The genesis of Bitcoin is one of the most intriguing mysteries of the 21st century, deeply intertwined with the very nature of its underlying technology. While Bitcoin itself is now a globally recognized digital asset, the fundamental question of “who created its algorithm” leads us down a rabbit hole of cryptography, pseudonymity, and a revolutionary approach to decentralized digital systems. This question isn’t merely about identifying a person; it’s about understanding the philosophical and technical underpinnings that allowed such a groundbreaking invention to emerge from the shadows, forever altering our perception of digital trust and secure data exchange. The creator, known only by the pseudonym Satoshi Nakamoto, not only designed a novel digital currency but also architected a complex, robust, and self-sustaining technological framework that continues to operate without central authority.

The Enigmatic Genesis and Satoshi Nakamoto
The story of Bitcoin begins not with a corporate launch or a public figure, but with a whitepaper published on October 31, 2008, titled “Bitcoin: A Peer-to-Peer Electronic Cash System.” This document, authored by “Satoshi Nakamoto,” laid out the design for a new form of digital money that promised to solve the long-standing “double-spending” problem inherent in digital transactions, without relying on a trusted third party. The publication of this paper marked a pivotal moment, introducing the world to the concepts of blockchain technology, cryptographic proof, and decentralized consensus.
The Whitepaper and Pseudonymity
The Bitcoin whitepaper wasn’t just a proposal; it was a blueprint. It detailed a meticulously designed system that combined several existing cryptographic techniques with a novel chain of proof-of-work blocks, forming the foundation of what we now call a blockchain. What was equally revolutionary was the decision of its author, Satoshi Nakamoto, to remain anonymous. This pseudonymity was not merely a quirky choice; it was integral to Bitcoin’s ethos. By not attaching a real-world identity to the creator, Satoshi ensured that Bitcoin could not be easily co-opted, influenced, or controlled by any single entity, be it a government, a corporation, or even the creator themselves. This act of disassociation from the project’s figurehead immediately decentralized the leadership, pushing the nascent technology towards a truly community-driven development path. The whitepaper itself served as the sole manifesto, guiding principle, and technical specification, allowing the technology to speak for itself.
The Cryptographic Foundations
Satoshi Nakamoto’s genius lay not in inventing entirely new cryptographic primitives, but in ingeniously combining existing, well-understood cryptographic techniques to create a novel system. The Bitcoin algorithm leverages:
- Hash Functions (SHA-256): Used extensively for various purposes, including creating unique digital fingerprints of data, securing blocks in the blockchain, and within the proof-of-work mechanism. Every block’s header is hashed to meet a specific difficulty target.
- Public-key Cryptography: Essential for securing transactions. Each participant has a pair of keys: a public key (derived from a Bitcoin address) and a private key. Transactions are signed with the private key, proving ownership without revealing the key itself.
- Merkle Trees: These are tree data structures where every leaf node is labeled with the cryptographic hash of a data block, and every non-leaf node is labeled with the cryptographic hash of its child nodes. They allow for efficient and secure verification of transactions within a block, ensuring that even a large number of transactions can be summarized by a single root hash.
- Digital Signatures: Used to authorize transactions. When a user wants to send Bitcoin, they create a transaction and sign it with their private key. This signature proves that the sender authorized the transaction and that the transaction has not been altered.
These elements, when woven together, formed a robust and tamper-proof ledger, the core innovation being the trustless verification system that allowed participants to agree on the state of the ledger without a central authority.
Deconstructing the Bitcoin Algorithm
At its heart, the Bitcoin algorithm is a set of rules and protocols that govern how the network operates, how transactions are validated, and how new units of Bitcoin are created. It’s a complex interplay of cryptographic functions, consensus mechanisms, and network communication protocols designed to maintain a consistent and secure ledger across thousands of decentralized nodes.
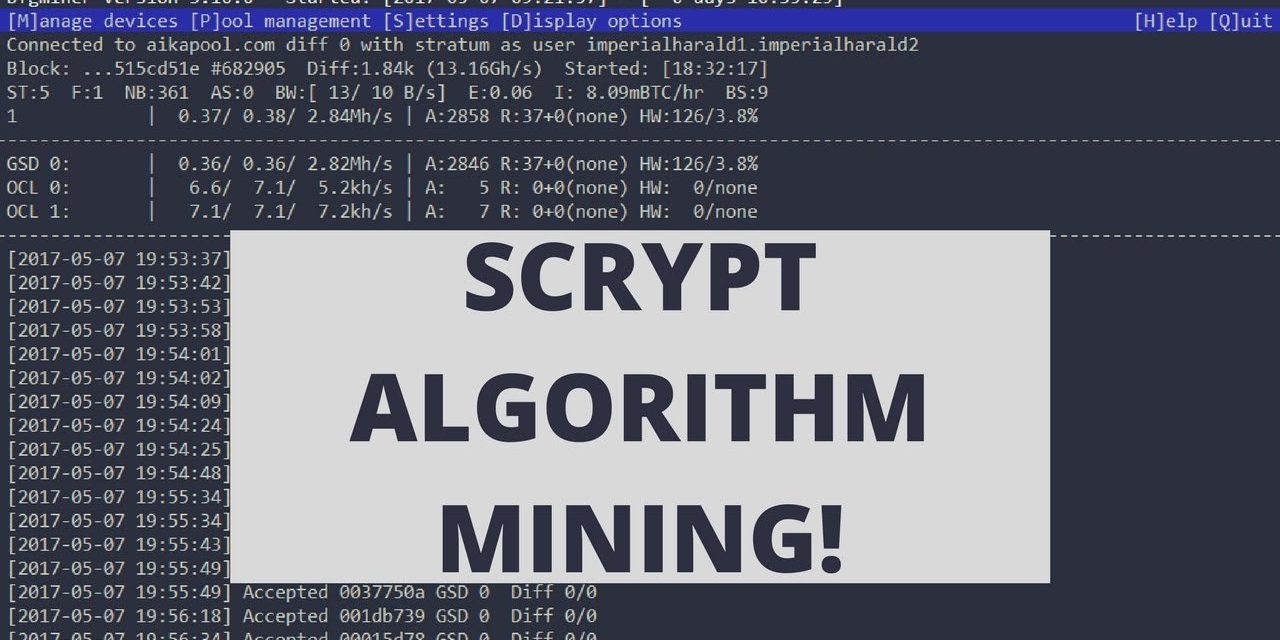
Proof-of-Work: The Core Mechanism
The most fundamental innovation within the Bitcoin algorithm is its use of a Proof-of-Work (PoW) consensus mechanism. This is what secures the network and prevents fraudulent transactions. Miners compete to solve a computationally intensive puzzle: finding a number (a “nonce”) that, when combined with the data in a block and hashed using SHA-256, produces a result that starts with a certain number of zeroes. This “difficulty target” is adjusted roughly every two weeks to ensure that, on average, a new block is found approximately every 10 minutes.
The process serves several critical functions:
- Securing the Blockchain: The immense computational effort required to find a valid hash makes it incredibly difficult and expensive for an attacker to alter past transactions. To rewrite history, an attacker would need to redo the PoW for the target block and all subsequent blocks faster than the rest of the network, which is practically impossible.
- Creating New Blocks: Successful miners get to add their block of validated transactions to the blockchain.
- Issuing New Bitcoin: As a reward for their computational effort, the miner who finds a valid hash receives a block reward, which includes newly minted Bitcoin and transaction fees. This is the only way new Bitcoin enters circulation.
The PoW mechanism is the engine of Bitcoin’s security and its decentralized issuance model, making it resistant to censorship and manipulation.
Hashing and Cryptographic Security
The SHA-256 (Secure Hash Algorithm 256-bit) function is ubiquitous within the Bitcoin algorithm. It’s a one-way cryptographic function, meaning it’s easy to compute the hash of a given input but practically impossible to reverse-engineer the input from the hash. Even a tiny change in the input data results in a completely different hash output, ensuring data integrity.
In Bitcoin, hashing is used for:
- Block Headers: Each block header contains critical information, including a hash of the previous block, a timestamp, the Merkle root of all transactions in the block, and the nonce. This hash links blocks together, forming the “chain.”
- Transaction IDs: Every transaction is assigned a unique transaction ID, which is essentially a double SHA-256 hash of the transaction data.
- Address Generation: Bitcoin addresses are derived from public keys using a series of cryptographic hashes and encoding, ensuring they are short and secure.
- Proof-of-Work: As mentioned, miners repeatedly hash block headers with different nonces until they find one that meets the network’s difficulty target.
This pervasive use of cryptographic hashing guarantees the immutability and integrity of the Bitcoin ledger.
The Blockchain Architecture
The “blockchain” itself is the distributed ledger, a chronological chain of blocks, each containing a list of validated transactions. Each block is cryptographically linked to the previous one via its hash, forming an unbroken chain extending all the way back to the very first “genesis block.” This architecture ensures:
- Immutability: Once a block is added to the blockchain, it is nearly impossible to alter, especially as more blocks are added on top of it, creating an ever-increasing amount of computational work that would need to be redone.
- Transparency: All transactions are publicly visible on the blockchain, though the identities of the participants remain pseudonymous (linked only to their Bitcoin addresses).
- Decentralization: Copies of the entire blockchain are maintained by thousands of nodes worldwide. There is no central server or authority controlling the ledger. If one node goes offline, the network continues to function seamlessly.
This interconnected, distributed, and cryptographically secured ledger is the technological backbone that gives Bitcoin its unparalleled resilience and security.
Tracing the Footprints: Attempts to Identify Satoshi
Despite intensive efforts by journalists, cryptographers, and enthusiasts, the true identity of Satoshi Nakamoto remains unknown. The creator ceased all public communication related to Bitcoin in mid-2010, effectively disappearing from the project they initiated. This enduring mystery has only added to Bitcoin’s mystique and reinforced its decentralized nature.

Linguistic Analysis and Coding Style
Early attempts to unmask Satoshi often focused on analyzing their communication patterns. Satoshi wrote extensively on forums, in emails, and, of course, in the whitepaper. Researchers have studied linguistic quirks, spelling preferences (e.g., using British English spellings like “colour” and “optimise”), and even timestamps of their posts. Some analyses suggested a potential origin in the UK or another Commonwealth country, or at least a familiarity with British English. Similarly, Satoshi’s coding style in the initial Bitcoin client source code has been scrutinized, but no definitive links to known programmers have emerged. These forensic analyses have been interesting academic exercises but have not yielded any conclusive evidence.
Early Collaborators and Speculations
Before disappearing, Satoshi Nakamoto corresponded with several prominent figures in the cypherpunk and cryptography communities, including Hal Finney, Nick Szabo, and Wei Dai (creators of “reusable proof-of-work” and “b-money” respectively, concepts that predated Bitcoin and likely influenced Satoshi). These individuals were among the first to understand the profound implications of Bitcoin and provided valuable feedback and contributions in its early days. While some have been speculated to be Satoshi, all have denied it, and no credible evidence has linked them directly to the pseudonym. The very act of collaborating with others while maintaining anonymity highlights Satoshi’s dedication to remaining a ghost in the machine.
The Craig Wright Controversy and Debates
Perhaps the most high-profile and contentious claim of being Satoshi Nakamoto has come from Australian computer scientist Craig Wright. Starting in 2015, Wright publicly claimed to be Satoshi, providing some cryptographic proofs and giving interviews. However, these proofs were widely debunked by the cryptographic community as either fabricated or insufficient. Wright’s claims have been met with widespread skepticism and scorn, particularly within the Bitcoin and cryptocurrency communities. While Wright continues to assert his identity as Satoshi, he has failed to provide verifiable, irrefutable cryptographic evidence (such as signing a message with the private key associated with the genesis block, or moving Bitcoin from Satoshi’s known early addresses) that would definitively prove his claim to the broader technical community. The controversy surrounding Wright underscores the difficulty, and perhaps the impossibility, of definitively unmasking Satoshi against their will.
The Impact of Pseudonymity on Decentralization
Satoshi’s decision to vanish remains one of the most critical aspects of Bitcoin’s technological design, beyond the code itself. It fundamentally shaped Bitcoin’s trajectory and reinforced its core tenets.
A Vision of Trustless Systems
The anonymous nature of Bitcoin’s creator perfectly aligns with the technology’s aim to build “trustless systems.” A trustless system doesn’t mean users don’t trust the technology; it means they don’t have to trust any single person, corporation, or government. Instead, trust is placed in the mathematics, the cryptography, and the open-source code that anyone can inspect. By removing themselves from the equation, Satoshi ensured that Bitcoin’s integrity stemmed from its protocol, not from the reputation of an individual. This technical design choice fostered an environment where the technology could evolve based on collective consensus and technical merit, rather than the directives of a single leader.
Ensuring Resistance to Centralized Control
If Satoshi Nakamoto had remained an identifiable public figure, Bitcoin would have faced immediate and immense pressure from governments, financial institutions, and special interest groups. The creator could have been coerced, silenced, or even bought out, compromising the project’s independence. By stepping away, Satoshi inoculated Bitcoin against such single points of failure. The lack of a central authority or a visible leader makes it incredibly difficult for external forces to shut down, regulate, or control the network. This resistance to centralized control is a direct consequence of the creator’s anonymity and is a core part of its technological resilience. It ensured that the network would truly be peer-to-peer, governed by its code and the consensus of its users and developers.
The Legacy of an Anonymous Creator
Satoshi’s legacy is not just the Bitcoin algorithm, but also the blueprint for a truly decentralized digital infrastructure. Their anonymity allowed the project to grow organically, attracting a global community of developers, miners, and users who collectively maintain and evolve the network. It demonstrated that a truly groundbreaking technology could be launched and sustained without traditional corporate structures or personal acclaim. The very fact that Bitcoin thrives today, without its creator’s presence, is a testament to the power of open-source collaboration and decentralized governance, a direct result of Satoshi’s original vision and profound understanding of cryptographic systems and human nature.
The Evolving Technology Beyond the Original Algorithm
While the core Bitcoin algorithm remains remarkably stable and secure, the technology built around it and its potential for scaling and broader application continues to evolve through community-driven development and innovation.
Forks and Protocol Upgrades
The open-source nature of Bitcoin means that anyone can propose changes or improvements to the protocol. Major changes, known as “forks,” can occur in two main forms:
- Soft Forks: Backward-compatible upgrades that tighten existing rules, allowing non-upgraded nodes to still validate transactions from upgraded nodes. Examples include Segregated Witness (SegWit), which optimized block space and fixed transaction malleability.
- Hard Forks: Non-backward-compatible changes that create a new set of rules. Nodes that don’t upgrade will follow the old rules, effectively splitting the blockchain. Bitcoin Cash, for instance, was a hard fork that increased the block size limit to allow for more transactions per block.
These processes demonstrate the decentralized governance model where changes are adopted through network consensus, reflecting the collective will of the community rather than a central directive.
Layer 2 Solutions: Scaling Bitcoin
The original Bitcoin algorithm, while robust, has inherent limitations in transaction throughput due to its 10-minute block time and 1MB block size limit. To address this, developers have focused on Layer 2 solutions that build on top of the main Bitcoin blockchain, rather than altering its fundamental protocol. The most prominent example is the Lightning Network.
The Lightning Network creates off-chain payment channels between users. Transactions within these channels happen instantly and with very low fees, without needing to be recorded on the main blockchain until the channel is closed. This significantly increases transaction capacity, making Bitcoin more viable for micro-payments and daily use, while still settling final balances securely on the main blockchain. Such innovations illustrate how the foundational algorithm can be extended and enhanced without compromising its core security principles.
Future of Bitcoin’s Underlying Tech
The future of Bitcoin’s technology continues to focus on improving efficiency, privacy, and smart contract capabilities, all while preserving the core tenets of decentralization and security. Developments like Taproot (a soft fork that improved privacy and allowed for more flexible smart contracts on Bitcoin) demonstrate the ongoing commitment to enhancing the original algorithm. Further advancements in cryptography, such as Schnorr signatures and potentially even quantum-resistant algorithms (though distant), could one day be integrated to bolster Bitcoin’s long-term security. The ongoing research and development by a global community of developers ensure that the technological legacy initiated by Satoshi Nakamoto will continue to adapt and thrive, remaining at the forefront of distributed ledger technology. The “who” behind the algorithm may be a mystery, but the “what” and the “how” are an open book of innovation.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.