The evolution of decentralized ledger technology has transformed the way we perceive digital assets. While the early days of cryptocurrency were reserved for cryptographic pioneers and high-level software engineers, the maturation of blockchain frameworks has democratized the process of asset creation. However, “creating a coin” is a multifaceted technical endeavor that requires a deep understanding of distributed systems, smart contract architecture, and network security.
To navigate this landscape, one must first distinguish between a “coin,” which operates on its own independent blockchain, and a “token,” which resides on an existing infrastructure like Ethereum or Solana. This guide focuses on the technical architecture, development lifecycle, and security protocols required to build a robust digital asset from the ground up within the modern technology ecosystem.

Understanding the Foundation: Blockchain vs. Token Infrastructure
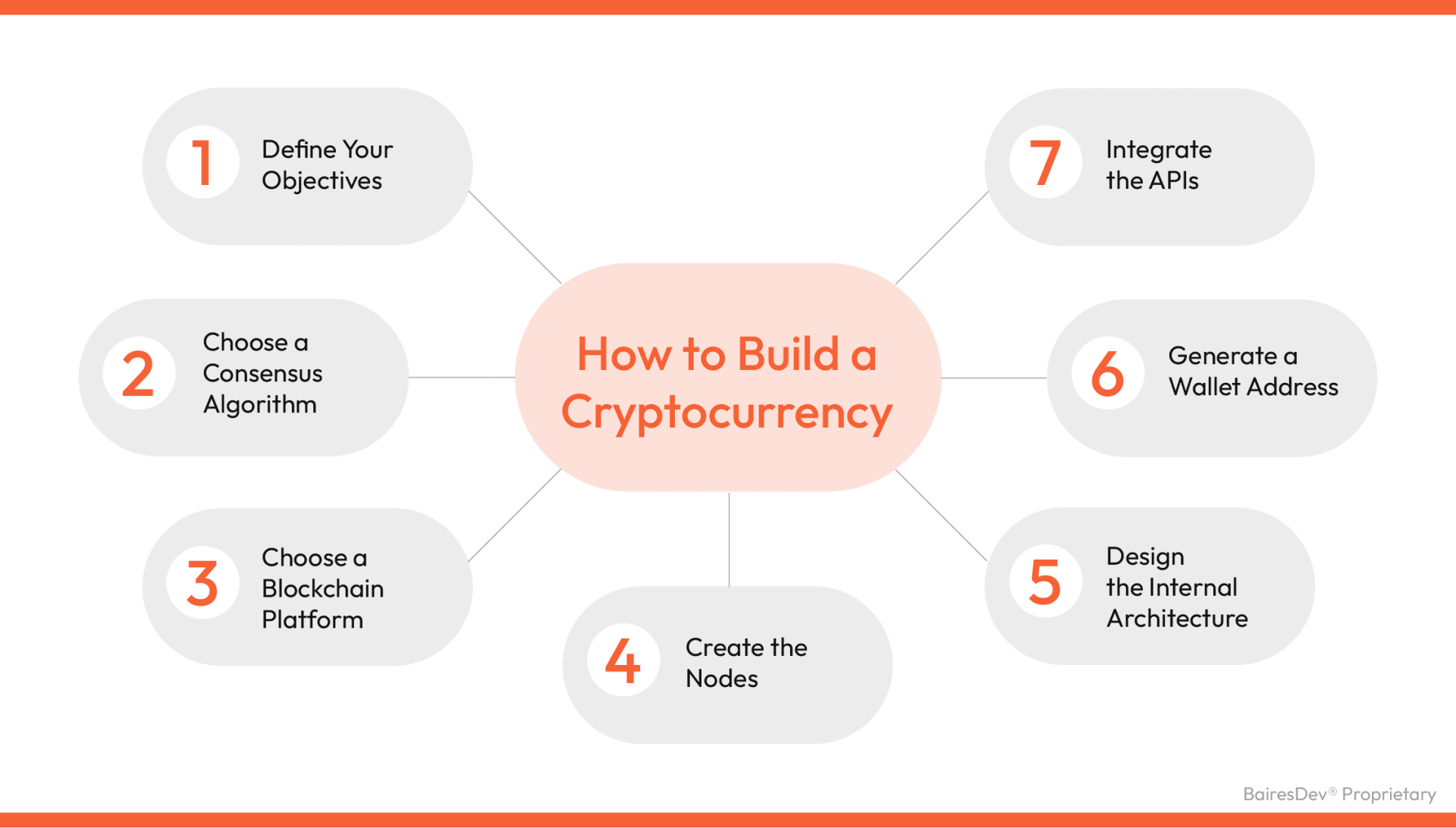
Before writing a single line of code, a developer must decide on the underlying infrastructure. This decision dictates the scalability, security, and interoperability of the asset. In the tech niche, this is referred to as choosing your layer.
Choosing the Right Infrastructure: Layer 1 or Layer 2?
Building a “coin” usually implies creating a Layer 1 (L1) blockchain. This involves developing a proprietary consensus mechanism and a network of nodes to validate transactions. Popular examples include Bitcoin and Cardano. Developing an L1 is a massive undertaking that requires building the peer-to-peer (P2P) networking layer, the storage engine, and the virtual machine from scratch.
Alternatively, many developers opt to create a “token” on an existing Layer 1 or Layer 2 (L2) network. By leveraging platforms like Ethereum, Binance Smart Chain, or Polygon, you inherit the security and decentralization of the host network. This approach allows developers to focus on the logic of the asset (the smart contract) rather than the maintenance of the hardware nodes. From a software engineering perspective, building on an established L2 is often the most efficient route for rapid deployment and high throughput.
The Role of Consensus Mechanisms (PoW vs. PoS)
If you choose to build an independent blockchain, the consensus mechanism is your most vital technical choice. Proof of Work (PoW), utilized by Bitcoin, relies on computational power and hardware (ASICs) to secure the network. While highly secure, it is energy-intensive and difficult to scale.
Modern tech stacks favor Proof of Stake (PoS) or its variants, such as Delegated Proof of Stake (DPoS) or Proof of History (PoH). In a PoS system, validators are chosen based on the number of coins they hold and are willing to “stake” as collateral. This significantly reduces latency and increases transactions per second (TPS). Understanding the algorithmic differences between these mechanisms is essential for any developer aiming to optimize network performance and Byzantine Fault Tolerance (BFT).
The Development Process: Coding and Smart Contracts
Once the infrastructure is decided, the development phase begins. This is where the specific rules of the cryptocurrency—such as total supply, minting logic, and transferability—are programmed.
Selecting a Programming Language (Solidity, Rust, or Go)
The choice of programming language depends heavily on the chosen blockchain. For the Ethereum Virtual Machine (EVM), Solidity is the industry standard. It is an object-oriented, high-level language specifically designed for developing smart contracts. Its syntax is influenced by C++, Python, and JavaScript, making it accessible to many web developers.
For high-performance networks like Solana or Polkadot, Rust is the preferred language. Rust offers memory safety and high concurrency, which are critical for processing thousands of transactions simultaneously. Meanwhile, many modular blockchain frameworks, like the Cosmos SDK, utilize Go (Golang) for its efficiency in building distributed systems. Selecting the right stack is a balance between developer familiarity and the technical requirements of the intended application.
Drafting and Auditing Your Smart Contract
A smart contract is a self-executing contract with the terms of the agreement directly written into code. When creating a crypto asset, the smart contract defines how tokens move between addresses. A typical contract includes functions for transfer, balanceOf, and approve.
However, the “code is law” philosophy of blockchain means that bugs are permanent once deployed. This necessitates a rigorous testing phase using frameworks like Hardhat or Foundry. Developers must conduct unit tests, integration tests, and formal verification to ensure the logic holds up under edge cases. A technical audit by an external security firm is non-negotiable; they use automated tools and manual code review to identify vulnerabilities such as logic errors or economic attack vectors.
Deploying Your Asset to the Network
Deployment is the transition from a local development environment to a live, distributed network. This phase requires a precise orchestration of software tools and network interactions.
Setting Up a Development Environment
Before going live on the “Mainnet,” developers use a “Testnet”—a sandbox environment that mimics the live blockchain but uses worthless testing coins. To interact with the blockchain, developers use Integrated Development Environments (IDEs) like Remix or VS Code extensions.
You will also need to configure a provider (like Infura or Alchemy) to connect your local machine to the blockchain nodes. This setup allows you to compile your code into bytecode, which the blockchain’s virtual machine can interpret. During this phase, developers often use “oracles” if the coin needs to interact with data from the outside world, ensuring the technical architecture is fully integrated with the broader digital ecosystem.
Mainnet Deployment and Gas Fees
Moving to the Mainnet requires “Gas”—the computational fee paid to the network’s validators to process your deployment transaction. The cost of gas fluctuates based on network congestion. From a technical standpoint, optimizing your code to be “gas-efficient” is a hallmark of a skilled blockchain developer.
Optimization techniques include minimizing state changes, using efficient data types (like uint256 instead of string where possible), and batching operations. Once the deployment transaction is confirmed by the network, your coin officially exists on the ledger, and its contract address becomes the unique identifier for all future interactions.
Technical Security and Scalability
The final and most critical stage of creating a crypto coin is ensuring its long-term viability through robust security measures and scalability planning.
Protecting Against Common Vulnerabilities
The history of decentralized finance (DeFi) is riddled with exploits. Developers must be intimately familiar with common attack vectors. One such vulnerability is the “Reentrancy Attack,” where an external contract calls back into the original contract before the first execution is finished, potentially draining funds. Implementing “checks-effects-interactions” patterns or using OpenZeppelin’s ReentrancyGuard can mitigate this.
Other security concerns include integer overflows (though modern Solidity versions handle this automatically) and front-running, where bots detect your transaction in the “mempool” and pay higher gas fees to execute their transaction first. Implementing “Commit-Reveal” schemes or using private transaction relays can help protect the technical integrity of your coin’s ecosystem.
Implementing Interoperability Standards (ERC-20, BEP-20)
To ensure your coin can be recognized by wallets (like MetaMask), decentralized exchanges (like Uniswap), and other dApps, it must adhere to specific technical standards. The most common is ERC-20 for Ethereum-based assets. This standard defines a common list of rules that a token must follow, including how it is transferred and how data can be accessed.
As the tech landscape shifts toward a multi-chain future, developers are increasingly looking at “Cross-Chain” interoperability. This involves using “bridges” or protocols like LayerZero to allow your coin to move between different blockchains. Designing your coin with these standards in mind from the beginning ensures that it is not siloed within a single ecosystem, but can instead function as a modular piece of the broader decentralized web.
![]()
Conclusion
Creating a crypto coin is a rigorous technical challenge that spans software engineering, cryptography, and network architecture. It begins with selecting the appropriate infrastructure—whether an independent Layer 1 or a smart-contract-based token—and continues through a disciplined development process involving Solidity or Rust. Deployment requires a deep understanding of network mechanics and gas optimization, while long-term success is predicated on rigorous security audits and adherence to interoperability standards. In the rapidly evolving world of technology, the ability to build and secure digital assets is a powerful skill, but it requires a commitment to technical excellence and a proactive approach to security.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.