In the intricate ecosystem of the internet, the Domain Name System (DNS) acts as the crucial translator, converting human-readable website addresses like www.example.com into machine-readable IP addresses. It’s the unsung hero that makes navigating the web as simple as typing a familiar name. However, this vital system is not immune to exploitation. One of the most insidious threats to DNS integrity is DNS cache poisoning, a sophisticated cyberattack that manipulates the DNS resolution process to redirect users to malicious websites. Understanding DNS cache poisoning is paramount for anyone concerned with digital security, as it can have far-reaching consequences for individuals and organizations alike.
The Mechanics of DNS Resolution: A Foundation for Understanding Attacks
Before delving into the intricacies of cache poisoning, it’s essential to grasp the fundamental workings of DNS resolution. This process, while seemingly straightforward, involves a hierarchical and distributed network of servers, each playing a role in fetching the correct IP address for a requested domain.
How DNS Resolution Works: From Query to IP Address
When you type a web address into your browser, or when an application needs to connect to a server by its domain name, a DNS query is initiated. This query doesn’t immediately travel to a single, definitive server. Instead, it embarks on a journey through a series of DNS servers.
-
Recursive Resolver (Your ISP or Public DNS): The first stop for your query is typically a recursive resolver. This server is responsible for fulfilling the DNS request on behalf of the client (your device). It will either have the answer readily available in its cache or will undertake the task of finding it from other DNS servers.
-
Root Name Servers: If the recursive resolver doesn’t have the answer, it contacts one of the 13 clusters of root name servers distributed globally. These servers don’t hold the IP addresses for specific websites but instead point to the Top-Level Domain (TLD) name servers (e.g.,
.com,.org,.net). -
TLD Name Servers: The recursive resolver then queries the relevant TLD name server. The TLD server, in turn, directs the resolver to the authoritative name server for the specific domain.
-
Authoritative Name Server: This is the ultimate source of truth for a domain’s DNS records. The authoritative name server holds the definitive IP address associated with the requested domain name. Once the recursive resolver receives this IP address, it returns it to your device.
This entire process is designed for efficiency and speed. To avoid repeating the same queries for popular websites, recursive resolvers and even local devices (like your computer or router) maintain a cache of recently resolved DNS records. This is where the vulnerability lies.
The Role of DNS Caching: Speed vs. Security
DNS caching is a crucial optimization technique. When a recursive resolver or a local system resolves a domain name, it stores the resulting IP address for a specific period, known as the Time-To-Live (TTL). If another request for the same domain arrives within the TTL, the cached record is returned instantly, bypassing the need for a full DNS lookup. This significantly reduces latency and the load on DNS infrastructure.
However, the integrity of this cache is paramount. If the cached information is incorrect, all subsequent requests that rely on that cache will be directed to the wrong destination. This is precisely the opportunity that DNS cache poisoning exploits.
DNS Cache Poisoning: Hijacking the Trust in DNS
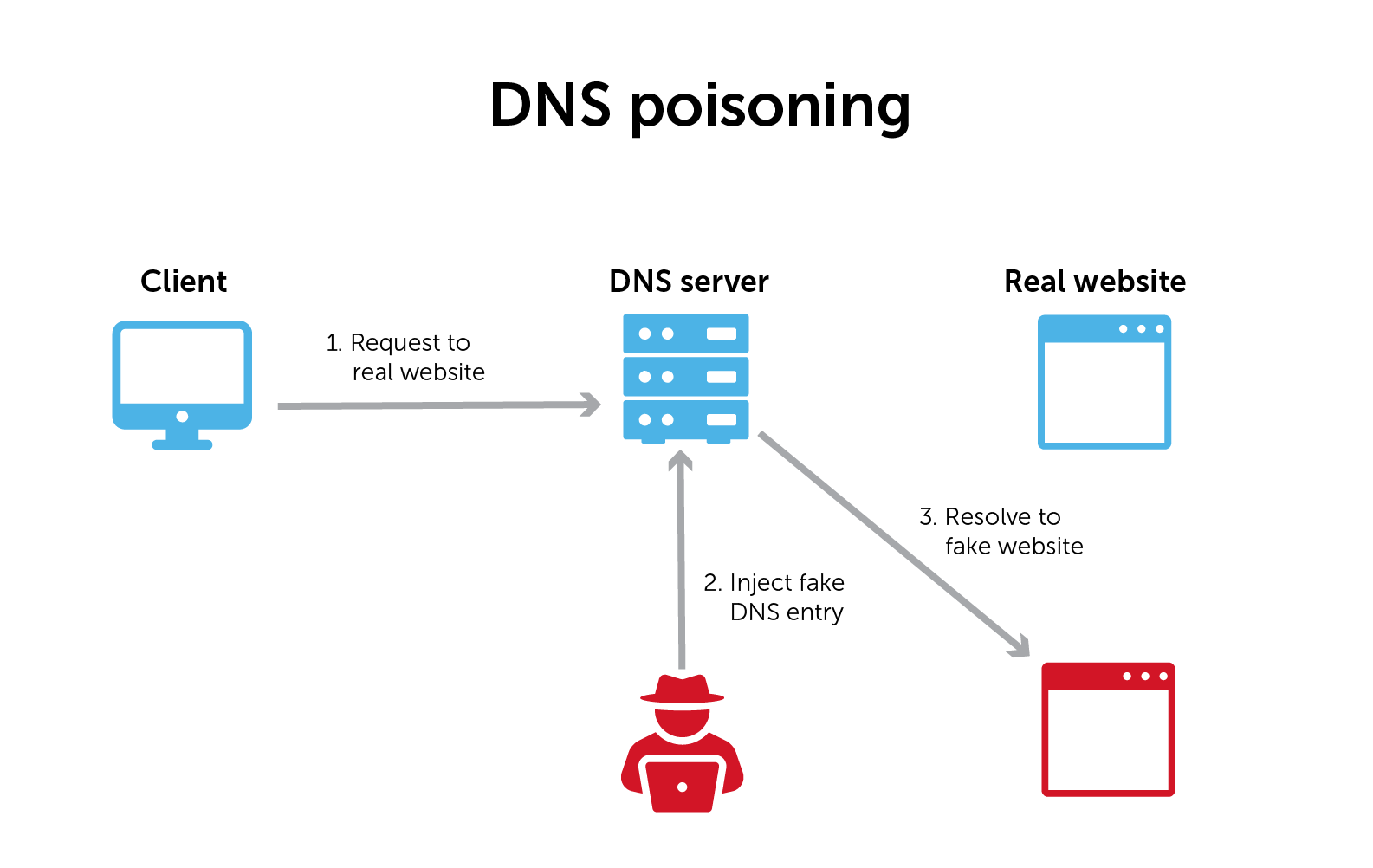
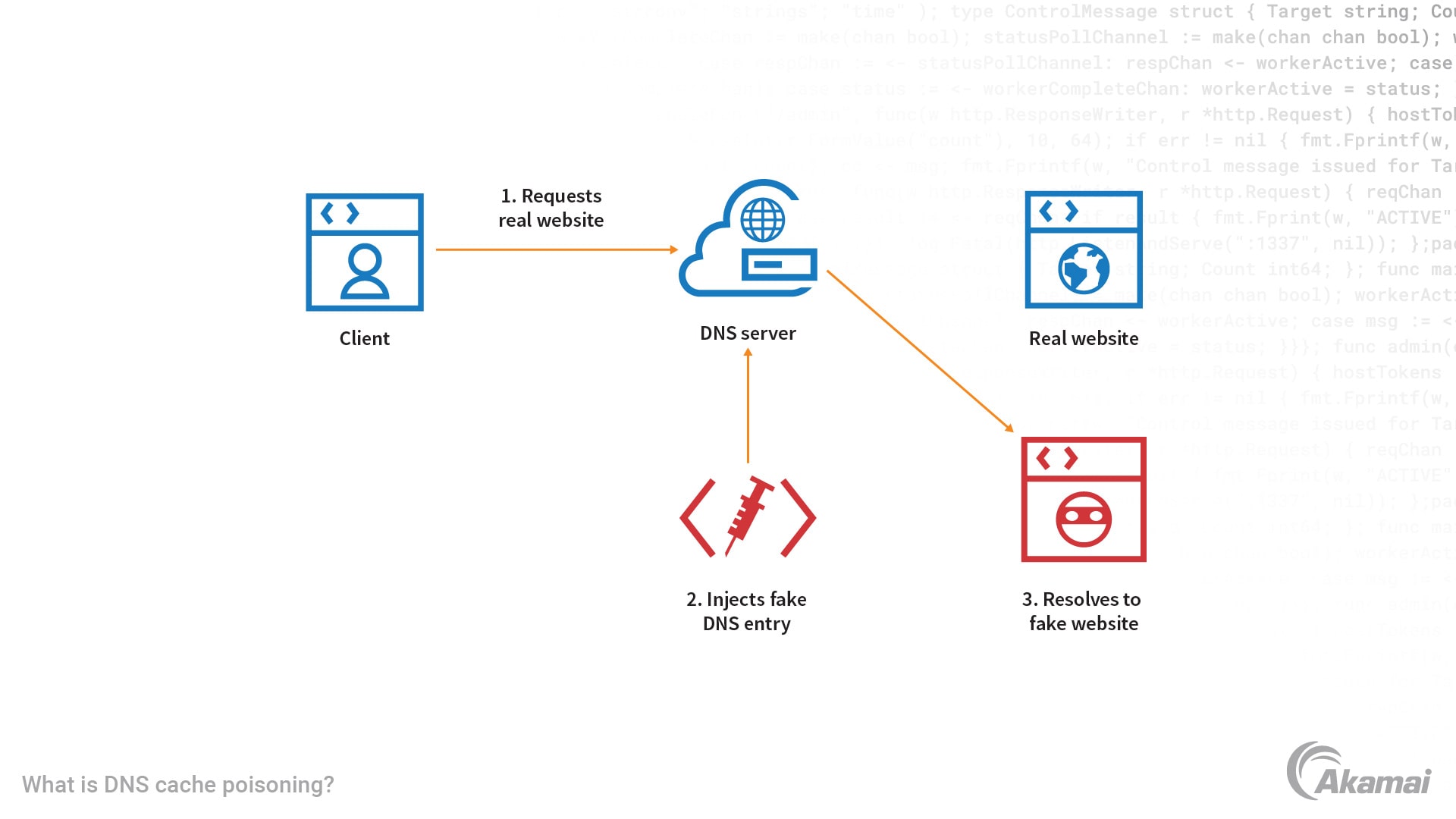
DNS cache poisoning, also known as DNS spoofing, is an attack where an attacker introduces falsified DNS records into a DNS resolver’s cache. The goal is to trick the resolver into believing that a malicious server is the legitimate host for a particular domain.
The Attacker’s Objective: Malicious Redirection
The primary aim of DNS cache poisoning is to redirect unsuspecting users to attacker-controlled websites. This redirection can serve various malicious purposes:
- Phishing: Users might be directed to a fake login page that closely resembles a legitimate website (e.g., a bank, social media platform, or email service). The attacker then captures the credentials entered by the user, compromising their accounts.
- Malware Distribution: The poisoned DNS record could point to a server hosting malware. When a user attempts to visit a legitimate site, they are instead served a malicious file that infects their device.
- Man-in-the-Middle (MITM) Attacks: By intercepting traffic and redirecting users to their own servers, attackers can gain the ability to read and modify communication between the user and the intended website.
- Denial of Service (DoS): In some scenarios, poisoned DNS records could be used to overload legitimate servers with traffic, making them unavailable to genuine users.
Exploiting the Query-Response Mechanism: The Core of the Attack
The success of a DNS cache poisoning attack hinges on the attacker’s ability to inject their forged DNS records into the cache before the legitimate record is obtained by the resolver. This often involves exploiting the stateless nature of UDP-based DNS queries, which are commonly used for performance reasons.
Here’s a simplified breakdown of a common poisoning technique:
-
Targeting a Vulnerable Resolver: The attacker identifies a DNS resolver that is susceptible to poisoning. This often involves resolvers that do not adequately validate DNS responses or use predictable transaction IDs.
-
Triggering a DNS Query: The attacker needs to cause the target resolver to query for a domain that they want to spoof. This can be done by tricking a user on the same network into visiting a specific website or by exploiting an application that makes such a query.
-
Flooding with Forged Responses: As soon as the target resolver sends its query to an authoritative server (or an upstream resolver), the attacker floods the network with spoofed DNS responses. These responses are crafted to look like they originate from the legitimate authoritative server.
-
Predicting Transaction IDs and Ports: A crucial element for the attacker is predicting the transaction ID (a unique number assigned to each DNS query) and the source port used by the target resolver. If the attacker can guess these correctly, their forged response will be accepted as valid.
-
Injecting the Malicious Record: The forged response contains a falsified DNS record, mapping the targeted domain to the attacker’s IP address. If this forged response arrives at the resolver before the legitimate response, and its transaction ID and port match, the resolver will cache the malicious information.
-
User Redirection: Once the cache is poisoned, any user whose request is resolved by that compromised resolver will be unknowingly directed to the attacker’s malicious server when they attempt to visit the targeted legitimate website.
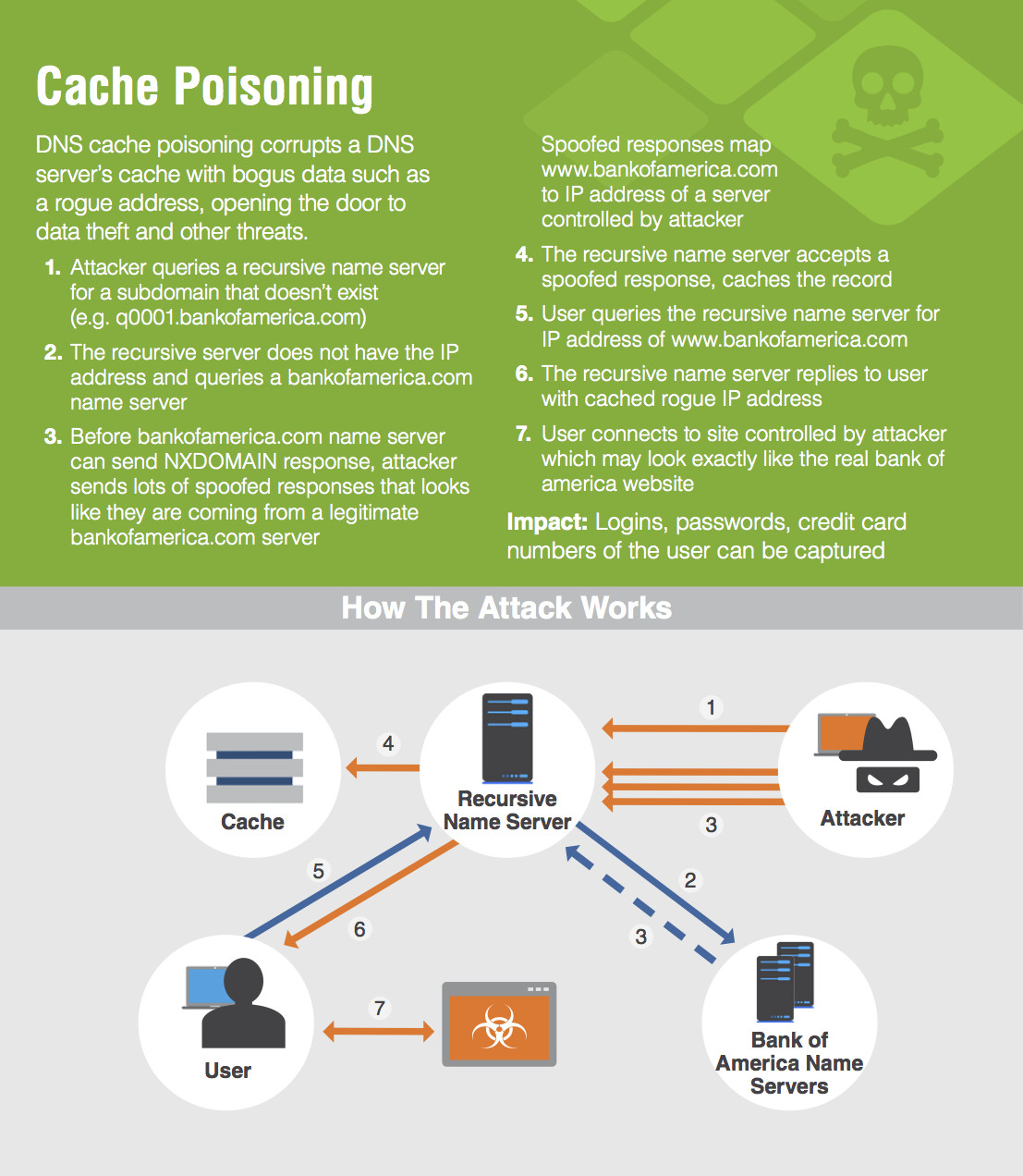
The effectiveness of this attack relies on the speed at which the attacker can deliver their spoofed response. Modern DNS security measures aim to make transaction ID prediction much harder, but vulnerabilities can still exist in older or misconfigured systems.
Defending Against DNS Cache Poisoning: Fortifying the Foundation
Protecting against DNS cache poisoning requires a multi-layered approach, involving both server-side configurations and client-side awareness. Organizations and individuals can implement several strategies to mitigate the risk of falling victim to these attacks.
Server-Side Defenses: Strengthening the Resolver
The primary responsibility for preventing DNS cache poisoning lies with the operators of DNS resolvers. Implementing robust security practices can significantly reduce the attack surface.
1. Randomizing Transaction IDs and Source Ports:
- Transaction ID Randomization: The most fundamental defense is to use cryptographically strong random numbers for DNS transaction IDs. This makes it extremely difficult for attackers to guess the correct ID for their spoofed responses.
- Source Port Randomization: Similarly, resolvers should use a wide range of randomized source ports for outgoing DNS queries. This further complicates the attacker’s ability to predict the necessary parameters for a successful spoof.
2. Implementing DNSSEC (DNS Security Extensions):
- Digital Signatures for DNS Records: DNSSEC is a suite of extensions that provides origin authentication and data integrity for DNS. It works by digitally signing DNS records, allowing resolvers to verify that the data they receive has not been tampered with and originates from the legitimate source.
- Chain of Trust: DNSSEC establishes a chain of trust from the root zone down to individual domains. Resolvers can validate the signature at each level, ensuring the authenticity of the entire DNS record chain. While DNSSEC is highly effective, its adoption is not yet universal, and it requires both domain owners and resolvers to implement it.
3. Using Secure Protocols for DNS Communication:
- DNS over TLS (DoT) and DNS over HTTPS (DoH): These protocols encrypt DNS queries and responses between the client and the resolver. While they primarily protect against eavesdropping and tampering during transit, they also add a layer of security by ensuring that the received DNS data has not been modified in transit by an intermediary attacker.
4. Keeping DNS Software Updated:
- Patching Vulnerabilities: Like any software, DNS server software can have vulnerabilities that attackers exploit. Regularly updating DNS server software to the latest versions is crucial, as updates often include security patches for known exploits, including those related to cache poisoning.
5. Limiting Recursive Queries and IP Address Spoofing:
- Restricting Recursion: DNS servers should be configured to only perform recursive lookups for authorized clients. Allowing open recursion makes them easier targets for attackers.
- Ingress Filtering: Network infrastructure should implement ingress filtering to drop packets with spoofed source IP addresses. This can help prevent attackers from successfully impersonating legitimate DNS servers.
Client-Side Awareness and Best Practices
While server-side defenses are critical, individuals and organizations can also take steps to reduce their personal risk.
1. Using Trusted DNS Servers:
- Public DNS Providers: Opting to use reputable public DNS providers (e.g., Google Public DNS, Cloudflare DNS) can be beneficial. These providers often invest heavily in security measures and may have more robust defenses against cache poisoning than your ISP’s default DNS servers.
- Manual Configuration: For enhanced security, users can manually configure their devices or routers to use these trusted DNS servers.
2. Being Wary of Suspicious URLs and Website Behavior:
- Unusual Domain Names: Be cautious of website URLs that seem slightly off or use unexpected Top-Level Domains.
- Website Discrepancies: If a website looks or behaves unexpectedly, especially after recent activity or network changes, it might be a sign of redirection.
- SSL Certificate Warnings: Browsers will issue warnings if an SSL certificate is invalid or doesn’t match the domain. Always heed these warnings and do not proceed if you are unsure.
3. Employing Endpoint Security Solutions:
- Antivirus and Anti-Malware Software: Keeping endpoint security software up-to-date can help detect and block malware that might be downloaded from a poisoned website.
- Web Application Firewalls (WAFs): For organizations, WAFs can help detect and block malicious traffic, including requests that might be part of a DNS poisoning attack or lead to compromised sites.
The Evolving Landscape of DNS Threats
DNS cache poisoning is not a static threat. As security measures evolve, attackers continuously seek new vulnerabilities and refine their techniques. The ongoing development and deployment of DNS security protocols, such as DNSSEC, are vital in combating these persistent threats.
The Importance of Proactive Security Measures
The internet relies on the fundamental trust we place in the DNS. When that trust is violated through DNS cache poisoning, the consequences can range from minor annoyances to severe data breaches and financial losses. Therefore, a proactive approach to digital security is essential. This involves staying informed about emerging threats, implementing best practices, and continuously evaluating and strengthening security postures.
By understanding the mechanics of DNS resolution, the methods employed in DNS cache poisoning attacks, and the comprehensive defense strategies available, both individuals and organizations can significantly reduce their vulnerability. The future of a secure and reliable internet depends on our collective commitment to fortifying the foundational systems that power our digital lives, ensuring that the translation from names to addresses remains a trusted and secure process.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.