In the world of gastroenterology, a “patulous esophagus” refers to an esophagus that remains abnormally open, failing to close the lower esophageal sphincter. This prevents the body from containing its internal environment, leading to reflux and systemic inefficiency. In the realm of high-scale software engineering and cybersecurity, the term has been adopted as a potent metaphor for a specific type of architectural failure: the Patulous Esophagus of Data.
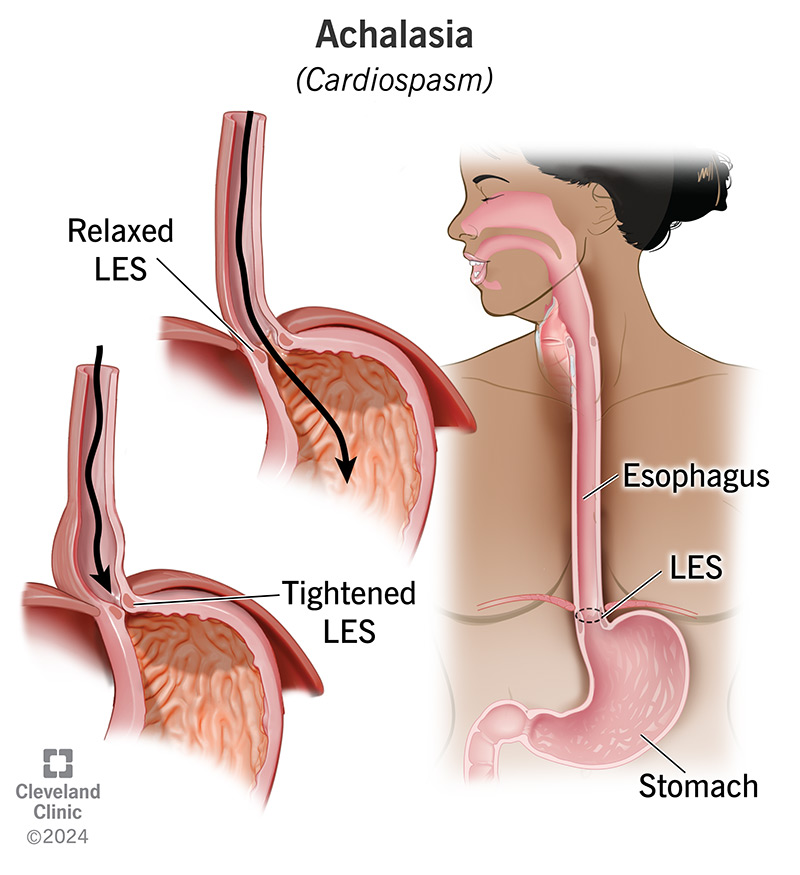
A Patulous Esophagus in a tech stack occurs when a system’s entry or exit points—specifically APIs, data streams, or cloud ingress points—remain “abnormally open.” This lack of a “sphincter” or gatekeeping mechanism results in resource exhaustion, security vulnerabilities, and “data reflux,” where sensitive information spills back into unintended layers of the infrastructure. Understanding this phenomenon is critical for architects building the next generation of resilient, secure, and cost-effective digital ecosystems.

The Anatomy of a Patulous System Architecture
At its core, the Patulous Esophagus metaphor describes a failure in state management and perimeter control. In a healthy system, connections should be ephemeral, authenticated, and tightly governed. When a system becomes “patulous,” the boundaries between the internal and external environments blur.
Persistent Connections vs. Ephemeral Requests
The shift toward real-time applications has led many developers to favor persistent connections, such as WebSockets or long-polling mechanisms. While these are essential for low-latency communication (like live trading dashboards or chat apps), they often lack the “valves” necessary to shut down idle connections. A patulous architecture keeps thousands of idle sockets open, consuming memory and CPU cycles without delivering value. This is the digital equivalent of an open valve that refuses to close, causing the system’s “stomach” (the database) to be constantly exposed to the “throat” (the public internet).
The Open Pipe Problem in Real-Time Data Streaming
Modern data architectures rely heavily on streaming platforms like Apache Kafka or Amazon Kinesis. A “patulous” data stream occurs when the consumer-producer relationship is unregulated. If a producer is pumping data into a stream without a back-pressure mechanism or a TTL (Time-to-Live) policy, the system becomes engorged. Without a functioning “sphincter” to regulate the flow, the downstream services suffer from “overflow,” leading to system-wide latency and eventual crashes.
Cybersecurity Risks: When the “Valve” Fails to Close
From a security perspective, a patulous esophagus is a nightmare. It represents a permanent invitation to bad actors. In cybersecurity, we often talk about “Least Privilege,” but a patulous system operates on the principle of “Maximum Exposure.”
Vulnerability to Data Siphoning and SQL Injection
When an API endpoint is left patulous—meaning it is poorly scoped or lacks robust rate-limiting—it becomes a straw through which an attacker can siphon an entire database. Most data breaches do not happen through a single catastrophic explosion; they happen through a slow, steady “leak” caused by an open architectural valve. If the “esophagus” of your application doesn’t have a mechanism to validate the “bolus” of data coming in, it allows malicious payloads to slide directly into the core logic of the application, leading to SQL injections or Remote Code Execution (RCE).
The Cost of “Always-On” Permissions (IAM Bloat)
Identity and Access Management (IAM) is the nervous system of cloud security. A patulous IAM configuration is one where permissions are granted “permanently” rather than “just-in-time.” When a service account has permanent, wide-open access to an S3 bucket or a database, that is a patulous connection. If that account is compromised, the “valve” cannot be remotely closed quickly enough to prevent disaster. In modern DevSecOps, the goal is to move away from these “always-open” pathways and toward “Zero Trust,” where every connection is closed by default and only opens when verified.

Modern Solutions: Implementing Smart Gateways and “Tight” Protocols
Fixing a patulous esophagus in a tech stack requires a combination of architectural “surgery” and better behavioral protocols. We must implement digital sphincters that are intelligent, responsive, and automated.
Zero Trust Architecture as the Corrective Surgery
Zero Trust is the ultimate cure for a patulous system. In a Zero Trust environment, the system assumes that the “esophagus” is always under threat. No connection is trusted simply because it originated from within the network. By implementing micro-segmentation, developers can ensure that even if one part of the system remains “open,” the rest of the organism remains protected. This involves using Service Meshes (like Istio or Linkerd) to manage how microservices talk to one another, ensuring that every “swallow” of data is authenticated, authorized, and encrypted.
API Gateways and Throttling Mechanisms
To prevent the “reflux” of unauthorized data, organizations must employ robust API Gateways. These gateways act as the “Lower Esophageal Sphincter” of the internet. They provide:
- Rate Limiting: Ensuring no single user can overwhelm the “valve.”
- Payload Validation: Checking the quality of the data before it enters the system.
- Circuit Breakers: If a downstream service is failing, the gateway automatically “closes the valve” to prevent the failure from cascading through the entire system.
By using tools like Kong, Apigee, or AWS API Gateway, companies can transform their wide-open, vulnerable connections into controlled, disciplined data pathways.
The Future of Streamlined Data Flow: AI and Predictive Scaling
As we move toward 2025 and beyond, the “patulous” problem will become more complex as AI-driven agents begin to interact with our systems. These agents can consume data at a rate far exceeding human users, meaning our architectural valves must become even more sophisticated.
AI-Driven Traffic Throttling
The next generation of load balancers will use Machine Learning to predict when a system is about to become “patulous.” By analyzing traffic patterns, these AI “surgeons” can dynamically tighten or loosen security protocols. For example, if the system detects a pattern of requests that looks like a slow-drip data exfiltration attempt, it can automatically introduce “latency-as-a-service” to frustrate the attacker, effectively “constricting” the esophagus to protect the stomach.
The Rise of Serverless and Ephemeral Computing
The most effective way to prevent a valve from staying open is to remove the valve entirely when it isn’t in use. This is the promise of Serverless computing (AWS Lambda, Google Cloud Functions). In a serverless model, the “esophagus” only exists for the duration of the request. Once the data is processed, the entire execution environment is dissolved. This “stateless” approach eliminates the risk of “always-on” vulnerabilities, providing a clean, healthy architecture that scales only when necessary.
Conclusion: Toward a Healthier Digital Organism
In technology, as in biology, the health of an organism is defined by its ability to maintain boundaries. A system with a “patulous esophagus”—one that cannot close its connections, regulate its data flow, or verify its inputs—is a system destined for failure. It will succumb to the “heartburn” of high operational costs, the “reflux” of security breaches, and the eventual exhaustion of its resources.
By identifying the “patulous” areas of your tech stack—whether they be idle WebSockets, over-privileged IAM roles, or unregulated data streams—you can begin the work of architectural refinement. Through Zero Trust principles, API management, and the adoption of ephemeral computing, we can build systems that are not just open to the world, but intelligently gated. In the digital age, the strongest systems aren’t the ones that are always open; they are the ones that know exactly when to close.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.