In an increasingly interconnected digital world, the question of “what is SMS authentication?” has become foundational to understanding modern cybersecurity. As our lives migrate further online – from banking and shopping to social interaction and professional work – the need for robust, accessible, and reliable identity verification methods has never been more critical. SMS (Short Message Service) authentication, often encountered as a one-time passcode (OTP) sent to your mobile phone, stands as a widespread and remarkably effective defense mechanism against unauthorized access to accounts. It acts as a crucial second layer of security, transforming a simple password into a more formidable barrier against cyber threats.
At its core, SMS authentication leverages the ubiquity of mobile phones to confirm a user’s identity. While passwords have long been the primary gatekeepers of our digital presence, their inherent vulnerabilities – susceptibility to phishing, brute-force attacks, and reuse across multiple services – necessitate an additional layer of verification. This is precisely where SMS authentication steps in, providing what is known as two-factor authentication (2FA) or multi-factor authentication (MFA), making it significantly harder for malicious actors to gain entry even if they manage to compromise a password. This article will delve into the mechanics, importance, different forms, and future considerations of SMS authentication, offering a comprehensive look at this vital component of digital security.
The Foundation of Digital Identity: Understanding SMS Authentication
SMS authentication isn’t just a technical feature; it’s a cornerstone of trust in the digital realm. It bridges the gap between a user’s known credentials and a physical, unique device they possess, significantly elevating the security posture of online interactions.
Defining SMS Authentication: A Layer of Trust
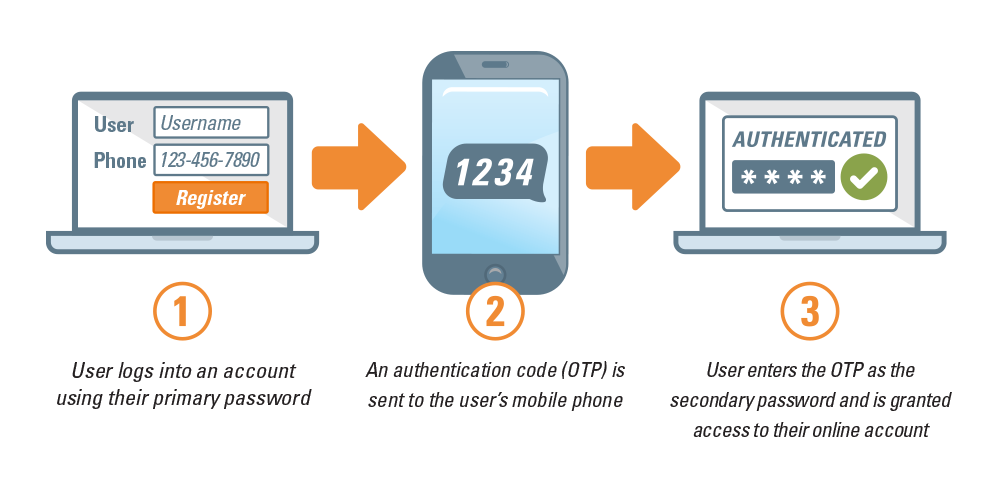
SMS authentication, at its simplest, is a security process that verifies a user’s identity by sending a unique code or message to their registered mobile phone number. This process typically occurs after the user has successfully entered their primary credentials, such as a username and password. The assumption is that only the legitimate account holder possesses the phone linked to that number, thus providing an additional, distinct factor of authentication.
This method falls under the broader umbrella of multi-factor authentication (MFA), which requires users to present two or more verification factors from independent categories. These categories are typically:
- Something you know: (e.g., a password, PIN)
- Something you have: (e.g., a mobile phone, hardware token)
- Something you are: (e.g., a fingerprint, facial scan, voice recognition)
SMS authentication explicitly uses “something you have” (your mobile phone) in conjunction with “something you know” (your password), creating a robust two-factor defense. This dual requirement drastically reduces the likelihood of unauthorized access, even if one factor is compromised.
How It Works: The Mechanics Behind the Message
The process of SMS authentication is remarkably straightforward from a user’s perspective, yet involves several background steps to ensure security:
- Initiation: A user attempts to log in or perform a sensitive action (e.g., changing a password, making a large transaction) on an application or website.
- Primary Authentication: The user first enters their username and password.
- Request for Second Factor: If the primary credentials are correct, the system recognizes that SMS authentication is enabled for the account. It then generates a unique, time-sensitive code (often 4-8 digits long), known as a One-Time Passcode (OTP).
- SMS Delivery: This OTP is sent via SMS to the mobile phone number pre-registered with the account.
- User Input: The user receives the SMS, retrieves the OTP, and enters it into a designated field on the application or website.
- Verification: The system verifies if the entered OTP matches the one it generated and if it is still valid (i.e., hasn’t expired).
- Access Granted: Upon successful verification, the user is granted access to their account or the sensitive action is completed.
This sequence ensures that even if a hacker possesses a user’s username and password, they cannot gain access without also having physical control of the registered mobile device to receive and input the OTP.
Why SMS Authentication is Crucial in Today’s Digital Landscape
The proliferation of cyber threats makes SMS authentication not just a convenience, but a critical necessity for individuals and organizations alike. Its widespread adoption highlights its effectiveness in combating an array of digital dangers.
Bolstering Security: Protecting Against Unauthorized Access
The primary rationale behind SMS authentication is to significantly enhance digital security. Passwords, despite their widespread use, are inherently vulnerable. They can be stolen through phishing attacks, guessed through dictionary attacks, cracked through brute-force methods, or exposed in data breaches. When a password alone is the only barrier, an attacker who obtains it gains full access.
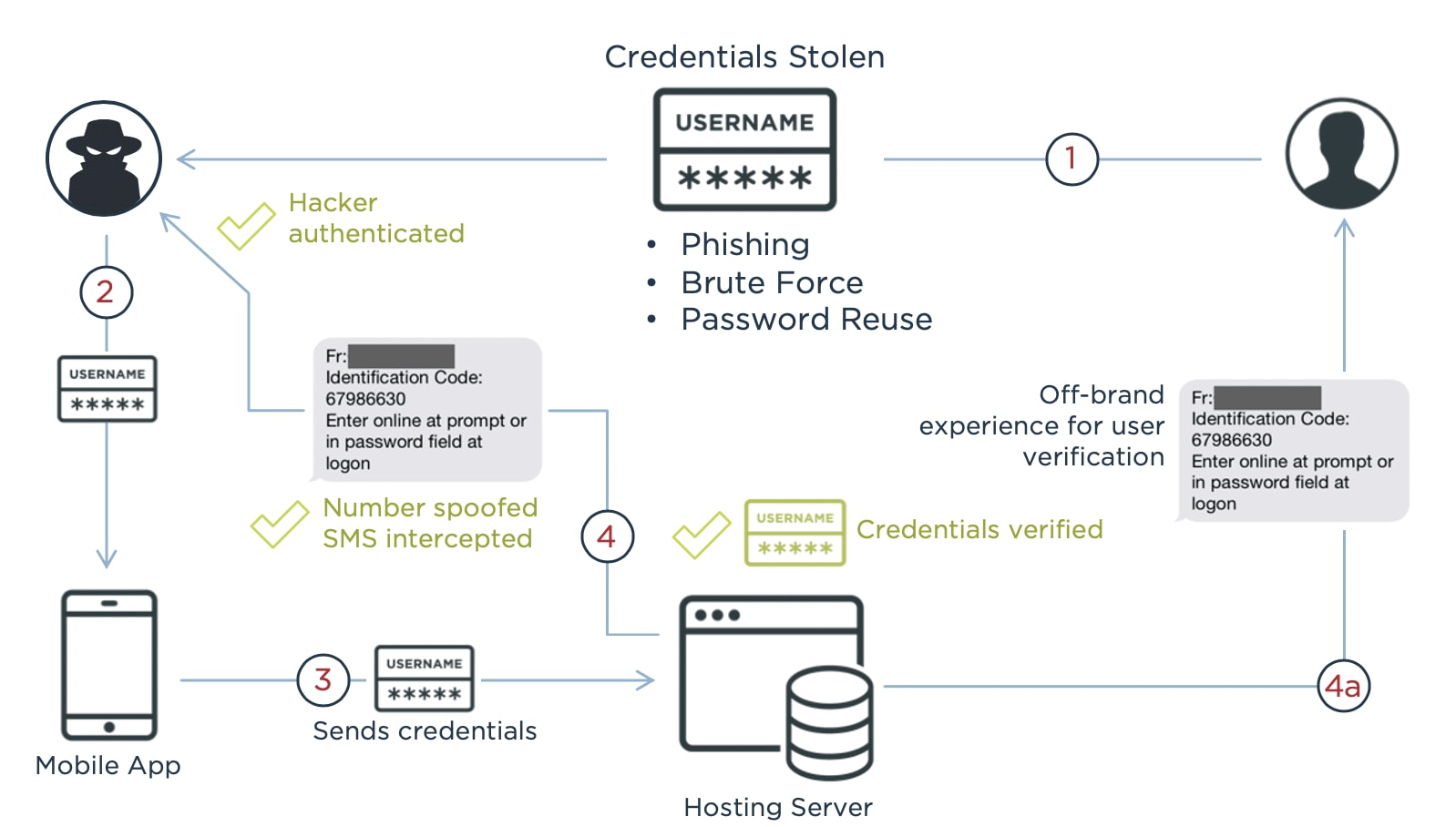
SMS authentication fundamentally changes this dynamic. By requiring a second, independent factor – something the user possesses – it creates a substantial hurdle for attackers. Even if a cybercriminal successfully compromises a user’s password, they would still need to intercept the SMS code or physically steal the user’s mobile phone to complete the login process. This dramatically reduces the success rate of many common cyberattacks, including:
- Phishing: Even if a user falls for a phishing scam and enters their credentials on a fake site, the attacker cannot log in without the SMS code.
- Credential Stuffing: This attack involves using breached credentials from one site to gain access to others. SMS authentication thwarts this, as the OTP would not be available to the attacker.
- Brute-Force Attacks: These automated attempts to guess passwords are rendered useless if a second factor is required.
User Experience vs. Security: Finding the Balance
One of the reasons for SMS authentication’s widespread adoption is its ability to strike a balance between enhanced security and reasonable user experience. Compared to more complex authentication methods, receiving and entering an SMS code is generally quick, intuitive, and requires no special hardware beyond a standard mobile phone. This low barrier to entry has made it palatable for a broad demographic, from tech-savvy individuals to those less familiar with intricate security protocols.
However, the “user experience” aspect can sometimes be challenging, especially in areas with poor mobile network coverage, leading to delayed or undelivered SMS messages. Despite these occasional glitches, for the vast majority of users, SMS authentication is perceived as a minor inconvenience that provides significant peace of mind.
Regulatory Compliance and Industry Standards
In numerous industries, the implementation of multi-factor authentication, including SMS authentication, is no longer optional but a regulatory requirement. Financial institutions, healthcare providers, and organizations handling sensitive personal data are often mandated by laws such as GDPR, HIPAA, and various payment industry standards (e.g., PCI DSS) to employ strong authentication mechanisms. SMS authentication frequently serves as a compliant and accessible method to meet these stringent security mandates, demonstrating a commitment to protecting customer and client data.
Different Flavors of SMS Authentication: Beyond the Basic OTP
While the concept of an SMS-delivered code is often associated with simple logins, SMS authentication can be deployed in various sophisticated ways to secure different types of interactions.
One-Time Passcodes (OTP): The Gold Standard
The most common form of SMS authentication is the One-Time Passcode (OTP). As discussed, this is a short, numerically or alphanumerically generated code sent to a user’s registered mobile device. Key characteristics of OTPs include:
- Time Sensitivity: OTPs are typically valid for a very short duration (e.g., 30 seconds to 5 minutes), minimizing the window for an attacker to intercept and use the code.
- Single Use: Each OTP is valid for only one login session or transaction, preventing replay attacks where a captured code could be reused.
- Randomness: OTPs are generated randomly, making them unpredictable and difficult to guess.
OTPs are widely used for initial logins, password resets, and confirming new device registrations.

Transactional Authentication: Verifying Critical Actions
Beyond merely logging in, SMS authentication is frequently employed to verify critical transactions or changes within an account. For instance:
- Financial Transactions: Confirming a funds transfer, a large purchase, or adding a new payee.
- Account Changes: Verifying a change in email address, phone number, or security settings.
- E-commerce: Authorizing a high-value online purchase.
In these scenarios, the SMS message might include details of the transaction itself (e.g., “Confirm transfer of $500 to John Doe. Reply YES to confirm.”), making it even harder for an attacker to proceed without the user’s explicit knowledge and confirmation.
Step-Up Authentication: Adapting Security to Risk
Some systems utilize “step-up” authentication, where the level of security required adapts based on the perceived risk of an action. For routine, low-risk activities, a simple password might suffice. However, for high-risk actions – such as accessing sensitive personal data, initiating a large financial transfer, or changing core security settings – the system might “step up” and require SMS authentication as an additional verification layer. This intelligent approach balances security needs with user convenience, avoiding unnecessary friction for everyday tasks.
Device Registration via SMS
When a user logs into an account from a new or unrecognized device, SMS authentication can be used to verify the legitimacy of this new device. A code is sent to the registered phone, and upon successful entry, the new device might be “trusted” or “remembered” for future logins, reducing the need for repeated SMS authentication on that specific device. This enhances both security and convenience.
The Strengths and Weaknesses: A Balanced Perspective
While SMS authentication offers significant advantages, it is not without its vulnerabilities and limitations. A clear understanding of both is essential for effective digital security.
Advantages: Accessibility, Simplicity, and Widespread Adoption
- Ubiquity: Mobile phones are pervasive globally, making SMS authentication highly accessible to a vast user base without requiring specialized hardware or software.
- Ease of Use: The process of receiving and entering a code is generally intuitive and quick, leading to high user adoption rates.
- Cost-Effectiveness: For service providers, implementing SMS authentication can be more cost-effective than developing and maintaining proprietary hardware tokens or complex biometric systems.
- Low Barrier to Entry: It requires minimal technical knowledge from the end-user, fostering broader security adoption.
Disadvantages: Vulnerabilities and Emerging Threats
Despite its strengths, SMS authentication is not foolproof. Several vulnerabilities have emerged over time:
- SIM Swapping/Porting Attacks: This is one of the most significant threats. An attacker socially engineers a mobile carrier to transfer the victim’s phone number to a SIM card controlled by the attacker. Once the number is swapped, the attacker can receive SMS OTPs and gain access to accounts.
- SMS Interception: While less common for the average user, sophisticated attackers can potentially intercept SMS messages using malware on the phone, rogue cell towers (IMSI catchers), or by exploiting vulnerabilities in SS7 (Signaling System No. 7), the protocol underlying global telecommunications networks.
- Phone Loss/Theft: If a phone is lost or stolen and not adequately secured (e.g., no screen lock), an attacker could access incoming SMS messages and potentially use them to compromise accounts.
- Network Latency/Reliability: SMS delivery can be subject to network delays, poor signal, or carrier issues, leading to frustrating wait times or failed login attempts for users.
- Phishing of OTPs: Attackers can create fake login pages that not only steal credentials but also prompt the user for the SMS OTP in real-time, relaying it to the legitimate site before it expires.
Best Practices for Robust SMS Authentication Implementation
To mitigate these risks, both users and service providers must adopt best practices:
- For Users:
- Enable screen locks and strong device passwords.
- Be wary of unsolicited messages or calls asking for OTPs.
- Monitor for suspicious activity from your mobile carrier (e.g., unexplained loss of service, new SIM cards).
- Consider alternative MFA methods (authenticator apps, hardware keys) for critical accounts.
- For Service Providers:
- Implement rate limiting for OTP requests to prevent abuse.
- Educate users about SIM swapping risks.
- Monitor for suspicious login patterns (e.g., login attempts from new locations followed by OTP requests).
- Consider implementing strong anti-fraud measures on the backend to detect and prevent SIM swap attacks.
- Offer multiple MFA options to users, allowing them to choose the most secure and convenient method for them.
The Future of Authentication: Moving Beyond SMS?
While SMS authentication remains highly relevant, the cybersecurity landscape is constantly evolving. Newer, often more secure, authentication methods are gaining traction, signaling a potential shift in how we verify our identities online.
The Rise of Authenticator Apps and Biometrics
- Authenticator Apps: Apps like Google Authenticator, Authy, or Microsoft Authenticator generate time-based one-time passcodes (TOTPs) directly on the user’s device. These codes are generated algorithmically and do not rely on cellular networks, making them immune to SIM swapping and SMS interception. They are generally considered more secure than SMS OTPs.
- Biometrics: Fingerprint scans, facial recognition, and iris scans offer a highly convenient and often secure “something you are” factor. Integrated into smartphones and laptops, biometrics provide a seamless authentication experience, though they come with unique privacy and spoofing concerns.
FIDO2 and Passwordless Authentication
The FIDO (Fast Identity Online) Alliance is driving the adoption of passwordless authentication through standards like FIDO2. This technology leverages cryptographic keys stored on a user’s device (e.g., via a USB security key like YubiKey, or built-in platform authenticators like Windows Hello) to verify identity. FIDO2 aims to eliminate passwords entirely, offering a highly secure and phishing-resistant authentication method.
The Continued Relevance of SMS as a Fallback or Secondary Method
Despite the emergence of more advanced authentication methods, SMS authentication is unlikely to disappear entirely in the near future. Its sheer accessibility and ease of use mean it will likely continue to serve as:
- A Primary Option for Less Critical Accounts: For services where the risk profile is lower, SMS authentication remains a perfectly adequate and convenient security measure.
- A Fallback Mechanism: When a user loses access to their authenticator app or hardware key, SMS can often serve as a recovery or fallback option, preventing account lockout.
- An Onboarding Tool: It’s an easy and universally understood method for onboarding new users to services.
Its role may evolve from a primary 2FA method to a secondary or fallback option, but its utility in providing an accessible layer of security remains undeniable.
Conclusion
SMS authentication has served as a pivotal component in strengthening digital security for over a decade, providing an essential second layer of defense against a myriad of cyber threats. By leveraging the ubiquity of mobile phones, it transformed a simple password into a more formidable barrier, significantly reducing the success rates of phishing, credential stuffing, and other common attacks. Its accessibility, ease of use, and alignment with regulatory standards have cemented its status as a widely adopted and effective security measure for millions of users worldwide.
While the digital landscape continues to evolve, bringing forth more sophisticated threats and innovative authentication methods like authenticator apps and passwordless technologies, SMS authentication is not obsolete. It maintains its relevance as a highly accessible primary option for many services, a crucial fallback mechanism for account recovery, and an effective tool for user onboarding. Understanding “what is SMS authentication” is not just about comprehending a technical process; it’s about appreciating a vital layer of trust that underpins our modern digital interactions, even as we look towards a future of even more robust and seamless identity verification. As technology progresses, the strategic integration of SMS authentication within a broader multi-factor strategy will continue to play a crucial role in safeguarding our digital lives.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.