In the realm of technology, a “near miss” isn’t just a casual descriptor for something that almost happened; it’s a critical concept, a signal, and a learning opportunity. It signifies an event or a situation that had the potential to cause significant harm, damage, or failure, but ultimately did not result in a negative outcome. In the fast-paced and complex world of technology, understanding, identifying, and analyzing near misses is paramount to fostering a culture of safety, security, and continuous improvement.
The implications of near misses extend across the entire technological landscape, from the intricate algorithms powering artificial intelligence to the robust infrastructure supporting global communication networks, and the user interfaces of everyday applications. Ignoring these close calls is akin to ignoring warning lights on a dashboard; eventually, a serious breakdown is inevitable. Conversely, a proactive approach to near miss analysis can prevent future incidents, enhance system resilience, and drive innovation.
This exploration delves into the multifaceted nature of near misses within the technology sector. We will dissect what constitutes a near miss in this domain, explore the various types and manifestations it can take, examine the crucial benefits of meticulously analyzing these occurrences, and outline effective strategies for identifying and mitigating them to build more secure, reliable, and robust technological systems.
The Digital Landscape of Near Misses
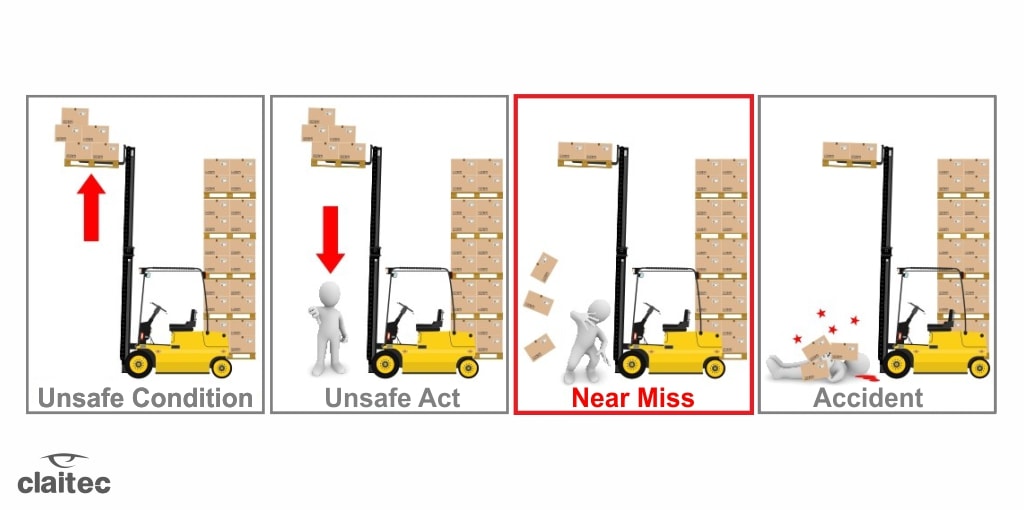
In the technological context, a near miss is an event that, if slightly different, could have led to a failure, a security breach, data loss, significant downtime, or even harm to users. These are the moments where systems performed inadequately, security protocols were almost bypassed, or user errors nearly caused catastrophic consequences, but some mitigating factor or sheer luck prevented the worst from happening.
Near Misses in Software Development and Deployment
Software development is a breeding ground for potential near misses. These can range from subtle bugs that were almost deployed to production environments, to near-misses in code reviews where critical vulnerabilities were identified just in time.
Code Vulnerabilities and Security Flaws
Imagine a scenario where a developer unknowingly introduces a critical SQL injection vulnerability into a web application. During a rigorous code review or an automated security scan, this flaw is discovered and fixed before it ever reaches a live server. The potential for a malicious actor to exploit this vulnerability and compromise user data was very real, making its discovery a classic near miss. Similarly, a buffer overflow vulnerability that was almost exploited by a sophisticated attacker but detected through anomaly detection systems prior to significant impact also falls into this category.
Infrastructure and Deployment Failures
Near misses also occur in the deployment and operational phases of software. A server configuration error that would have caused widespread service disruption but was caught by a pre-deployment staging environment check is a prime example. Another instance might be a flawed rollout of an update that, due to a last-minute rollback triggered by early monitoring alerts, prevented a complete system outage. These events highlight the importance of robust testing, staging environments, and real-time monitoring.
Near Misses in Cybersecurity
The cybersecurity domain is inherently defined by the constant battle against threats, and near misses are frequent occurrences. These are the times when an attack was launched, a system was targeted, but the defense mechanisms held, or the attack was misdirected, preventing a breach.
Almost Breached Systems
A sophisticated phishing campaign targeting an organization’s employees might see several individuals almost click on malicious links, but robust email filtering systems or employee training prevent the actual infection. This is a near miss; the intent and execution of the attack were present, but the desired outcome for the attacker was not achieved. Another example is a denial-of-service (DoS) attack that almost overwhelms a critical service but is successfully mitigated by network traffic management and load balancing strategies.
Uncovered Exploits and Vulnerabilities
Security researchers often discover vulnerabilities in widely used software or hardware. The process of discovering and responsibly disclosing these vulnerabilities is a continuous near-miss operation for the broader tech ecosystem. A zero-day exploit that is discovered by a security firm before it can be widely weaponized by malicious actors is a significant near miss for millions of potential victims. This highlights the vital role of proactive security research and ethical hacking.
Near Misses in User Experience and Human-Computer Interaction
While often associated with tangible failures, near misses also manifest in how users interact with technology, impacting usability, accessibility, and overall satisfaction.
Usability Issues That Almost Lead to Frustration
A poorly designed user interface element that almost causes users to abandon a task or make a critical mistake but is recognized and improved during user testing is a near miss. For instance, a confusing checkout process that almost leads to a high cart abandonment rate but is redesigned based on early user feedback is a testament to this.
Accessibility Blunders That Were (Almost) Missed
In the pursuit of inclusive design, near misses can occur when accessibility features are almost overlooked or implemented incorrectly. A website that was almost launched without proper alt text for images or keyboard navigation support, but where these oversights were caught during an accessibility audit, represents a near miss in ensuring digital inclusivity.
The Power of Analyzing Technology Near Misses
The true value of a near miss lies not in the fact that disaster was averted, but in the insights and lessons learned from the experience. A systematic approach to analyzing these events transforms them from fortunate escapes into catalysts for significant improvement.
Preventing Future Incidents and Catastrophes
The most immediate benefit of analyzing near misses is the ability to prevent similar events from occurring in the future. By dissecting the chain of events that led to the near miss, organizations can identify the root causes and implement corrective actions.
Identifying Weaknesses in Systems and Processes
A near miss often exposes underlying weaknesses in technological systems, operational procedures, or human processes. For example, a near miss in a data backup process might reveal a flawed script or inadequate testing of the backup recovery procedure. Analyzing this allows for the correction of the script or the implementation of more rigorous testing, thus strengthening the overall data resilience.
Understanding Threat Landscapes and Attack Vectors
In cybersecurity, near misses provide invaluable intelligence about evolving threats. By studying an attempted but failed cyberattack, organizations can gain a deeper understanding of the tactics, techniques, and procedures (TTPs) employed by adversaries. This knowledge can be used to proactively update security defenses, develop better threat detection models, and train security personnel more effectively.

Enhancing System Reliability and Resilience
Beyond preventing specific incidents, the analysis of near misses contributes to building more inherently reliable and resilient technological systems.
Improving Fault Tolerance and Error Handling
When a system behaves unexpectedly but doesn’t fail completely, it presents an opportunity to examine its fault tolerance and error handling mechanisms. A near miss in a distributed system might reveal a scenario where a single node failure almost caused cascading failures but was contained by designed redundancy. This analysis can lead to optimizations that enhance the system’s ability to withstand failures gracefully.
Optimizing Performance and Stability
Near misses can also highlight performance bottlenecks or stability issues that, if left unaddressed, could eventually lead to more severe problems. For instance, a web application that almost experienced a performance collapse under moderate load but recovered due to adaptive scaling mechanisms might indicate that the scaling triggers need fine-tuning or that underlying code optimizations are required to prevent future performance degradation.
Fostering a Culture of Continuous Improvement
The act of actively seeking out and analyzing near misses cultivates a proactive and learning-oriented culture within technology teams and organizations.
Promoting Transparency and Open Communication
When near misses are treated as learning opportunities rather than failures to be hidden, it encourages transparency and open communication. Team members feel more comfortable reporting close calls without fear of reprisal, leading to a richer dataset for analysis and a more collaborative approach to problem-solving.
Driving Innovation and Best Practices
By consistently learning from near misses, organizations can drive innovation and refine their best practices. The insights gained can inform the development of new technologies, the implementation of more effective security protocols, and the establishment of industry-leading standards for software development and system operation.
Strategies for Identifying and Mitigating Technology Near Misses
Effectively harnessing the power of near misses requires a deliberate and systematic approach to their identification and mitigation. This involves establishing clear processes, leveraging appropriate tools, and cultivating the right mindset within teams.
Establishing Robust Reporting and Documentation Mechanisms
The foundation of near miss analysis is the ability to capture these events. Without a clear and accessible way to report them, near misses will remain undocumented and their lessons unlearned.
Creating Accessible Reporting Channels
Organizations must provide clear and easy-to-use channels for employees to report near misses. This could include dedicated online forms, incident reporting software, or designated individuals to whom reports can be made. It’s crucial to emphasize that reporting a near miss is a positive contribution, not an admission of fault.
Standardizing Documentation and Incident Analysis
Once reported, near misses need to be documented consistently. This documentation should include details such as the date and time of the incident, the systems or processes involved, the potential consequences, the mitigating factors, and any initial observations. A standardized incident analysis framework can then be applied to systematically investigate the root causes.
Leveraging Technology for Detection and Analysis
Technology itself can be a powerful ally in identifying and understanding near misses, particularly in complex digital environments.
Implementing Proactive Monitoring and Alerting Systems
Advanced monitoring tools that track system performance, network traffic, security logs, and user behavior can detect anomalies and potential issues in real-time. Configuring these systems with appropriate thresholds and alert mechanisms can flag events that might otherwise go unnoticed until they escalate into full-blown incidents.
Utilizing AI and Machine Learning for Anomaly Detection
Artificial intelligence and machine learning are increasingly being used to identify subtle patterns and deviations from normal behavior that might indicate a near miss. These technologies can analyze vast datasets to detect unusual activity that human analysts might miss, thereby enhancing the proactive identification of potential problems.
Cultivating a Proactive and Learning-Oriented Culture
Ultimately, the most effective strategy for dealing with near misses is to foster an organizational culture that values learning, transparency, and continuous improvement.
Encouraging a Blameless Post-Mortem Approach
When analyzing near misses, it’s crucial to adopt a “blameless post-mortem” approach. The focus should be on understanding what happened and why it happened, rather than assigning blame to individuals. This encourages honesty and open discussion, which are essential for uncovering the true root causes.

Integrating Near Miss Lessons into Training and Development
The insights gained from near miss analysis should be actively integrated into employee training and development programs. This ensures that lessons learned are disseminated throughout the organization and that future employees are equipped with the knowledge to prevent similar occurrences. Regular “lessons learned” sessions or updates can reinforce these key takeaways.
In conclusion, near misses in technology are not simply lucky escapes; they are invaluable indicators of potential vulnerabilities and opportunities for improvement. By understanding their nature, recognizing their diverse manifestations, appreciating the profound benefits of their analysis, and diligently implementing strategic identification and mitigation approaches, the technology sector can move towards building more secure, reliable, and resilient systems that benefit us all. Embracing a proactive stance towards near misses is not just good practice; it is a fundamental requirement for navigating the ever-evolving technological landscape.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.