is the bedrock of modern, agile software development.
Cloud Security Groups and Network Access Control Lists (ACLs)
Cloud providers leverage fenestration extensively to provide secure and manageable infrastructure. Security groups and Network ACLs are prime examples of this. These features act as virtual firewalls, controlling inbound and outbound traffic to instances (virtual servers) and subnets within a cloud environment.
A security group is essentially a fenestrated rule set that dictates which types of traffic (protocols, ports) are allowed to reach or leave an instance. For example, a web server instance might have a security group that only allows inbound traffic on port 80 (HTTP) and port 443 (HTTPS) from any IP address, while denying all other inbound traffic. It might also allow outbound traffic on specific ports required for its operation. Similarly, Network ACLs operate at the subnet level, providing a stateless layer of access control. These tools create “windows” of permitted communication, effectively fenestrating the network and allowing users to precisely define their security perimeter in the dynamic cloud environment.
Data Lakes and Warehouses: Controlled Access to Information Assets
In the realm of data management, particularly with the advent of data lakes and large-scale data warehouses, fenestration is crucial for governing access to vast repositories of information. Simply dumping all data into a single location without controls would create immense security and usability risks. Instead, fenestrated access models are employed.
This involves defining specific roles, permissions, and access patterns that govern who can view, query, or modify which datasets. For instance, a data scientist might have fenestrated access to raw sensor data for analysis, while a business analyst might only have access to aggregated and anonymized sales figures. This is achieved through features like table-level permissions, column-level security, and row-level security within databases and data warehousing platforms. The data itself is conceptually fenestrated, with access carved out through meticulously defined interfaces and controls, ensuring that information is accessible to those who need it, in the form they need it, without exposing unnecessary sensitive details.
The Impact of Fenestration on Performance and Scalability
Beyond security, the fenestrated approach has significant positive implications for the performance and scalability of technological systems. By breaking down complex systems into manageable, interacting components, fenestration enables greater efficiency and agility.
Decoupling Components for Independent Scaling
In monolithic systems, scaling often means scaling the entire application, even if only one part is experiencing high demand. Fenestrated architectures, particularly those based on microservices, allow for independent scaling of individual components. If a particular service is under heavy load, only that specific service needs to be scaled up.
This is possible because the interactions between services are mediated by well-defined fenestrated interfaces. As long as these interfaces remain stable, individual services can be replicated, optimized, and scaled independently. This leads to more efficient resource utilization and better overall system responsiveness, especially in high-demand scenarios. The ability to scale individual “fenestrated” modules rather than the entire system dramatically improves cost-effectiveness and performance under varying loads.
Improved Resilience and Fault Tolerance
Fenestrated designs inherently contribute to resilience and fault tolerance. When systems are broken down into smaller, independent units with controlled communication channels, the failure of one component is less likely to bring down the entire system.
If a microservice responsible for generating user recommendations experiences an error, the rest of the application – like user authentication or product browsing – can continue to function. The fenestrated nature of the interaction means that other services will simply not receive recommendations, or they might receive a default response, rather than experiencing a complete system outage. This fault isolation, enabled by fenestration, is critical for building robust and reliable applications that can withstand unexpected issues and maintain a high level of availability.

Streamlined Development and Deployment Cycles
For development teams, fenestrated architectures simplify the development and deployment process. With microservices, smaller, focused teams can work on individual services concurrently, each responsible for its own fenestrated API. This reduces coordination overhead and allows for faster iteration.
Furthermore, the ability to deploy individual services independently means that new features or bug fixes can be rolled out more quickly and with less risk. A faulty deployment of one microservice will have a contained impact, unlike a monolithic deployment where a single error can halt all updates. The defined “windows” of interaction between services provide clear boundaries for development, making it easier for teams to manage their codebase and release cycles effectively. This agility is a direct benefit derived from embracing fenestrated design principles in software engineering.
In conclusion, while the word “fenestrated” may seem to originate from the physical world of architecture, its conceptual application in technology is profound and far-reaching. It represents a sophisticated approach to building secure, scalable, and resilient digital systems by creating controlled openings and pathways for interaction. From granular access control and network segmentation to microservices and cloud infrastructure, fenestration is a cornerstone of modern technological design, enabling the complexity and interconnectivity that define our digital age. Understanding this concept is key to appreciating the intricate engineering that powers the technology we use every day.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.