In the history of software engineering, few innovations have been as disruptive or as misunderstood as Bitcoin. While often discussed in the context of market volatility or investment strategies, Bitcoin is, at its core, a groundbreaking technological protocol. It is an open-source, peer-to-peer software system that solved a problem computer scientists had struggled with for decades: how to create a digital asset that cannot be copied, spent twice, or controlled by a central authority. To understand how Bitcoin works is to understand a sophisticated convergence of cryptography, distributed systems, and consensus algorithms.
The Foundation of the Network: Blockchain and Distributed Ledger Technology
At the heart of Bitcoin’s technical architecture is the blockchain. Contrary to popular belief, a blockchain is not a complex database but rather a simplified, linear, and append-only ledger. It is a chronological record of every transaction ever made on the network, shared across a global network of computers.
The Anatomy of a Block
Every “block” in the Bitcoin blockchain acts as a page in a ledger. A block consists of two primary components: the header and the body. The body contains the list of validated transactions that have occurred since the last block was created. The header is more technical, containing metadata such as a timestamp, a reference to the previous block (the “hash”), and a “Merkle root.” The Merkle root is a mathematical fingerprint of all the transactions within that block, allowing the system to verify large amounts of data without requiring a user to download the entire transaction history. By linking each block to the previous one via a cryptographic hash, the system creates a “chain.” If a single bit of data in an old block is altered, the hash changes, breaking the chain and alerting the entire network to the attempted fraud.
Decentralization: The Power of Peer-to-Peer Architecture
Unlike traditional software that relies on a central server (like a bank or a social media platform), Bitcoin operates on a Peer-to-Peer (P2P) network. Every participant—or “node”—in the network maintains a copy of the entire blockchain. This redundancy is the bedrock of Bitcoin’s security. Because there is no central point of failure, the network cannot be shut down by a single government or entity. Nodes communicate with each other constantly, broadcasting new transactions and new blocks to ensure that every participant has an identical, up-to-date version of the ledger.
Securing the System: Cryptography and Digital Signatures
Bitcoin does not rely on usernames or passwords. Instead, it utilizes asymmetric cryptography, a branch of mathematics that allows for secure communication and verification in an environment where no one knows or trusts each other.
Public and Private Keys
When a user “holds” Bitcoin, they are actually holding a pair of cryptographic keys: a public key and a private key. Your public key is like an email address; it is the alphanumeric string you share with others to receive data (or in this case, value). Your private key, however, is a secret piece of data used to “sign” transactions. This digital signature is a mathematical proof that the transaction came from the owner of the funds. The genius of this system lies in the fact that while anyone can use your public key to verify that your signature is valid, it is mathematically impossible for them to derive your private key from your signature or your public address.
Hashing: The Fingerprint of Data
The most critical tool in Bitcoin’s security toolkit is the SHA-256 hashing algorithm. Developed by the NSA, SHA-256 is a “one-way” function. It takes any input (a word, a file, or a block of transactions) and turns it into a fixed-length string of 64 characters. This process is irreversible; you cannot work backward from the hash to the original data. In the Bitcoin protocol, hashing is used to ensure the integrity of the data. Because even a tiny change in the input results in a completely different hash, the network can instantly detect if someone has attempted to tamper with a transaction.
The Consensus Mechanism: Proof of Work and Mining

One of the greatest challenges in a decentralized system is reaching a consensus. How do thousands of independent computers agree on which transactions are valid without a central “boss” to decide? Bitcoin solves this through a process called Proof of Work (PoW).
The Role of Nodes and Miners
While all miners are nodes, not all nodes are miners. Standard nodes validate transactions to ensure they follow the rules of the protocol. Miners, however, perform the heavy lifting. Mining is the process of adding new blocks to the blockchain. To do this, miners use specialized hardware (ASICs) to solve a complex mathematical puzzle. This puzzle involves finding a hash for a new block that meets a specific “difficulty target” set by the network. This is essentially a massive game of trial and error, where miners guess billions of combinations per second until one finds the correct solution.
Solving the Double-Spending Problem
The primary purpose of Proof of Work is to prevent “double-spending”—the digital equivalent of a person spending the same $20 bill at two different stores simultaneously. Because mining requires significant computational power and electricity, it creates a “cost of entry.” If a malicious actor wanted to rewrite the ledger to spend their Bitcoin twice, they would need to control more than 51% of the network’s total computing power. This makes attacking the network exponentially more expensive than simply participating honestly and earning the rewards for mining new blocks.
The Lifecycle of a Transaction
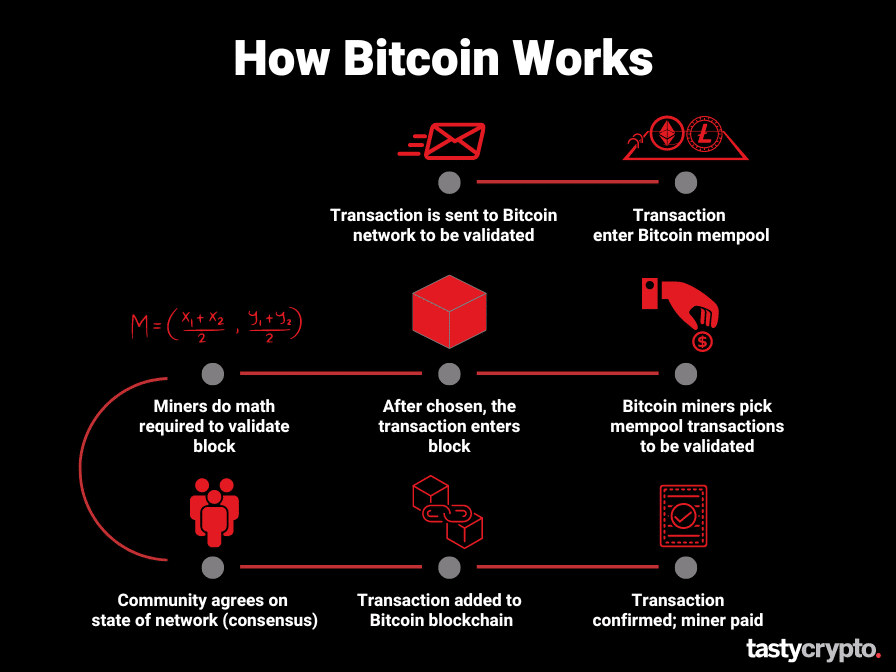
To truly understand how Bitcoin works, one must follow the path of a transaction from the moment a user clicks “send” to the moment the funds are finalized on the ledger.
From Wallet to Mempool
When you initiate a transaction, your wallet software creates a digital message. This message includes the amount of Bitcoin, the recipient’s address, and your digital signature. This transaction is then broadcast to the nearest nodes on the P2P network. Before a transaction is added to a block, it sits in a temporary holding area called the “Mempool” (Memory Pool). Here, nodes check the transaction to ensure the digital signature is valid and that the sender actually has enough Bitcoin to complete the transfer.
Confirmation and Finality
Miners select transactions from the Mempool—usually prioritizing those with higher fees—and group them into a candidate block. Once a miner solves the Proof of Work puzzle, they broadcast the new block to the network. Other nodes quickly verify that the solution is correct and that the transactions within the block are valid. If everything checks out, they add the block to their copy of the ledger and begin working on the next one. A transaction is considered “confirmed” once it is included in a block. As subsequent blocks are added on top of it, the transaction becomes increasingly “buried” under layers of computation, making it virtually impossible to reverse.
Future-Proofing the Protocol: Scalability and Security Upgrades
The Bitcoin protocol is not static. While its core rules are difficult to change (requiring widespread consensus), the technology continues to evolve to meet the demands of a global user base.
Layer 2 Solutions: The Lightning Network
One of the primary technical criticisms of Bitcoin is its throughput; it can only process about 7 transactions per second. To solve this without compromising decentralization, developers created Layer 2 solutions like the Lightning Network. This technology allows users to open “payment channels” with one another. Transactions within these channels happen instantly and for nearly zero cost, as they occur “off-chain.” Only the final balance of the channel is recorded on the main Bitcoin blockchain. This effectively turns the main blockchain into a high-security settlement layer while allowing for millions of micro-transactions to happen on top of it.

The Impact of Soft Forks and Protocol Improvements
Bitcoin’s code is updated through “soft forks”—backward-compatible upgrades that introduce new features. Notable examples include SegWit (Segregated Witness), which optimized how data is stored in a block to increase capacity, and Taproot, which enhanced privacy and enabled more complex “Smart Contracts.” These technical milestones demonstrate that Bitcoin is a living piece of software, capable of integrating modern cryptographic breakthroughs (like Schnorr signatures) while maintaining the rigid security and scarcity that define its value proposition.
By combining the immutability of the blockchain, the security of SHA-256 cryptography, and the game-theory-driven consensus of Proof of Work, Bitcoin has created the world’s first truly resilient digital infrastructure. It is more than just a digital asset; it is a masterclass in distributed systems engineering.
aViewFromTheCave is a participant in the Amazon Services LLC Associates Program, an affiliate advertising program designed to provide a means for sites to earn advertising fees by advertising and linking to Amazon.com. Amazon, the Amazon logo, AmazonSupply, and the AmazonSupply logo are trademarks of Amazon.com, Inc. or its affiliates. As an Amazon Associate we earn affiliate commissions from qualifying purchases.