The evolution of decentralized ledger technology has transformed the concept of digital value from a niche cryptographic experiment into a global financial standard. However, beneath the market fluctuations and speculative fervor lies a complex layer of software engineering and distributed systems architecture. Creating a cryptocurrency is not merely an exercise in financial theory; it is a rigorous technical undertaking that requires a deep understanding of consensus algorithms, network protocols, and cryptographic security.
This guide focuses on the technical roadmap required to build a cryptocurrency from the ground up, exploring the architectural choices, development frameworks, and security protocols necessary to launch a robust digital asset in today’s interconnected ecosystem.
Understanding the Architectural Foundations of Digital Assets
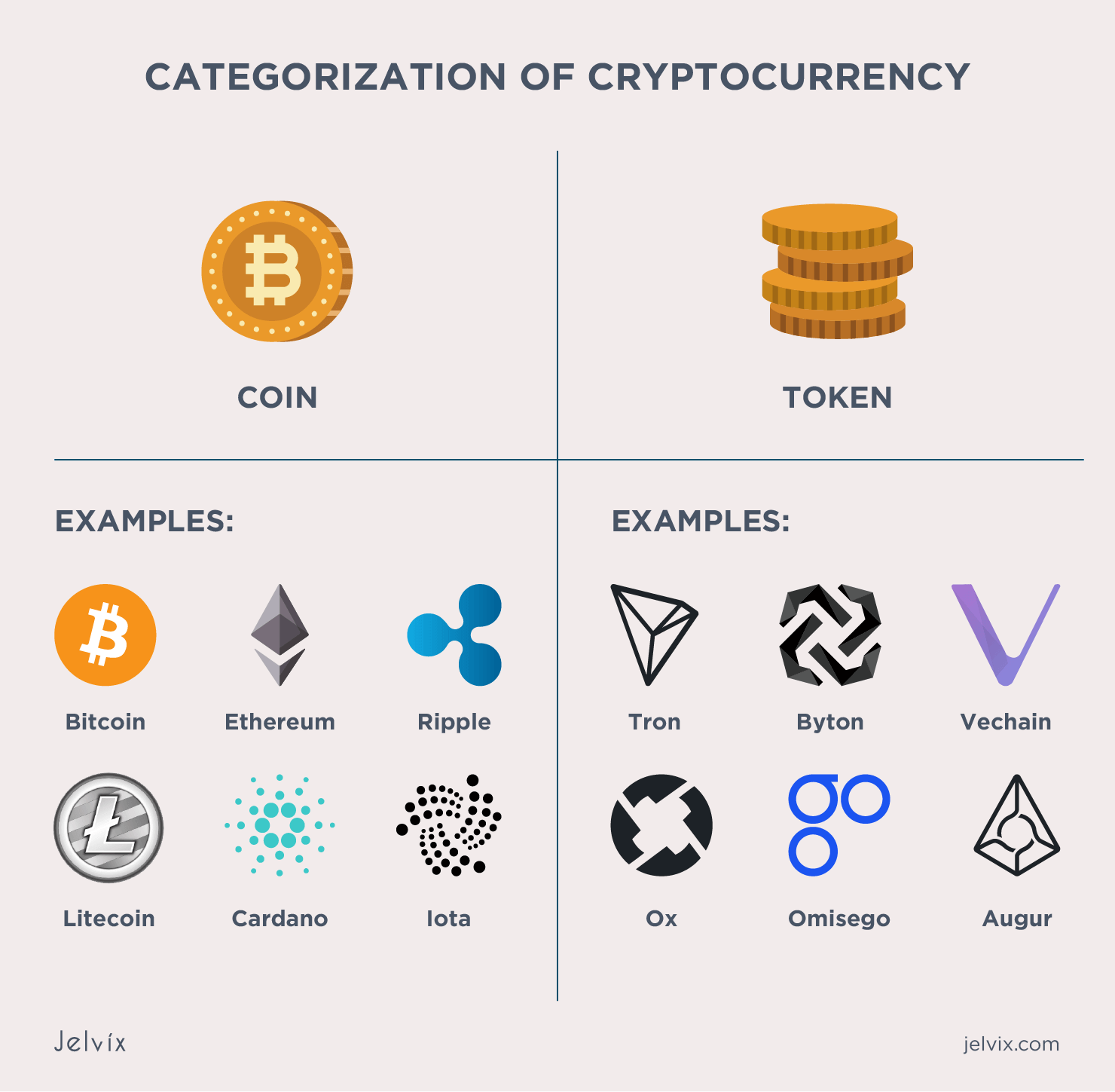
Before writing a single line of code, an architect must define the fundamental structure of the digital asset. This begins with a critical distinction in the blockchain world: the difference between a “coin” and a “token.”
Coin vs. Token: Deciding Your Infrastructure
Technically, a coin (such as Bitcoin or Ether) operates on its own independent blockchain. Creating a coin requires building or forking an entire distributed ledger, establishing a network of nodes, and defining a proprietary protocol for transaction validation. This is a high-effort endeavor that offers maximum control over the environment.
Conversely, a token (such as an ERC-20 or BEP-20 asset) is built on top of an existing blockchain like Ethereum, Solana, or Binance Smart Chain. By leveraging an established infrastructure, developers can inherit the security and decentralization of the host network. For most modern applications, tokens are preferred due to their interoperability and lower technical overhead, though they remain subject to the gas fees and governance of the underlying layer.
Choosing a Consensus Mechanism: PoW, PoS, and Beyond
The consensus mechanism is the heartbeat of any cryptocurrency; it is the protocol through which a distributed network of computers agrees on the validity of transactions.
- Proof of Work (PoW): The legacy system used by Bitcoin. It requires significant computational power to solve complex mathematical puzzles. While highly secure, it is difficult to scale and requires a massive hardware footprint.
- Proof of Stake (PoS): The modern standard, adopted by Ethereum 2.0. It selects validators based on the number of coins they hold and are willing to “stake.” PoS is significantly more energy-efficient and allows for higher transaction throughput.
- Delegated Proof of Stake (DPoS) and Proof of History (PoH): Advanced variations used by networks like Solana to achieve lightning-fast speeds by optimizing how time and voting are handled across the network.
Selecting the Development Pathway: From Scratched Code to Hard Forks
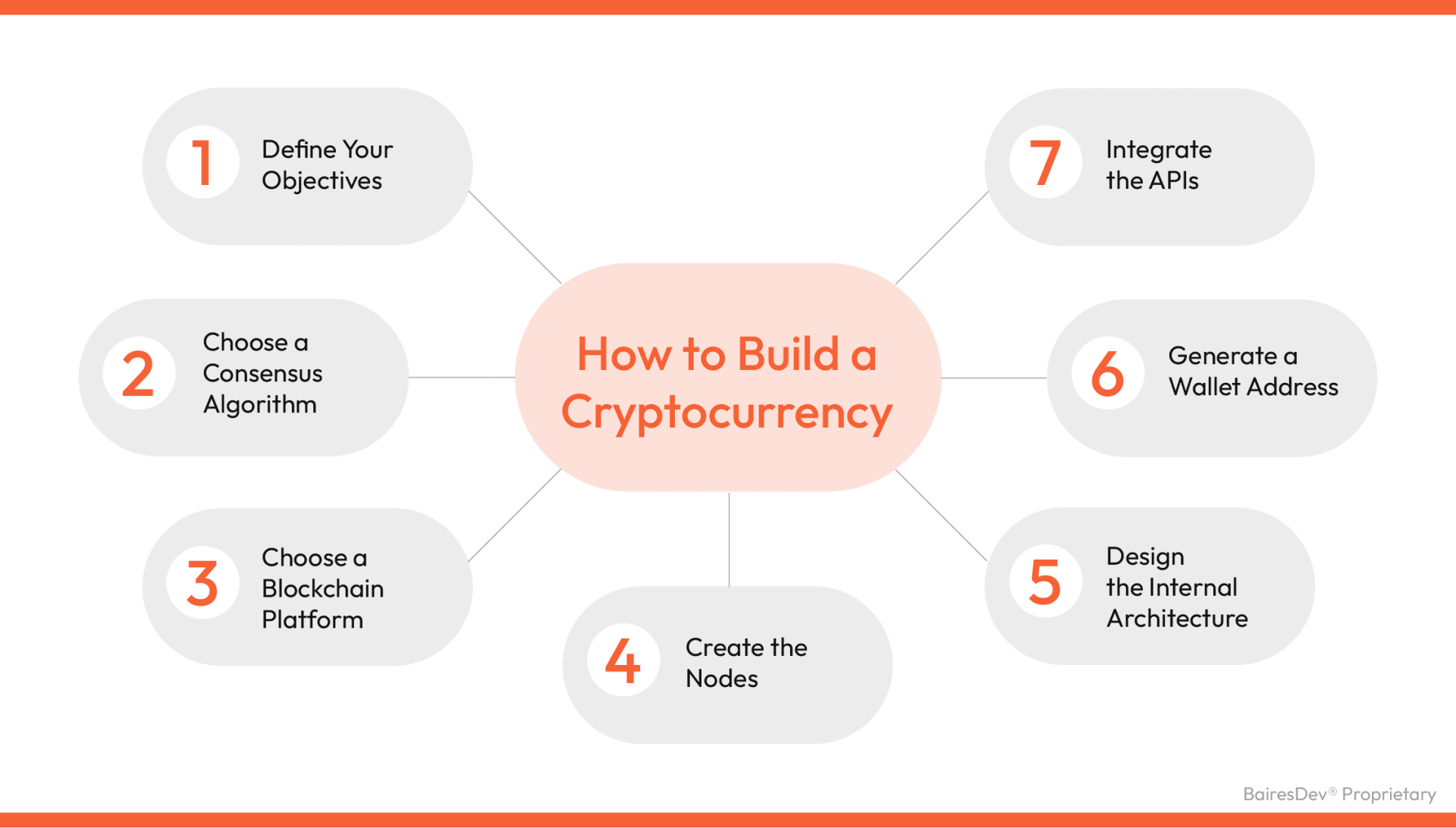
Once the architecture is defined, the developer must choose the methodology for implementation. There are three primary technical routes to creating a cryptocurrency.
Building a Proprietary Blockchain
For projects requiring unique functionality—such as a specific privacy feature or a non-standard block time—building a new blockchain from scratch is the most rigorous path. This involves using languages like C++, Rust, or Go to develop the core engine. You must define the block size, the reward frequency for miners or validators, and the peer-to-peer (P2P) communication protocol that allows nodes to synchronize. While this path offers total sovereignty, it requires the developer to bootstrap their own network of validators to ensure security.
Leveraging Existing Frameworks
To avoid reinventing the wheel, many developers use “blockchain-in-a-box” frameworks. Tools like Substrate (used for Polkadot) or the Cosmos SDK allow engineers to build modular, custom blockchains without having to write the networking layer from scratch. These frameworks provide pre-built modules for governance, staking, and identity, allowing the developer to focus on the unique logic of their specific application.
Implementing a Hard Fork
A “hard fork” involves taking the open-source code of an existing blockchain (like Bitcoin or Litecoin), modifying its parameters, and launching it as a new network. This was the origin of Bitcoin Cash and Dogecoin. While this is the fastest way to launch a standalone coin, it requires a significant effort to convince node operators to support the new software version rather than the original one.
The Technical Implementation Phase
With the framework selected, the development shifts toward the actual creation of the digital ledger and the rules that govern it.
Designing the Nodes and Internal Architecture
Nodes are the individual computers that run the blockchain software. In a custom-built cryptocurrency, you must program the “Node Logic,” which includes the mempool (where unconfirmed transactions wait), the database (usually a LevelDB or RocksDB structure to store the chain state), and the API layer. The architecture must be designed to handle asynchronous data transmission, ensuring that if one node goes offline, the rest of the network continues to function without data corruption.
Smart Contract Development and Security Auditing
If you are building a token on an existing chain, the “cryptocurrency” is actually a smart contract—a self-executing piece of code. On Ethereum, this is written in Solidity. The code defines the total supply, how tokens are transferred, and how they can be “burned” or retired.
This stage is the most vulnerable point in the lifecycle. Because blockchain transactions are irreversible, a single bug in a smart contract can lead to the permanent loss of all funds. Professional developers utilize automated testing suites (like Truffle or Hardhat) and engage third-party security firms to perform manual code audits. These audits look for common vulnerabilities such as reentrancy attacks, integer overflows, and front-running risks.
Integrating APIs and User Interfaces
A cryptocurrency is useless if users cannot interact with it. The technical stack must extend beyond the ledger to include the tools required for human-to-machine interaction.
Connecting the Backend to Wallets and Explorers
For a new cryptocurrency to be functional, it must support wallet integration. This involves implementing the BIP-32/39/44 standards for hierarchical deterministic wallets, which allow users to generate public and private keys from a seed phrase.
Furthermore, developers must build or configure a Block Explorer. This is a web-based tool that queries the blockchain’s database and presents it in a human-readable format, allowing users to verify transactions, check balances, and view block height in real-time. This is usually achieved by creating a middleware layer that indexes the blockchain data into a traditional SQL or NoSQL database for fast querying.
Ensuring Scalability and Network Stability
Technical scalability is often the “Trilemma” of blockchain: balancing security, decentralization, and speed. During the implementation phase, engineers must optimize the data structures to ensure the network doesn’t bottleneck as transaction volume increases. This might involve implementing Layer 2 solutions, such as State Channels or Rollups, which process transactions off-chain and only post the final state to the main ledger.
Post-Deployment Security and Maintenance
The launch of the Genesis block—the very first block in a blockchain—is not the end of the technical journey, but the beginning of a continuous maintenance cycle.
Continuous Testing and Bug Bounties
In the software world, “stable” is a relative term. As new cryptographic exploits are discovered, the core protocol must be updated. Many technical teams establish “Bug Bounty” programs, inviting white-hat hackers to find vulnerabilities in the code in exchange for rewards. This crowdsourced security model is essential for maintaining the integrity of a decentralized system.

Upgradability and Governance Protocols
How does a decentralized network change its code? This is a technical challenge known as “Governance.” Developers must implement mechanisms for “on-chain” or “off-chain” voting. In a technical sense, this often involves a “Proxy Contract” pattern (for tokens) or a “Soft Fork” mechanism (for coins), where the network can transition to a new set of rules if a majority of the computing power or staked capital agrees to the update.
In conclusion, making a cryptocurrency is an intensive exercise in software engineering that demands precision across multiple disciplines. From the initial selection of a consensus algorithm to the final deployment of smart contracts and wallet APIs, every step must be reinforced with rigorous security protocols. By focusing on the technical integrity of the architecture, developers can build digital assets that are not only functional but resilient enough to withstand the complexities of the modern digital landscape.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.