In the history of digital innovation, few technologies have promised—and delivered—as much disruption as the blockchain. While often conflated with cryptocurrencies like Bitcoin, blockchain is fundamentally a breakthrough in computer science, cryptography, and distributed systems. At its simplest level, a blockchain is a distributed, immutable ledger that records transactions across a network of computers. However, the “how” behind this definition involves a sophisticated interplay of consensus algorithms, cryptographic hashing, and peer-to-peer networking.
To understand how blockchain works from a technical perspective, we must move beyond the financial hype and examine the structural integrity of the software and the protocols that maintain it.
The Structural Foundation: Blocks, Hashes, and the Chain
The architecture of a blockchain is defined by its data structure. Unlike a traditional database managed by a central authority (like a bank or a tech giant), a blockchain stores information in “blocks” that are linked together in a chronological, permanent sequence.
The Anatomy of a Block
Every block in the chain consists of three primary elements: the data, the nonce, and the hash.
- Data: This is the specific information being recorded. In a financial context, it includes the sender, receiver, and amount. In a technical context, it can be any digital asset or piece of code, such as a smart contract.
- Nonce: A “number used once.” This is a random whole number that is generated when a block is created, which then generates a block header hash.
- Hash: This is a fixed-length alphanumeric string generated by a cryptographic algorithm (most commonly SHA-256). The hash acts as a digital fingerprint, uniquely identifying the block and all of its contents.
The Cryptographic Link
The “chain” aspect of blockchain comes from the fact that each block contains the hash of the block that preceded it. This creates a mathematical dependency. If any data within a block is altered, the hash of that block changes instantly. Because the subsequent block contains the original hash, the link is broken, and the network immediately identifies the discrepancy. This design ensures that the history of the ledger remains intact and tamper-evident.
Distributed Ledger Technology (DLT)
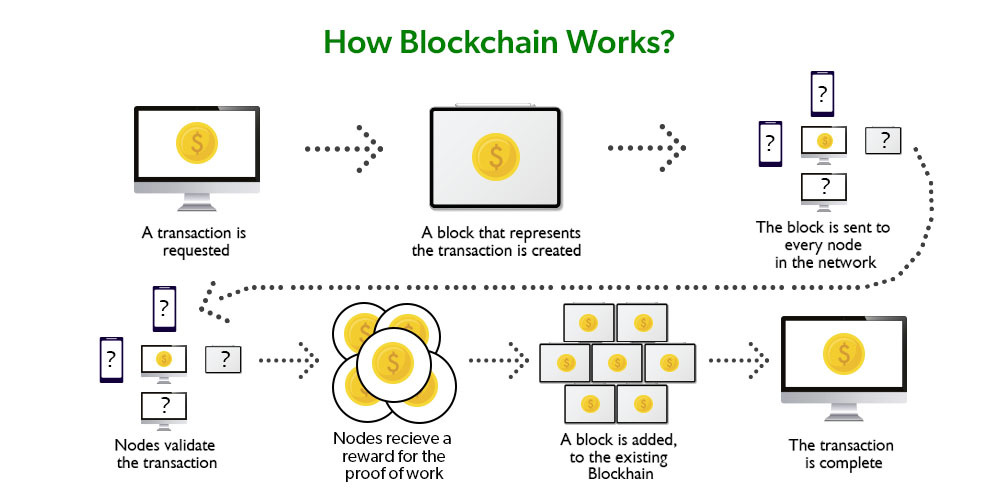
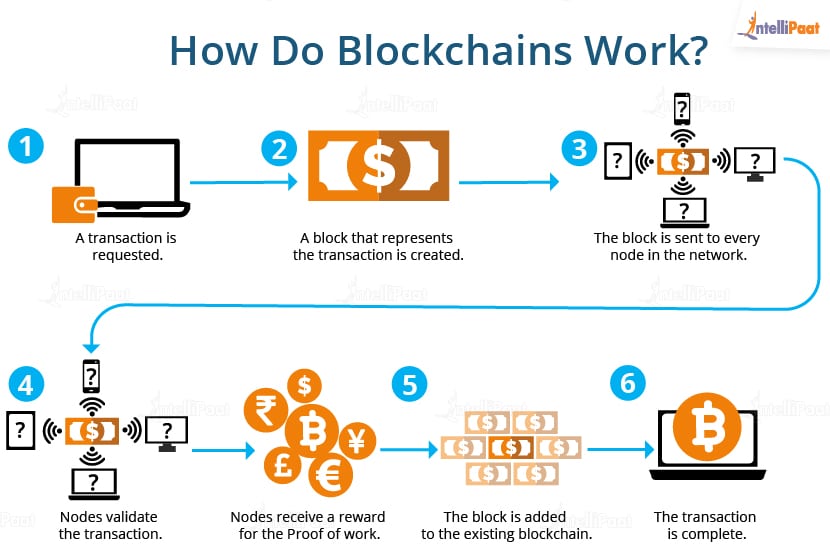
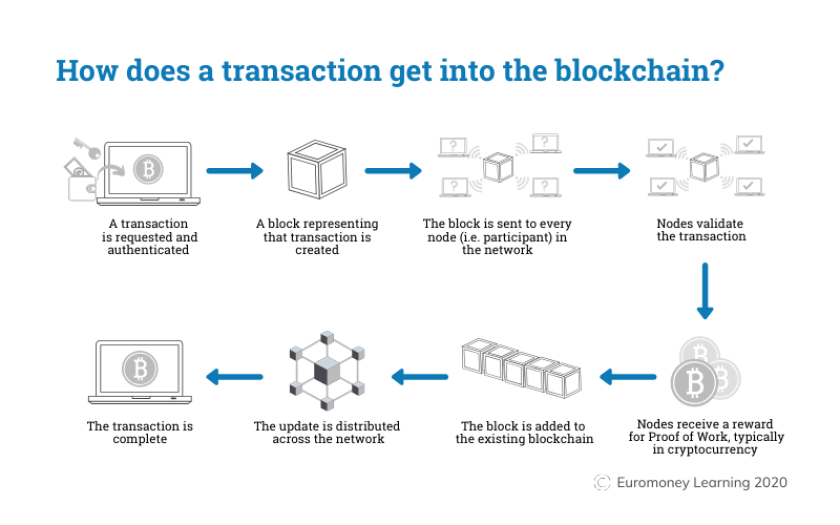
While a single chain of blocks is conceptually simple, the power of blockchain lies in its distribution. The ledger is not stored in one central server. Instead, it is replicated across a vast network of “nodes”—individual computers running the blockchain software. Every node has a full copy of the entire history of the blockchain. When a new block is added, every node updates its version of the ledger, ensuring there is no single point of failure.
The Engine of Trust: Consensus Mechanisms
Because there is no central administrator to decide which transactions are valid, the network must rely on a “consensus mechanism.” This is a set of rules and protocols that allow distributed nodes to agree on the state of the ledger.
Proof of Work (PoW)
Proof of Work is the original consensus algorithm used by Bitcoin. It requires nodes (called miners) to solve complex mathematical puzzles to validate transactions and create new blocks. This process is computationally expensive and requires significant energy. The “work” serves as a deterrent to bad actors; to successfully cheat the system, an attacker would need to control more than 51% of the network’s total computing power—a feat that is practically impossible in a sufficiently large network.
Proof of Stake (PoS)
As a more energy-efficient alternative, many modern blockchains (such as Ethereum 2.0) use Proof of Stake. In this system, “validators” are chosen to create new blocks based on the number of tokens they “stake” or lock up as collateral. If a validator attempts to process a fraudulent transaction, they lose their staked assets. This aligns the technical security of the network with the economic incentives of the participants, ensuring that the software remains secure without the massive electricity consumption of PoW.
Byzantine Fault Tolerance
At the heart of consensus is a classic problem in computer science known as the Byzantine Generals Problem. It asks: how can multiple parties reach a consensus when they do not trust each other and some may be malicious? Blockchain solves this through algorithmic agreement. By requiring a majority of nodes to verify a block before it is added to the chain, the system achieves “fault tolerance,” meaning it can continue to operate correctly even if some nodes fail or act dishonestly.
Digital Security and Immutability
The primary technical appeal of blockchain is its inherent security. In a world of frequent data breaches and centralized vulnerabilities, blockchain offers a “trustless” environment where security is guaranteed by mathematics rather than human oversight.
The Role of Hashing in Integrity
Cryptographic hashing is the cornerstone of blockchain security. Using algorithms like SHA-256, the software takes an input of any size and produces an output of a fixed size. This process is a “one-way function”—it is easy to generate a hash from data, but computationally impossible to determine the original data from a hash. This ensures that data remains private and that any attempt to modify even a single bit of information will result in a completely different hash, alerting the network to a security breach.
Public and Private Key Cryptography
Blockchain utilizes asymmetric encryption to manage identity and authorization. Users possess a “public key” (which acts like an email address or account number) and a “private key” (which acts like a digital signature or password). When a transaction is initiated, the user signs it with their private key. Nodes on the network use the corresponding public key to verify that the signature is authentic without ever needing to see the private key. This ensures that only the rightful owner of a digital asset can move it.
The Concept of Immutability
Once a block is verified and added to the chain, it becomes “immutable.” To change a record in an old block, a hacker would have to re-mine that block and every subsequent block, out-pacing the rest of the network’s collective computing power. This makes the blockchain a “write-once, read-many” system, providing a level of data integrity that traditional databases, which allow for “Create, Read, Update, Delete” (CRUD) operations, cannot match.
Advanced Logic: Smart Contracts and Programmable Tech
The evolution of blockchain technology has led to the development of “Smart Contracts.” Popularized by the Ethereum network, these are self-executing contracts with the terms of the agreement directly written into lines of code.
Automating the Logic Layer
A smart contract is essentially an “if-then” statement stored on the blockchain. For example, “If Party A delivers the digital asset, then the payment is automatically released to Party B.” Because these contracts run on the blockchain, they operate exactly as programmed without any possibility of downtime, censorship, fraud, or third-party interference. This removes the need for intermediaries (like lawyers or escrow agents) and automates complex technical workflows.
Decentralized Applications (dApps)
Smart contracts serve as the back-end code for Decentralized Applications, or dApps. Unlike standard apps (like Twitter or Uber) where the data and logic are controlled by a single company, dApps run on a peer-to-peer network. This shift in software architecture moves us toward “Web3,” a decentralized version of the internet where users own their data and the underlying protocols are transparent and open-source.
Interoperability and Scaling Solutions
One of the current frontiers in blockchain tech is solving the “Blockchain Trilemma”—the challenge of balancing security, decentralization, and scalability. Engineers are developing “Layer 2” solutions (like Lightning Network or Rollups) that process transactions off the main chain to increase speed and lower costs, while still relying on the main chain for final security. Additionally, “cross-chain” protocols are being built to allow different blockchains to communicate with one another, creating a more cohesive global digital infrastructure.
Conclusion: The Future of the Digital Ledger
Blockchain is far more than a foundation for digital currency; it is a fundamental shift in how we handle data and digital trust. By combining the transparency of a shared ledger with the security of advanced cryptography, blockchain creates a system where “the code is the law.”
As the technology matures, we are seeing its integration into supply chain management, secure voting systems, digital identity verification, and the Internet of Things (IoT). In each of these cases, the “how” remains the same: a decentralized, immutable, and cryptographically secured chain of data that ensures truth without the need for a central authority. Understanding this technical architecture is essential for anyone looking to navigate the next wave of the digital revolution.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.