In the biological world, the nuclear envelope serves as a sophisticated gatekeeper, a double-membrane structure that encases the cell’s genetic blueprint, shielding it from the chaotic environment of the cytoplasm. In the realm of high-level information technology and digital security, the concept of a “nuclear envelope” has been adopted as a powerful metaphor for the architectural safeguards that protect an organization’s “nucleus”—its most sensitive data, proprietary algorithms, and critical source code.
As we navigate an era defined by sophisticated cyber warfare, ransomware, and the rapid decentralization of data, understanding what a digital nuclear envelope does is no longer a niche concern for systems architects; it is a foundational requirement for any enterprise aiming to survive the modern threat landscape. This article explores the functions of the digital nuclear envelope, the mechanics of its protective layers, and its role in the future of secure computing.
The Architecture of the Digital Nuclear Envelope
In a tech context, the nuclear envelope represents the multi-layered security perimeter that isolates core assets from the external network and internal “noise.” This is not a single firewall but a coordinated ecosystem of hardware and software protocols designed to ensure that the “DNA” of the company remains uncorrupted.
Defining the Perimeter in a Decentralized World
Traditionally, the “perimeter” of a network was easy to define: it was the office building and the local server. Today, with the rise of the Internet of Things (IoT), remote work, and multi-cloud environments, the “nucleus” of a company is often fragmented. The digital nuclear envelope functions as a logical boundary rather than a physical one. It utilizes software-defined perimeters (SDP) to create a “black cloud” around sensitive data, making it invisible to unauthorized users and external probes.
Why “Nuclear” Security Matters for Big Data
We refer to this level of security as “nuclear” because of the stakes involved. When we talk about protecting the nucleus of a modern tech enterprise, we are referring to the crown jewels: the customer databases, the financial transaction logs, and the unique IP that provides a competitive edge. If these are compromised, the “cell” (the organization) ceases to function. The envelope’s primary duty is to prevent unauthorized transcription or replication of this vital data.
The Layers of Protection: How the Envelope Functions
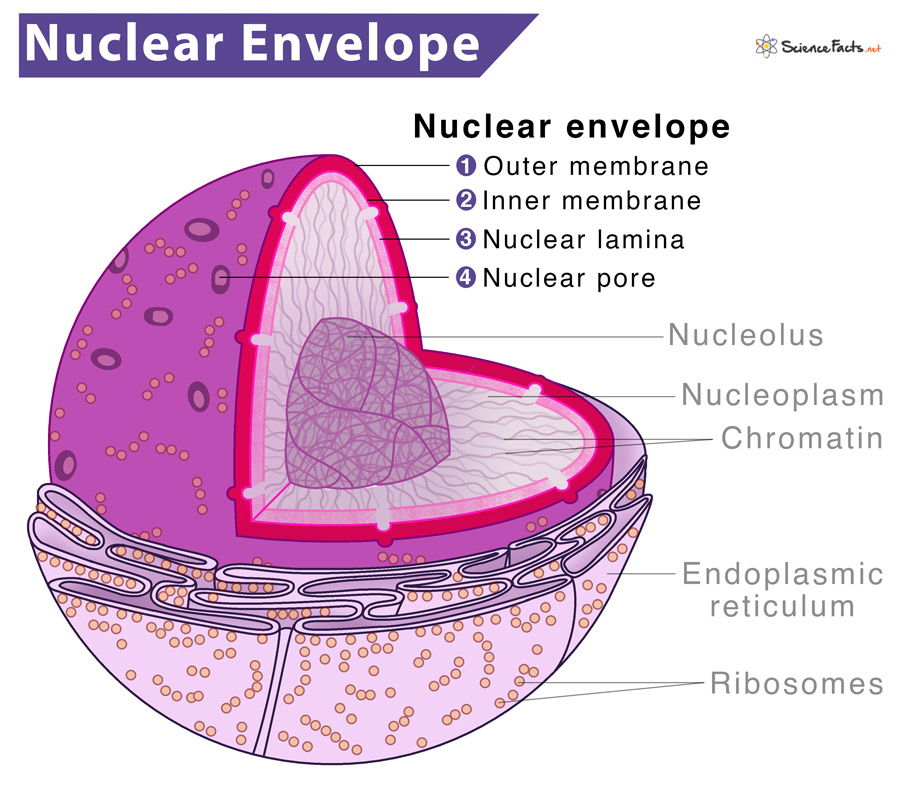
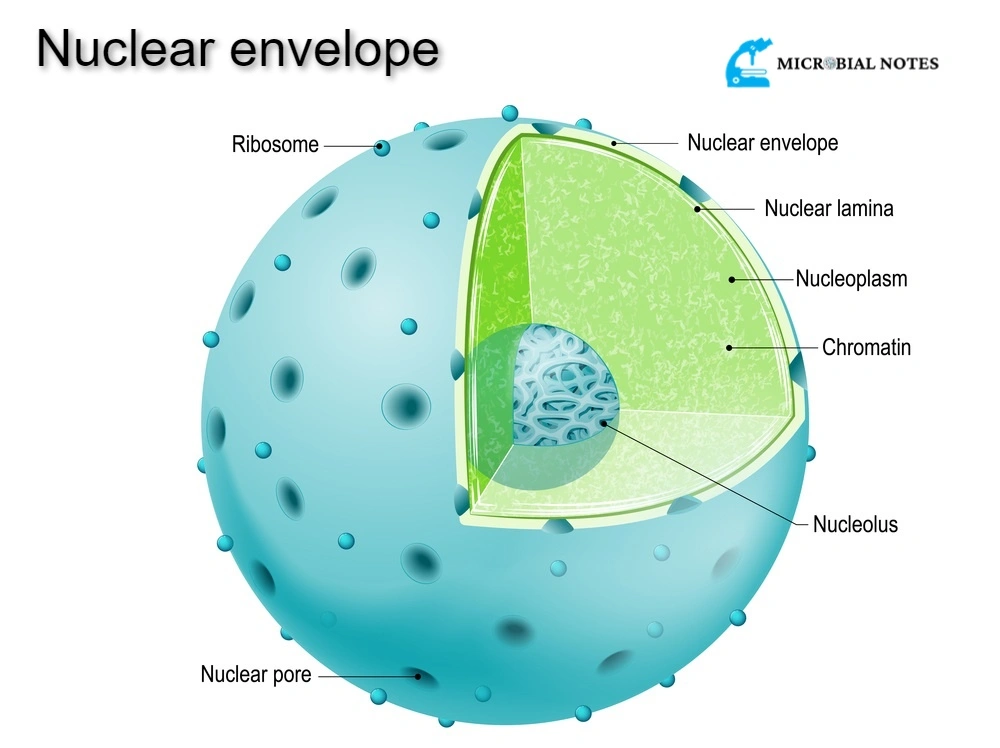
Just as the biological envelope consists of an inner and outer membrane, a digital security envelope utilizes a dual-layered approach to ensure that even if one layer is breached, the core remains protected. This redundancy is the hallmark of a “Defense in Depth” (DiD) strategy.
The Outer Layer: Firewalls and Intelligent Gateways
The outer membrane of the digital nuclear envelope is the first line of defense. This includes Next-Generation Firewalls (NGFW), Intrusion Prevention Systems (IPS), and Distributed Denial of Service (DDoS) protection. This layer is responsible for scanning the “extracellular environment”—the public internet—and filtering out known malicious traffic. By utilizing machine learning algorithms, these gateways can identify patterns of attack before they reach the internal network, acting as a highly selective filter.
The Inner Layer: Access Management and Zero Trust
The inner membrane is where the most critical protection occurs. Even if a user or a packet of data passes the outer firewall, they are not automatically trusted. This is the implementation of the “Zero Trust” model. Within the digital nuclear envelope, every request for data access must be authenticated, authorized, and continuously validated. This layer utilizes Identity and Access Management (IAM) and Multi-Factor Authentication (MFA) to ensure that only the most privileged “proteins” (authorized users and processes) can interact with the core data.
Regulating Information Flow: The Digital “Nuclear Pore”
In biology, the nuclear envelope is perforated by “nuclear pores” that regulate the movement of molecules between the nucleus and the cytoplasm. In technology, these pores are represented by Application Programming Interfaces (APIs) and secure data ports. These are the most vulnerable and yet the most necessary parts of the system.

Data Encapsulation and Packet Inspection
A digital nuclear envelope must allow for the flow of information; otherwise, the data is useless. The “pore” function is managed through deep packet inspection (DPI) and data encapsulation. When data attempts to enter or leave the core, it is “wrapped” in encryption protocols (such as TLS 1.3). The envelope inspects the metadata of these packets—checking their origin, their destination, and their “signature”—to ensure that no malicious code is being smuggled into the nucleus under the guise of legitimate traffic.
Identity as the Key to the Pore
The modern tech envelope has shifted from “IP-based” security to “Identity-based” security. In this model, the “pore” does not open for a specific computer; it opens for a specific, verified identity. Using biometrics, hardware tokens, and behavior analytics, the digital nuclear envelope creates a dynamic gatekeeping system. If an authorized user suddenly attempts to download the entire database at 3:00 AM from a new location, the “pore” recognizes the anomaly and seals the envelope, preventing a data exfiltration event.
Guarding Against “Genetic” Code Manipulation
The most critical function of a biological nuclear envelope is protecting the integrity of DNA. In the tech world, the “DNA” is the source code. If a hacker can inject malicious code into a software’s core, they can control the entire system from the inside out—a digital version of a viral infection.
DevSecOps and the Integrity of the Core
To protect the integrity of the “digital DNA,” the nuclear envelope must extend into the development pipeline. This is known as DevSecOps. By integrating security checks directly into the Continuous Integration/Continuous Deployment (CI/CD) pipeline, the envelope ensures that every “strand” of code added to the core is scanned for vulnerabilities, secrets (like hardcoded passwords), and backdoors. This proactive shielding ensures that the nucleus is built to be resilient from the moment of inception.
Responding to “Viral” Malware Infiltrations
Despite the best defenses, threats like polymorphic malware and zero-day exploits act like viruses, attempting to bypass the envelope’s defenses. A robust digital nuclear envelope includes “Endpoint Detection and Response” (EDR) and “Extended Detection and Response” (XDR) capabilities. These tools act like an immune response within the envelope. If a breach is detected, the system can automatically isolate the affected “cell” or segment of the network, preventing the lateral movement of the threat and protecting the central nucleus from contamination.
The Future of the Envelope: AI and Quantum Resilience
As technology evolves, the threats against the digital nucleus become more sophisticated. The nuclear envelope of tomorrow will look very different from the static firewalls of the past, moving toward a self-healing, intelligent architecture.
AI-Driven Adaptive Envelopes
The next generation of digital security involves “Autonomous SOC” (Security Operations Centers). These are nuclear envelopes driven by Artificial Intelligence that can reshape themselves in real-time. If an AI detects a new type of attack pattern on the global web, it can instantly update the “membranes” of all protected systems, hardening the envelope before the attack even arrives. This predictive capability transforms the envelope from a passive shield into an active, evolving organism.
Quantum-Proofing the Core
The looming threat of quantum computing poses a significant risk to current encryption methods—the very “fabric” of our digital membranes. A quantum computer could potentially “unzip” traditional encryption in seconds. Consequently, tech innovators are currently developing “Quantum-Resistant Cryptography.” This will be the next evolution of the nuclear envelope, utilizing lattice-based cryptography to ensure that the nucleus remains secure even in the face of the most powerful computing capabilities ever developed.
Conclusion: The Indispensable Role of the Digital Envelope
What does a nuclear envelope do? It preserves the essence of the system it protects. In biology, that essence is life; in technology, it is information and integrity. As our reliance on digital infrastructure grows, the “nuclear envelope” model of security provides a vital framework for understanding how to protect what matters most.
By implementing multi-layered membranes, regulated “pores” of communication, and an immune-like response to threats, organizations can ensure that their digital nucleus remains uncompromised. In an era where data is the most valuable resource on earth, the digital nuclear envelope is the most important piece of technology an enterprise can build, maintain, and evolve. It is the difference between a system that thrives and one that is lost to the digital void.
