In the realm of telecommunications and digital security, the term “restricted call” might conjure images of clandestine operations or top-secret communications. While the reality is far less dramatic, understanding what a restricted call entails is crucial for both individual privacy and effective network management. A restricted call, at its core, refers to a phone call where the caller’s identification is deliberately withheld from the recipient’s device. This deliberate obscuring of the caller ID can stem from a variety of sources, ranging from user-initiated privacy settings to network-level configurations and even specific service provider limitations. Navigating this feature requires an understanding of its technical underpinnings, its implications for security and privacy, and the practical ways users and organizations interact with it.
The Technical Foundation of Caller ID Blocking
The ability to restrict calls is fundamentally built upon the technical protocols that govern telephone networks. Historically, the transmission of caller information was not a standard feature. As technology evolved, particularly with the advent of digital switching and the integration of services like Caller ID, the capability to transmit subscriber data alongside a call became possible. However, this also paved the way for methods to circumvent or disable this transmission.
Signaling System No. 7 (SS7) and Caller ID Transmission
At the heart of modern telephone network infrastructure lies the Signaling System No. 7 (SS7). This suite of communication protocols is responsible for setting up and tearing down phone calls, handling billing information, and, critically for our discussion, transmitting caller information. When you make a call, SS7 protocols facilitate the exchange of data between the originating and terminating network switches. This data includes the dialed number and, if not blocked, the calling number and associated name (if subscribed to a service like CNAM – Caller Name).
The Mechanism of Restriction
Restricting a call involves manipulating the data packet sent via SS7. Instead of transmitting the originating subscriber’s telephone number, a specific code or flag is inserted into the signaling message. This code essentially tells the recipient’s network that the caller ID information is either “unavailable” or “restricted.” The exact code can vary depending on the telecommunication carrier and the type of network (e.g., landline, mobile). On mobile networks, this is often achieved through network-specific commands or service settings managed by the carrier. For instance, a user might access a setting within their phone’s call settings or dial a specific code before making a call to trigger this restriction.
Per-Call vs. Permanent Blocking
It’s important to distinguish between two primary methods of call restriction: per-call blocking and permanent blocking.
-
Per-Call Blocking: This is the most common method for individual users. By dialing a specific prefix before the phone number, the caller can ensure that their number is withheld for that single outgoing call. The universally recognized prefix for per-call blocking in North America is *67. When a user dials *67 followed by a 10-digit number, the originating carrier instructs the SS7 network to suppress the caller ID for that specific call. Other regions may have different prefixes. This provides a temporary solution for privacy on a case-by-case basis.
-
Permanent Blocking: This option, often referred to as “Caller ID Blocking” or “PermaBlock,” is a service that can be subscribed to through a telephone company. Once activated, all outgoing calls from that line will have their caller ID withheld by default, unless the user explicitly chooses to display their number (often by dialing a different prefix, like *82 in North America). This is a more persistent approach to privacy, suitable for individuals who consistently wish to remain anonymous or for businesses that manage their outbound caller ID for various strategic reasons. The activation and management of permanent blocking are typically handled through the subscriber’s account with their service provider.
Why Restrict a Call? Motivations and Use Cases
The decision to restrict a call is rarely arbitrary. It stems from a desire to control information, enhance security, or achieve specific communication objectives. These motivations can span personal privacy concerns, professional protocols, and even legitimate security measures.
Personal Privacy and Avoiding Unwanted Contact
For many individuals, restricting calls is a straightforward way to protect their personal privacy. This is particularly relevant in situations where someone might wish to make a call without revealing their phone number for various reasons, such as:
- Contacting unfamiliar individuals: When reaching out to someone for the first time, perhaps for a social engagement, a classified ad response, or a service inquiry, withholding one’s number can prevent unsolicited follow-up calls or the sharing of personal contact information with unknown parties.
- Avoiding telemarketers and spam: While many services now offer robust spam blocking, some persistent telemarketers may still attempt to reach individuals. Restricting one’s own number doesn’t block incoming calls, but it can prevent one’s own number from being added to unsolicited outbound call lists originating from the recipient’s side if they were to return a call.
- Protecting personal safety: In sensitive situations, such as dealing with stalkers or abusive individuals, withholding a phone number can be a crucial step in maintaining a degree of separation and personal safety, preventing the other party from tracing or identifying the caller.
Professional and Business Applications
Beyond personal use, restricted calls play a significant role in professional contexts, often serving strategic and operational purposes.
- Executive and confidential communications: High-level executives or individuals involved in sensitive negotiations might use restricted calls to maintain a degree of anonymity during initial contact or when reaching out to external parties where revealing their direct line might lead to unwanted solicitations or compromise strategic positioning.
- Sales and customer service outreach: While often businesses will display their company number or an identifiable outbound line, there are scenarios where sales representatives or customer service personnel might be instructed to make outbound calls with restricted caller ID. This could be to avoid being directly contacted by a customer outside of official channels or to prevent their personal numbers from being associated with specific customer interactions. However, best practices often encourage identifiable outbound calling to foster trust.
- Law enforcement and investigative purposes: In certain controlled environments, law enforcement agencies or private investigators might utilize restricted calls as part of their operations, particularly when initiating contact with individuals without revealing their investigative affiliation prematurely. This is done under strict protocols and legal frameworks.
Technical and Operational Considerations

In a more technical sense, restricted calls can also be a result of how phone systems are configured or managed.
- Private Branch Exchange (PBX) configurations: Larger organizations often use Private Branch Exchange (PBX) systems to manage their internal and external phone calls. These systems can be configured to present a specific outbound caller ID for all calls originating from the organization, or in some cases, to mask individual extensions and present a generic company number. In certain setups, the system might be configured to default to a restricted display for specific types of outbound calls.
- VoIP and Softphone limitations: With the rise of Voice over Internet Protocol (VoIP) and softphone applications, the management of caller ID can be more complex. While these platforms offer flexibility, misconfigurations or specific service provider settings can sometimes result in calls appearing as restricted. Ensuring correct configuration and understanding the service provider’s policies are crucial.
Implications and Challenges of Restricted Calls
While the ability to restrict calls offers benefits in privacy and operational flexibility, it also presents a unique set of implications and challenges, particularly concerning security and the recipient’s experience.
Security Risks and Scamming
One of the most significant downsides of restricted calls is their potential to be exploited by malicious actors. Scammers and spammers often leverage caller ID spoofing and call blocking to disguise their identity and appear more legitimate, or to simply avoid being traced.
- Vishing (Voice Phishing): Scammers frequently use restricted or spoofed numbers to conduct vishing attacks. By making a call appear as if it’s coming from a legitimate source (like a bank, a government agency, or a well-known company), they can trick unsuspecting individuals into divulging sensitive personal information, such as bank account details, social security numbers, or passwords. The lack of verifiable caller ID makes it harder for recipients to immediately discern a fraudulent call from a genuine one.
- Robocalls and Harassment: Unwanted robocalls, often from telemarketers or scammers, can also be made to appear as restricted. This makes it more difficult to report these numbers to authorities or to block them effectively through standard caller ID blocking features on the recipient’s device. Persistent harassment through restricted calls can be particularly distressing.
- Difficulty in Identification: For businesses and individuals receiving calls, a restricted number presents an immediate hurdle. They are forced to decide whether to answer an unknown, unidentifiable call, potentially exposing themselves to unwanted solicitations or scams, or to let it go to voicemail, which might mean missing an important call from a legitimate source who was simply trying to be discreet.
Impact on Recipient Trust and Communication Flow
The consistent appearance of restricted calls can erode trust and disrupt normal communication patterns.
- Hesitation to Answer: Many people have adopted a policy of not answering calls from unknown or restricted numbers, fearing scams or unwanted solicitations. This can lead to missed opportunities, such as potential job offers, important personal messages, or legitimate service inquiries.
- Challenges for Businesses: For businesses that rely on customer interaction, an inability to reliably identify incoming callers can be problematic. If a customer calls from a restricted number, a business might struggle to retrieve their account information efficiently or to personalize the interaction. Similarly, if a business’s outbound calls are consistently restricted, it can lead to lower answer rates and a perception of being less professional or transparent.
- The “Blocked” Perception: While intending to protect privacy, a consistently restricted caller ID can sometimes be perceived negatively by recipients. It might imply that the caller has something to hide, or is being deliberately evasive, which can create a less than ideal first impression.
Regulatory and Technological Countermeasures
In response to the challenges posed by restricted and spoofed calls, regulatory bodies and technology providers are continually developing countermeasures.
- STIR/SHAKEN Framework: In the United States and Canada, the STIR/SHAKEN (Secure Telephone Identity Revisited/Signature-based Handling of Asserted Information using Tokens) framework is a significant effort to combat caller ID spoofing. This technology allows voice service providers to digitally sign calls, verifying that the caller ID displayed is legitimate and authorized. While its implementation is ongoing and primarily targets spoofing, it has implications for how calls with withheld information are handled and verified.
- Carrier Policies and User Education: Telephone carriers play a role in educating their customers about the risks associated with restricted calls and often provide tools to help identify and block unwanted calls. They also implement internal policies to detect and mitigate fraudulent calling patterns.
- Third-Party Call Blocking Apps: A growing ecosystem of third-party applications offers advanced call screening and blocking capabilities. These apps often utilize vast databases of known spam numbers, crowd-sourced reporting, and AI-driven analysis to identify and flag suspicious calls, including those that might be restricted or spoofed.
Managing Your Own Restricted Calls and Receiving Them
Understanding how to control your own outgoing restricted calls and how to manage incoming ones from restricted numbers is essential for navigating modern communication.
Initiating a Restricted Call
As discussed earlier, the method for initiating a restricted call typically depends on your carrier and device.
- Per-Call Blocking: The most common method is to dial a specific prefix before the phone number. In North America, *67 is widely used for this purpose. For example, to call 555-123-4567 with your number restricted, you would dial *675551234567. It’s advisable to check with your specific mobile carrier or landline provider for the correct prefix in your region, as it can vary.
- Permanent Caller ID Blocking: If you wish for all your outgoing calls to be restricted by default, you will need to contact your telephone service provider to enable this feature on your line. There might be a small monthly fee associated with this service. Once enabled, you can usually override permanent blocking for a single call by dialing a specific prefix (e.g., *82 in North America) before the phone number, forcing your number to be displayed for that specific call.
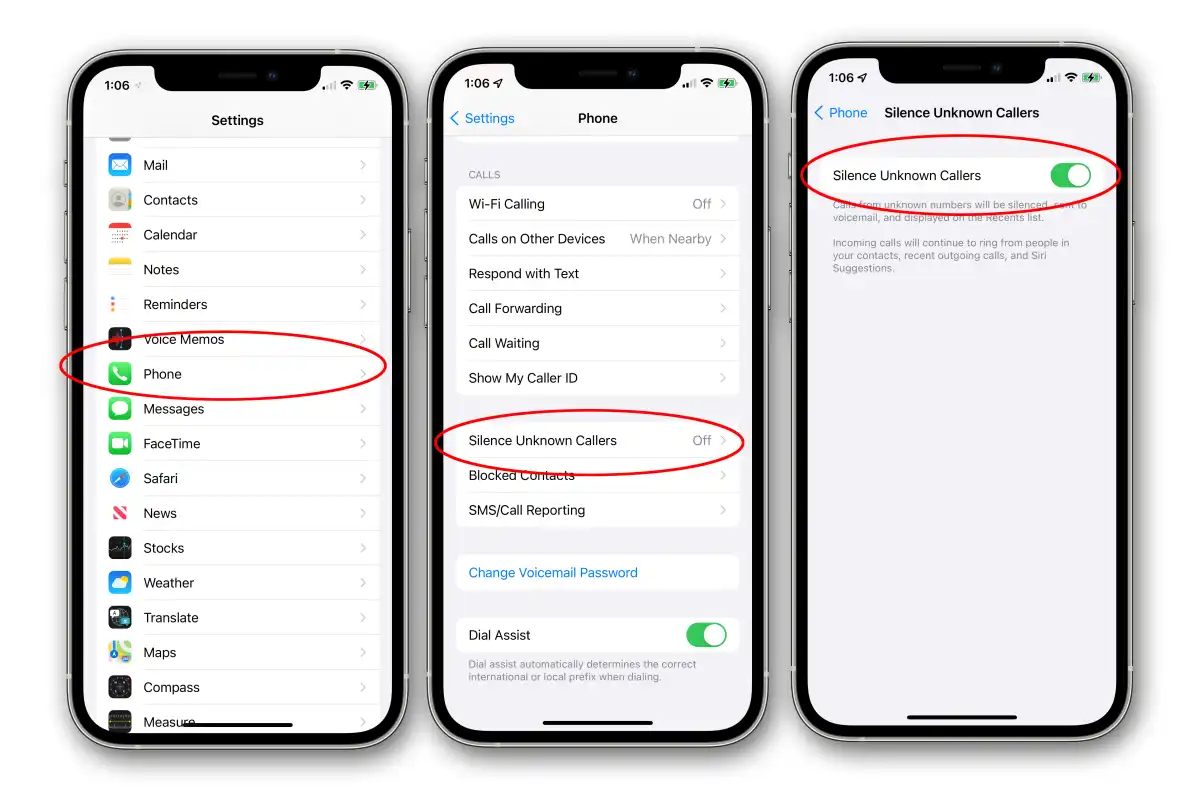
- Smartphone Settings: Many modern smartphones offer a setting within the phone or call settings menu to control Caller ID display. You can often choose to “Show my caller ID,” “Hide my caller ID,” or “Network default.” Selecting “Hide my caller ID” usually activates permanent blocking, while the per-call prefix is a network-level override.

Receiving and Managing Incoming Restricted Calls
When faced with an incoming call from a restricted number, you have several options and considerations.
- The Decision to Answer: Ultimately, the decision to answer a restricted call is personal. Weigh the potential benefits against the risks. If you are expecting a call from someone who might have a legitimate reason to restrict their number (e.g., a doctor’s office, a sensitive business contact), you might choose to answer. If you have no such expectations, it is generally safer to let it go to voicemail.
- Voicemail as a Filter: Allowing the call to go to voicemail can serve as an effective filter. If the caller has a legitimate reason for contacting you, they will likely leave a message. This allows you to assess the legitimacy of the call before deciding whether to call back. If it’s a scam or unwanted solicitation, you’ll know not to engage.
- Blocking Features: While you cannot directly block “restricted” as a caller ID because it’s not a specific number, you can often use your phone’s features to block numbers that you have identified. If you choose to call back a restricted number and it rings your voicemail, or if you recognize the caller after they leave a message, you can then save that number (if they eventually reveal it) and block it. Many call-blocking apps also offer options to block calls that are marked as “unknown” or “private,” which can sometimes encompass restricted calls.
- Utilizing Call Blocking Apps: As mentioned, third-party call blocking applications can be highly effective. These apps can be configured to automatically reject calls from numbers that are not in your contact list, or to flag calls from sources known for spam or telemarketing. Some advanced apps may even have heuristics to identify patterns associated with restricted calling tactics.
In conclusion, a restricted call is a communication where the caller’s identity is intentionally concealed from the recipient. While this feature can serve legitimate purposes for personal privacy and specific professional scenarios, its potential for misuse by scammers and the challenges it presents for clear communication necessitate a cautious and informed approach. By understanding the technical underpinnings, the motivations behind restricting calls, and the practical strategies for managing both outgoing and incoming restricted communications, individuals and organizations can better navigate the complexities of modern telephony while safeguarding their privacy and security.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.