In the intricate and often volatile landscape of digital security, understanding the mechanisms behind cyberattacks is paramount for both prevention and defense. One such insidious technique that has plagued networks for decades is IP spoofing. Often operating silently and with deceptive simplicity, IP spoofing allows malicious actors to impersonate legitimate systems, bypass security measures, and launch a myriad of further attacks. Far from a mere technical trick, it represents a fundamental vulnerability in how internet communication is structured, demanding a comprehensive grasp for anyone involved in securing digital assets.
At its core, IP spoofing is the act of creating Internet Protocol (IP) packets with a falsified source IP address, making the packet appear to originate from a different, usually trusted, machine. This manipulation exploits the stateless nature of many IP-based communications, where the recipient typically trusts the source address declared in the packet header. By disguising their true origin, attackers can achieve anonymity, circumvent access controls, and facilitate a range of illicit activities, from simple prank calls to sophisticated distributed denial-of-service (DDoS) attacks and data breaches. To truly appreciate the threat, one must delve into its technical underpinnings, the varied methods of its execution, and the profound impact it can have on individuals, businesses, and critical infrastructure.
Understanding the Fundamentals of IP Spoofing
To fully grasp what IP spoofing entails, it’s essential to first establish a foundational understanding of IP addresses and the basic principles of network communication. This will provide the necessary context to appreciate how the manipulation of these fundamental elements can lead to significant security vulnerabilities.
What is an IP Address?
An IP (Internet Protocol) address is a unique numerical label assigned to every device connected to a computer network that uses the Internet Protocol for communication. Much like a street address for your home, an IP address serves two primary functions: host or network interface identification and location addressing. It allows devices to send and receive data across networks, ensuring that information reaches its intended destination. There are two main versions of IP addresses in use today: IPv4 (e.g., 192.168.1.1) and IPv6 (e.g., 2001:0db8:85a3:0000:0000:8a2e:0370:7334), with IPv6 designed to address the exhaustion of IPv4 addresses and offer enhanced features. When you send an email, browse a website, or stream a video, your device’s IP address is part of the information embedded in the data packets that traverse the internet, telling servers where to send their responses.
The Core Concept of Spoofing
The term “spoofing” in cybersecurity refers to the act of deceiving a system or user by masquerading as something or someone else. In the context of IP spoofing, this deception specifically involves manipulating the source IP address within the header of an IP packet. When a computer sends data over a network, it breaks the data into small chunks called packets. Each packet contains a header with vital information, including the source IP address (where the packet originated) and the destination IP address (where it’s going). IP spoofing occurs when an attacker modifies the source IP address field to an address other than their own, making it appear as though the packet came from a different, often legitimate or trusted, host on the network. This act bypasses standard identification mechanisms, making the attacker’s true identity harder to trace and allowing them to potentially exploit trust relationships between systems.
How IP Spoofing Works Technically
The technical mechanics of IP spoofing revolve around the construction and injection of modified network packets. Attackers typically use raw socket programming, a low-level network programming interface, to craft custom IP packets. With raw sockets, an application can directly manipulate various fields in the IP packet header, including the source IP address, destination IP address, protocol type, and other flags. The attacker sets the source IP address to one that belongs to a different device or network, often one that is known to be trusted by the target system. These custom-crafted packets are then injected into the network.
When the target system receives these spoofed packets, it processes them as if they originated from the falsified source IP address. For instance, if a target server has a rule to trust traffic from a specific internal IP address (e.g., a database server), an attacker could spoof that internal IP address to gain unauthorized access. The key challenge for the attacker, particularly in “non-blind” spoofing scenarios (where they need to receive responses), is to ensure that responses sent by the target system to the spoofed source IP address are somehow redirected back to them, or that they can predict the responses. In “blind” spoofing, the attacker simply sends packets without needing to see the response, often for denial-of-service attacks. Modern operating systems and network devices have implemented some protections, but the fundamental nature of IP routing still makes spoofing a persistent threat.
Common Types and Methods of IP Spoofing
IP spoofing is not a monolithic attack but rather a versatile technique employed within a broader range of cyber warfare strategies. Its application varies depending on the attacker’s objective, ranging from simple anonymity to complex network infiltration. Understanding these different types and methods provides insight into the diverse threat landscape.
Blind Spoofing vs. Non-Blind Spoofing
The distinction between blind and non-blind IP spoofing lies in the attacker’s ability to receive responses from the target.
- Blind Spoofing: In blind spoofing, the attacker sends spoofed packets without needing to see or predict the responses from the target system. This method is particularly effective for attacks where the attacker’s goal is simply to elicit a reaction from the target, rather than establish a full two-way communication session. A prime example is a Denial-of-Service (DoS) or Distributed Denial-of-Service (DDoS) attack, where the objective is to overwhelm a server with traffic. The attacker sends numerous packets with spoofed source IPs, and the target server attempts to respond to these non-existent or innocent source IPs, wasting its resources and becoming unavailable to legitimate users. The attacker remains anonymous because the responses are sent elsewhere.
- Non-Blind Spoofing: Non-blind spoofing is more sophisticated and challenging to execute. In this scenario, the attacker does need to receive responses from the target system to complete a task, such as establishing a connection or receiving data. To achieve this, attackers often employ techniques like sniffing the network to predict sequence numbers (critical for TCP/IP communication) or diverting the responses back to their machine through other means, such as ARP spoofing or routing table manipulation. This type of spoofing is typically used in more targeted attacks, like session hijacking or exploiting trusted relationships between systems.
Denial-of-Service (DoS) and Distributed Denial-of-Service (DDoS) Attacks
One of the most common and devastating applications of blind IP spoofing is in DoS and DDoS attacks. In a DoS attack, an attacker floods a target system with an overwhelming volume of traffic, rendering it inaccessible to legitimate users. When multiple compromised systems (a botnet) are used to launch such an attack, it becomes a DDoS attack. IP spoofing plays a crucial role here for several reasons:
- Anonymity: By spoofing source IP addresses, the attackers can obscure their true location and make it significantly harder for law enforcement and security teams to trace the origin of the attack.
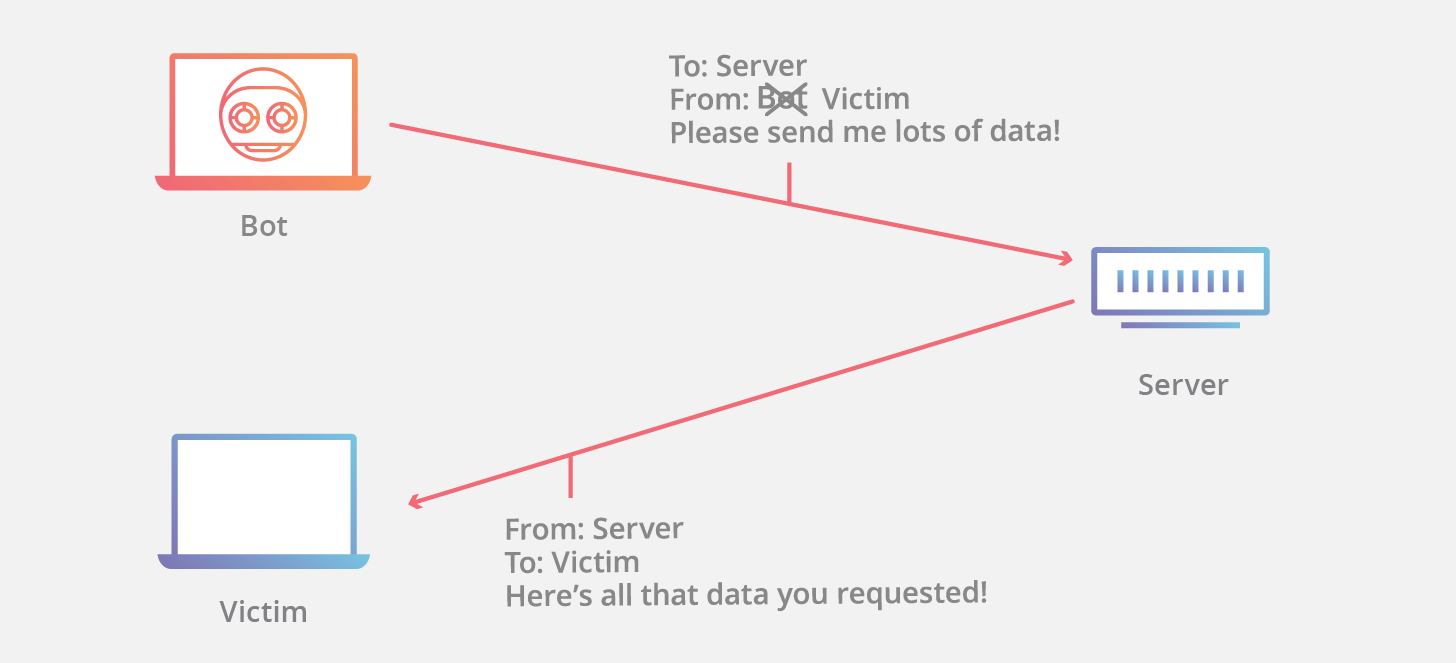
- Amplification: Some DoS/DDoS techniques, such as DNS amplification or NTP amplification attacks, rely heavily on IP spoofing. Attackers send small requests with the target’s spoofed IP address to a large number of open reflectors (e.g., DNS servers). These reflectors then send much larger responses to the target, amplifying the attack traffic and overwhelming the victim.
Man-in-the-Middle (MITM) Attacks
While not exclusively an IP spoofing technique, IP spoofing can be a component of more complex Man-in-the-Middle (MITM) attacks. In a classic MITM attack, an attacker intercepts communication between two parties who believe they are communicating directly with each other. IP spoofing might be used to trick one or both parties into sending traffic through the attacker’s machine. For example, by spoofing the IP address of a default gateway, an attacker could convince local machines to send their internet traffic through the attacker’s system, allowing them to inspect, modify, or drop packets. This is often combined with other spoofing techniques like ARP spoofing at the data link layer.
Session Hijacking
Session hijacking involves an attacker taking over an existing authenticated session between two parties, typically a client and a server. If the attacker can predict or intercept the sequence numbers of a TCP connection, they can use IP spoofing to inject packets into the ongoing session, impersonating one of the legitimate parties. By successfully spoofing the IP address and guessing the correct sequence numbers, the attacker can send commands to the server as if they were the legitimate client, gaining unauthorized access to accounts, data, or system resources without needing to authenticate themselves.
The Malicious Intent: Why Cybercriminals Use IP Spoofing
The underlying motivation for employing IP spoofing techniques is almost always malicious, driven by a desire to exploit vulnerabilities, evade detection, and achieve illicit objectives. Attackers leverage IP spoofing to gain an upper hand in various cyber operations.
Bypassing Network Security Measures
Many network security systems, such as firewalls, access control lists (ACLs), and intrusion prevention systems (IPS), are configured to permit or deny traffic based on source and destination IP addresses. They establish trust relationships where certain IP ranges or specific hosts are deemed “safe” and allowed privileged access. By spoofing a trusted IP address, an attacker can effectively trick these security measures into granting unauthorized access to restricted network segments, internal resources, or sensitive data. This allows them to sidestep perimeter defenses that would otherwise block their true, untrusted source IP.
Anonymity and Evasion of Detection
One of the most significant advantages of IP spoofing for cybercriminals is the anonymity it provides. When an attacker’s real IP address is masked by a spoofed one, tracing the origin of an attack becomes incredibly difficult. The logs on the victim’s system and intermediate network devices will show the spoofed IP address, leading investigators down a false trail. This evasion of detection allows attackers to operate with a reduced risk of identification, prosecution, or having their infrastructure taken down. It buys them time to carry out their operations and move on before their true identity is uncovered.
Launching Further Attacks
IP spoofing is often not the end goal but rather a stepping stone or an enabler for more complex and damaging attacks. Once an attacker has successfully spoofed an IP address, they can leverage this advantage to launch subsequent attacks with greater impact. For example, by spoofing an internal IP address, an attacker could perform port scanning, vulnerability exploitation, or malware injection within the network, appearing as a trusted internal entity. This internal presence can then be used to elevate privileges, exfiltrate data, or establish persistent backdoors, escalating the initial breach into a full-scale compromise.
Exploiting Trust Relationships
Many network architectures are built on a foundation of implicit trust between internal systems. For instance, a web server might trust an application server, which in turn trusts a database server. These trust relationships are often based on IP addresses; if traffic originates from a certain IP, it’s automatically granted a certain level of access or privilege. Attackers exploit this trust by spoofing the IP address of a trusted entity. This allows them to bypass authentication mechanisms, gain access to sensitive services, and inject malicious commands or data into systems that would normally require strict credential verification. This is particularly dangerous in environments where internal network segmentation and zero-trust principles are not rigorously applied.
Real-World Impacts and Dangers of IP Spoofing
The consequences of successful IP spoofing attacks can be far-reaching, affecting individuals, organizations, and even critical national infrastructure. The dangers extend beyond immediate technical disruptions to encompass financial losses, reputational damage, and long-term security implications.
Data Theft and Unauthorized Access
Perhaps one of the most immediate and critical dangers of IP spoofing is its role in facilitating data theft and unauthorized access. By bypassing network security controls or exploiting trusted relationships, attackers can gain entry to systems containing sensitive information. This includes personally identifiable information (PII), financial records, intellectual property, trade secrets, and classified government data. Once inside, they can exfiltrate this data, leading to severe privacy breaches, corporate espionage, and financial fraud. The unauthorized access can also lead to direct manipulation of systems, causing data corruption or alteration.
Service Disruption and Financial Loss
IP spoofing is a cornerstone of many Denial-of-Service (DoS) and Distributed Denial-of-Service (DDoS) attacks. These attacks aim to disrupt the normal functioning of websites, online services, or entire networks by overwhelming them with traffic. For businesses, this translates directly into significant financial losses due to:
- Downtime: Websites, e-commerce platforms, and critical business applications become unavailable, halting sales and operations.
- Loss of Productivity: Employees may be unable to access necessary systems, leading to reduced efficiency.
- Recovery Costs: Remediation efforts, including forensic analysis, system restoration, and enhanced security measures, can be extremely expensive.
- Missed Opportunities: In competitive markets, service disruption can lead to customers switching to competitors, resulting in long-term revenue loss.
Reputational Damage
Beyond the immediate financial and operational impacts, successful IP spoofing attacks can severely damage an organization’s reputation. When a company experiences a data breach or a prolonged service outage due to an IP spoofing-enabled attack, public trust erodes. Customers, partners, and investors may lose confidence in the organization’s ability to protect their data and provide reliable services. Rebuilding a damaged reputation can take years and significant investment in public relations and security enhancements, sometimes even proving insurmountable for smaller entities.
Escalation of Cyber Attacks
IP spoofing often serves as the initial vector or an enabling technique in a multi-stage cyberattack. A seemingly isolated IP spoofing incident can quickly escalate into a more severe compromise. For example, an attacker might use spoofing to gain a foothold, then elevate privileges, install malware, establish persistent backdoors, or launch internal phishing campaigns. This allows them to pivot through the network, accessing more critical systems and eventually achieving their ultimate objective, whether it’s industrial espionage, ransomware deployment, or complete network takeover. The stealth and deception offered by spoofing make it a dangerous precursor to a wide array of advanced persistent threats (APTs).
Detecting and Mitigating IP Spoofing Threats
Given the pervasive and insidious nature of IP spoofing, organizations must implement robust strategies for both detection and mitigation. A multi-layered defense approach is crucial to minimize the risk and impact of these attacks.
Network Monitoring and Packet Filtering
Continuous network monitoring is fundamental to detecting anomalies that might indicate IP spoofing. Intrusion Detection Systems (IDS) and Security Information and Event Management (SIEM) solutions can analyze network traffic in real-time for suspicious patterns, such as packets arriving with internal source IP addresses from external interfaces, or unusual traffic volumes. Packet filtering, implemented at network perimeters and internal routing points, is a proactive measure.
Strong Authentication and Encryption Protocols
While IP spoofing manipulates the source IP address, strong authentication and encryption protocols provide additional layers of security that can mitigate its effects.
- Authentication: Technologies like two-factor authentication (2FA) or multi-factor authentication (MFA) ensure that even if an attacker spoofs an IP, they still cannot gain access without proper credentials. Secure protocols like Kerberos or digital certificates for mutual authentication can prevent unauthorized access even when IP addresses are compromised.
- Encryption: Using encrypted communication channels, such as VPNs (Virtual Private Networks) and TLS/SSL for web traffic, ensures that even if an attacker intercepts spoofed packets, the data payload remains unreadable. This also helps in verifying the identity of communication endpoints, making spoofing harder to leverage effectively for data theft.
Ingress and Egress Filtering
These are two critical network security practices specifically designed to combat IP spoofing at the router level:
- Ingress Filtering: Implemented at the network’s boundary (e.g., by an Internet Service Provider or at an organization’s edge router), ingress filtering inspects incoming packets. It checks if the source IP address of an incoming packet legitimately belongs to a network segment that is allowed to send traffic through that interface. If an external packet arrives with a source IP address that appears to be internal to the network, the filter will drop it. This prevents attackers from outside the network from spoofing internal IP addresses.
- Egress Filtering: Applied to outgoing packets, egress filtering ensures that only packets with legitimate internal source IP addresses leave the network. This prevents internal attackers or compromised internal systems from launching IP spoofing attacks against external targets, thereby protecting the organization’s reputation and preventing it from becoming a source of cyberattacks.
Firewalls and Intrusion Detection Systems (IDS)
Modern firewalls act as sophisticated gatekeepers, enforcing security policies based on various criteria, including source/destination IP addresses, ports, and protocols. Configured correctly, firewalls can block traffic from spoofed IPs. Intrusion Detection Systems (IDS) and Intrusion Prevention Systems (IPS) go a step further. An IDS monitors network or system activities for malicious activity or policy violations and can alert administrators. An IPS takes preventive action, such as blocking suspicious traffic, dropping malicious packets, or resetting connections. Both can be configured with rules to identify and react to common IP spoofing patterns, such as packets with impossible source IP addresses (e.g., private IPs from a public interface).
Regular Security Audits and Updates
Maintaining a strong security posture against IP spoofing, and cyber threats in general, requires ongoing vigilance. Regular security audits, penetration testing, and vulnerability assessments help identify weaknesses in network configurations, firewall rules, and authentication mechanisms that could be exploited by spoofing attacks. Furthermore, keeping all network devices, operating systems, and security software up-to-date with the latest patches and firmware updates is crucial. These updates often contain fixes for vulnerabilities that attackers could leverage to perform spoofing or bypass existing defenses, thereby strengthening the overall resilience against such threats.

Conclusion: The Ever-Evolving Battle Against IP Spoofing
IP spoofing stands as a testament to the enduring challenges in digital security. While conceptually straightforward, its effective implementation can lead to a cascade of complex and damaging cyber incidents, from the disruption of critical services to the insidious theft of sensitive data. It exploits the very fabric of internet communication, leveraging the trust inherent in IP addresses to deceive and infiltrate.
As technology evolves, so too do the sophistication of attack vectors and the defenses erected against them. The battle against IP spoofing is an ongoing one, demanding perpetual vigilance and a multi-faceted approach. Organizations and individuals alike must commit to robust network security practices—implementing ingress and egress filtering, deploying advanced monitoring tools, enforcing strong authentication, and maintaining diligent patching schedules. Only through a combination of technical safeguards, continuous monitoring, and a proactive security mindset can we hope to mitigate the risks posed by this stealthy and persistent cyber threat, ensuring a more secure and trustworthy digital future.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.