In the ever-evolving landscape of digital threats, cybersecurity professionals are constantly seeking ways to enhance their defensive capabilities. As the volume and sophistication of attacks grow, manual response and analysis become increasingly unsustainable. This is where SOAR – Security Orchestration, Automation, and Response – emerges as a crucial technology. SOAR platforms are designed to streamline and optimize cybersecurity operations, enabling organizations to respond to threats faster, more efficiently, and with greater accuracy.
The core concept behind SOAR is to bring together disparate security tools, automate repetitive tasks, and orchestrate complex incident response workflows. Imagine a highly skilled cybersecurity team, but amplified by intelligent automation. That’s the promise of SOAR. By integrating various security technologies and automating predefined actions, SOAR empowers security operations centers (SOCs) to move beyond manual, time-consuming processes and embrace a more proactive and agile approach to security.

This article will delve into what SOAR is, how it operates, its key benefits, and how it aligns with the broader technological advancements shaping our digital world, as well as its implications for brand reputation and financial efficiency in organizations.
Understanding the Pillars of SOAR
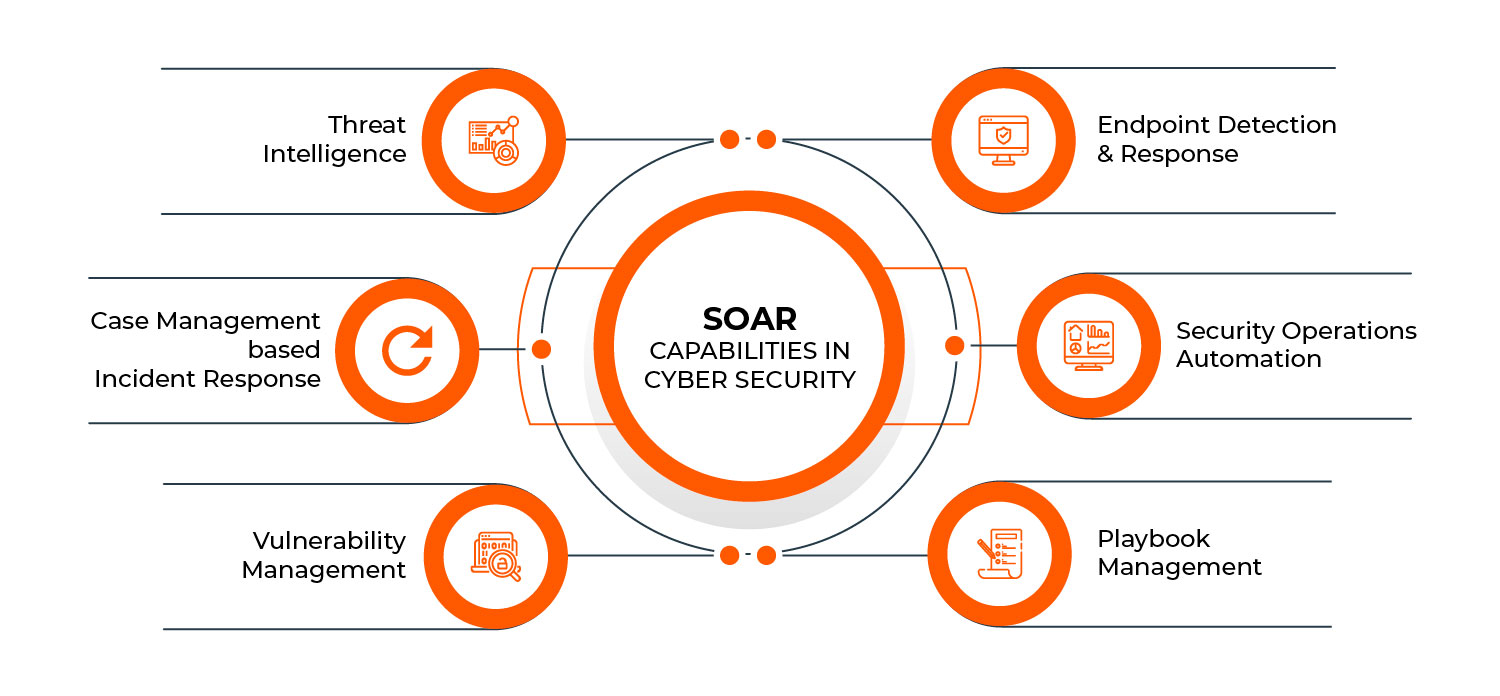
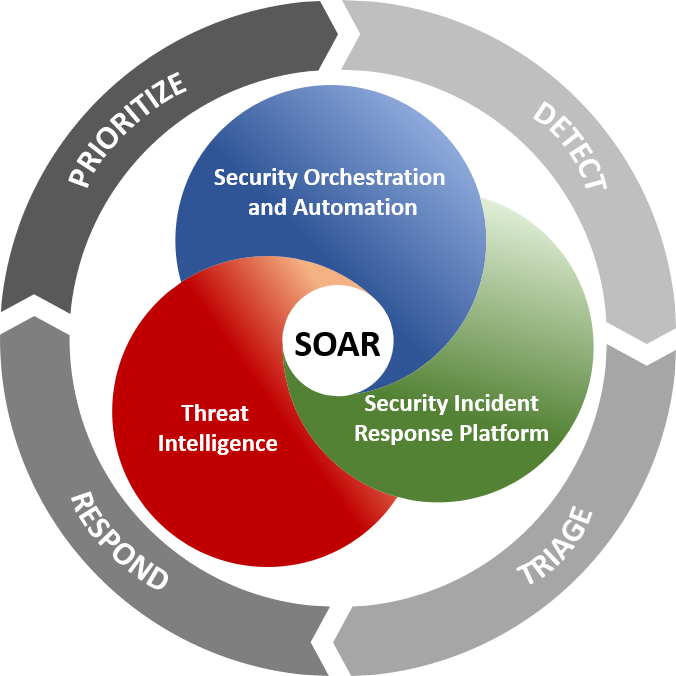
SOAR is not a single product but rather a category of solutions that combine three critical functionalities: Orchestration, Automation, and Response. Understanding each of these components is essential to grasping the full potential of SOAR.
Orchestration: Connecting the Dots
At its heart, orchestration in SOAR refers to the ability to connect and manage different security tools and technologies within an organization’s ecosystem. Modern cybersecurity relies on a multitude of specialized tools, from firewalls and intrusion detection systems (IDS) to endpoint detection and response (EDR) solutions, security information and event management (SIEM) platforms, and threat intelligence feeds. These tools often operate in silos, making it difficult to get a unified view of a security incident and coordinate a comprehensive response.
SOAR platforms act as a central nervous system, integrating these disparate tools through APIs (Application Programming Interfaces). This integration allows for seamless data sharing and enables actions to be triggered across multiple platforms. For example, when a security alert is generated by a SIEM, an orchestrated SOAR workflow can automatically query an EDR for endpoint details, retrieve threat intelligence from a specialized feed about the observed malicious IP address, and then update the firewall rules to block that IP. This interconnectedness eliminates manual data gathering and contextualization, significantly speeding up the initial stages of incident investigation.
The orchestration layer of SOAR is crucial for building efficient security workflows. It ensures that the right tools are used at the right time, with the right data being passed between them. This not only reduces the burden on human analysts but also minimizes the risk of errors that can occur during manual data transfers or cross-referencing. The ability to orchestrate these complex interactions is what allows SOAR to transform fragmented security operations into a cohesive and responsive unit.
Automation: Eliminating Repetitive Tasks
Automation is arguably the most tangible benefit of SOAR. It involves using technology to perform repetitive, rule-based tasks that would otherwise consume valuable time and resources of human analysts. Think about the daily deluge of security alerts – many of which are low-fidelity or false positives. Manually triaging each of these alerts is a monumental task.
SOAR platforms enable the automation of these tasks through pre-defined playbooks or workflows. These playbooks are essentially step-by-step instructions that dictate how the SOAR system should react to specific types of security events. For instance, a playbook for a phishing email alert might involve automatically:
- Isolating the affected endpoint: Preventing the malware from spreading further.
- Scanning the email for malicious attachments or links: Using built-in or integrated sandboxing tools.
- Searching for similar emails across the organization: Identifying potential widespread campaigns.
- Blocking identified malicious URLs or IP addresses at the firewall level.
- Enriching the alert with threat intelligence data: Providing context about the sender or payload.
By automating these actions, SOAR frees up human analysts to focus on more complex, strategic tasks that require human judgment, critical thinking, and creativity. This includes investigating novel threats, developing new security strategies, and conducting proactive threat hunting. The efficiency gained through automation directly translates into reduced incident response times and a lower likelihood of successful attacks due to delayed detection or response.
The power of automation in SOAR lies in its scalability and consistency. Automated workflows execute precisely as programmed, every time, regardless of the time of day or the workload of the human team. This ensures a baseline level of security vigilance and a predictable, rapid response to common threats.
Response: Streamlining Incident Handling
The “Response” in SOAR is about facilitating and optimizing the entire incident response lifecycle. While orchestration and automation lay the groundwork, the response component focuses on guiding the investigation, remediation, and documentation of security incidents.
SOAR platforms provide a centralized console where security analysts can monitor ongoing incidents, review the automated actions taken, and initiate further manual or automated steps. When a complex incident occurs that requires human intervention, SOAR presents all relevant information in a consolidated view, making it easier for analysts to understand the scope and impact of the threat.
Furthermore, SOAR can automate the creation of incident tickets, the generation of reports for management and compliance purposes, and the notification of relevant stakeholders. This streamlines the administrative aspects of incident response, which can often be as time-consuming as the technical investigation itself. By providing a structured framework for response, SOAR ensures that incidents are handled systematically and thoroughly, minimizing the chances of overlooked details or missed steps.
The response capabilities of SOAR also extend to facilitating collaboration. When multiple teams or individuals are involved in an incident, SOAR platforms can act as a central hub for communication and task assignment, ensuring that everyone is working with the latest information and moving towards a common goal. This coordinated approach is critical for effectively mitigating sophisticated attacks.
The Value Proposition: How SOAR Benefits Organizations
The adoption of SOAR technology offers a compelling value proposition for organizations across various sectors. Beyond the immediate gains in efficiency, SOAR contributes to stronger security posture, enhanced brand reputation, and improved financial management.
Enhancing Digital Security and Threat Mitigation
The most apparent benefit of SOAR is its direct impact on an organization’s digital security. By automating incident response, SOAR significantly reduces the “dwell time” – the period between when a compromise occurs and when it is detected and contained. A shorter dwell time means less opportunity for attackers to exfiltrate data, cause damage, or establish a persistent presence within the network.
SOAR’s ability to orchestrate multiple security tools also leads to a more comprehensive understanding of threats. Instead of relying on isolated alerts, analysts can leverage SOAR to correlate data from various sources, providing a richer context for threat detection and analysis. This improved context allows for more accurate identification of true threats and a reduction in false positives, enabling security teams to focus their efforts where they are most needed.
Moreover, SOAR empowers organizations to adopt a more proactive security stance. By analyzing patterns in past incidents and threat intelligence, SOAR playbooks can be refined to anticipate and neutralize emerging threats before they cause significant harm. This shift from a reactive to a proactive security model is essential in today’s threat landscape.
Protecting Brand Reputation and Building Trust
In today’s hyper-connected world, a data breach can have devastating consequences for an organization’s brand reputation. News of a security incident can spread rapidly, eroding customer trust, damaging public perception, and leading to significant financial losses. SOAR plays a vital role in safeguarding brand reputation by enabling faster and more effective incident response.
When a security incident does occur, the speed and efficiency with which it is handled can significantly influence the public’s perception. A swift, well-managed response demonstrates that an organization takes its security seriously and is capable of protecting its customers’ data. Conversely, a slow, disorganized response can amplify negative sentiment and further damage brand equity.
SOAR’s automation of routine response tasks ensures that even during a crisis, the essential steps are taken promptly. This allows human analysts to focus on the strategic aspects of communication and damage control, ensuring that the organization can provide accurate information to affected parties and the public. By minimizing the impact of a breach through rapid containment and remediation, SOAR helps to preserve customer trust and protect the long-term value of the brand. In essence, robust cybersecurity, facilitated by technologies like SOAR, is no longer just an IT concern but a fundamental pillar of brand integrity.
Optimizing Financial Resources and Driving ROI
From a financial perspective, SOAR offers substantial benefits by optimizing resource allocation and driving a significant return on investment (ROI). Cybersecurity is an increasingly expensive endeavor, with organizations investing heavily in talent, tools, and processes. SOAR helps to maximize the value of these investments.
By automating repetitive tasks, SOAR reduces the reliance on manual labor, which can be a significant cost center for SOCs. This allows organizations to do more with their existing security staff, or to reallocate those resources to more strategic initiatives. The increased efficiency also means that fewer security incidents can cause significant financial damage, such as lost revenue due to system downtime, regulatory fines, or legal fees.
The proactive capabilities of SOAR, enabled by intelligent automation, can prevent costly breaches from occurring in the first place. The cost of preventing an attack through robust security measures is almost always significantly lower than the cost of recovering from a successful breach. Therefore, the investment in SOAR can be viewed as a strategic financial decision that mitigates risk and protects the bottom line.
Furthermore, the improved incident response times facilitated by SOAR can lead to reduced business disruption. When systems are compromised, downtime can translate directly into lost revenue and decreased productivity. By rapidly detecting and containing threats, SOAR helps to minimize these disruptions, ensuring business continuity and protecting financial performance. The demonstrable improvements in efficiency, risk reduction, and operational continuity contribute to a strong ROI for SOAR deployments.
The Future of SOAR and Its Role in Emerging Tech
The evolution of SOAR is closely intertwined with broader technological trends. As new threats emerge and existing ones become more sophisticated, SOAR platforms will need to adapt and integrate with emerging technologies to remain effective.
The Symbiotic Relationship with AI and Machine Learning
Artificial Intelligence (AI) and Machine Learning (ML) are revolutionizing cybersecurity, and SOAR is a key beneficiary and enabler of this transformation. AI and ML can analyze vast datasets to identify subtle patterns indicative of malicious activity, detect anomalies that human analysts might miss, and predict future threat vectors.
SOAR platforms leverage AI and ML in several ways. For instance, AI algorithms can be integrated into SOAR playbooks to enhance threat detection and analysis. ML can be used to automatically enrich alerts with contextual information and provide risk scores, helping to prioritize incidents. AI-powered chatbots can even be used to guide analysts through incident response workflows or to answer common queries.
Conversely, SOAR provides the structured data and operational framework that AI and ML models need to be effective in a real-world security context. The automation and orchestration capabilities of SOAR ensure that the insights generated by AI are acted upon quickly and efficiently. This symbiotic relationship means that as AI and ML capabilities advance, SOAR platforms will become even more powerful and intelligent.
Adapting to the Evolving Threat Landscape
The threat landscape is in constant flux, with new attack vectors and malware variants emerging daily. SOAR platforms must be agile enough to adapt to these changes. This involves the ability to quickly update playbooks, integrate with new threat intelligence feeds, and learn from new attack patterns.
As organizations increasingly adopt cloud computing, the Internet of Things (IoT), and remote work models, the attack surface expands. SOAR solutions are being developed to address the unique security challenges posed by these evolving environments. For example, SOAR playbooks can be designed to automate the response to compromised IoT devices or to manage security incidents in distributed cloud environments.
The continuous development and refinement of SOAR playbooks are crucial. Organizations need to regularly review and update their automated workflows to ensure they remain effective against current threats. This might involve incorporating new detection methods, adding new remediation steps, or adjusting the logic of existing playbooks based on the latest threat intelligence.
In conclusion, SOAR is a transformative technology in cybersecurity, offering a powerful combination of orchestration, automation, and response capabilities. By connecting disparate security tools, automating repetitive tasks, and streamlining incident handling, SOAR empowers organizations to enhance their digital security, protect their brand reputation, and optimize their financial resources. As technology continues to evolve, SOAR will undoubtedly play an even more critical role in helping organizations navigate the complex and dynamic world of cybersecurity.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.